We're back for the fourth and final installment of our Ask the Mac Guy series. We've covered a wide range of topics in the series thus far, but today, I want to discuss a potentially controversial one.
In this blog, the question I hope to address is: "As a Mac user, should I use an antivirus (AV) on my Mac?"
Let's dive in.
To AV, Or Not to AV?
Over the years, AV use has fluctuated. Once an extremely popular option for users, as Apple prompted that "Macs don't get viruses," fewer and fewer users opted to run an AV on their machine.
Now this isn't all bad, as the downfall of many AVs—such as being more taxing on the system (resource allocation, CPU usage, etc.)—outweighs the benefits of getting some signature-based detections. But before we dive into the answer, I want to give a little background on AVs in general, what they do, and how they differentiate from EDR.
AV vs. EDR
An AV uses signatures to block malware before it executes. On the other hand, endpoint detection and response (EDR) can detect items based on behavior, and then take steps to remediate it.
The idea behind an AV is to have a preset collection of signatures. These signatures may be based on different things—written Yara rules (as seen in XProtect), file hashes (sha1, sha256, md5), team or developer identifiers (a 10-character ID required by Apple to develop software for macOS), and others. This allows an agent running on the endpoint to have a set of items that it is responsible for blocking, so if it encounters malware, it can interrupt it prior to its execution. This is particularly helpful when trying to stop known malicious threats, as well as collecting threat intelligence. You could say that AV looks to block some of the low-hanging fruit, which in turn can reduce the noise to allow your EDR to hunt for the behavioral techniques of malware.

When we talk about if an AV is necessary, I think it is. As macOS becomes a larger target for threat actors, it is beneficial to end users to run some type of software that can block known malicious hashes and developers. Now, many people can leverage XProtect in order to do this, and for users who just use macOS as their personal machine, I believe that it suffices. However—and I've mentioned this in another blog, (dm)XProtect: Stop, Drop, Shut Malware Down Before It Opens Up Shop—at scale, I don't think XProtect is robust enough to fully protect Mac end users.
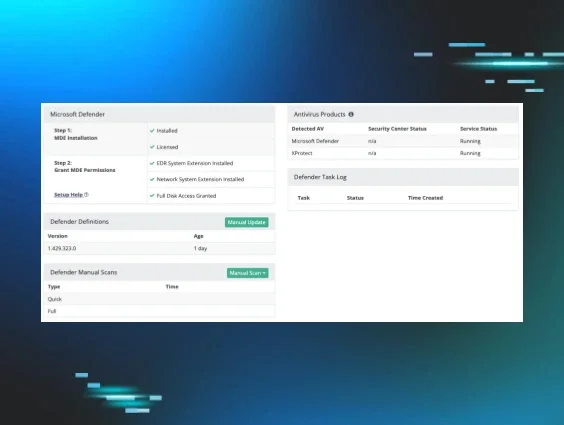
As Huntress’ macOS agent continues to evolve and the feature set expands, we will continue to look at integrating some type of managed AV offering. As of now, it monitors for different types of persistence mechanisms, which can be read about in our Insistence on Persistence blog. And a managed EDR offering is currently in the works.
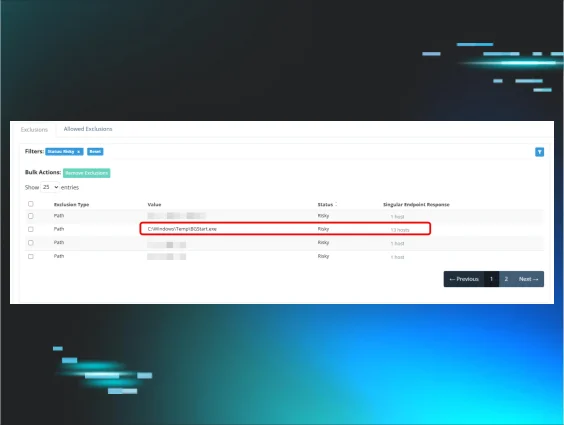
The goal is for the Huntress macOS agent to keep as close parity to our Windows agent as possible. Of course, there are nuances with macOS, specifically installation, the multitude of prompts to the user if the endpoints are not enrolled in an MDM, and just architectural decisions that are required to be different. But as far as pure functionality is concerned, the goal is to keep them similar. So as we start moving toward MAV, you can see how analysts work on the backend.