
Watch this video for a breakdown of the ransomware attack path, so you can spot it early, shut it down, and steer clear of hacker paydays.

One exposed server. One stolen password. One minute too late. That’s all it takes for productivity to grind to a halt. Downtime, data loss, and costly ransom payments can ruin everything you’ve worked so hard to build. We find the backdoors your current tools missed and wreck the hacker before encryption begins.
Yes, if you have the right visibility across your network and systems. These days, many initial access broker groups and ransomware gangs rely on weaknesses in security tools like firewalls and VPNs to gain access to a network. But they can’t do it quietly, making it possible to detect attacks through log and event monitoring.
Ransomware groups prey on employees because they can provide an expressway into a network. Employees can be phished to install an attackers' tools or steal administrative passwords making it easy to compromise a network.


Ransomware groups prey on employees because they can provide an expressway into a network. Employees can be phished to install an attackers' tools or steal administrative passwords making it easy to compromise a network.
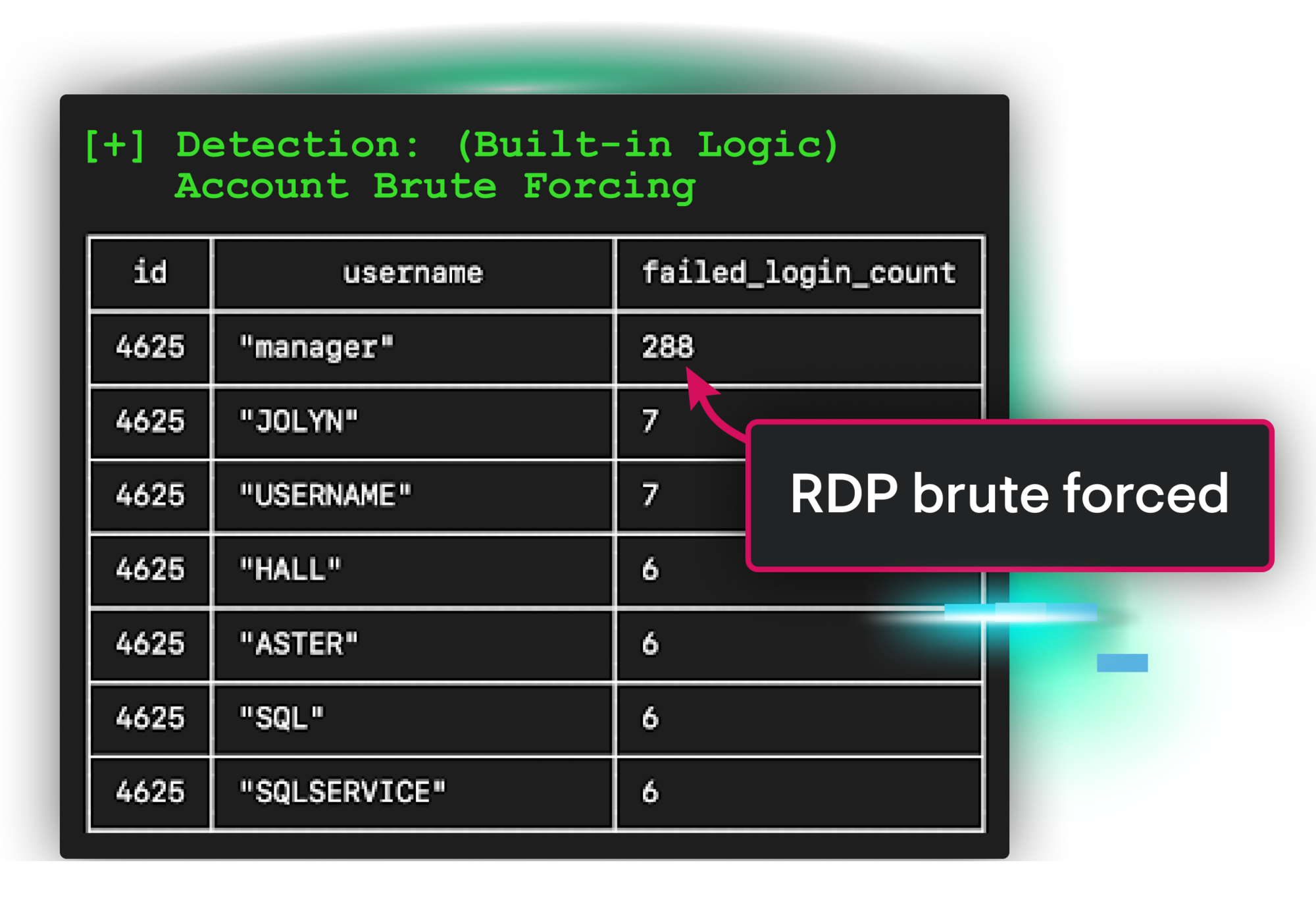
You’re asleep, so you miss what’s just happened—a brute force login. The attacker moves fast. They’re stealing credentials, installing a disguised remote access tool, and hiding persistence under a fake system process.
But Huntress moves faster. Our threat hunters detected the attack, validated it, and acted immediately by:

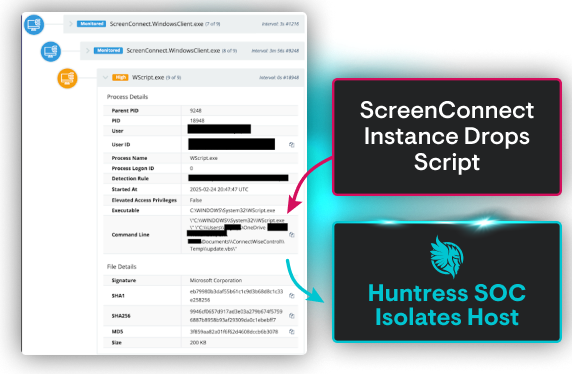
Our SOC—a 24/7 team of elite threat analysts backed by AI—is your always-on force multiplier. We provide the fast, agile response you need to maintain business operations, protect your reputation, and keep your mind at ease.



RAFTRx had expansion down to a science. But their rapid growth meant their tools couldn't keep up. When phishing attacks, suspicious logins, and compromised accounts started causing trouble, their two-person IT team needed backup—like, yesterday.
See how Huntress swapped their growing pains for effortless, scalable protection, helping them onboard seven tenants in just two weeks and putting control firmly back in their hands.


Global threat analyst coverage
Led by a team of elite, industry-recognized threat analysts who’ve seen it all, our 24/7, AI-assisted SOC works around the clock to find and eliminate ransomware threats before they can damage your business.
False positive rate across 4M+ endpoints
Alert fatigue is brutal, and it’ll burn out your most skilled pros. That's why we cut through the noise and surface only the alerts that matter. Let us handle the distractions, so you and your team can focus on what matters most.
Organizations protected by Huntress
We see millions of attacks each year, and every one of them makes us smarter. These insights constantly evolve our tech and our approach to wrecking hackers. The result is greater efficiency for your team and herd immunity across our customers.












Huntress Managed EDR doesn't just watch your endpoints—it’s a complete solution. From the second a threat appears until it’s eliminated, we handle everything. You get 24/7 continuous protection, detection, and response that disrupts and remediates threats.
Identity Threat Detection and Response (ITDR)
Finds and stops identity-based threats in Microsoft 365—because identity is the new endpoint, and attackers know it. Huntress Managed ITDR is designed to detect, respond to, and resolve critical identity-based threats like account takeovers, business email compromise, unauthorized logins, and more.
Huntress Managed SIEM takes away the complexity and overhead usually associated with traditional SIEMs, giving you everything you need and nothing you don’t. 24/7 threat response and strengthened compliance, fully managed by SOC experts, at a predictable price.
Engaging, expert-backed, personalized training content built on real-world threat intelligence and created by Emmy® Award-winning animators to reduce human risk and build a strong security culture.
Most hackers don’t "break in"—they just take advantage of messy settings, bad defaults, and accounts with too much access. Huntress Managed Identity Security Posture Management (ISPM) continuously audits and enforces configurations, policies, and permissions in Microsoft 365 so those easy attack paths are never open in the first place.
Huntress Endpoint Security Posture Management is proactive security that hardens endpoints to defend against attacks like ransomware and infostealers, and prevent breaches. Get broad endpoint visibility and control over configurations, applications, vulnerabilities, and more in one location and a single solution.
2025 World’s 50 Most Innovative Companies
Top 25 CRN Technology Disrupters
2025 Best SIEM Solution SC Awards Europe






Protecting against ransomware requires a defense in depth approach due to the multiple approaches threat actors use to gain access to your systems and data. Endpoint detection and response is no longer the single solution. Businesses need to be educating their employees to detect and avoid phishing and credential theft attacks, and secure password practices. You need visibility into pre-attack activities by threat actors targeting your IT infrastructure, and monitoring for identity and credential theft in the event the “human firewall” is compromised.
Speed matters when responding to a ransomware attack. The faster an attack is detected and the threat is contained, whether that’s shutting down VPN access or isolating an endpoint, the greater likelihood your business will minimize the impact of a ransomware attack.
Current trends in ransomware protection are to ensure protections are in place to counter the range of ransomware attacker tradecraft - phishing users for access to their systems and accounts, abusing vulnerabilities in systems to gain access to networks, gaining access to endpoints and moving laterally around a network. And being able to quickly recover from an incident with documented and tested incident response procedures along with a robust and secure data backup strategy.
AI is helping IT and Security teams defend against ransomware attacks by allowing them to triage and prioritize alerts faster, letting them move at the speed ransomware attacks are happening.
Antivirus is based on known file signatures and often fails against modern, fileless attacks. Huntress Managed EDR looks for the tradecraft of the human attacker—how they move, escalate privileges, and execute commands—after they bypass basic defenses. Our human-led SOC is dedicated to threat hunting for these subtle activities, ensuring a response that generic preventative tools simply cannot deliver. We stop the human attacker before they can deploy the automated ransomware payload.
Our focus is on speed and quality. For example, Huntress Managed SIEM provides broad-visibility across your security controls and IT infrastructure to detect signs of threat actor activity before they can compromise your network. The human-led, AI-assisted SOC ensures verified, actionable alerts are delivered within minutes with the specific context and steps needed to defend against an attack. Unlike solutions that leave you to investigate a flood of alerts, we provide a definitive path to eject the attacker immediately, dramatically reducing the window of opportunity for the ransomware to execute.
Backups are crucial for recovery, but they don't prevent downtime, reputational damage, or the increasing risk of data exfiltration (where attackers steal data before encrypting it). Modern ransomware is a two-step attack: steal data, then encrypt. Huntress helps stop the attacker before they can execute either step, saving you the massive cost, time, and reputational hit of a full recovery process. Prevention is always cheaper than recovery.
Ransomware groups prey on employees because they can provide an expressway into a network. Employees can be phished to install an attackers' tools or steal administrative passwords making it easy to compromise a network.
Definitely. Identities are the new perimeter. Ransomware groups will intercept MFA requests, steal session tokens, and ultimately compromise accounts to get access to your systems and data.


Our platform combines a suite of powerful managed detection and response tools for endpoints and Microsoft 365 identities, science-backed security awareness training, Managed SIEM, and the expertise of our 24/7 Security Operations Center (SOC).