Cyberattacks can be flashy. Zero Day exploits, massive data breaches, and ransomware with newsworthy names steal the spotlight. But here’s a reminder for all the cybersecurity pros out there: common, run-of-the-mill (some might even say boring) tradecraft is always trending for attackers.
Most threat actors don’t need fancy tradecraft. Techniques like brute forcing, VPN compromise, or credential theft might seem overrated, but they get the job done for attackers. Don’t underestimate their impact on your environment because these tactics continue to pay off for attackers and are often subtle enough to slip by undetected.
“Don’t worry about the zero day and the black swan events, because there is very little you can do. Instead, do the basics right. The boring and routine tradecraft is what 99% of attackers do. Attackers copy and paste from playbooks and do the same thing every time, and that gives us a defensive opportunity to neutralize and stop them,” says Dray Agha, Senior Manager, Security Operations Center, EMEA.
In a recent Tradecraft Tuesday episode, “The Most Boring (Not Really) Tradecraft Tuesday Ever,” Dray Agha and Anton Ovrutsky from our 24/7 Security Operations Center (SOC) shared their insights on the no-frills techniques threat actors use on repeat. Check out highlights below and learn why boring (but not really!) tradecraft is one of the biggest security risks to your business.
Why threat actors love basic tradecraft
Most often, threat actors chase efficiency and profit above all else. The common hacking techniques we see attackers use are:
Simple: Many basic tactics exploit human error or common misconfigurations
Consistent: These methods are reliable and usually give predictable results
Stealthy: Many of these techniques blend into the noise, making them harder to detect
Low-cost: They’re accessible and don’t require nation-state-level resources
While convenient for attackers, common tradecraft is a truly pervasive challenge for defenders.
“Assume nothing. If you think something is configured a certain way in your network, test your assumptions. All of this is complex. It sounds pretty easy, but if you are in charge of a production network with different functionalities, requirements, compliance regulations, and users, this stuff is hard,” says Anton Ovrutsky, Principal Threat Hunting and Response Analyst at Huntress.
Common tradecraft, complex threats
Let’s dive into the tradecraft we see attackers use around the clock. These tactics might not seem exciting, but they are anything but harmless for your business.
Brute force
Let’s be honest. Brute forcing doesn’t have the clout of a shiny new zero day exploit, but it’s effective and accessible with little effort. And that is what matters most to opportunistic threat actors seeking easy wins.
We track millions of endpoints and identities 24/7, so we see a lot of brute force activity, including:
- Successful brute force attacks
- Failed attempts from:
- Non-existent user accounts in the targeted network
- Password errors
Unfortunately, from a defender’s perspective, brute force attacks are surprisingly easy to gloss over. Here’s why:
The speedy persistence of brute force attempts fills up Windows endpoint event logs, causing them to roll over every few minutes. This can easily mask not only brute force attempts, but also other attacker shenanigans happening in your environment.
Brute force attempts blend into activity from legitimate tools like vulnerability scanners and network management or inventory tools
Knowing how to quickly spot brute force attempts is critical to preventing attackers from reaching their targets.
What you can do:
Don’t rely on IP geolocation deny-listing. Attackers are constantly spinning up new ways to get around this.
Use Huntress Security Information and Event Management (SIEM) to catch brute force attempts quickly and secure logs for SOC analysis
VPN compromise
“We see too much VPN compromise, more than we'd like to see. And in many cases, we don’t have evidence to support that the threat actor landed on the appliance via some kind of zero day,” says Ovrutsky.
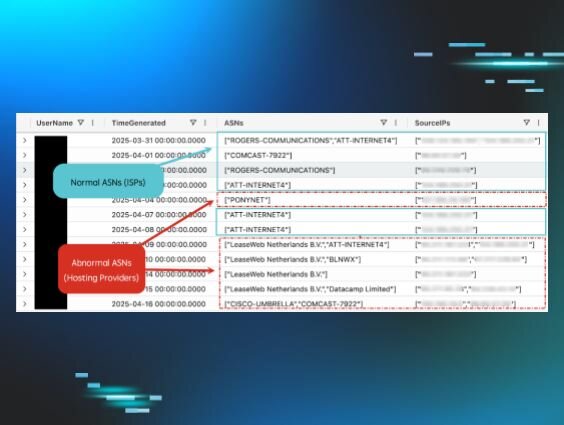
So what’s the driver behind widespread VPN compromise? Plain and simple tradecraft like stolen credentials, appliance brute force, or disabled MFA accounts are consistent culprits.
More alarmingly, we’ve started to see attackers level up their VPN game with:
- Logins from malicious IP addresses that don’t fit the normal user authentication patterns
- Modifications to the VPN appliance, like the firewall policy, to allow ports that weren’t previously allowed
- Adding users for persistence
Carefully tracking common tradecraft might not always be thrilling, but it is essential for understanding and detecting changes in tradecraft over time.
What you can do:
Add additional security layers to VPN appliances like MFA and time-of-day login restrictions, especially for admin accounts
Make sure unused accounts are removed from the VPN appliance
Patch early, patch often
Tunneling
Think tunneling is boring? Not a chance! Attackers need persistence to snoop around your environment without setting off alarms, and tunneling is often the best option.
Spoiler alert: it gets dicey quick, because attackers abuse legitimate functionality like SSH and Ngrok, which makes detection squirrely.
Tunneling also lets attackers bypass perimeter controls like firewall configurations that you’ve set up and audited to a tee.
Tunneling isn’t glamorous tradecraft, but it is extremely impactful when attackers use it with bad intent.
What you can do:
Stay alert to signs of malicious endpoint activity with Managed Endpoint Detection and Response (EDR)
Credential access
Credential theft is bread-and-butter tradecraft for attackers. Logging in as a trusted user makes it harder to get caught. If admin credentials are reused across endpoints, attackers can move freely in your environment, and a major intrusion is just a matter of time.
Credential theft doesn’t require creativity or innovation. We constantly shut down attempts at unauthorized credential access, including from well-known open-source, post-compromise credential theft tools like Mimikatz.
But deviations from the norm, like these examples below, are when credential theft gets spicy:
Abusing password storage tools like Xenarmor to collect a boatload of credentials at one time
WiFi password theft from the host
While these techniques aren’t new, they’re showing up more often across targeted environments, and we’re tracking these trends.
What you can do:
Remove local administrator access from workstations where there’s no business justification
Segment your network to minimize lateral movement with stolen credentials
Identities are the new perimeter, so set up Managed Identity Theft Detection and Response (ITDR) to catch early signals of credential theft and abuse
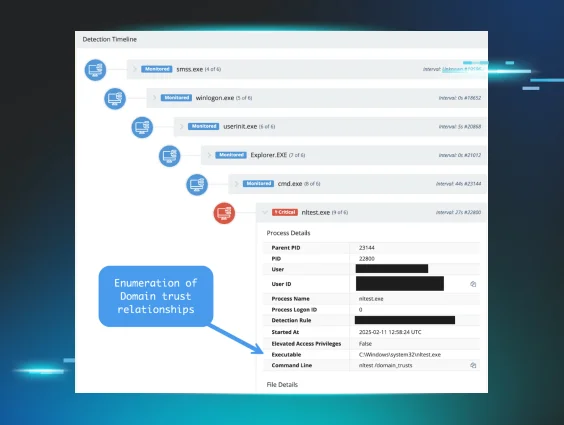
Lateral movement
“Threat actors do lateral movement in the same way, every time, with the same tools and techniques. They’re never interesting until they are,” says Agha.
Lateral movement is the point where attackers dig deeper into your environment. Once an attacker breaches your perimeter, and even worse, has admin credentials, there isn’t much friction to put the brakes on their attack plans. We see two types of lateral movement:
Abuse of legitimate Windows functionality like RDP or PsExec
Windows protocols wrapped around hacking tools like Impacket or CrackMapExec
Disappointingly, we don’t often see threat actors fumble lateral movement attempts.
“I wish we saw a lot more failed attempts at lateral movement, like the workstation doesn’t recognize the login, the time of day isn’t correct for a login, or the password doesn’t work. Unfortunately, we just don’t see that,” Ovrutsky says.
What you can do:
Toughen up your Windows environment and remove communication channels that aren’t vital for operations
Strategize how and what admin accounts are used for
Use Managed EDR to detect sketchy lateral movement or privilege escalation attempts
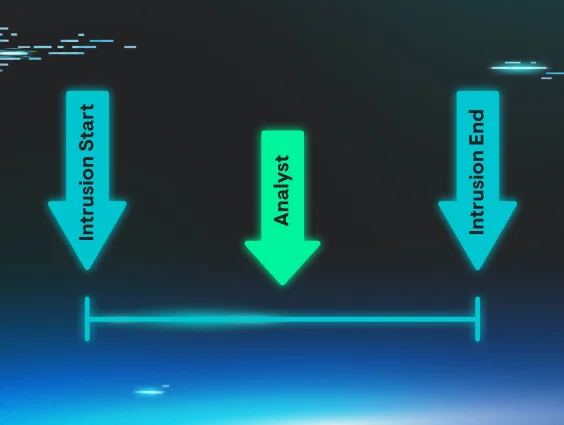
Don’t sleep on a security strategy that flags intrusions early, before attackers start moving around your network.
Level up your defenses now
Basic doesn’t mean powerless, not for attackers, and certainly not for your defense playbooks. No tactic is too common to prioritize and master. You’ll stay miles ahead of attackers betting on gaps they hope you’ve ignored.
Remember, not all cyberattacks are headline-worthy, but that doesn’t mean they’re harmless. Stay sharp, stay curious, and keep your defenses tight.
Don’t tackle boring tradecraft alone. Get the experts behind the wheel of a managed security solutions approach with a Huntress free trial.