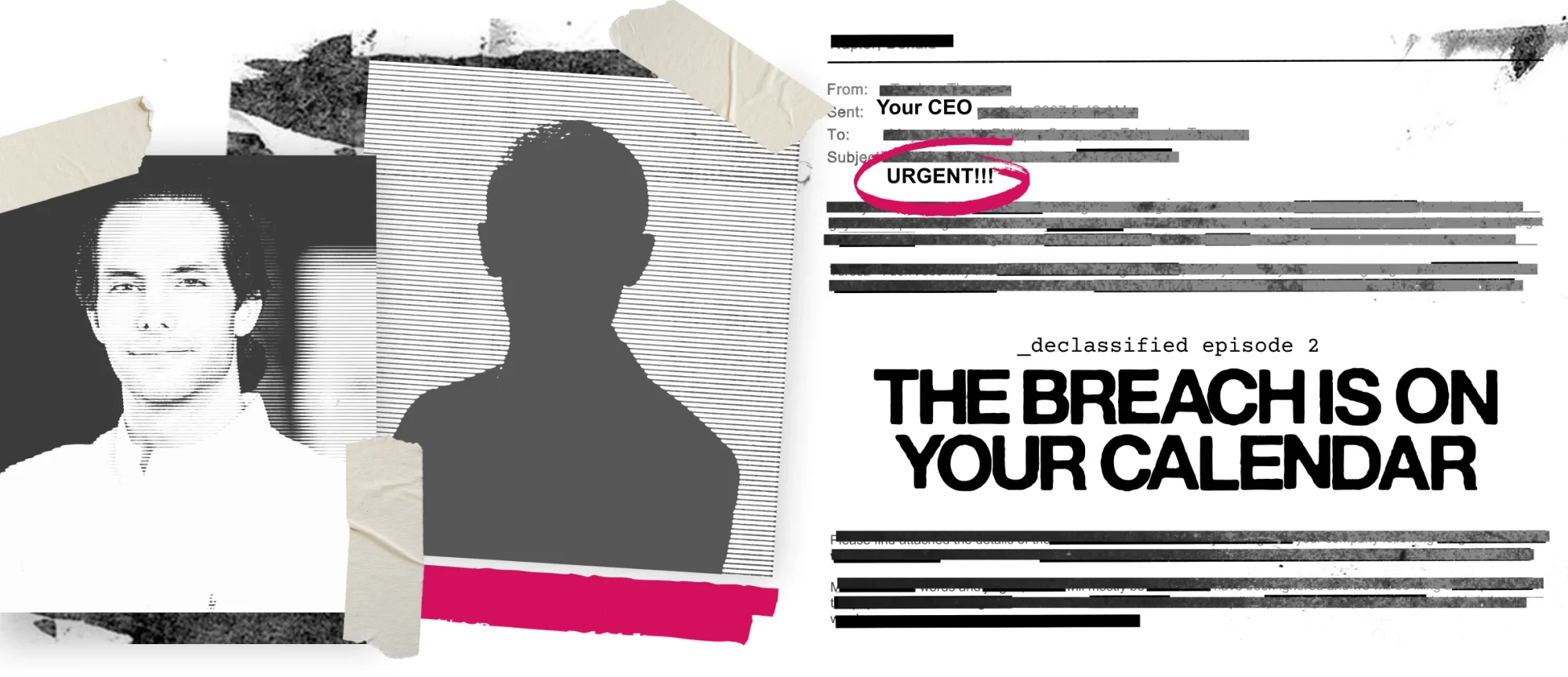




The webinar series exposing the realities of cybercrime and identity risk—hidden truths and all.
Episode 2: May 20, 2026 | 12:00pm ET | 4:00pm GMT | 60 minutes
Missed the live session? It's not too late to hear from John Hammond and Jim Browning.
Join them as they step inside the dark world of cybercrime, where you'll see how bad actors now operate like legitimate businesses, running scams for fast profit. Watch now, on your own schedule.
Alrighty. Hi, everyone, and welcome. Welcome to Declassified. Hey. This is the series premiere, the whole new series, Declassified, that's meant to be a raw intel drop on the dark economy of cybercrime. Now there's a key phrasing there. Right? I wanted to make this, like, some central tension here. The dark economy economy is really like, okay. We're we're breaking this bigger. Because normally, we think of cybercrime and we think of, oh, some hobby in a basement, but it's much, much bigger than that. Right? These are real businesses. It's it's a whole standard industry of hackers and threat actors and fraudsters and scammers that honestly use the same tools, the same org charts, the same sort of KPIs. Right? Really business tech inside and stuff that that you do just as well. All the companies, all the organizations tuning in to watch declassified here. We really wanted to show that, hey. There's this sort of mirror image, a sort of hidden competition for the threats that are out there. But look. Hey. Hi. Hello. My name is John. Right? Hey. I'm John Hammond. I'm the senior principal security researcher at Huntress and really excited to bring the show to you all. I think I'll be your host, but truth be told, we have an extremely special guest that honestly needs no introduction, but I'll do my best. I did wanna help tee him up. Look, Jim Browning. Jim Browning joining the party to help step inside the business of modern cybercrime. And Jim is incredible for one thing. Hey. He's a software engineer. He's a YouTuber alongside myself, fellow content creator, helping share some education, get some awareness out the door for the whole wide world. But, Jim, I think you're mostly all about scams. Scam. Scam baiting, scam call centers, but you take it a little bit further and you get inside of the environment to help take down these scams. Can you tell me a little bit more about it, who you are, and, honestly, can I ask, hey? Why are you willing to keep hanging out with us over here at Huntress? Well, first of all, thank you for having me. I appreciate the invite. Thanks to you. Thanks to Huntress. And, yes, I love digging deep into scams, scammers. And as you say, these people are your hidden adversaries. And I like, just like you do, like to educate people about scams, how they work, and I'm an engineer as well. I like digging into the depths of those scams, and I expose scams and scammers. Now I have to apologize for this because if people don't know, I don't normally show my face on camera. So I'm I'm I've got a little bit of a disguise on. We have met face to face before, but this is for my safety. I am not one of those kind of hacker types who's doing something illegal. Far from it. What I do is actually expose people who are going after your business. So apologize apologies for this getup. It is really for my safety, so I'll say that first of all. But, yes, thank you for the invite. And, yes, it's an interesting topic we're about to talk about. No. Thank you. I should have teed it up a little bit better. I knew look. Yeah. You're gonna be coming in hoodie on, mask up because, hey. You are an ethical hacker for all the right reasons. Right? Doing the right thing to kinda fight back against these threats that are out there. But it makes complete sense keeping that anonymity, keeping that sort of op sec. Right? Operational security intact. But I do have to say something else that we're a little bit excited about for this show. If folks are willing to stick through to the end with us, we have some incredible visuals, show and tell, like CCTV footage, real audio and video from inside the operations here for scam call centers, cybercrime operations. But hold on. Hold on with us till the very end. We do have a cool giveaway for folks that were tuning in. Some sweet AirPods Max that, we'll announce at the very end, but wanted to make sure oh, maybe if you're at the edge of your seat, if we get any audience participation, there's a cool queue for you, then look, we'll have a sweet prize. But if I could kinda set the stage, right, I think there's a cool distinction, that is honestly even a little bit blurry. Right? Because I know right over here at Huntress, we are managed security platform chasing hackers, wrecking hackers to really get what I know that I consider sometimes just traditional ransomware or info stealer malware or cryptocurrency miners or folks that are doing adversary in the middle doing business email compromise, blah blah blah. And I I know sometimes I've almost sort of separated that between what you do, Jim, in in stopping scams. But when I thought about it more, realizing look. This is blurry. The these two are honestly together. When it boils down to it, hackers, threat actors, fraudsters, and scammers, they're all still doing these illicit activities with ill intent to cause real damage, to wreak havoc, to do cybercrime, organized cybercrime. That's the keyword, how it's organized and become a real true business here. Honestly, hackers and scammers, they're one and the same. Exactly. Exactly. And and that's the kinda key point. They really are your hidden competition. So I what I do is I dig a little bit deeper into those. I'm an engineer, much like yourself, probably a lot like everyone or a lot of people who are on this webinar. And what you'll find is your hidden competition is exactly the same as your organization. And what I've been able to do over a few years at this point is dig deep into those organizations. It's not just about me hacking them or similar. A lot of this information comes from people who are disgruntled employees, people on the inside. And a lot of what I'm about to show you here doesn't necessarily come from those hacks or compromises of scam organizations. They could well be insiders. So I would like to take you through what those organizations look like, and maybe you will see a lot of similarities to your own. So if I can talk about really their business, and that is key to it. They do run this like a proper business. And key to all of that is, you know, when you look at these slides, you will see that they look exactly like your business. And that is kind of one of the probably surprising things. They run this thing extremely professionally. They do, for example I think I'll just share these slides here. And while you're getting things going, Jim, I may I wanted to sprinkle in one little teaser because I think you've actually got some exclusives to share with us. Some, like, never never been seen before really cool new fireworks. Yeah. Yeah. Some of this, yes, you will have seen on my YouTube channel. But what you will also see is a few things which I've actually held back from my channel. And even something I record I'm sorry. I'm going to spring this on you a little bit, but something I recorded just earlier today because it is relevant to what we're going to talk about. So this is some of this has definitely never been seen before, and it's like I said, it's a bit of a pleasure to kinda talk through this. But what it once I go through this, I want to emphasize are really the three points that you see here. And you will find that whatever business you're in, what you're about to see, it will look incredibly similar to your own business. And that is no accident. The people who run scams, the people who are your hidden adversaries have to be professional about what they do. And if if they didn't do that, then they would lose money. And it is all about stealing your money, so they have to be extremely careful about that. So as we go through here, they're after your customers, and you will see a lot of overlap between the way they run their business and probably the way you run yours as well. So let me just change this. Let me go. I get the right the right slide. There we go. Sorry. I'm having a little difficulty pushing these slides on. One second. I'll give you some air cover while you're going. Okay. You got it. There we go. Thanks. Finally got it going. So this is something that I lifted from one of those organizations. And what it is, it's a just a single file. Now it's a little bit busy, but what you'll probably see on the left here is that this is a network diagram. Probably, if you're in a small business, this will look very familiar to you. But what I wanted to point out was the fact that the people who created this diagram are scammers. Okay? So all of the kind of back office you know, they've got their internal IP addresses. They've got these rooms mapped out, but it's the rooms. It's the the words in green here that might surprise you because they have their training room. They have their HR room, they have their operations room, and down at the bottom, an IT and quality room. And that's kind of key. And, you know, if you have never seen this before, this probably looks exactly the same as your own business. The fact that they have quality associated with running a scam operation probably doesn't come as a surprise to some people, but absolutely, they have they train their operatives to make sure that they steal as much money as possible. So this sort of layout is probably very similar to your own business, I'd suggest. And I'm sure from what I've seen before, this looks quite familiar to probably a lot of people here. So when I talk about going inside the operation, what you're about to see here has come from, yes, me trying to engage with scammers. I get them to connect into my computer, and I quite deliberately lead them on. I I follow the scam the whole way so that I can unpick their business. And for me, that's the most interesting part of this. How does a business run? I'm an engineer. I like to understand how things work. Can I pull it apart? And that's exactly what I do here. So when you have a look at this, I'm gonna go through a few examples of some of the scam operations that I have managed to disrupt over a number of years. So we've got a picture of four different call centers. And, yes, you're looking at CCTV here. So I I literally mean I can see the people who are running those, like, fraudulent operations. These are four different call centers. They're all in different count well, most of them are in India in this case. One is in Pakistan. And I'll I'll run you through well, you probably the obvious question is, how do I even get the CCTV? And I I think if you ever watch my channel, you'll probably get a bit more of a clue. I don't go into the exact detail because, hey, I don't want them to know exactly what my techniques are. But the most interesting part of this is we're just about to see some scams actually running where I see them on CCTV, and I can hear their telephone calls. Now just to give you an idea about the kind of breadth of scam operations, here are four different call centers. The one on my on the top left here is a travel agency or at least they describe themselves as a travel agency. They're nothing of the sort. It is a front for a scam operation. They run a a legitimate travel company, but, actually, what they do and where most of their money comes from is a fake Microsoft scam operation. They produce fake pop ups or at least they pay people to do their to send out those pop ups, and it will say, hey. Your computer's got a virus. Call this number. And, of course, the people sitting on this top left here are very willing to help diagnose your computer. Strangely, they always find a fault in your computer, and they will, of course, charge you for that. So this particular company, we're making upwards of three million dollars a year running just those pop up And I was able to get that figure because, hey, I've dug into them. I can see where the money goes, and this is just one example. Now there's three others here as well. The one on the top right, it's in Lahore in Pakistan, Pakistan, and it's a company called Tech Harbor Services, and they steal mobile phones. And you might be wondering how on earth do they steal mobile phones? And the answer is they've got a good script to allow them to do that. And the way they do it is they call you up, offer you a discount on your cell phone plan, and if you comply with them or if that sounds interesting and who wouldn't want a discount, they will send what they describe as a promotional code to your cell phone. And as you can imagine, and I'm sure on you will comment on this as well, a code to your phone is then resetting your password, and I'm sure that is quite often what you and Huntress and everything see quite often. It's one huge attack factor, I'm sure. Yeah. I mean, it's funny. We tend to think there's extra safety and security in multifactor authentication. And, of course, without a doubt, there absolutely is that you need to have that layered security, defense, and depth. But one of the craziest things when look. You're kind of on the phone with someone, and that's how a lot of these things happen. Right? Oh, you get a random call, tech support, or whatever the case may be. The pop up tells you to call this number, and then you have a person walking you through the steps, and they say, oh, I'll send you this PIN code that maybe they dress up as a coupon or discount or whatever. Right? But in all reality, that's the access to your account. And we parallel that a lot in our ITDR world, like identity threat detection response. When we see wild stuff like Evil Jinx or Naked Pages or all these sort of phishing kits just to gain access, there's like an adversary in the middle waiting to capture those credentials. But in this case, you're just, like, synchronized on the phone with someone giving it because you're duped. You fell victim to the scam. Yeah. Absolutely. And like I say, a very, very common tactic that and kind of fake invoices, of course. Bottom left here, we have a different one. This one's called DK Business Patron. Unlike a lot of these operations, again, they have their legitimate side. During the day, this company would actually be Amazon resellers. And I could check that because when I got access to it, it was at nighttime. It was the daytime in the US, nighttime in India where this one is, is in Delhi. And they, again, were pretending to be Microsoft, calling people up. Your computer has got a problem, and, of course, no problem at all exists. But that's what they did. And, again, because I could see them in CCTV, I got a very detailed view of how their scam operation went. And the one on the bottom right, this one you may not have heard of before because this is a particularly sneaky scam. And the the although it looks quite a comfortable office, there's lots and lots of people involved in this, what they do is accept inbound calls from people in the US who think they've dialed their bank or their electric company company or someone that they have managed to search the web to get their phone number, but these guys have bought up either similar numbers or old or defunct phone numbers close to real organizations. So say you have a problem with your electric bill, they will be one digit away from the actual genuine electric company. And if you called them up, they would very happily take all of your personal details, including your credit card number. And during the call, they would play what they described as an advert. But in fact, they would sign you up for a monthly subscription service based on the personal details that you thought you were legitimately giving to your electric company. So all very different scams, but all running in a very similar way. So, again, this is what your competition looks like. They may be sitting on phone numbers very similar to your own office, but that's exactly what goes on. Now these are just still images. I have a little example here of me actually able to watch on CCTV one of one of the live calls. So let's have a little listen to this one. Hello? Hello? Yeah. Hi, sir. Very good day to This is Olivia Roger, and I'm Have we got audio okay? Just checking. Can you hear that okay? Just Cool. Excellent. Thank you so much. Audio. Good. I will continue this. There is subtitles here as well because she may be a little bit difficult to make out. I will continue. Calling from the security department of Commonwealth Bank. So how are you doing today? Commonwealth Bank, if you didn't know, is an Australian bank. Well, this call is regarding to your bank account which you are holding with us. It's a verification call to you. Do you authorize any transaction of eight hundred dollars to mister James Smith? Are you sending any overseas money to anyone? I don't know what you're talking about. I'm talking about your bank account. Okay? Your bank account has been holding with us. Okay? It's been with us. Hello? I will I will pause that one there because she can be quite difficult to make out, and I just want to make sure that you definitely hear that one. First of all, you definitely can. Yes? I guess. Okay. I will go past it, but suffice to say that is not Commonwealth Bank as you can plainly imagine. But nevertheless, there's a few other things I just want to point out in this picture. On usually, these guys have got telephones. Normally, what they do is they plug their headsets into their computers. They they will not be using proper phone lines. And, of course, they will be spoofing US, UK, whatever phone numbers. Now in the UK, they have been prevented from spoofing landline numbers. So what they have moved to is spoofing mobile or cell phone numbers. And I think that's something that I would love to see change in the future. But, this may be where Huntress can maybe help with the kind of detection of these sorts of attacks. I don't know if you want to say anything about this one, John. Yeah. Absolutely. It's for one thing, watching the video is insane to me because I see the people, like, snickering and kinda laughing, giggling in the corner, and everyone, every single person is on the phone on a headset dialing and making calls like nonstop, which is crazy to see. But without a doubt, look, Huntress is still trying to track and keep businesses protected. And whenever we acknowledge the fact that there's nothing really stopping any threat actor or adversary from kind of just impersonating you, anyone, brand ajacking has kind of been a thing we've been talking about. That's hey. Why not just claim and say, hey. I am x y z a b c. And then if they get in the middle of some business email compromise, maybe they mid thread or change or redirect a conversation that could lead to things like, I don't know, some wire transfer shenanigans, so many trouble. Those are all the things I know, especially, don't wanna keep harping back to our identity threat work, but that is kind of the big component here is like, okay. Do you know who you're having a conversation with? Are they real or are they totally duping you? Yeah. Yep. I mean, this one and if you haven't seen this thing before, there's plenty of more of this on my channel and other scam builders channel. Sometimes we get to see them and it's kinda nice to be able to really pick them apart this way. Now this is another way that, of course, these scammers, these adversaries impersonate you. This one's obviously a bit more obvious because anytime you see Elon Musk promoting something, you can almost guarantee that is going to be a scam. And this is no exception. Here, they've obviously just edited a real Elon Musk post and put their little message below it. And I'm the kind of person who actually clicks on next trading dot a I or whatever the scam domain is because what I do then is engage with whoever calls me. Now I did happen to register my, obviously, fake details on this particular website, and I got about thirteen different phone calls as a result of that. Each one of those phone calls told me that if I get any more phone calls, the other guys are the scammers. It's not us. We're the real deal. Stick with us. And in fact, a lot of them even had a little password system so that if I didn't quote the password to the next caller, then I should hang up the phone. And that's that's because they knew that this particular trading system, the data that I filled in, would be sold to multiple organizations, all of whom would try to scam me. And the level of sophistication might surprise you. You think this is just, oh, this is somebody trying their luck pretending to be Elon Musk. In fact, the people who are behind this have a whole infrastructure and a very, very sophisticated level of expertise in how to manage people who think that they're about to invest in something. And what I've managed to do here and I've had to kind of remove and redact a little bit of the information because this is a live CRM system from one scam organization who run one of those fake trading apps. And if you can make out what a lot of this says, you can see down the left hand side here, there's a whole lot of things about a ticketing system, a task, a leaderboard even for the people who are running the scams, a leaderboard. And you can get an idea roughly what this is about because on the right hand side on your dashboard, you have the statuses of your, what they call, customers, their scam victims, and how much money each of them has put in here. And I've redacted this deliberately because this is a real live trading system, and I the police are already on to this one. But it gives you an idea of the level of sophistication with it. So not only is there a little overview where you can kinda see how things go, here, I've just drilled down into one what they call customer customer insight. And, obviously, they'll have a a name which I've redacted here. And they've got a particular team. One's called retention with DE, DE for Deutschland or Germany. So not only do they attack people in the US and Europe and English speaking countries, here you can see they've actually got a German speaking team who will target people in Germany. Below this again, again, overview of what they call customers, but, again, there are no such thing. But look at the other things in this. This is all integrated with their fake trading system. And you can see here that there's different countries. They are targeting people in multiple countries. They have affiliates. So not only are they selling this, they buy the data from a third party. There's a whole ecosystem around their scam. And that level of sophistication, you'll probably only see in a really professional organization. So that's just their customer overview. This is their own admin view. So I haven't redacted these names because they're all just names fake names of scammers. So you might have a scammer called Amy Lopez or El Patron is the the boss. They they give themselves this. On the desk that it's associated conversion means that the the person has signed up to a fake investment, and they wanna convert their money into crypto. And retention is someone who's already been scammed, and they are offering to recover their money for them. And this is what they call retention. They've already been scammed. We're going to retain them for yet more money. And not only does it integrate with their fake systems, but they also have their own security around it. So this is an admin account, and even the people who sign up, they are told, for example, they can use two factor authentication. So this isn't just a normal kind of put together, knocked together using AI system. They have sophisticated enough quality control and security systems around it, and that may surprise people the level of sophistication here. And, of course, this is all about getting money out of people. So they have an agent performance, and FTD, by the way, is first time depositor. They're very keen on that stat because if you deposit a little bit of money, this is their opportunity to take yet more from you. So they will collect lots and lots of stats. And remember the little diagram at the start where they've got a quality assurance room and a HR room? That's exactly what this is about. So agent performance is particularly well measured. So any thoughts on that one, John? Because I'm sure if you've worked in any big organization, performance is always key, and there's no exception exception for scammers. Yeah. I mean, for one thing, this is insane. Second, if I could, like, break the fourth wall a little bit. Right? I don't know. Hey, folks tuning in, audience, organizations. Right? I have to think this system, the CRM management dashboard, and everything they've got cooking here probably looks a heck of a lot like what you might have in your own business. Even the sure. Two factor authentication, the security setup, and it's, again, it's just mind blowing to me to see this in both the front of, yes, okay, our scam operation business, and then a front that is a fake company to pretend and to do good in one direction. But then the, like, zoomed in aspect of this for the CRM system or other components in the tech stack that they use, like, literally a shared tech stack mirroring what you use in your organization, sometimes still all for show, all for the lie. Like, the added two factor authentication makes it look legitimate because you feel like you've got the right security connectivity there, and that's just mind blowing to me. But Yeah. I mean, honestly, it it's it's down to the training as well. Yeah. And, you know, I I've also uncovered, and this is a genuine document that I've picked up from a different scam group. This particular group were involved in something called scareware where it you will download a bit of software. And initially, it might be free software, but all of a sudden, it will come up with scary messages that your PC has got all these problems, and you need to upgrade your bit of software. And this particular group trained their employees, in this case, in Japanese so that they could dig out the scam or the scareware market in Japan. And this is a real Japanese language proficiency test entrance on a university in India where they sent this guy in to make sure he could run the scam in Japanese. Listening to to these guys speak Japanese was quite funny, but that's a real document that has been picked up from a scammer. So, yes, very, very sophisticated. And if you think that your office has got its own training department, have a look at what your competition is doing as well. Jim, can I ask, I don't know, just a question, especially from the CRM and that whole management system? Do you know just how much money, I guess, they would have made or they've raked in for scams like this? And I think we got a cool poll that we could fire up. Like, what is Yeah. Audience hey. Folks tuning in. What do you think? How much money do things like this cybercrime economy really make? Or how does it fare amongst the markets of the world? And, Jim, I'd love to get your opinion. What is the real number, if you know, for Yes. What that group was making? I I do have to know for this group. And because they're involved in scareware, you might imagine that those sort of figures be quite difficult to come by. Not if you have my sort of access. And in quite a lot of cases, I'm able to see exactly what those figures look like. This particular group, they're one of or were one of the largest groups involved in this sort of scam. At at one point, employed over three hundred people running scam, and they made upwards of twenty million a year using that scam alone. So I think you've got a little poll up there. I would be interested to see exactly what people think might be the kind of cybercrime economy levels with this because the figures may well be surprising, I think. Yeah. We can leave up the real answer for the end, but please do if anyone's willing to chime in and chat even after you submit your question in the poll and the answer there. But, Jim, you said something that kind of threw me off guard. Right? You you you dangled in the hot commodity, hot topic, new acronym these days. You said AI. AI. Yes. Before we go to AI, though, I'm gonna I have a little exclusive because I mentioned we there's something I've been holding back for quite a while. I've never published on my video on my channel. So this is my little exclusive, first of all, and it's to do with just the the makeup of those organization. So I mentioned, for example, there's a HR department. And what I've been able to do in the past is actually encourage some in in this case, Indian local people who are just very disgruntled. The vast majority of people in India can't stand the scammers and can't stand what they're doing. But there are some very brave individuals who will actually try to infiltrate those organizations. I mentioned at the start of our webinar that sometimes I can get people to actually go in to these scam call centers and actually see how the scam starts. How do these organizations even recruit people in running this sort of scam organization. And what I've got here, I'll just bring it over here. Hopefully, you can see this. I'm gonna keep this video on mute, but I'm just going to play it as I'm speaking. This very brave individual in India is actually going into one of those scam call centers for an interview. And I knew before he went in that this is actually quite a notorious scam group. In fact, the name of the business let me bring that to the front again. Name of the business is VRM Business Services, and they were one of the biggest scam operations in Kolkata or Kolkata in India. And this is the guy going into the offices. He's got a little camera in his top lapel pocket. And, obviously, if he was discovered filming, I mean, goodness knows what would happen to him. So he's very bravely going in past the security here, and he's going to film his interview with VRM business services. I've kind of kept this back because I've exposed this group in the past, and I fully expected them to go, hey. We're a legitimate organization. You know, how dare you pick on us for running scams? We aren't like that. Because as I said before, this group deliberately run a legitimate org organization, a legitimate process alongside their scam operations. And that way, they can kinda cleanly launder money. And if anyone did come in and raid them, then they could point to all legitimate work they're doing and so on. So I'll kinda zoom past this one. He he actually goes into you'll see, for example, the VRM logo in the back here, the security part, but he's still filming. And I'll cut back to the slides because he's going to be brought into an interview room, and the HR lady, yes, they have a HR service as with any normal organization. And she will ask him some questions, the type of questions you would normally hear in one in a normal interview, but notice the terminology they're about to use. They're going to ask, for example they won't mention the word scam. There's an unwritten language that they both understand. And as we as he goes into the scam office, you're going to hear him use some of those terminology. So listen carefully to this. It's subtitled because it's a little bit difficult to hear, but I'm just going to play a little clip where they kind of acknowledge a scam goes on without using the word scam. So have a little listen to this. So like I say, note the terminology here. Yes. These are technical sales, Amazon, you know, refund, and all the all that stuff with the Tech support on date first? Yes. It was tech support. Tech support. Yes. We are telling taxes. What is taxes? Oh, it's it's technical support. I'm sorry. Fine. We also have the same process. You have experience in refund? No, ma'am. I have we have we had that refund process. On the refund process, if you don't know or not familiar with that is, this is a refund scam where they accidentally seem to put too much money into somebody's account. They'll say they'll send you a fee invoice, you spent two hundred dollars. They will get remote access to your computer. They will right on your bank account. And when they say they're going to refund you, what they're really doing is doing the old right click, inspect element, updating it not to two hundred dollars, but to twenty thousand dollars. And then they'll say, oh my goodness. We've given you too much money, and you're gonna have to pay us back or I'll lose my job, and the sob story will start. And I'm sure, again, that is exact although they haven't used the word refund scam here, it's a refund process, there is an unwritten language that they both understand here. So, again, the the director of this operation has been arrested, thankfully. But, you know, this is the kind of competition that you may well see that is operating against your business. So, again, I know that's something that Huntress and your own organization can help with to an extent, I think, John. Yeah. Watching the video is just crazy. They don't even say the word. The the double speak, right, when they kinda skirt around the word scam. You know, one thing that we do, right, for the endpoint detection response efforts and the big side of huntress, we're protecting a boatload of businesses. But, look, how scammers ultimately kinda gain access to your computer. Right? And then they do that, oh, HTML element inspect, tweak and tune the number to make it look crazy. We're we're really trying to keep an eye on, okay, what's normal in your environment, especially for tools that give that sort of control? We talk about remote monitoring and management solutions, things that have, oh, the connectivity to see your screen, to use your keyboard and mouse. If we're looking for stuff like TeamViewer, UltraViewer, AnyDesk, ScreenConnect, right, that list is a laundry list. But those are the things that we wanna know, okay, what is intended to be inside of your environment? And if we ever see some of the strange, random, rogue, different connections that are unexpected or even when scammers leave notes in your notepad. We've told that story before as to, hey. They they said our our phone call dropped. Let me call you back. Don't talk to anyone else. All the things that they do to keep you brainwashed when there are real forensic artifacts kind of on disk, right, Huntress is still gonna hey. Monitoring and triaging and bubbling those up so that we can help spring into action and save the day. But it's wild that, hey. We're kinda going toe to toe with the adversary, hacker, scammer, fraudster, threat actor, whatever the case may be. Yeah. And, like I say, this is sadly, this is quite a I mean, this guy could have gone into multiple organizations. Even in that area alone, there were at least ten or twelve different call centers running similar scams. Should we say this happened to be one of the bigger ones? I'll I'll skip past this one because there was one thing you mentioned, and that was AI. And I think we well, I I've you know, I don't think any webinar would be complete without talking about what's going on with AI because, of course, fraudsters, your adversaries, and, hopefully, you guys as well will also be attempting to use AI in a way that benefits your business. But, of course, your adversaries will try and use AI against you. And I think, John, that's that's one thing that I know that your own business is encountering time and time again. Yes. Without a doubt, we have seen, we are seeing. I know there's a conversation. Oh, is the world changing? Look. No. The world has already changed. I think threat threat actors and organized organized cybercriminals were kind of, I gotta say, the earliest adopters and maybe first movers to leverage artificial intelligence, but we're all over it. Like, Huntress is really leaning into this because, for the longest time, we have been and we still are like, one of the big things we pride ourselves on is a managed security operation center. So twenty four seven, hey, threat hunters and analysts that are all over the world, we fall in the sun, and we that's all funneling up through people, to human beings, to real expertise and real human eyes. But Yeah. We know we now have threats that are moving sort of at machine speed. They're leveraging AI to pull off these attacks. So we still wanna keep being tiptoe, toe to toe with the adversary, and we wanna keep up and keep pace with them. And that's what we are doing. We really believe, hey. That, agentic sock sort of humans and AI together kinda joining forces in a really cool way. But we see it both for, yes, our defensive work and the offensive hackers doing damage. One thing that we're doing, like, right now actively internally, we've kind of got our own little rapid response process happening. We're seeing widespread phishing attacks that are just fanned out with threat actors prompting for infrastructure to come up and then do some of the, you know, classic adversary in the middle, intra ID takeover attacks. We've got some really cool blog posts and some material coming up on that super duper soon, but it's it's happening right now. It's real time. That's the world we're living in. Yeah. I mean, I see that as well. And sadly, over the last couple of years, it is one thing that I've seen well, I mean, I have a few examples on these slides, and I'll I'll talk you through some of them. This is this is what I have seen personally just in the last year. Now remember I mentioned that I engage with the people who run those kind of fake investment sites. One of those people sent me her passport, and I know this is actually something you actually tweeted out just before our our conference. So some people will recognize this slide. But this is something that somebody who called herself Margaret Marshall sent to me to convince me that she was real. Now it used to be that I could take the photograph that's being used in this passport, run it through reverse image search, and you would find the real person behind it. But, of course, these days, it's so easy to create a fake image using AI that that's just not possible anymore. But there is a level of sophistication. This isn't just a a Photoshop version of a passport. This is something where, at very least, it's been edited using Photoshop, but then a real or some sort of passport has been printed, and they have taken a photograph. So all of the metadata, for example, will be there that you would expect a normal photograph to have. It may even have a United States location because they've convinced somebody to take a photograph in a in a location maybe in New York because this person is claiming to be from New York. And when they sent me this, I had to scratch my head. How's is this a victim passport? Because it looked too real. But, no, it is a Photoshop version of this all to convince me that the person is real. And the the the fraudsters are getting more sophisticated. And the other thing that I mentioned at the very start was just before this call, I had a scammer who was willing to join me on a Zoom call. And I'm seeing this a little bit more nowadays. They're not afraid to join Zoom calls for the very reason that they are starting to use deepfix to convince people. Now you've probably seen deepfix before. There is something I'm going to show you here that you may be able to use as a way to kind of figure out whether this is a deepfix or not. So this is a personal Zoom call. Let me just share this first of all, and I'm going to unmute it face anyway. So you'll hear my voice on this guy. I want you to look at two things here. One is the office that he's in. It looks a bit fake, but very shortly, you'll see that it's not fake. But I also want you to look at the little bit of hair on his top right or left as he's talking to me. And I'm going to give you a hint about if you're ever on one of these Zoom calls, and I'm going to ask him particular questions that will figure out whether he is a deepfake or not. And have a listen to what I'm this is only two minutes, less than two minutes, but I do want you to have a little listen to this. This may be of interest to you. Thank you very much. Thank you. You So are you with them on a on a computer or just Yeah. Not a computer, but it's kind of an old computer. You have a a nice office there, I must say. Alright. Yeah. I mean, it's pretty good. It's pretty good. Are you at home right now? His lips Yes. I'm at home. Lying. Getting a little bit behind what he's saying. Great. How do how I know you're not some AI thing? What what what how would I be able to tell? Here, man. Here. Oh, is that sorry. Can you hold that up? It's not AI. Can you Yeah. Of course. But it's not his name. That's a That's our director. Oh, I see. I thought it would be your name. No. No. No. That's our director. We have a multiple. You see all of them here. Oh, I see. Go, Ronnie. But but, you know, it's in What's going on? Way of telling whether you're real or not. Can you, like, hold up three fingers in front of your face or anything? Oh, come on. That's too much. Oh, you don't want to do that? The three fingers in front of your face is deliberate. So What do you mean? I mean, that's too much. Come on, Ronnie. Why would it would it affect the AI if it was in front of your face? Well, not at all. You can hold it up. Hold here. Much to ask somebody. Making sure you're not AI is not unreasonable. I mean, can you do that in front of your face? Well, I think that that's too much to ask somebody. Don't you think that? No. I don't think it is. If I'm making sure you're not AI, I think that's a reasonable thing to ask. Can you hold up three fingers in front of your face? Well, I think that well, is that enough? No. It's not in front of your face. He's really doing his best here. That's too much, don't you think? Yes. It is. Because, you know, if you were real, you would put up three fingers in front of your face. Yes. And of course, he then exited the Zoom call quite deliberately because, you know, I was asking him just to do this. So if you ever if you're ever in any doubt whether someone is using a deepfake, that's quite a good question to ask because you can see him squirming on that one. So yeah. Like I say, that's one way of combating them. I don't know your your thoughts here, John. I mean, I'm sure everybody has seen deepfake videos at this stage, but it's kinda nice to wind them up too. Holy crap, Jim. That happened just before this call, didn't I? Yeah. You came on when we were, you know, getting prepped, getting ready to go live, and I wanted to, again, maybe break the fourth wall because Jim was like, can we show this? Is this cool? I'm like, absolutely. This is insane. I know it's one thing. Hey. We see some pictures of old deepfakes out and about in news and articles, but being able to see and hear you and have this conversation, and that's that's you in the call and hysterical and insane. No. I I that's too much. You know? You wouldn't ask someone of that. And then they just rage quit. Oh, of course. Yeah. Yeah. I I was pushing it too much. So we're like, the guy, you know, just just you can do it to here. Why not do it just here? You know? It's not unreasonable to ask, but, no, he wouldn't do it. He definitely didn't wanna show his face. I I can tell purely because he volunteered at the Zoom call. So, obviously, he has been set up. You know, they they've got their whatever software they're using to do the kind of overlay of the face, but it's only the face you could see him reach behind everything Yeah. That was that was working. But The fingers in front of the face, that is a good way of seeing whether it's deepfake or not. Thank you for covering those, especially. I know we're gonna have a whole ton of questions, and please don't hesitate. Keep them coming. I think it would be awesome for us to dive into, hey. What are some of the tells? How do you identify this? How do we I don't know. Get back in action. How do we fight back against scams that are targeting you, your business? Strangely, it is just what I want to talk about because AI is one thing. It's not just about your adversaries using AI, of course. Your own business, I'm sure, will be using AI to an extent. I I'm certain Huntress is doing this as well, but fighting AI with AI is always a good thing. I'm going to talk about one of the characters that I use. So I give myself several aliases, and one of whom is called Orson Cart, and Orson is an older gentleman with cat pictures on his desktop. So whenever scammers connect to my computer, they see lots of pictures of cats. They've got kind of a a large background. This is my AI face of the guy whose pic photographs you'll see if you ever connect to my computer. He has his own electricity bills in the same way that your fraudsters will kind of, you know, impersonate people. I'm impersonating a victim here, and I have my own fake passport. You saw a better version of this from other scammers, but I have my own one with Orson Cart in here as well just in case. But sadly, even though I'm using AI in kind of a basic level, unfortunately, I do see the fraudsters upping their game with AI. And one of the annoying updates that they have is the fact that they'll use it for robocalls. And I'll play a very quick clip here, but this is what I'm beginning to hear when it comes to normally, you saw rooms full of people making those robocalls, making those fake calls. This is what I picked up the other day. Hello? Hello, Ronnie. This is Sydney calling from Mempool. How do you feel today? I I'm okay. I'm okay. And you'll get the gaps between sent Reason of my call is that you have initiated a withdrawal request. So did you get your funds? And, again, I'll pin I'll ask her what do it to repeat things. So, obviously, this is a bot. Of course. The reason I'm calling is because you initiated a withdrawal request. Sydney. Sydney. Can you hear me? Yes. I can hear you clearly, Ronnie. You can hear the beep sound like a bot. While accused of being a bot and what our answer is is I understand that, Ronnie. Well, are you? I'm a see No, Ronnie. I'm a senior support agent at Mempool. I'll not play anymore of that, but you get the idea. And the only reason why I knew immediately that it was a bot or an AI voice was it had an American accent. I don't normally get people using American accents. Or if I do, it'll be one of those kind of speech to text to text to speech type audio messages, and that's as much as it goes. So, anyway, that sadly is going to be the future of robocalls. They will get quicker. And I know that AI, of course, is getting more sophisticated, so those are all telltale gaps in the conversation. That will change soon as well. And it will be harder to spot whether you're speaking to a bot. That's all I comments on this. Horrifying. Yeah. I mean, that is both scary. And, like, I know we, you and I, and everyone tuning in, like, we've got context. We knew, okay. Sure. That's a scam. That's fake. That's that's AI. But for mom, dad, sons and daughters, grandma, grandpa, coworkers, peers, and colleagues, if they just you know, we're trying to be polite on the phone. You let the other person speak, and we could catch the oh, sure. They got literally truncated and cut off in their sound clip and the the real time processing to wait to get a new response after it's parsed and proceed. But other than that Yeah. You would be convinced that that sounds Yeah. Definitely. Yep. So That does anyway, we're we're kind of approaching the end of this. There are other ways of fighting back. I am currently working with a group in in the UK, who have created something called Daisy. Some people in Skull may have heard of this, but I'll let Daisy introduce herself. This film isn't about getting scammed. This is about getting even. Meet my friend, Daisy. Hello, scammers. I'm your worst nightmare. I'm an AI created by o two to waste phone scammers' time. So w's then a dot. Three times w and then dot. I think your profession is bothering people. Right? I'm just trying to have a little chat. It's nearly been an hour for the love of Gosh. How time flies. It's showing me a picture of my cat, Fluffy. It's showing you the picture of your cat, Fluffy. So you get the idea. And, you know, again, just to have somebody like Daisy answering scam calls is a big victory. And the reason why the cell phone company wanted to do this is actually not only is to showing off the technology, but they have a load of phone numbers which are genuinely not connected to real people. So if they can divert the calls to Daisy in this case, they will actually make the revenue from those calls. And they're looking to see, for example, if you get a someone that you know sounds like a scammer, you can forward the call to Daisy and have a little listening to it and kind of amuse yourself that way. So it's kind of a win win. You're you're wasting scammers' time, and the mobile company who are developing this can make a little bit of money from it. So always good thing to kinda keep scammers at bay. So I I any more thoughts on AI, John? Well, one of the wildest things. Right? I know when we're sort of putting robots against robots, putting them together like this, if it ends up wasting scammers' time and I know that's exactly what you're up to in scam baiting and this whole effort. But Daisy and a solution like that, there's a funny line. I know she says, like, look. I've got all the time in the world. I'll I'll just play it up because that's just what she's gonna say. Got it, dear. Because while they're busy talking to me, they can't be scamming you. And let's face it, dear, I've got all the time in the world. That that that just sums up Daisy exactly, and and, yeah, I'm all for that. There used to be something called rescan. In fact, rescan is still around, and that's used for emails. But only emails, you can forward your email to me at rescan dot org if you wanna look that one up. So if you're getting email scams, that's one way, but this is kind of the the voice equivalent of rescan. Well, honestly, Jim, hey. Thank you. Because I know there is a real community, of folks that are kind of willing to go into this effort. And we've been together with a handful of other creators like yourself, Skip or Payback. We've seen, Pleasant Green and Kit Boga. I know he's building his own army of these, robot calls that can help fight back with AI. And it's really inspiring, especially to us because we're wanting to and we're diving in. We're all over AI to go toe to toe with the adversary. You know, we're protecting, like, over ten million identities, over at Huntress, and that's an incredible thing. But I know when I say you or I or scammer payback or Kipburger or members of the community, hey. That's awesome. But it also can't scale between just the one person. Having this extra automation, having together supplementing human and AI in the agentic world is is pretty cool to bring this all together. With that, I think we've got a little extra fireworks that we might be able to showcase if you are willing to keep hanging out with us for a little bit past the hour. I know we have, Jim, I don't know if you'll believe it, like, three dozen questions in our q and a pool. It will be a lot to talk about. Oh, that's good. Yeah. For folks that are willing to hang after the hour with us, we'll absolutely dive into some of those. But, we can pull up my slides again real quick. I do wanna get us to the end, clean this thing up to fit all in for the top of the hour. Let's celebrate that sweet giveaway and the big winner. I don't know if you caught it. Maybe a little bit of a secret, but when we popped up that poll, we wanted to see, hey. Who is willing to jump in and be part of the conversation right away? So, hey, today's winner is Adon l or Adon l. First name, a d o n, last name with a initial of l. We'll be reaching out, after the webinar to get shipping details situated, but thank you so, so much. Thank you all for being here. And I do wanna let you know, Declassified. Right? That was a cool new fun series and series premiere that I'm so thankful that you all joined us here for. Look. We wanted to talk about your hidden competition, and I think we're keeping the party going now with maybe some self fails. But Truman Truman Kane, our principal product researcher, will be showcasing that. Coming up next, the second segment episode two of Declassified on May twentieth, and the title, your breach is on the calendar. So big props. I hope you tune in for that. I think we've got some more polls running around to let you learn a little bit more about Huntress and see how we could join in the fight. But, Jim, can I ask you again? I I'd love to just get your honest take. We reached out. We wanted to spend some time with you for this incredible show together, but what do you why were you willing to do this thing? Why why Huntress? Can I ask you? Well, I mean, obviously, the the massive massive pay for it. No. Only joking. No. We're we're in this it's a common fight, and that is the real reason. My YouTube channel is all about education. And, honestly, for me, being an engineer and listening to fellow engineers, I'm guessing a lot of people who are on this call are also, you know, tech guys, IT guys, girls. I find scams, scammers, and digging into this sort of material fascinating, and I think that's probably the reason why a lot of people are here. Understanding your opposition, you know, going toe to toe against the people who are trying to decimate your business, who are trying to attack you, is always going to be interesting. Unpicking them, I always find fascinating. I hate to say this. Have a sneaking admiration sometimes for people who run those scams because you could be doing a normal job, but instead, you think you're competent enough to steal money effectively from other people. And that mindset fascinates me, and that is part of the reason why I got into this. I can't understand why you can't use the Internet for good. But if there are people out there who are prepared to attack you, attack your systems, your business, the best way of defending yourself is to understand how they do this, who they are, and how they work. And if you understand all of that, you're far better able to protect yourself. And that's exactly why there's so much overlap between what you do, what I do, what Huntress does. And I think just to have this as a as a team effort, if you like, to say, this is what really happens in the real world. It's always a good thing to do. So, yes, it was just the short answer is overlap. And thank you. Thank you for helping to shine the spotlight really on what we consider, you know, that your your hidden competition, and it's a whole attacker business model. I'm hoping this is still stuff that you could bring into, I don't know, board meetings, budget conversations, like, knowing what the threats really are that are out there. And we don't mean to bring this to you all as, like, a fear by any means. That that's not that's not the goal. It was constructive urgency. We want you to know what you're up against, and I hope you've been able to get some extra insight on that with all of the things that we got to see today. So, hey, please don't just hang out in the chat. We do wanna let you, hey. Join the party. There were some sweet Huntress demo things if anyone wanted to learn a little bit more out and about. But I think we are at the top of the hour, Jim. I know we wanted the main course, the entree for our show to be tight and cutting it in there. But with, holy cow, forty five questions now in our q and a, would you like for us to Yeah. Show any more of your visuals, show any more of your bonus content, or should we dive into questions, or what's the plan? Mean, I'm I'm happy to do I have, like we were together in a room last year. I do have a little bit of video where we kind of collaborate a little bit on that. But, honestly, I think given that there's so many questions, I think we'll maybe dive into the questions. I will try and answer them. If we run out of time or people get a little bored of what we're talking about, then I can show them a little live demo or live demo from last year at least and have a bit of fun at a scammer's expense. Any questions that stick out to you in your mind already? I'm just scrolling through them here. I noticed Daniel Rock is saying we he needs my biometrics to prove I'm the real Jim Brown. I'm hoping my voice will do it, and I'm able to hold up the three fingers as well even though I'm in disguise. So hopefully, that covers that one. I'm just scrolling back through these. Right. Interesting thought. I I see one of them from Kevin Walker. Interest in Jim's thoughts on Mohammed Mazir Red Bull on people being forced to work in scam call centers. This particular one and I know that you have your interest has dug quite deeply into quite a number of what they term pig butchering scams or pig butchering is a term just used for a cross between both a romance scam and an investment scam. And, sadly, the a lot of the people who are involved in those scams are human trafficked. They are literally sleeves to the scam call centers. And what are my thoughts on it? Well, my thoughts are this is an absolute disgrace. The people who are being forced to work there are being forced into this. So there is no way that I can directly blame the people who are trafficked to do this. I have personally been involved in closing down some of those scam call centers in or the one there was one two years ago now in Dubai. Now that happily, most of the people over there weren't human traffic, but they were taken advantage of, shall we say. And I worked with the police in Dubai to help bring that down. So what do I think of it? They're a disgrace, and I would love to do more on them. But they're notoriously difficult to shut down because they're literally in war zones. So, yes, I'll still try and do my my bet from that too. Don't know. Any thoughts from yourself, John, on this? Or No. We had a webinar previously, a time with Red Bull that was just Yep. Moving, kind of the gravity of the situation. It was with Andy Greenberg. It was with Jen Easterly and Kyle Hansloven, right, CEO over at Huntress. But I I can't say any more than that they already have that. Please do tune in to the recording or check that out because there's so much there. But I would not do it justice. The it is a certain thing to see for yourself. Yeah. Yep. I've got another one. A lot of scams call center videos when you guys get in and break their stuff. There are other scam beaters who do actually break their stuff. I tend not to because what I try to do is actually get the police, the authorities involved, and get them raided. And it is far better to have an intact scamming PC sitting there as evidence than it is for someone to go in and destroy it. Now that said, sometimes the authorities are not interested at all. And, possibly, I can see justification in destroying PC if I thought that it would do a good personally, I don't do that for that reason that I am hoping the police will turn up. It's far more valuable if it's intact. I don't know if there's any any questions which jump out at you there, John, as well. There was a silly one. Hey. How often are you recognized by scammers or groups before you are too often in the mix? Thankfully, because of this, it's only my voice. But believe it or not, there are people who recognize me just from my voice. And I do have a it's kind of hidden away here, but I have a voice changer. When I talk to a lot of scammers, I'll sound like an old lady for that very reason. Downside with a big YouTube channel is you do get recognized if only for your voice. Would you be willing if you wanted to pull up any of the extra extra bonus content? And again, huge thanks to everyone still hanging out with us. I know this is, after show. We're letting our hair down, But if we've got some more fun, let's do it. We do. Let me just reshare. I will and I can give a little bit of background context while you're pulling it up if that's a okay. Yep. Yep. Hopefully, you can see this one. Jim and I and I am just so grateful. They let me kinda join the party, really just fly under their wing because they're doing the incredible work. But there have been some get together events, things like the people's call center, to be able to get all the great minds together to do some of this work to disrupt scams, to, stop and put a dent in their operations. But I I wanna be real with you. These are things that are trying to be preventive to scams and to save a victim mid scam. So we do a couple silly things. Like, there's some hijinks. There are things that are just intentionally maybe they sound and look goofy to us listening in, but they're very strategic and purposeful to save a victim so that the scam can't continue. But there are incredible people that we collaborate with, and I think you'll see Pleasant Green and some others that Yes. Showcase this in action. Yeah. Let me actually, just before we do that, let me show you the actual tool he's about to use. So yeah. I think that's safe. Let me just do that. And that this is the actual tool that he will use. Okay? And it has got a few functions at the top here. And one of them is the word listen. So I can listen in to individual calls. And when I do that, I can change the, basically, the pitch of the voice of the scammer, not the victim, but the scammer. And I can change them into a chipmunk, baby chipmunk, and so on. But equally, I can also mute the agent or mute the customer, and that is actually a very effective tool. Well, both that and the chipmunk. But you're about to see this tool being used live by our friend, the scammer well, no, Ben from Pleasant Green. And this happened when we were all together in last year's people's call center. So John and I were there and a few other well known scam bidders. So You might be able to see me cheesing in the background, but I had fun playing with the tools just well. You're you're you're there in the background somewhere. But, yeah, this is Ben of Pleasant Green. If you don't know his channel as well, have a look there. And he's using the tool here. Verify your details, and they will help you with the paperwork. I would request you, please do cooperate with the verifiers. The verifier might ask you the same question. Please do cooperate with them. You you you get the idea anyway. I mean, I could I could play this free. Just it it never gets old. Oh, did just hang up? But but that's the whole thing about it is as soon as you change their voice, not only can they not be understood, but they think it's a prank at that point, and most people hang up. So it's a very, very effective way of getting a scammer to to hang up without being obvious. And, you know, if we tore down the call, which in theory we can do, then, you know, they're gonna know something's up and things change. If you make them squeaky without them realizing, of of course, it's going to be really effective. So the the whole load of those, you can have a bit of fun at a scammer's expense. There's nothing quite making them sound like a chipmunk though to have a bit of a laugh. I I I enjoy doing that, and I know John, I think I think last year, it was it was good fun to be able to do that too. My favorite is when you turn the pitch down and they sound like a spooky, like, super low tone demon, and it does just Wait. Wait. We actually have one of those. I I think this one has a little bit of that as well. You. This is this time. Let me see if I can get one here. That's still that's baby chipmunk and there's baby chipmunk. Let me see if I have it. Yeah. Back to human. No. Maybe I haven't got that one. But, yes, as you say, we can alter the pitch, and you can make them sound like a demon or worse. I'm just as happy tell you. Always good for a laugh, but, yes, that that's exactly how we do it. And thanks to the author of this. This is when we got together. The person who wrote this little tool was actually there with us and was developing the tool as we were there. So many thanks to the author. I'll I'll not name the author, but, yeah, I will say it was good fun to use it. Well, Jim, I know we're about maybe ten minutes or so past the hour. Any other questions that are coming through that you tend to see that look really good? I know a lot of folks might be asking to learn a little bit more about your tricks of the trade. I know how not everything that we could particularly say or talk about, but even some of the more defensive things of, hey. How do you identify this? What's the telltale on the call? What's the indicator that, hey. This could be a scam. And for the folks that are still with us, I really wanna drive the point home. I I think sometimes, you know, we might think, look. This is something that affects an end user or an individual, but it bubbles up. It it boils to a business, an organization because think of, even just, oh, hey. Getting something done on your work computer. Maybe you got a shared device. Maybe some things just intermix and bleed together for business and, individual, and business email compromise is still something that opens the door for a much wider blast radius. You understand? So Yeah. Yep. So yes. And I'd just like to thank you, and I know there's loads and loads of questions in there. I know I can't possibly get through all of we've now gone up to sixty. Yeah. Yeah. I'm just having a look here to see if there's anything. I'm yeah. Again, I appreciate everybody who actually tunes in to this sort of webinar because it's good to spread the word, and you guys who are in the webinar are equally responsible, whether it's for yourself or for your organization or for your family and friends. It's just good to talk about these things. So, you know, mention this to other people. I think the webinar will be available online, I think, as well, John. Is that correct? Yes. We'll be sharing the recording and all for everyone. So we'd absolutely wanna make sure this can be well known for what we got to see here. Thank you. Yeah. Yep. Okay. Thank you very much. Well, thank you again again, everybody. I won't keep yapping for the sake of, oh, ad nauseam talk, but this has been a real treat. I hope you tune in to Declassified episode two next time around, but thank you. Thank you all.
We all have those tasks we mean to get to later. But in cybersecurity, “later” can cost you.
On May 20, join Truman Kain and a special guest for a live conversation and demo on how overlooked obligations, delayed fixes, and ignored warning signs can quickly spiral into real trouble.
May 20, 2026 | 12:00pm ET | 4:00pm GMT
60 minutes
The Breach Is On Your Calendar


A side-by-side look at the business processes and technologies used by both legitimate organizations and their cybercriminal counterparts
Insights into how threat actors organize, communicate, and execute attacks using the same business tools you use
Actionable strategies to anticipate, spot, and defend against adversaries who think and operate like your own team
A fresh take on the threat landscape—one that treats cybercriminals not just as faceless hackers, but as sophisticated competitors vying for the same resources and opportunities.
Speakers

John Hammond
Senior Principal Security Researcher
John Hammond is a cybersecurity researcher, educator and content creator. As part of the Adversary Tactics team at Huntress, John spends his days making hackers earn their access and helping tell the story. Previously, as a Department of Defense Cyber Training Academy instructor, he taught the Cyber Threat Emulation course, educating both civilian and military members on offensive Python, PowerShell, other scripting languages and the adversarial mindset. He has developed training material and information security challenges for events such as PicoCTF and competitions at DEFCON US.

Jim Browning
Software Engineer and YouTuber
Jim Browning is the Internet alias of a software engineer and YouTuber from Northern Ireland whose content focuses on scam baiting and investigating call centres engaging in fraudulent activities. His YouTube channel has over 4 million subscribers and his videos have been viewed more than 300 million times. He is part of the BBC's 'Scam Interceptors' team who attempt to stop UK-focused scams on their BAFTA award-winning TV programme.
SPEAKERS
Truman Kain
Truman Kain has worked for years as a social engineer conducting phishing, vishing and physical penetration tests against the Fortune 500. He has also developed and presented novel security tooling at DEFCON, GrrCON, SaintCon and Devoxx. His previous experience spans software development and more traditional forms of penetration testing. Truman holds OSCP and CESE (formerly SEPP) certifications. He also creates content on social media covering cybersecurity tips, tricks and threats (@trumancyber). At Huntress, he is a Principal Researcher for Security Awareness Training.


Don’t wait for "later"
Register now to see how small security gaps can turn into big problems, and what you can do to help stop them.