How It Works
Keep Your Educational Institution Protected from Catastrophic Cyberattacks
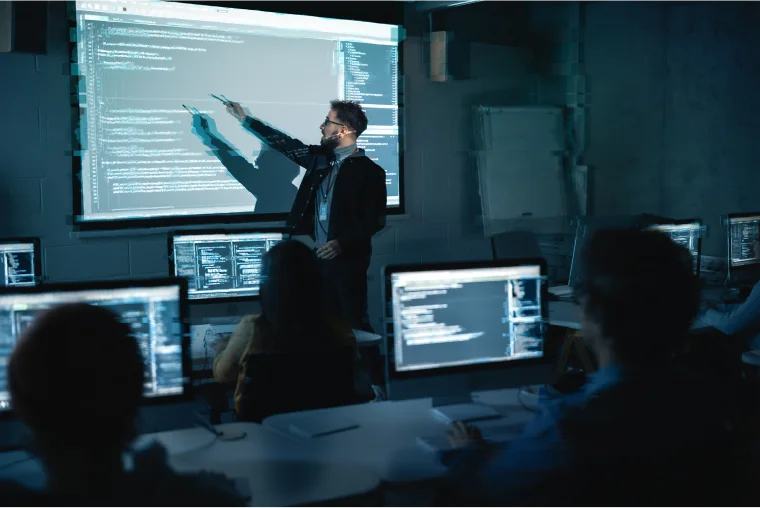
Cyberattacks don’t just happen to businesses—practically every sector is a potential target, and the education realm is no different. Daily cyber threats are the new reality for all educational establishments, with threats like ransomware, malware, and phishing attempts putting your crucial data and operations at risk.
For example, ransomware can make its way into critical systems and networks with devastating results. Lost learning time, hefty ransom payments, and leaking of private data are just a few of the consequences a successful ransomware attack can wreak on schools, districts, and universities.
Huntress monitors your systems in real time with a dedicated team of 24/7 security experts that address potential threats as they occur; we provide proactive remediation and instant alerts to any situations that need your attention.

Featured Case Study
Homer Community Consolidated School District 33C
When a public school district needed to meet new cyber insurance requirements, they had to find a solution that wouldn't take time or budget away from students. See how their small IT team used Huntress to get 24/7 coverage across endpoints, speed up remediation, and build a stronger security culture.



Helping to Keep Education Safe
Huntress is custom built for you. But don’t take our word for it – hear directly from businesses like yours.
79%
3 weeks
500,000+
$9B+



Why hackers target educational institutions?
Educational institutions have been a favorite target for hackers since the first days of cross-campus networks. These threats show no signs of slowing down.
Unfortunately, it’s not uncommon for educational institutions to have limited budgets and resources allocated to in-house cybersecurity measures. This often makes them softer targets—especially when compared to large businesses and corporations—because they tend to have weaker defenses and outdated systems that are much easier to exploit.
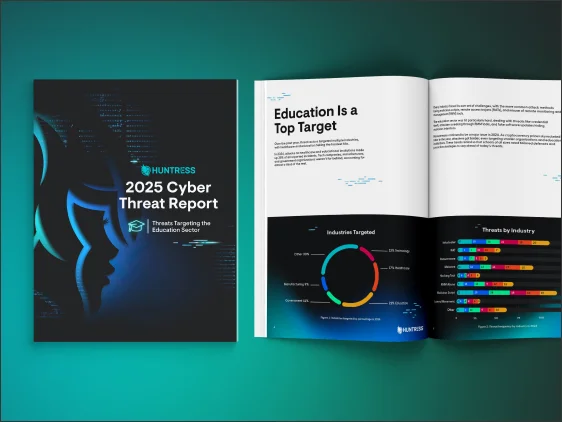
2025 Cyber Threat Report for Education
In 2024, more than 20% of all incidents Huntress tracked hit the education sector, revealing that attackers are more than willing to put students, faculty, and your institution at risk.
But you can stay ahead of the learning curve with Huntress' 2025 Cyber Threat Report: Threats Targeting the Education Sector.
Huntress Solutions for the Education Sector
How Huntress can help the education sector
Let Huntress Managed EDR take on the burden of cybersecurity in education. Our dedicated Security Operations Center constantly monitors your network environment and systems for malicious activity with 24/7 detection and response. If anything suspicious is detected, our team will investigate, contain, and eliminate the threat, followed by a guided cleanup and recovery process, if needed. Bolster your defense even further by taking advantage of our engaging Security Awareness Training that teaches staff, administration, and students to identify and report cyber threats as they occur, preventing potential attacks before they even have a chance to get off the ground.
FAQs
First, schools and colleges have a lot of valuable info like student records and financial data that hackers want to get their hands on. Plus, many educational institutions don't have the newest tech or enough resources to protect against cyber threats, which makes them easier targets. Also, with so many devices and open access for students and staff, it's tough to keep everything secure. Ransomware attacks can hit schools hard financially and disrupt their day-to-day operations, so cybercriminals see them as a way to make money fast.
The main cyber threats to schools and districts include ransomware, phishing, and social engineering. Phishing is especially common in education, targeting both students and faculty. It involves deceptive emails or messages that prompt recipients to click a link or share sensitive information under false pretenses. For example, attackers might impersonate school leadership, urging users to click a link and log in to resolve an issue or claim a reward, leading them to a fake website that steals their login credentials so they can then launch a ransomware attack or sell their access on the dark web.
Teachers face cyber risks primarily through phishing and weak passwords. They may lack awareness of current threats and best practices, making them targets for ransomware and data breaches. For instance, if teachers are not cautious about opening attachments or clicking on links in emails, they could inadvertently trigger a ransomware infection.





Protect What Matters