Hackers don’t need elite exploits to break in anymore. Instead, they shop on the dark web for stolen identities and abuse the built-in functionality of the legitimate tools and platforms you rely on every day, like Microsoft 365. By stringing together a series of simple, overlooked features, attackers bypass security measures and gain full access to your environment.
In our recent webinar, “Live Hacking into Microsoft 365” (on demand here), Huntress CEO and former NSA hacker Kyle Hanslovan walks through the steps a modern cybercriminal takes, from purchasing stolen credentials on the dark web to completely hijacking a Microsoft 365 account and moving laterally across an organization.
Our goal is to show you, not tell you what hackers are capable of, so you’re better prepared to defend your organization against these real-world threats.
Come join us in the fight against #ShadyHacks.
The modern hacker’s playbook
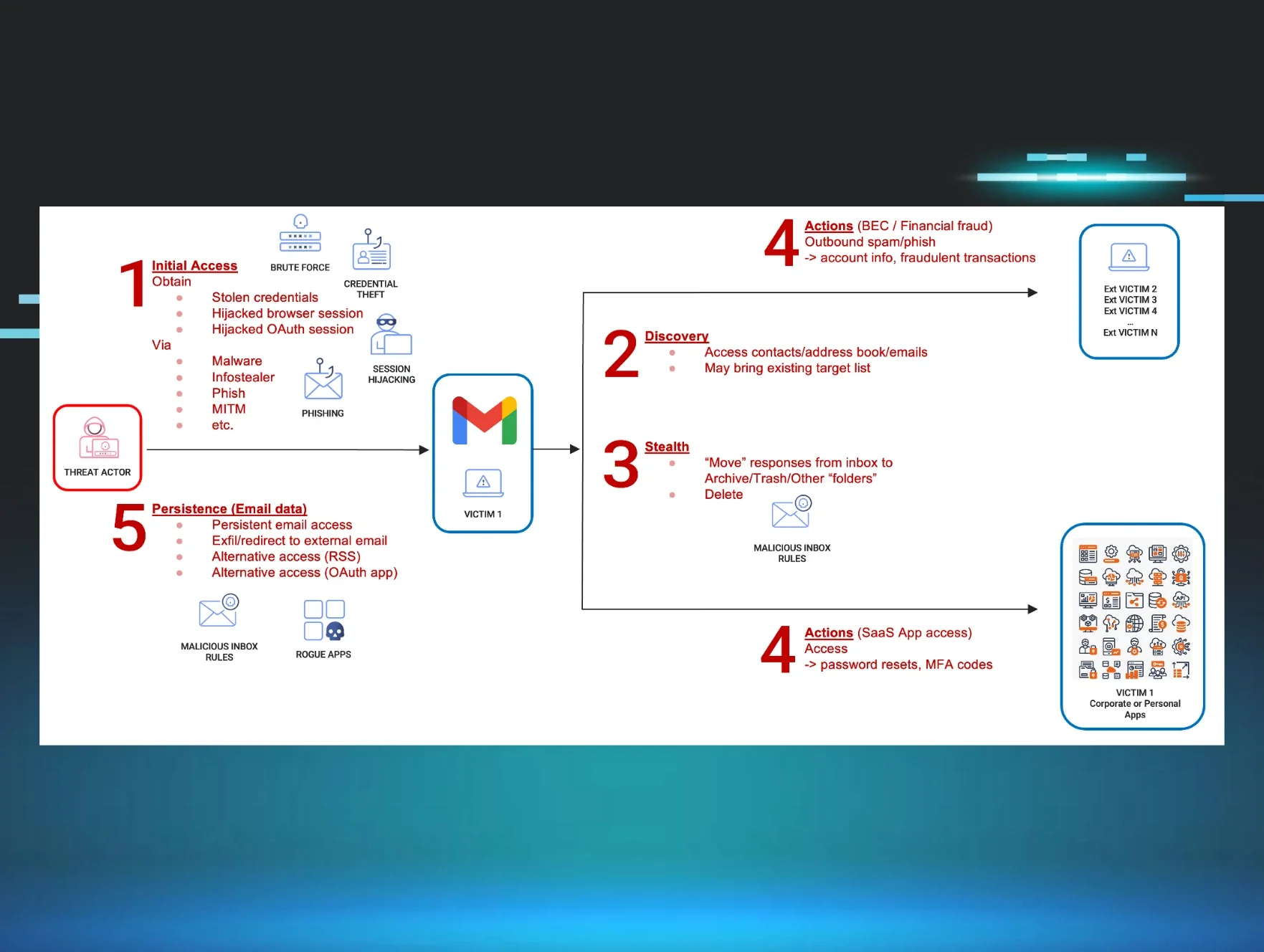
For many years, hacking was all about compromised endpoints: think laptops, servers, and workstations. Today, identity abuse is happening on a massive scale. In fact, our recent data shows three times the number of “high” and “critical” incidents for identities compared to endpoints. If a hacker can log into your Microsoft 365 or Google Workspace account, they can potentially move laterally and gain access to everything you're connected to.
Let’s walk through the steps these malicious actors take.
Step one: Getting credentials on the dark web
The attack often starts on a dark web marketplace. Cybercrime has become a full-fledged black market economy, where credentials for services like Microsoft 365 are bought and sold. For only a few dollars, attackers can buy usernames and passwords, often stolen from phishing campaigns, browser data dumps, or previous data breaches. These illicit marketplaces are surprisingly streamlined and professional, with features like user reviews, customer support, and even refund policies.
Kyle kicks off the #ShadyHacks demo with fictitious stolen law firm credentials of "Grady A.," from a dark web marketplace called Russian Market. These credentials are new, which is important for attackers, as security products are getting smarter at detecting and invalidating previously compromised passwords.
Step two: Bypassing multi-factor authentication (MFA)
With a valid username and password, the first roadblock attackers usually encounter is MFA. While MFA is a critical defense layer, it’s important for defenders to understand how some attackers get around it.
In the demo, Kyle tries to log in as Grady with the stolen username and password, but an MFA prompt temporarily blocks his attack path. He realizes stolen tokens are needed to keep hacking.
In less than five minutes (and with minimal effort),Kyle pulls together a social engineering email with a ChatGPT prompt about updated company holiday policies. It checks all the boxes for a successful phishing attempt: looks legit, has a sense of urgency, and includes a link that seems to be a corporate SharePoint site, but actually redirects Grady to an attacker-controlled infrastructure designed to steal session tokens.
These tokens are what keep you logged in to websites. But in the hands of an attacker, they can impersonate you without needing your password or MFA device.
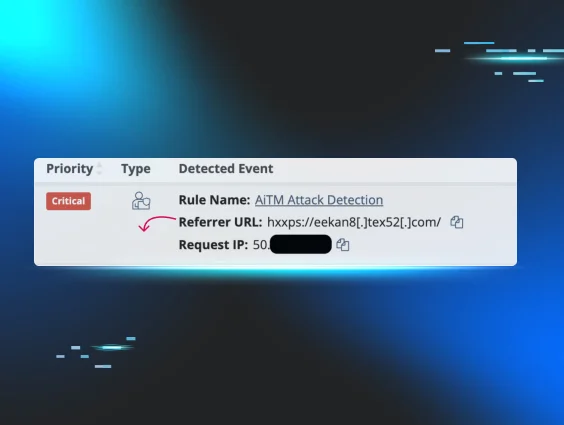
Step three: Stealing session tokens with ClickFix
When Grady clicks the link in the phishing email, he’s taken to a fake login page and prompted with a CAPTCHA challenge instead of his password. We’ve all seen these, right? You check the box to verify that you’re a human, not a robot.
But what about this attack path scenario using CAPTCHA:
-
The user clicks the button to confirm they’re “not a robot.”
-
It copies a malicious PowerShell command to their clipboard.
-
The page instructs them to do something like:
-
Open the "Run" dialog (Windows key + R)
-
Paste the command (Ctrl + V)
-
Hit Enter to complete the "verification."
This technique is known as ClickFix, and it’s a serious red flag for cyberattacks.
Unfortunately, Grady doesn’t know how to spot this warning sign (yet), so he runs the command as prompted. It executes an infostealer script that steals all active session cookies from his browser and sends them to the attacker.
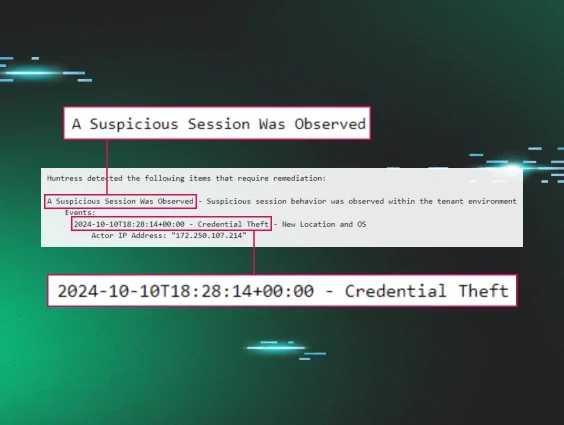
Step four: Session hijacking and gaining access
With the stolen session tokens, Kyle uses a free browser extension called Cookie Editor to import them into his browser. After quickly refreshing the Microsoft 365 login page, he’s got full access to Grady’s account, bypassing MFA completely. #ShadyGrady has entered the chat 😎
This technique, known as token impersonation or session hijacking, is wildly effective for hackers. Logged in as Grady, the attacker can see his emails, access his files, and use any application connected to his Microsoft 365 identity. No exploits. No malware. No zero-days.
Grady is totally unaware that anything has happened, and as far as he knows, he successfully viewed the new company holiday policy.
The mayhem after the breach
Once inside an account, a hacker has endless opportunities. The initial access is just the beginning. The real damage comes from what they do next. Here are some of the most common—and devastating—actions we see attackers take in our customers’ and partners’ environments.
Creating malicious inbox rules
One of the first things hackers do is set up inbox rules to maintain control and hide in the noise. They often create rules with inconspicuous names, like a single period ("."). These rules can be configured to:
-
Forward sensitive emails: Any email containing keywords like "invoice," "password reset," "confidential," or "wire transfer" is automatically forwarded to the attacker's own email address.
-
Move emails to hidden folders: To avoid alerting the user, emails are moved to rarely viewed folders, like RSS Feeds or Junk. The attacker can then log in later to collect the data.
Lateral movement and social engineering
With account access, attackers move laterally. A common tactic is using Microsoft Teams and social engineering to message IT support, claiming their phone was lost or damaged, and asking to register a new device for MFA. Because the request comes from the legitimate user's Teams account, it's trusted.
Resetting passwords for other applications
Many critical business applications don't support single sign-on (SSO). Instead, they rely on email-based password resets. So an attacker with inbox access can simply request a password reset for things like your payroll software, CRM, or legal case management system. By creating an inbox rule to immediately forward and delete the reset email, they gain access to these systems completely under the radar.
Imagine if an attacker stopped your company from running payroll for two pay periods in a row. Or blocked your ability to bill clients or schedule logistics. That’s how modern cybercriminals bring a business to its knees. The scary reality is that it’s not always about ransomware anymore.
How to defend against these attacks
Protecting your organization from modern cyber threats requires a multi-layered approach that combines technology, process, and education.
On the technical side
-
Enforce MFA, but don't stop there: MFA is essential, but as you've seen, it can be bypassed. Still, it's a critical barrier that will stop less sophisticated attackers.
-
Use conditional access policies: Configure conditional access policies if you have Microsoft licensing, like Business Premium or E3/E5. Block logins from unwanted locations or enforce stronger authentication for risky sign-ins.
-
Audit for risky apps and inbox rules: Regularly review the applications integrated with your Microsoft 365 environment, and audit for suspicious inbox rules. Attackers can abuse legitimate backup applications to exfiltrate data, so it's important to know what's connected to your tenant.
-
Harden your email security: Set up modern email authentication standards like DMARC, DKIM, and BIMI. These technologies help protect against spoofing and give users a visual indicator that an email is legitimate.
On the human side
-
Process is key: What’s your process when a breach is suspected? How quickly can you revoke a user's session tokens if you detect a suspicious login? A documented and practiced incident response plan is crucial for minimizing the blast radius.
-
Continuous education: Use Managed Security Awareness Training (SAT) that shows users how these attacks work, rather than just telling them. Invest in teaching your employees how to spot suspicious requests that ask them to run commands or perform unusual actions.
Arm yourself with knowledge
The landscape of cyber threats is always changing. Attackers are constantly finding new ways to abuse the tools we rely on every day. While it’s impossible to be 100% secure, understanding attackers’ playbooks is the first step toward building a stronger defense.
These #ShadyHacks tactics aren't theoretical. They're happening every day to businesses everywhere. It's no longer a question of if your organization will be targeted, but when. So take proactive steps to lock down your identities, educate your users, and invest in a multi-layered defense strategy. You’ll minimize your risk and make sure that when an attack does happen, you're ready to respond quickly and confidently. Book a free demo today and see how the Huntress platform can help minimize your cyber risk.