Running a business, big or small, isn’t easy. Some challenges you’ll see coming, while others will catch you completely off guard. One day, everything's running smoothly, but the next, a cyberattack can shut you out of your systems. Your emails, files, and workflows are suddenly frozen. And the losses start mounting—productivity drops, customers grow frustrated, and revenue slips away. In that moment, you can’t help but ask yourself, “How did all this happen?” But the more urgent question is, “How fast can I bounce back?”
This might sound dramatic, but for businesses that ignore cybersecurity, it’s a brutal lesson learned the hard way.
Cybersecurity isn’t just about protecting your data. It’s about protecting your reputation, ensuring operational stability, and avoiding financial losses. It’s almost cliche to say at this point, but if you’re a business owner, you have to understand it’s not a matter of if a cyberattack will hit you—it’s a matter of when.
No one’s off-limits anymore
There’s a dangerous myth that attackers only go after big-name enterprises. But today’s malicious hackers don’t care if you think you’re too small or too niche. They don’t care about your budget constraints. If you have data, they want it. If you have money, they’ll find a way to take it. So, that mom-and-pop shop around the corner is just as appealing as a well-known Fortune 500 company. According to the Huntress 2025 Cyber Threat Report, attackers are now using the same sophisticated playbook across businesses of all sizes.
Our analysis revealed that attackers targeted a broad range of industries last year, with healthcare and education bearing the brunt of the attacks. These two sectors alone, arguably the most critical, accounted for nearly 40% of all observed incidents. Big threats to the tech, manufacturing, and government sectors were close behind.
Industries targeted in 2024, as observed by Huntress. Source.
What makes smaller, non-enterprise businesses easier targets, however, are their resource gaps. As we explore in The True Cost of a Cyberattack:
- 61% of these businesses don’t have a dedicated cybersecurity team.
- 47% lack an incident response plan.
- 27% don’t have cyber insurance.
Whether it’s stealing customer data, demanding ransoms, or disrupting operations, the aftermath can be catastrophic for an unprepared business.
Cyberattacks are pricier than you think
Many business owners might think, “Oh, it can’t happen to me,” or worse, “I’ll just pay the ransom and move on.” Both perspectives are horribly flawed.
First, paying the ransom doesn’t guarantee you’ll get your data back. Keep in mind you’re putting your trust in criminals, which is never a smart move. Second, there's more at risk than just the ransom itself. Here’s what the numbers say from The True Cost of a Cyberattack:
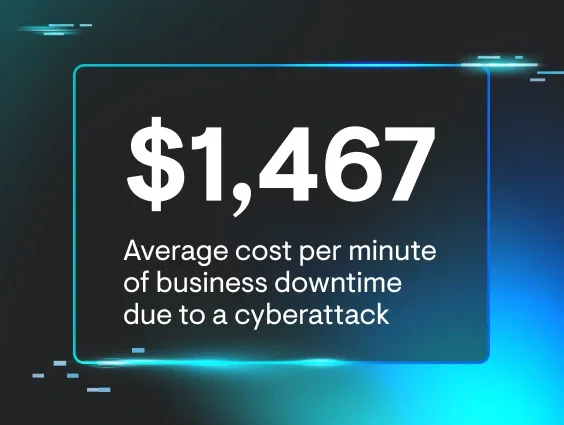
- $1,467 per minute is the average cost of business downtime.
- $250,000+ is what 20% of “mid-sized” businesses end up paying to recover from a cyberattack.
- 60% of small businesses permanently close within six months of an attack.
Average cost of downtime due to cyberattacks. Source.
Beyond these immediate costs, there are other potential indirect expenses:
- Legal fees and compliance fines
- Customer compensation
- Forensic investigations
- Operational disruptions
And then there’s the hardest hit to recover from—a damaged reputation.
Trust is hard to rebuild after a breach
Customers may shrug off a late order, but expecting forgiveness for a data breach is another story. When info like bank numbers or medical records gets leaked, it’s more than just a technical failure—it’s personal.
Take the Minneapolis Public Schools data breach from 2023. After a ransomware attack exposed 300,000 files, which included sensitive info like abuse claims and Social Security numbers, the fallout was intense. Faculty morale tanked, students reported trauma, and parents pulled their children out of the school district altogether. Not surprisingly, lawsuits followed. In the end, trust was shattered.
For businesses, the math is simple: a breach equals broken trust, and broken trust equals lost customers. Proactive security measures aren’t just about protecting data—they’re about protecting your most valuable relationships and the longevity of your business.
Slow detection can debilitate your business
If an attacker breaches your business today, it could take weeks before you even realize it. According to The True Cost of a Cyberattack, the median dwell time—the period between a breach and its detection—is 16 days. That’s over two weeks for hackers to root around your systems, steal data, and entrench themselves within your network. By then, it’s no longer just an attack. It’s a full-blown takeover.
Look at Shields Health Care Group. The organization took 21 days to identify a breach that exposed over two million patient records. Although the breach was discovered on March 28, 2022, evidence shows it began as early as March 7. To make matters worse, notification letters weren’t sent until April 19, nearly a month after the breach was detected. This delay gave hackers more than enough time to use sensitive medical data for financial gain, leading to legal challenges and a devastating loss of trust.
Delayed identification gives attackers ample time to collect and use data for financial gain.
Long detection and response times give attackers a head start, letting them abuse stolen info long before victims can take protective measures. In Shields’ case, the lack of a rapid response compounded the damage, leaving millions exposed to heightened risks.
This is where fully managed cybersecurity could’ve really helped. If you’re a business owner who’s been putting off security measures, it’s probably not because you don’t care. Chances are, you’re just not sure where to start or if you have the right tools in place. That’s exactly why managed security services exist—to take the weight off your shoulders and make protecting your business easier.
Instead of doing nothing and hoping for the best, you can count on a solution run by a dedicated security operations center (SOC). With around-the-clock monitoring and real-time threat alerts, a SOC acts quickly to help stop breaches before they turn into bigger problems.
The role of SOCs in proactive cybersecurity
A SOC is like the heart of your company’s cybersecurity. It’s a team of experts working 24/7 to keep an eye on your systems, catch threats, and stop them before they cause any damage. By blending expert skills with advanced technology, a SOC provides:
-
Continuous monitoring: A SOC monitors your systems, networks, and devices nonstop, looking for anything suspicious. It's like having a guard on duty around the clock so hackers don’t slip through unnoticed.
-
Threat detection and response: By analyzing vast amounts of data in real time, SOCs identify emerging threats and act quickly to neutralize them.
-
Incident management: If a breach occurs, the SOC coordinates a swift and effective response, minimizing damage and reducing recovery time.
Put simply, a SOC helps ensure your business is always protected, no matter what cyber threats are out there. And though it sounds like a luxury only the biggest corporations can afford, SOCs are now more accessible for businesses of all sizes, offering everyone a stronger layer of defense.
How to build a resilient business
The key to minimizing your risk is preparation. Not just reacting to threats but creating a proactive strategy that reduces vulnerabilities and ensures faster recovery. Here’s how to get started:
1. Adopt a SOC-driven approach
Having a dedicated SOC behind you is one of the most effective ways to ensure your cybersecurity is active 24/7. By leveraging the power of skilled analysts, automated tools, and real-time monitoring, a SOC creates a solid foundation for threat management.
2. Invest in EDR and ITDR tools
Think of endpoint detection and response (EDR) as a critical line of defense. It continuously monitors your devices—like laptops, servers, and workstations—for suspicious activities.
And identity threat detection and response (ITDR) focuses on protecting your employees’ digital identities. With hackers increasingly targeting weak or stolen credentials, ITDR identifies and neutralizes unauthorized access attempts.
Combining EDR and ITDR with a SOC can radically upgrade your threat detection and response capabilities.
Example of ITDR report flagging a session hijacking attempt from Huntress
3. Educate your team with security awareness programs
Cybersecurity isn’t just IT’s job—it’s something everyone in your organization needs to be part of. That’s where good security awareness training (SAT) comes in. It helps employees spot scams, avoid phishing, and act as your first line of defense.
Take Huntress Managed SAT, for example. It offers fun, bite-sized training episodes created by cybersecurity experts to tackle real-world threats they’ve observed in the wild. Plus, it includes phishing simulations to test employees safely. If someone falls for a simulation, they’ll get helpful feedback on what to watch for next time. It’s all about keeping your team informed, prepared, and ready to handle potential threats.
With Huntress Managed SAT, after a phishing scenario compromises a learner—like this example asking recipients to execute malicious commands—they're immediately prompted to complete their Phishing Defense Coaching
4. Develop an incident response plan
This is your roadmap for what to do when an attack happens. Your plan should outline:
- Team roles and responsibilities
- Steps to contain and respond to breaches
- Communication protocols for stakeholders
If you lack an in-house IT team, you should work with a managed service provider (MSP) to ensure your business is ready to respond quickly.
Proactive cybersecurity is a smart investment, not a wasteful expense
Cybersecurity doesn’t just protect you from attacks—it creates opportunities. Customers trust businesses that take security seriously, giving you a competitive edge in the market. Here’s how acting now can pay off:
- Reduce downtime and inefficiencies
- Avoid legal, reputational, and financial pitfalls
- Build customer trust and strengthen brand loyalty
Take the first step to resilience today
The cost of ignoring cybersecurity risks is simply too high. Identify your vulnerabilities and explore cost-effective solutions like Huntress Managed EDR and Huntress Managed ITDR. Purpose-built for our human-led SOC, these tools deliver around-the-clock protection through seamless integration of our proprietary technology and our expert-led teams. Because our tech and our people work as one, you get fast, accurate threat detection, response, and remediation.
To dive deeper into the hidden costs of cyberattacks, download The True Cost of a Cyberattack and learn more.
Hackers won’t wait. Neither should you. Start your free Huntress trial and secure your business before an attack strikes.