Every beep, ding, and red flag screams, "You’ve been compromised!" If you’re a security professional drowning in an endless sea of alerts, this probably sounds familiar. Rest assured, you’re not alone.
For anyone in IT or security, alert fatigue can be a real challenge and concern, and can put a lot of stress on teams (especially in an industry where you feel like you can’t slip up or put your business or clients at risk).
Our 24/7 Security Operations Center (SOC) keeps watch over millions of endpoints and identities day in and day out, so we know a thing or two about managing alert fatigue and staying focused on threats that matter.
This blog breaks down the causes of alert fatigue, why it matters, and practical tips for alert-heavy environments.
Here’s how some of our SOC analysts fend off alert fatigue and burnout:
What is alert fatigue, and why does it matter?
Alert fatigue happens when security professionals are overwhelmed by the sheer volume of notifications flooding their dashboards. Never-ending false positives, repetitive alerts, and non-critical notifications create a toxic cycle of noise and desensitization to critical threats.
According to 2025 industry benchmarks, modern SOC teams now juggle an average of nearly 1,000 alerts per day—with enterprise environments often seeing 10,000+ signals. Even with advanced tools, a proper investigation now requires an average of 30 to 40 minutes of an analyst's time. This is a perfect storm for:
Burnout and low morale: Repetition, long hours, unreasonable workloads, communicating with stressed-out clients, and creativity voids
-
Missed or ignored threats: Critical issues get stuck at the bottom of the stack or don’t get addressed at all
-
Reduced speed: Valuable time is wasted investigating smoke and mirrors instead of real vulnerabilities, exposures, and threats.
Imagine getting several hundred text messages in a single day—the triage process is a beast to sort through, plus the added risk of missing something important from family members or friends.
Why does all this matter? The steady influx of incident alerts keeps many defenders gainfully employed but can also feel like an endless merry-go-round with no visible exit. Cognitive overload from alert fatigue isn’t just water-cooler talk anymore. It puts a strain on mental health and makes businesses acutely vulnerable to cyberattacks, data breaches, regulatory noncompliance, operational downtime, and financial turmoil.
Alert fatigue: How to keep your cool
We’ve rounded up a list of ideas to help you stay calm and carry on with the persistent pressure of alert fatigue.
Rediscover your attack surface
Take a deep dive into your attack surface. Prioritize asset management and assess which assets are needed for your business. It's simple—fewer assets produce fewer alerts while significantly reducing vulnerable exposures across your perimeter. This doubles the result with one effort.
For more real-world examples of how attackers compromise vulnerable perimeter exposures, check out our on-demand webinar, “Cracks in the Shell: How Hackers Exploit the Perimeter to Gain Access.”
Streamline the critical stuff
Not all alerts are created equal. Separate critical threats from less important pings like informational alerts or non-malicious network anomalies. By assigning priority levels, you can focus your time and expertise where it matters most for your business.
Divide and conquer
Collaborate and communicate with your team to distribute the workload. Use tagging systems, shared dashboards, and task assignments to ensure a balanced workflow. Remember, cybersecurity isn’t a solo sport. It’s team defense.
Put managed automation to work
Automation tools like our Managed Security Information and Event Management (SIEM) use Smart Filtering at the log source to capture only threat-specific data. This cuts the chaos of alert fatigue by organizing threat visibility across your network. Our security experts manage all things Huntress Managed SIEM, so you don’t have to.
For more on SIEM, check out these on-demand webinars:
-
“Solving the SIEM Problem: A Hard Reset on Legacy Solutions”
-
“Reimagining SIEM for Healthcare: Enhancing Patient Data Security and Compliance”
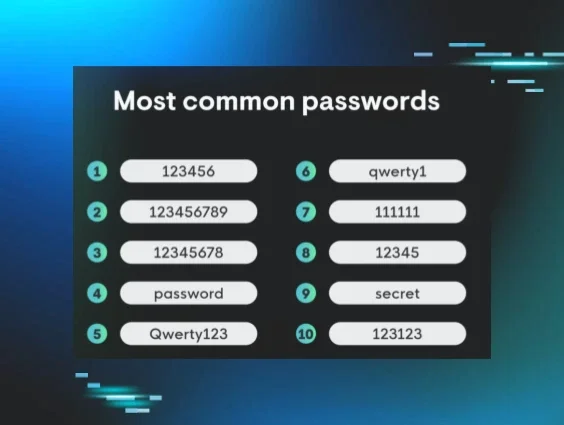
Fine-tune alerting rules
Default settings are fine, but a little tuning can drastically reduce the noise. If you’re using tools with pre-configured alerting systems, go in and customize the thresholds for alerts.
Outsource to experts
Endpoints are noisy, but ignoring them is far too risky for your business—70% of breaches come from compromised endpoints. Luckily, there’s a solution to keep your endpoints secure and quiet, reducing the pressure of alert fatigue.
With Huntress Managed Endpoint Detection and Response (EDR), you can pass the “alert torch” to our human-powered threat hunters to manage the chaos coming from your endpoints. We get all the alerts instead of you. Then, we filter, contextualize, and dig into the threat details, eliminating a ton of noise for defenders.
Here are just a few examples of Huntress’ response to and management of security alerts:
How security leaders can support teams dealing with alert fatigue
Cybersecurity leaders play a critical role in helping balance alert fatigue.
Here are a few things to consider:
1. Choose tools wisely
Outdated systems or fragmented toolsets significantly contribute to alert fatigue. Leaders should explore modern, consolidated platforms with human-backed support and threat validation, such as Managed EDR, Managed Identity Threat Detection and Response (ITDR), and Managed SIEM.
2. Address the stress
Alert fatigue is both a technical and a human issue. It takes a toll, so check in regularly with teams. Encourage an open and honest dialogue about workplace stressors. Don’t brush alert fatigue under the rug.
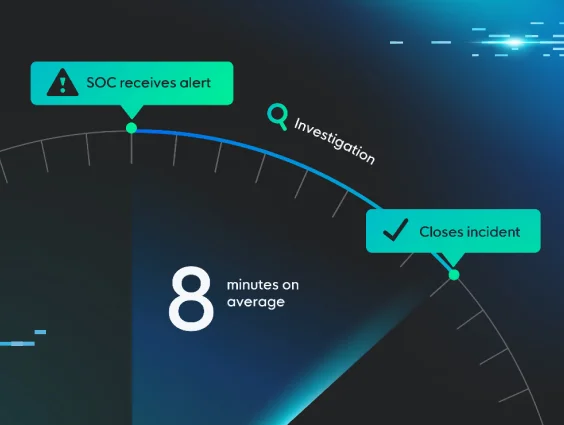
3. Measure metrics that matter
Regularly measure and track metrics like Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR). Declining numbers often signal well-optimized alert strategies. Celebrate these wins and build upon successful strategies.
Example of SOC response metrics Source
Burnout? Not on your watch
Dealing with alert fatigue doesn’t have to feel like an endless game of keep-up. By working smarter—not harder—with prioritization, automation, and human-backed managed technology solutions, you can turn the noise into a well-oiled and balanced machine.
Get Huntress up and running now to get rid of alert fatigue for your organization. Sign up today for your free trial.