When it comes to identity security in Microsoft 365, the forecast is often cloudy, especially when some vendors lean into half-truths or conveniently cropped facts to market their products. But let’s clear the air.
Here at Huntress, we believe in clarity over cloudiness. So let’s bust some of the most common Microsoft 365 and identity security myths floating around out there. If you’ve heard statements like “logins are only 2% of the data” or “you don’t need more protection if you have MFA,” you’ve likely caught a whiff of one of these myths. Let’s break them down.
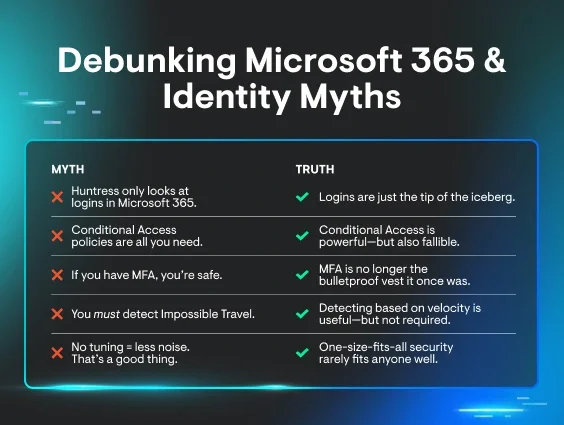
Myth #1: “Huntress only looks at logins in Microsoft 365.”
Truth: Logins are just the tip of the iceberg.
Yes, login events are important, but they’re far from the only signal Huntress Managed ITDR pays attention to. Our telemetry includes signals from Azure Active Directory and Microsoft Exchange, covering a range of events from group membership changes and role escalations to suspicious inbox rules and mailbox permission updates.
In fact, while login events help us spot the early stages of compromise—such as adversary-in-the-middle (AiTM) attacks or session hijacking—mailbox events often give you the downstream context, like malicious inbox rules. But we’re not stopping there. We're actively expanding into SharePoint, OneDrive, and additional Microsoft event categories to make sure defenders have visibility across the entire kill chain—not just the front door. We also detect Rogue Apps (malicious OAuth applications), which is a new form of telemetry that we build from disparate data sources floating around the average tenant.
The truth? Huntress looks way beyond logins and always will.
Myth #2: “Conditional Access policies are all you need.”
Truth: Conditional Access is powerful—but also fallible.
Microsoft’s Conditional Access capabilities (especially with P1/P2 licensing) offer impressive granular control. You can block logins from specific geos, require device compliance, enforce strong MFA, and more.
But here’s the catch: you still have to configure it. We’ve found that 24% of P1 license holders and 9% of P2 license holders don’t configure Conditional Access policies. And misconfigurations are more common than you'd think. One misplaced exception or oversight can create unintended security gaps—or worse, lock you out of your own tenant.
We’ve seen seasoned admins get it wrong. That’s why Managed ITDR doesn’t rely on your Conditional Access being perfect. It assumes attackers are looking for cracks in your policies and detects behavior that slips through.
Conditional Access is a guardrail. Huntress is the net that catches what falls through.
Myth #3: “If you have MFA, you’re safe.”
Truth: MFA is no longer the bulletproof vest it once was.
MFA fatigue. AiTM phishing kits. Session hijacking. Attackers have evolved, and today’s threat landscape treats MFA as an obstacle, not a roadblock.
Just because your users are prompted for a second factor doesn’t mean they’re immune to attacks. We regularly detect attackers bypassing MFA entirely by stealing session tokens, authenticating as the user, skipping the challenge, and setting up shop unnoticed.
Huntress Managed ITDR is purpose-built to spot these tactics, catching what traditional MFA-based defenses miss. Because “logged in successfully” doesn’t always mean “authorized.”
Myth #4: “You must detect Impossible Travel.”
Truth: Detecting based on velocity is useful, but not required.
Is it valuable to know if a user logged in from Florida and then France within two minutes? Sure. But focusing solely on Impossible Travel scenarios creates blind spots, especially for attackers using residential proxy networks or cloud hosts to spoof realistic locations. Plus, NOT detecting impossible travel saves a massive amount of useless noise. Location itself is a useless data point without taking into account the other kinds of client address technologies like datacenter or VPN.
We give our partners the flexibility to track travel anomalies where relevant, but we don’t hinge our entire detection logic on it. Instead, we look at the whole picture: session behaviors, app consent activity, inbox manipulation, role escalations, and more.
Because not every attack comes with a boarding pass.
Myth #5: “No tuning = less noise. That’s a good thing.”
Truth: One-size-fits-all security rarely fits anyone well.
Some vendors frame “lack of customization” as a feature. No tuning! No fuss! But the reality is, at scale, environments vary. And context is king.
Huntress partners can customize what counts as expected versus unauthorized access, set travel rule exceptions, and suppress alerts based on their needs. Do you have to configure anything? Nope. But if you’re managing thousands of identities across diverse tenants, you’ll appreciate having the option.
Trust us. We learned the hard way. The first iteration of Managed ITDR had little to no customization, but over time, scale taught us how mandatory customization actually is for reducing noise and increasing efficacy.
We believe thoughtful tuning reduces false positives and empowers you to make smarter decisions faster. No alert fatigue, no cookie-cutter detections. Just flexible, context-rich security that scales.
Final forecast: Less fog, more facts
In a world of “cloudy truths” and buzzword-laden marketing, it’s easy to get swept up in vendor claims that sound impressive on the surface. But when you peel back the layers, the real question is simple: Can they detect real threats, in real time, with real context, and help you respond before damage is done?
Huntress Managed ITDR was built to do exactly that. We see what others miss, deliver high-fidelity detections with human-backed response, and give you the flexibility and clarity you need to defend identities in a constantly shifting threat landscape.
Sick of the fog? Let’s cut through it together.
👉 Start your free trial of Managed ITDR