What used to be simple invoice fraud and credential phishing has evolved into multi-stage identity abuse campaigns that exploit cloud authentication protocols, SaaS trust relationships, and native Workspace features, often without triggering traditional security alerts.
If your organization still treats BEC as “just an email problem,” you’re already behind.
The new BEC playbook
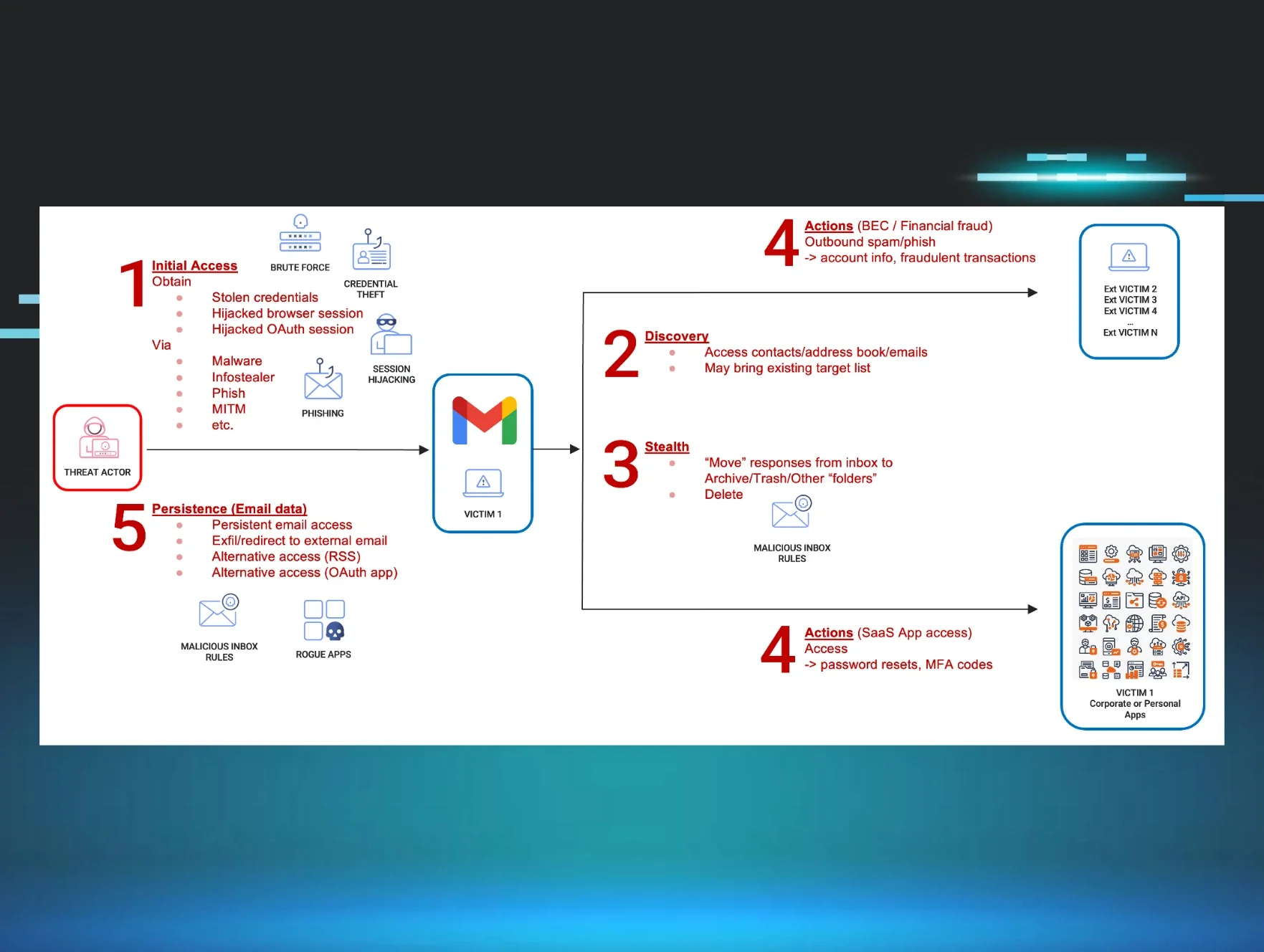
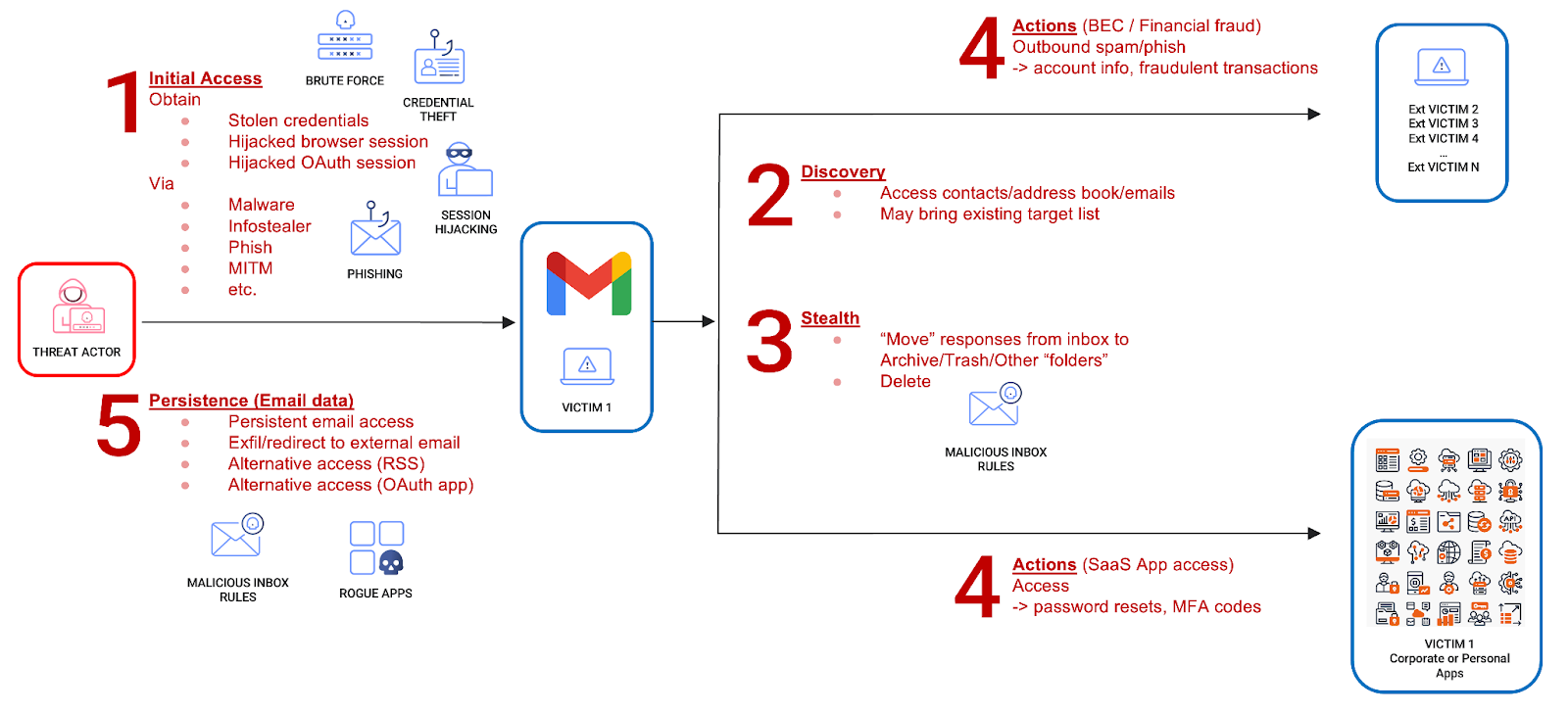
Modern BEC campaigns rarely stop at inbox access. Once attackers gain initial access—through phishing, session hijacking, or OAuth abuse—they immediately begin expanding their foothold.
A typical BEC attack chain now includes:
-
Initial access – Stolen credentials, token theft, OAuth abuse
-
Discovery – Mining email content, contacts, workflows
-
Stealth – Hiding alerts, suppressing replies, inbox manipulation
-
Actions – Fraud, lateral SaaS compromise, phishing expansion
-
Persistence – Forwarding rules, OAuth tokens, alternate access paths
Each stage compounds the damage and makes remediation more difficult.
Gmail as a lateral movement engine
Attackers increasingly use compromised Gmail accounts to pivot into other SaaS platforms by abusing:
-
Password reset emails
-
MFA codes delivered via email
-
OAuth authorization workflows
-
Recovery confirmation links
This turns Gmail into a launchpad for cloud lateral movement. Instead of scanning the inbox for sensitive attachments, attackers look for automated emails that unlock access to adjacent systems.
In many cases, email compromise is merely the first step in a much larger identity breach.
Stealth is the real superpower
One of the most effective attacker techniques is suppressing evidence of compromise inside the mailbox itself.
By creating filters that automatically delete or archive:
-
Security alerts
-
Password reset confirmations
-
MFA notifications
-
Victim replies to phishing emails
…attackers can operate for extended periods without raising suspicion.
These actions blend seamlessly into legitimate user behavior, making them difficult to detect unless defenders monitor mailbox configuration changes alongside authentication activity.
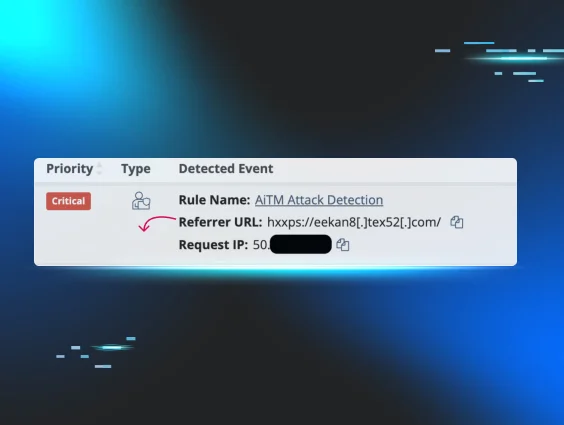
Modern identity detection platforms focus on exactly this type of behavior correlation, linking mailbox changes, authentication patterns, and anomalous access into a single investigative signal rather than isolated alerts.
Outbound abuse scales the attack
Once inside, attackers leverage the trust associated with a legitimate Workspace identity to expand their reach:
-
Sending phishing emails to internal users
-
Targeting external partners and vendors
-
Requesting sensitive information or payments
-
Harvesting replies while hiding them from the victim
Because messages originate from trusted accounts, technical controls and human skepticism both weaken, accelerating the impact.
Persistence keeps the door open
Experienced threat actors don’t rely on a single access method. They establish redundancy by:
-
Creating forwarding rules to exfiltrate all inbound mail
-
Maintaining OAuth tokens that survive password resets
-
Leveraging alternate access channels
-
Establishing secondary access paths
This persistence allows attackers to maintain visibility even after partial remediation, enabling reinfection or delayed fraud.
Why detection is harder than ever
Traditional BEC detection focuses heavily on:
-
Suspicious email content
-
Known phishing indicators
-
User-reported alerts
-
Static rules
But modern BEC often:
-
Uses legitimate authentication flows
-
Avoids malware entirely
-
Exploits platform-native features
-
Blends into normal administrative activity
-
Spans multiple systems and timelines
Single-signal detections miss multi-stage campaigns. High-volume alerts overwhelm teams. False positives erode trust in controls.
BEC has become an identity defense problem
Stopping modern BEC requires visibility beyond the inbox:
-
Identity authentication behavior
-
Token lifecycle monitoring
-
OAuth consent anomalies
-
Mailbox configuration abuse
-
SaaS access patterns
-
Cross-platform correlation
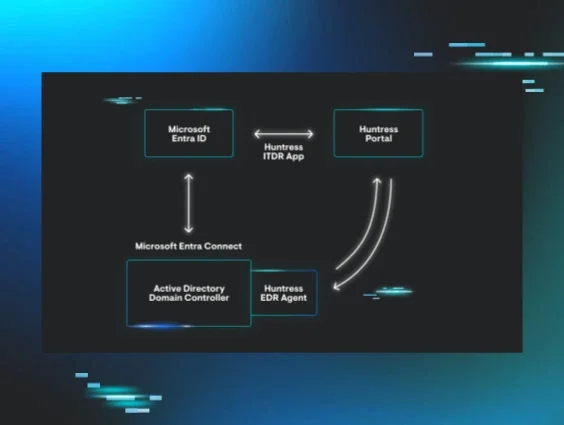
This is exactly why BEC increasingly falls under Identity Threat Detection and Response (ITDR), where detection focuses on identity behavior rather than email content alone—and response is guided by human analysts who understand real attacker tradecraft.
At Huntress, we’ve spent years building managed detection and response around identity threats in Microsoft environments. That same operational experience and threat research is now expanding to Google Workspace, giving organizations a managed way to detect, investigate, and respond to identity-driven BEC attacks without building a SOC from scratch.
The bottom line
BEC hasn’t disappeared. It's matured.
Attackers now exploit identity infrastructure embedded inside Google Workspace to operate stealthily, persist longer, and move laterally across cloud environments. Email is simply the entry point. Identity is the real battlefield.
Organizations that continue to treat BEC as an inbox problem will keep playing defense from behind.
Those that adopt identity-first detection and response—and prepare their Google Workspace environments accordingly—will finally start disrupting attackers where it matters most.