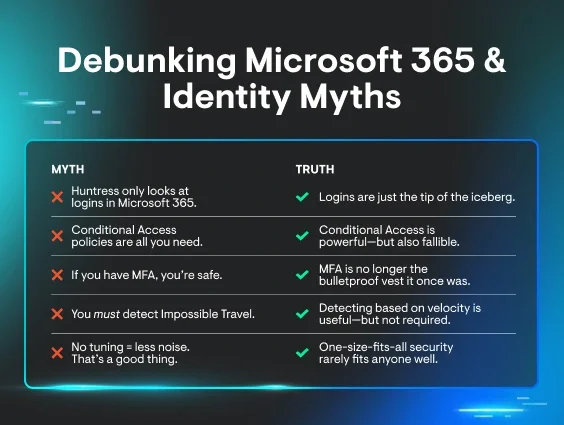
If you think your Microsoft 365 setup is secure, you’re probably betting on cybercriminals breaking in through locked doors. But what if they're strolling through the front entrance like legitimate users (and trust us, they are) with stolen credentials and bypassing your MFA? No warning signs. No red flags.
Is your defense strategy ready?
Learn to spot these attacks before they go HAM, in a Microsoft 365 live hacking demo on November 13.
Here’s your sneak peek
Huntress CEO, Kyle Hanslovan—a former NSA operator and legendary ethical hacker—will host a live hacking demo that takes you behind the scenes of today’s modern cyberattack techniques. This isn't another fluffy PowerPoint presentation filled with what-ifs. Kyle will simulate real attacks in real time, showing you exactly how hackers do things like:
-
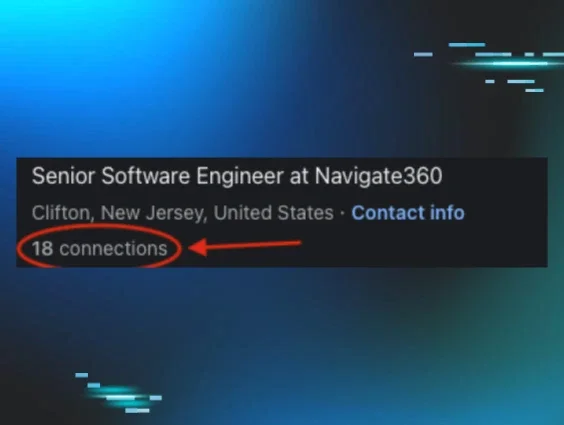
Target employees with sophisticated social engineering tactics
-
Quickly steal credentials directly from Chrome and Edge browsers
-
Bypass Microsoft 365 MFA functionality
-
Rapidly compromise interconnected systems
You'll watch these attacks unfold, understand why they work, and learn strategies to shut them down in your environment.
Join us live: No FOMO, just awesome freebies
Come hang out with us live. You’ll get free access to:
-
Identity Security Assessment for Microsoft 365: Uncover hidden vulnerabilities in your systems with a comprehensive assessment designed to reveal weak spots before hackers find them.
-
Setup instructions for your own live demo: You'll get instructions to recreate Kyle's demo and deliver your own live hacking session. Nothing drives home the importance of cybersecurity like seeing an attack happen in real time.
Plus, you'll learn the specific defense strategies that power down each attack tactic Kyle walks you through. No BS advice or generic tips allowed—just actionable steps you can run with right away.
Now’s the time to defend smarter
Remember when your biggest security woes were malicious macros in Word documents that logged your keystrokes and lurked through your webcam? Well, that was way back in 2020, and those days are long gone. Cybercriminals have upgraded their toolkit, and they're using techniques and resources, like AI and credential marketplaces, to exploit the go-to software for businesses everywhere: Microsoft 365.
Your team depends on Microsoft 365 running smoothly for email, file sharing, collaboration—basically all your daily operations. That makes it a massive target for cybercriminals. And when they get in, they don't just steal data. They create new accounts to persist under the radar, make email forwarding rules, impersonate your C-suite execs, redirect payments to their own accounts, drop ransomware, and bring operations to a grinding halt.
The truth is, most businesses don't know where their vulnerabilities are until it's too late. This webinar gives you a front-row seat to see how attackers think and operate, so you can shore up your defenses way before any damage is done.
Mark your calendar, save your spot
Cybersecurity shouldn’t be scary or out of reach. When you understand how attacks work, you can build smarter defenses and protect what matters most.
Come get shady with us, bring all your tough questions, and walk away with a solid plan to challenge modern cybercriminal tradecraft. Register now.