Usernames and passwords are the foundation of almost every application we use and every network we access. But these conventional credentials, first introduced more than 60 years ago by researchers at MIT in 1961, have become shockingly inadequate. The days of only relying on a simple username and password for protection are long gone.
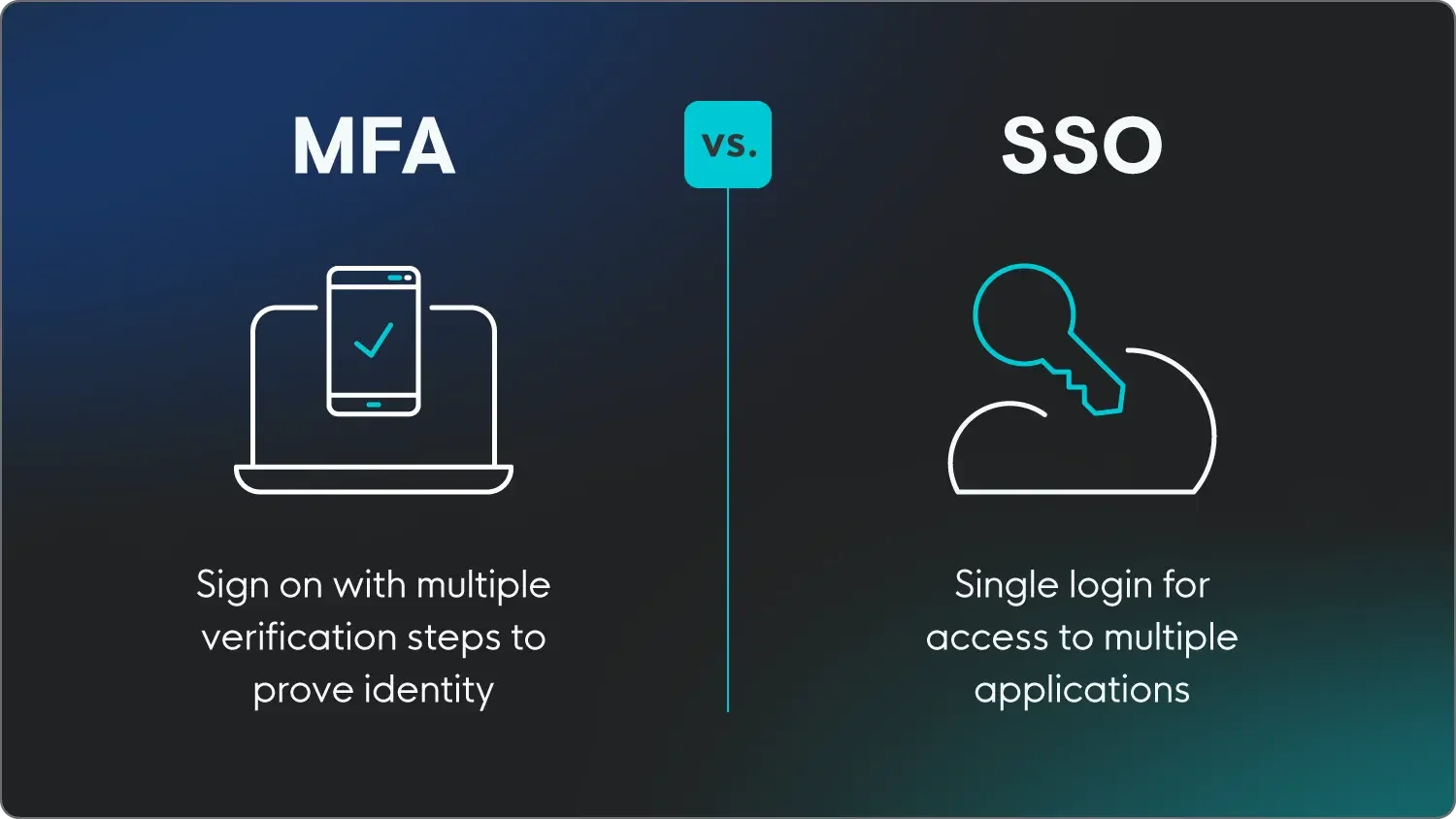
As threat actors have become more clever and resourceful, companies need a stronger, more resilient defense. Enter single sign-on (SSO) and multi-factor authentication (MFA), two fundamental layers of security that can bolster your cyber defense in a relatively easy way. So, how do you choose between SSO vs. MFA? It’s not one or the other—it’s both!
In this blog, we'll delve into the world of SSO vs. MFA, explore their individual benefits, and explain why combining them can be a game-changer for your security posture.
Key takeaways
- SSO and MFA serve different but complementary purposes: SSO simplifies access by letting users log in once to reach multiple applications, while MFA strengthens security by requiring additional verification factors beyond a password.
- Passwords alone are no longer enough: First introduced in 1961, traditional username and password credentials have become dangerously inadequate against modern threat actors—making layered authentication essential.
- Combining SSO and MFA is the recommended approach: SSO reduces login fatigue and encourages stronger passphrases, while MFA ensures that even compromised credentials can't grant unauthorized access.
- Not all MFA methods are equally secure: Passkeys, biometrics, and push factors offer stronger protection than SMS codes or one-time passcodes, and organizations should prioritize the strongest available options.
What is single sign-on?
Single sign-on, or SSO, is when applications or websites allow a person to log in using an already trusted third party to verify that the user is who they say they are.
Instead of juggling multiple usernames and passwords for different systems, users log in once, and SSO securely handles their access to various resources. You’ve probably seen or used this before as most websites today offer the option to log in with Google or Apple or Microsoft or Facebook or… you get the idea.
What is multi-factor authentication?
Multi-factor authentication, or MFA for short, is an authentication method that requires users to provide two or more verification factors before they can get access. These factors typically fall into one of three categories:
- Knowledge: Something only the user knows (e.g., a password)
- Possession: Something only the user has (e.g., a smartphone or security token)
- Inherence: Something only the user is (e.g., fingerprint or facial recognition)
MFA brings a major security enhancement by adding an additional layer of authentication beyond just a username and password. Even if threat actors manage to steal login credentials, they can’t access the account without the second factor.
Key differences of MFA and SSO:
SSO (single sign-on) and MFA (multi-factor authentication) both play a role in the login process, but they solve different problems. SSO is built for convenience—it lets users log in once to access multiple applications without managing separate credentials for each. MFA is built for security—it requires users to verify their identity through two or more factors, such as a password plus a biometric scan or a push notification, before gaining access. In short, SSO reduces how often you log in, while MFA makes each login more trustworthy. The most effective approach uses both together: SSO streamlines the user experience, and MFA protects it.
Here’s an overview of the key differences between MFA and SSO.
|
MFA |
SSO | |
|
Main goal |
Security, reduces the risk of unauthorized access |
Convenience, reduces login fatigue |
|
User experience |
Extra steps added to verify identity |
Single login for multiple apps |
|
Complexity |
Layered authentication, requires more setup |
Integrates apps into one login system |
|
Typical use case |
Protecting the SSO identity |
Brokering access to enterprise and cloud applications |
|
Potential advantages |
Enhanced security, mitigates credential theft, and ensures compliance |
Convenient, reduces potential user fatigue, saves time, cost-effective, centralized control, improved security |
|
Potential disadvantages |
Users may find it inconvenient/fatiguing, SMS codes can be vulnerable, potential implementation challenges |
Single point of failure, reliant on identity provider (IdP) |
Why you should use both MFA and SSO
While SSO and MFA serve different purposes, combining them gives you a robust defense against cyber threats. Implementing both lets organizations improve their security without creating a bad user experience, while also making it easier to monitor network activity.
Let’s face it: Passwords are a vulnerability. It’s tough for people to remember the complex, multi-character passwords that almost every application requires today. So wouldn’t it be so much easier to remember just one? One solid, complex, and hard-to-guess passphrase, that is.
With SSO, that one passphrase is all a user has to remember. But of course, SSO means fewer potential entry points for hackers—and once they’ve cracked the code, the doors have opened to all the user’s other accounts and applications. This is why using strong, uncommon passwords and requiring an additional authentication layer with MFA is so important.
By combining SSO and MFA, you strike a balance between convenience and security. Users enjoy the simplicity of logging in once, while MFA adds an extra layer of protection: even if their credentials are compromised, an attacker still can't access their account.
Security tips for implementing SSO and MFA
Strengthening your security posture with SSO and MFA isn’t just a smart choice; it's a basic and essential step. To protect your employees and your organization, we highly recommend implementing both SSO and MFA.
When combined, SSO can help limit employee frustration and increase password strength, while MFA allows for verification of user identity before they log in to any application or network you want to maintain tight control over.
Here are some essential tips for successfully implementing MFA and SSO in your organization:
- Choose a reliable SSO provider: Select a trusted SSO solution that offers seamless integration with your applications and robust security features.
- Implement MFA everywhere: Enable MFA for all critical applications and services to ensure a consistent security posture.
- Not all MFAs are created equal: Consider only enabling passkeys, biometric verification, and/or push factors instead of the weaker one-time passcodes, SMS, or voice verifications.
- Educate users: Train your users on the importance of security, especially regarding protecting their MFA methods, such as smartphones or tokens.
- Regularly review and update policies: Continuously monitor and update access policies and authentication methods to adapt to evolving threats.
Not “either or”, it’s both and then some
Cybersecurity is a challenge for IT departments across all industries. Not only are expectations getting higher, but the workforce is also evolving with new technologies and an ever-expanding global ecosystem. That means the risks are high as well.
Single sign-on and multi-factor authentication represent two fundamental layers of security that can work in tandem to combat the vulnerabilities of traditional authentication methods. By choosing SSO and MFA, rather than SSO vs. MFA, you have a bit more peace of mind while protecting your organization or managed environments.
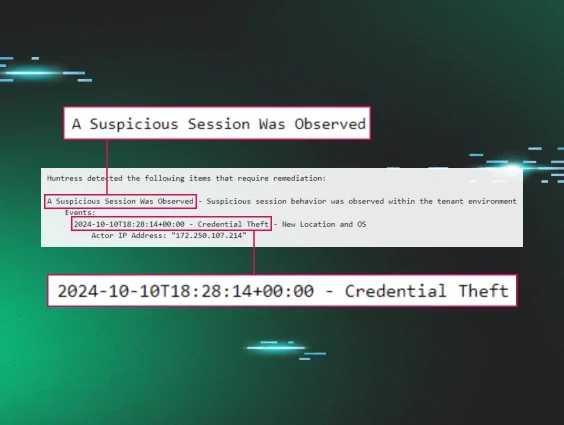
At Huntress, we’re hyper-aware of how hackers are getting smarter and evolving their tradecraft. We need to implement changes to make it that much harder for attackers to access an application or network. That’s why the Huntress platform is enabled for both multi-factor authentication and two-factor authentication (2FA).
Huntress empowers your employees to be part of the cybersecurity solution with security awareness training (SAT), giving you personalized phishing defense coaching based on real threats our security experts see in the wild.
FAQ
What's the difference between SSO and MFA?
SSO stands for single sign-on, which means logging into one account to gain access to multiple services, like your Google account. MFA, or multi-factor authentication, is an identity verification process in which users are required to confirm their identity after logging in with something like a biometric scan or typing in a received code.
Can you have both MFA and SSO?
Yes, absolutely. In fact, it’s encouraged to implement both MFA and SSO to provide users with the best and most secure experience.
Is MFA the same as 2FA?
Two-factor authentication is a type of multi-factor authentication where two kinds of identity verification are required. MFA refers to when at least two types of verification are required, but sometimes more.