If a threat actor launches a ransomware, extortion, or identity theft attack, the odds are that infostealers—and the credentials they’ve compromised—are behind it. Infostealers have quickly evolved into a major threat, fueling high-profile data breaches. It’s no wonder Huntress’ 2025 Cyber Threat Report found that infostealers represented almost a quarter of all incidents our team saw last year.
Threat actors deploy infostealers to harvest credentials, financial information, and sensitive data, which is then sold on underground marketplaces to buyers that may want to target individuals or corporations with ransomware, extortion attacks, and more.
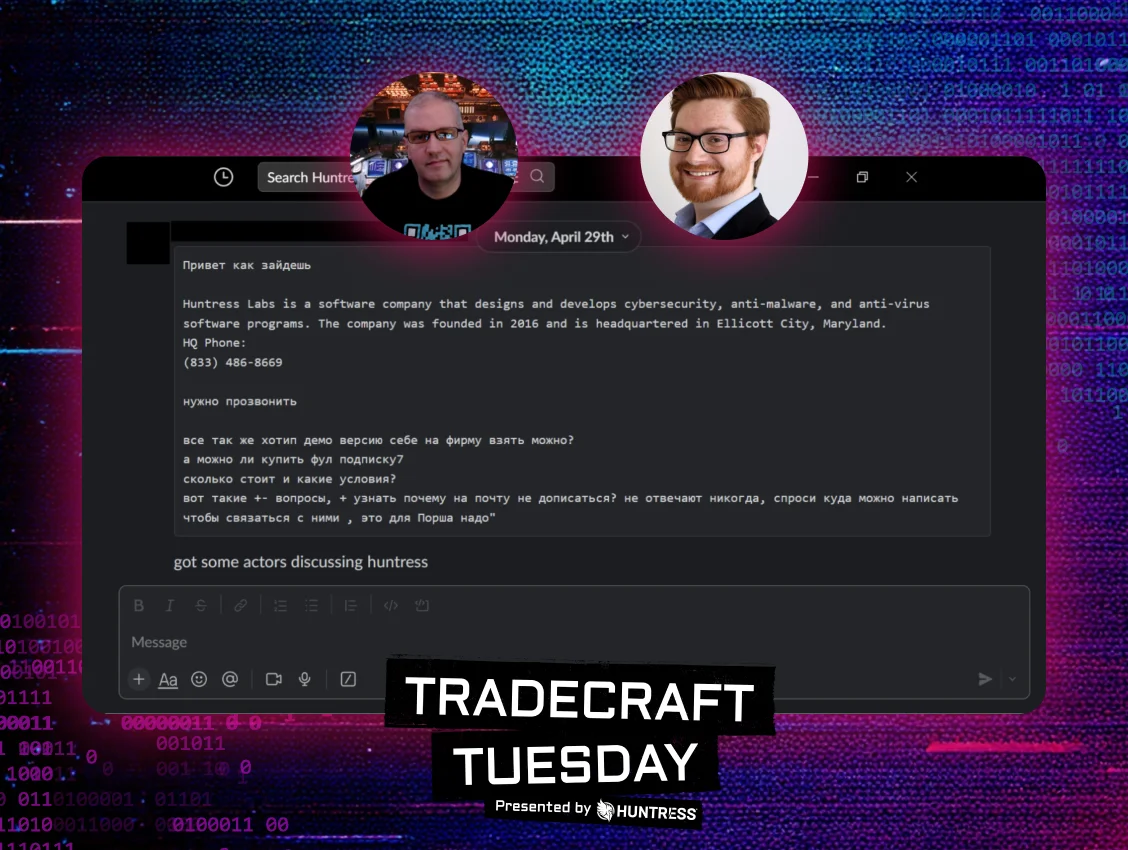
In the May Huntress Tradecraft Tuesday, Greg Linares, Principal Threat Intelligence Analyst at Huntress, and Lindsey O’Donnell-Welch, technical community engagement writer at Huntress, discussed how infostealers have transformed into the modern threat that they are today, how infostealer attacks present themselves in the SOC environment, and how businesses can protect themselves.
It all started with Zeus: A quick history of infostealers
Infostealers can be traced back to Zeus, malware which was first introduced in 2007. In its original variant, it could access victims’ banking credentials and financial information. In 2011, the source code of Zeus leaked, leading to the rapid expansion of infostealers like AZORult and HawkEye across the threat landscape (as we’ll see later in this blog, source code leaks and subsequent infostealer variants that pop up Hyra-style represent a repeating trend).
Not only were more infostealers starting to crop up, but they were also targeting more than just financial data, including crypto wallets and software license data. Soon, the true industrialization of infostealers began to take form, with power players like Raccoon, Vidar, and RedLine being built out. At the same time, marketplaces like Genesis and Russian Market started booming.
Today’s infostealer landscape has continued this shift, with even more variants forking off of existing families, and cybercriminals targeting information like multi-factor authentication (MFA) codes, as well as Discord and Slack credentials and logs. Meanwhile, marketplaces have further matured and integrated APT groups as well, enabling an environment where threat actors can identify specific information, down to the details about specific corporations or individuals, to launch targeted attacks.
All your data are belong to us
While infostealers are known for swiping victims’ email and browser credentials and credit card data, modern infostealers target a broad set of information aimed at identity and financial theft, and they can enable further data harvesting.
The “primo data” from infostealers currently is corporate information, specifically SAML, SSO, VPN, SSH, RMM, RDP, Slack, and FTP credentials. Slack tokens, for instance, are considered extremely valuable on underground marketplaces, and many breaches (including attacks launched by Scattered Spider) have occurred exclusively using Slack tokens. API keys and cloud service credentials are also ramping up in popularity amongst threat groups as well.
Here are some other types of data that infostealers target:
-
Cookies, single sign-on (SSO) tokens, session tokens, JWT tokens
-
2FA, MFA, and OTP keys
-
Crypto wallets, recovery, and seed phrases
-
API keys and cloud service credentials
-
Personally identifiable information (PII), protected health information (PHI), geolocation data, chat data, and photos (specifically for extortion)
After infostealers gather all this data, it’s then turned over in underground marketplaces to be used in further attacks. The cost of this stolen data varies, ranging from email account credentials with an average price per access of $10 to $65, up to SSO tokens (costing on average $100 to $250) or cloud service credentials (costing on average $30 to $200).
There are several notable infostealer marketplaces, including Russian Market, 2Easy Market, and InfoLog Empire. Several more marketplaces have ceased to exist over the years (including Genesis Market, StealerNet, and RaidForums), either because they shut down or because they were seized by law enforcement. These marketplaces have unique characteristics: for instance, Genesis Market (which started in 2018 and was seized in 2023) was invitation-only, and it included an interface that allowed cybercriminals to browse stolen data by location, IP, browser fingerprint, or otherwise.
The Banshee Stealer source code leak and macOS stealers
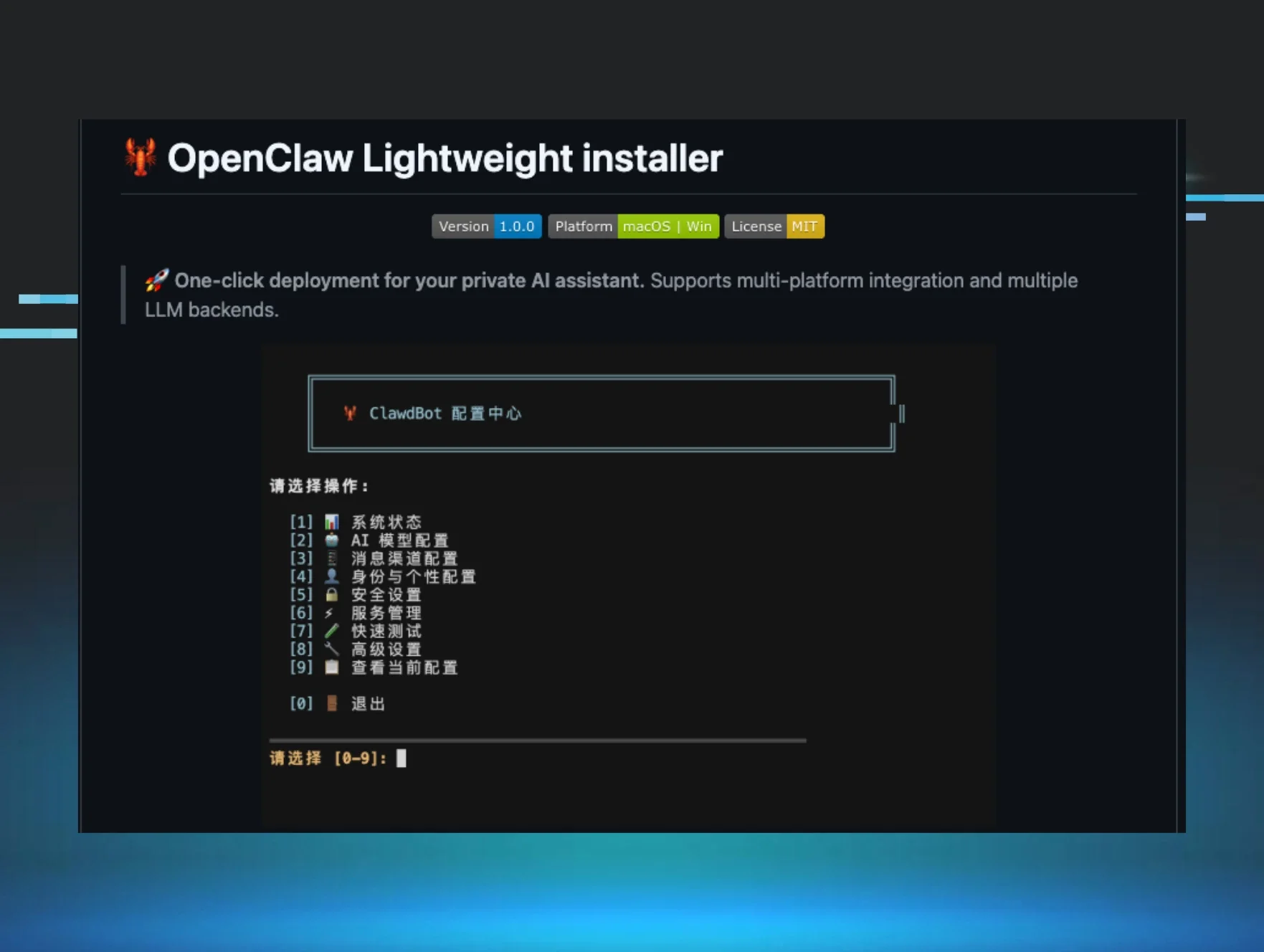
The macOS infostealer landscape has gone through an interesting evolution over the last year, due in part to the source code leak of Banshee Stealer. In November 2024, Banshee Stealer’s source code was leaked, and it abruptly shut down. While the leak enabled better detection measures for defenders, many infostealer developers also took advantage, using the source code in order to branch out with their own variants, including:
- FrigidStealer: Targets Safari and Chrome credentials, Apple Notes documents, and crypto wallet data
-
FleshStealer: Targets Chromium-based web browsers for credentials and cookies, as well as 2FA passwords or Wi-Fi network credentials
-
Realst Stealer: Targets macOS Keychain data, crypto wallet data, and Chromium-based browser information
Overall, macOS infostealers operate in a slightly different way from Windows infostealers due to the differences between the operating systems (as we previously touched on in our April Tradecraft Tuesday episode, “Say Hello to Mac Malware”). macOS infostealers primarily target Apple’s iCloud and Keychain, which are where most of the credentials are stored.
In some cases, macOS stealers attempt to bypass Apple-specific protections like the Transparency Consent and Control (TCC) framework, Apple’s database used to prompt users when an app tries to perform actions requiring their specific permission. Infostealers like Realst also abuse the AppleScript framework (Apple’s scripting language) to simulate Apple prompts, with the end goal of stealing end-user credentials.
Law enforcement takedowns: Marketplaces and infrastructure
Law enforcement authorities have cracked down on various parts of the infostealer lifecycle over the past year, with takedowns of infostealer infrastructure, arrests of high-profile infostealer developers and administrators, and the targeting of marketplaces where infostealer credentials are sold.
In October 2024, international authorities announced the takedown of the RedLine and META infostealer after seizing domains, servers, and Telegram accounts used by the infostealers’ administrators. The US Department of Justice (DoJ) also unsealed charges against Maxim Rudometov, one of the developers and administrators of RedLine infostealer.
Then, in January, the DoJ announced an international operation, called Operation Talent, to take down cybercrime marketplaces Cracked and Nulled. The takedown is notable as it relates to infostealers because they are major marketplaces used to sell stolen login credentials (in addition to hacking tools and servers) from infostealer campaigns. Takedowns of marketplaces in general can have a significant influence on the infostealer landscape overall, with the takedowns of Genesis Market and RaidForums having major impacts.
More recently, in May, Europol announced a law enforcement operation targeting Lumma Stealer, which disrupted its technical infrastructure with federal authorities seizing its infrastructure and control panel. The operation was part of a public-private sector partnership effort, and Microsoft announced it had seized 2,300 domains linked to Lumma’s infrastructure.
Infostealers in the wild (and how to prevent them)
Huntress has detected various attacks involving infostealers in the wild. In one incident in March 2025, a user downloaded an executable notiom.exe from a newly registered domain that is linked to a malicious IP address. Here, the threat actor appeared to be disguising the executable as the legitimate Notion app, which is a productivity and note-taking application. As Figure 5 below outlines, the autorun name is electron.app.Notion—Electron is a framework used for developing apps, which has previously been abused by threat actors for infostealers.
After the executable was downloaded, it misused remote debugging in Chrome, which is a common malicious activity that is observed by infostealers in order to extract cookies. A file named raretemp was also created in the temp directory (this is a name that has been used by Lumma Stealer). Lumma Stealer is the second most common infostealer (behind ChromeLoader) that Huntress has observed over the last year.
This is just one example of an attack involving an infostealer. Infostealers are distributed in various ways, including malicious websites, phishing emails, and malvertising.
A common infostealer attack vector that threat actors use is Google-based malvertising, where they buy a domain and hide infostealers in Google Ads that target people looking for certain things, like popular tools. Because of the popularity of this attack vector, businesses should train their employees not to trust Google Ads and rely on ad blockers. Companies can prevent or mitigate the risks caused by infostealers with a multi-layered defense strategy. Measures like MFA can reduce the effectiveness of stolen credentials.
Endpoint detection and response (EDR) controls can also detect unauthorized access on session tokens or encrypted files. There are other common indicators of compromise that can tip off infostealer attacks, including the creation of Run Keys, noisy file activity, and higher DiskIO activity. Infostealers will also start downloading components into non-standard folders.
The future of infostealer threats
As we’ve outlined here, infostealers have a long and varied history, and the current infostealer landscape includes mature marketplaces and a wide variety of targeted data. Infostealers operate in a vicious cycle, stealing credentials in initial campaigns, which are then sold to other cybercriminals and used to launch further attacks.
The increase of remote and hybrid work environments—and the blending of personal and professional devices and accounts—has exacerbated the threat of infostealers. These trends have widened the attack surface and allowed threat actors to grab work credentials that may be stored on unmanaged, personal devices.
With the pervasiveness of infostealers, it’s important for companies to better understand security measures they can take to mitigate this threat. Tune into our Tradecraft Tuesday for more information on infostealers and the risks that they pose to businesses.