In cybersecurity, we talk about attack vectors like they operate in silos—endpoint threats over here, identity-based attacks over there. But the truth is attackers don’t care about our silos. They care about outcomes: access, persistence, and profit.
And more and more, they’re using identities to get all three.
If you’re a managed service provider (MSP) or a business relying on endpoint protection alone—or worse, trying to stitch together tools that don’t talk to each other—you’re giving attackers the exact visibility gaps they need to move undetected.
It’s time to connect the dots between endpoint and identity because today’s cyberattacks aren’t choosing between the two. They’re using both.
Identity: The new hotness
We all know endpoints are a classic target. Phishing, malware, Remote Desktop Protocol (RDP) exposure: these are bread-and-butter techniques for attackers. And they still work. But what’s new—and growing fast—is the surge in identity-based attacks.
According to our data, 67% of all critical and high-severity incidents Huntress reported in 2024 were identity-related. In the first two months of 2025 alone, that number jumped to 81%.
Why the surge?
Because identity attacks are:
- Low-effort: Phishing or buying credentials on the dark web requires far less skill than building malware.
- High-reward: Stolen credentials offer persistent, privileged access to cloud apps, SaaS platforms, VPNs, and more.
- Hard to detect: Multi-factor authentication (MFA) bypasses, session hijacking, and rogue OAuth apps don’t throw traditional EDR alerts.
Hackers don’t need to break the door down when they can just steal your identity and walk in. And once they have it, they aren’t acting like you. They are you.
So, what is an identity attack?
Think of your digital identity as more than a username and password. It’s your entire digital fingerprint: credentials, tokens, MFA, permissions, session cookies, behaviors, and cloud-access patterns.
Identity attacks typically follow a three-phase structure:
- Credential theft or compromise
-
Via phishing, adversary-in-the-middle (AiTM) attacks, or dark web purchases.
-
Common tools include spoofed login pages, session hijackers, or password spray attacks.
-
Credentials sell for as little as $10 on dark web marketplaces.
-
- Privilege escalation and lateral movement
-
Once inside, attackers move laterally, abuse single sign-on (SSO), or hijack OAuth tokens.
-
They may use stolen session cookies from browsers like Chrome or Edge to bypass MFA.
- Persistence and evasion
-
Attackers create inbox rules, change MFA devices, or install rogue apps to maintain access.
-
Once embedded, they can exfiltrate data or deploy ransomware, all without raising alarms.
Endpoint-to-identity and identity-to-endpoint pivots
Today’s attacks don’t stick to one surface. They pivot between endpoints and identities based on opportunity and defense gaps. Let’s walk through two common pivot paths.
1. Endpoint → Identity
Step 1: Attacker phishes a user or exploits RDP to compromise an endpoint.
Step 2: Dumps credentials from memory using tools like Mimikatz or scrapes session cookies.
Step 3: Uses those credentials to log into cloud services, bypassing endpoint defenses.
Step 4: Abuses identity access to disable security tools, moves laterally, or exfiltrates data.
Endpoint protection may catch the malware in this flow, but it won't stop the attacker from logging into Microsoft 365 and escalating.
2. Identity → Endpoint
Step 1: Attacker steals credentials or buys access on the dark web.
Step 2: Bypasses MFA using AiTM techniques or stolen session tokens.
Step 3: Uses cloud-based admin privileges to push malicious scripts or disable EDR tools.
Step 4: Deploys ransomware, steals data, or establishes persistence on endpoints.
Here, the endpoint compromise is the final stage, not the starting point.
Real-world tradecraft
These pivots aren’t theoretical. They’re happening daily.
Case 1: Healthcare identity breach
A threat actor used a doctor’s forgotten credentials to access a healthcare org’s network. From there, they:
-
Moved laterally across systems
-
Punched holes in local firewalls to expand access
-
Were moments away from deploying ransomware when Huntress detected and stopped them
The kicker? The doctor had left the practice, but their credentials hadn’t been deactivated.
How the attack was detected
Case 2: Adversary-in-the-middle attack
-
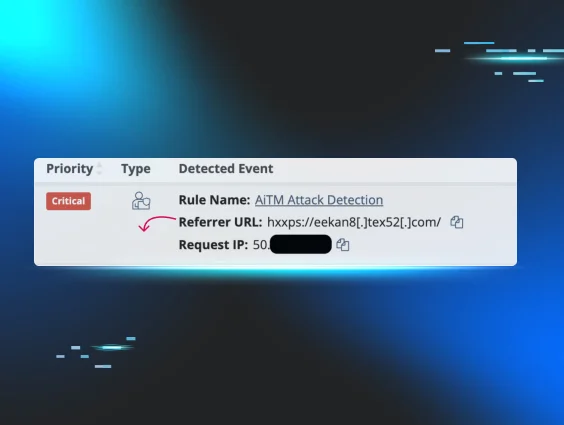
An oil & gas firm narrowly avoided compromise when an attacker spoofed a Microsoft login page. A user entered their credentials, and the attacker tried to “replay” the session to access the mailbox.
-
Huntress detected it in real time, disabled the identity, and notified the partner before damage was done.
Example of Managed ITDR detecting an AiTM attack
Case 3: Rogue OAuth app
-
At a school district, a suspicious app named “XXX” was found with high-level permissions. It wasn’t malware—it was stealthware (rare, unknown apps used by attackers to create backdoors).
-
Huntress flagged the app, removed it, and walked the admin through restoring identity hygiene.
Huntress SOC provides step-by-step remediation after an identity attack
The cost of siloed security
If you’re only using EDR:
✅ You’ll detect malware and suspicious processes.
❌ But you’ll miss stolen credentials, MFA bypasses, or rogue apps flying under the radar
If you’re only using identity protection:
✅ You’ll catch login anomalies, OAuth abuse, and session hijacks.
❌ But you’ll miss credential dumping, script execution, and persistent malware on endpoints.
Security teams need both sides of the coin because attackers are operating across both planes.
Why Huntress: Managed EDR + ITDR
Huntress gives you fully managed EDR and Identity Threat Detection and Response (ITDR)—built together, operated together, and powered by the same elite 24/7 Security Operations Center (SOC).
- EDR: Detects malware, persistent footholds, credential dumping, and ransomware signals.
- ITDR: Flags suspicious logins, account takeovers, rogue OAuth apps, and MFA abuse.
- SOC: 100+ expert humans (not bots) who investigate, respond, and remediate threats on your behalf.
Every alert is validated by a human, enriched with context, and actionable. No noise. Just results.
And yes, we manage Microsoft Defender too, at no extra charge.
Try Managed ITDR
If you’re already using Huntress Managed EDR, you’re halfway protected. But without Managed ITDR, identity-based threats are flying under the radar.
Take a free trial of Managed ITDR and gain:
- 24/7 identity monitoring by real security analysts
- Detection of rogue apps, credential theft, MFA bypasses, and session hijacking
- Actionable, human-verified alerts
- Full access to the Huntress SOC for the duration of the trial
Today, 75% of organizations that deploy to 200+ identities catch an incident during the trial.
Deploying to a single tenant takes two minutes. There’s no commitment, no fluff, just clear visibility into the identity threats already targeting your business.
🎯 Start your free trial now and let us show you what attackers hope you’ll never find.