Cybercriminals are some of the hardest working people around. For those of us who aren’t among the criminally inclined, a 40-hour work week is more than plenty. But not them. For hackers, there’s no such thing as 9 to 5. They’re hustling all day, even when the rest of us are asleep. Especially when the rest of us are asleep.
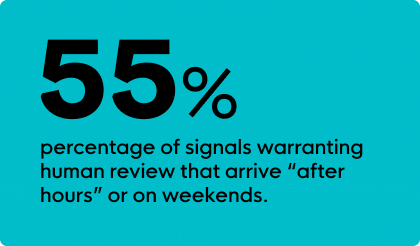
Huntress’ internal research has revealed:
- >50% of signals that warrant human review occur during standard business hours (e.g., Monday to Friday, 8am to 6pm)
- 55% of signals warranting human review arrive “after hours” and on weekends
As employees now embrace both remote and hybrid work, endpoints—such as laptops, desktops, and tablets—are proliferating. That means there are now more devices vulnerable to attack, expanding entryways for cybercriminals to access data. That’s why it’s vital that small- and mid-sized businesses (SMBs) adopt endpoint detection and response (EDR) solutions.
Before we dive into the ideal solutions for SMBs, let’s first look at the challenges that can accompany some EDRs.
The Challenges of an Unmanaged EDR
When it comes to EDR solutions, there are two options—unmanaged or managed. Unmanaged EDR solutions monitor and analyze endpoint activities, and when something suspicious is detected, your in-house IT teams can take action accordingly. They’re great against cyber threats, but that’s assuming you also have the manpower, resources, and know-how to remediate threats when one strikes.
Unless you have your own team—or at least one knowledgeable person on staff—who can consistently monitor the security of your systems, a managed EDR has to be your answer. This is particularly true for SMBs that may not always have the budgets, infrastructure, or capabilities to support the rigorous demands of an unmanaged EDR, such as:
- Tending to frequent alerts
- Dedicating staff to monitor activities
- Hiring and retaining cybersecurity talent
An Unmanaged EDR Can Be Loud and Exhausting
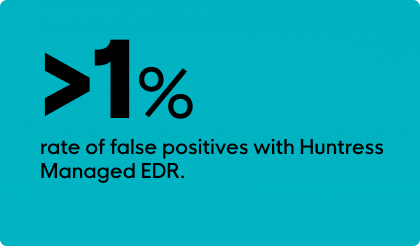
Unmanaged EDR solutions can be quite “noisy.” Being a vigilant solution, they’ll send out regular alerts, leaving it up to your internal staff to decide whether they’re worthy of attention. This can be notably irksome when deciphering false positives, which can lead to confusion and time wasted. Essentially, if you lack the in-house expertise to parse which notifications to focus on and which to disregard, you’ll succumb to a condition known as “alert fatigue.” It’s inevitable. You’ll become sick and tired of checking constant alerts, and ultimately, due to sheer weariness, you might inadvertently let some malicious threats pass through. And that’s never good.
SMBs Have Limited Time and Resources, and Cybercriminals Know This
It’s a familiar tale these days to hear SMBs having to do more with the same, if not less, budget. Even while purse strings might be getting tighter, cyber threats are propagating. Employing an unmanaged EDR still requires an IT team or in-house expertise, which can get pretty costly, pretty quickly.

In fact, largely due to the time, money, and resources needed to build an internal cybersecurity infrastructure, it’s become a common phenomenon for SMBs to forgo necessary investments in robust cybersecurity products and people. Unfortunately, this kind of oversight only leaves them open to a world of hurt in the near term, as tireless hackers are becoming far more aggressive in targeting smaller businesses.
A Managed EDR is Working, Even When You’re Not
For SMBs, cyber insurance often stipulates they must have an EDR in place to mitigate potential risks, and as a result, an unmanaged EDR is an easy solution to "check the box." At Huntress, we recognize EDRs as valuable tools, but to maximize their value, they must be placed in the right hands. If you have plenty of hands to spare, then you’re among the lucky few. However, if you don’t have the extra bodies necessary to manage your EDR, it can become nonstop tedium instead of an effective solution. That’s because an unmanaged EDR solution simply flags suspicious activities, putting the burden of response and remediation on your own people.

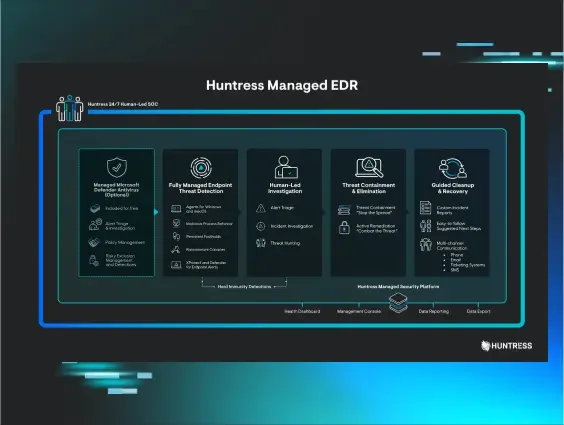
On the other hand, a managed solution, such as Huntress Managed EDR, utilizes human cybersecurity experts who can take care of that heavy lifting for you. Our team works around the clock to look out for any threats that our EDR tech flags. And we don’t stop there—we provide actionable insights, remediation guidance, and even single-click fixes when we detect something.
A Managed EDR Can Help Solve for the Shortage of Quality Cybersecurity Talent
Finding quality cybersecurity talent has become a Herculean task. There are currently millions of cybersecurity roles going unfilled. And even if you can recruit the best candidates with the right skill sets, can you afford to pay them the salaries they can justifiably command?
Huntress Managed EDR is backed by our 24/7 Security Operations Center (SOC). It provides everything you need in one place, and it delivers the backing of human analysts with up-to-date knowledge of the latest threats.
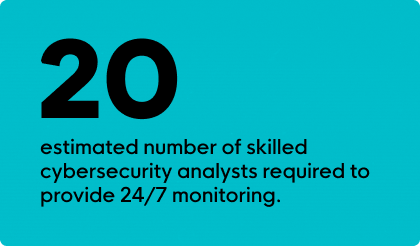
We estimate it takes at least 20 skilled analysts to provide 24/7 monitoring capabilities. Huntress Managed EDR takes these staffing and resource limitations off your plate, as there’s no need for you to invest heavily in building your own internal team of experts. It’s easy to deploy and simple enough for even the most junior-level talent to use.
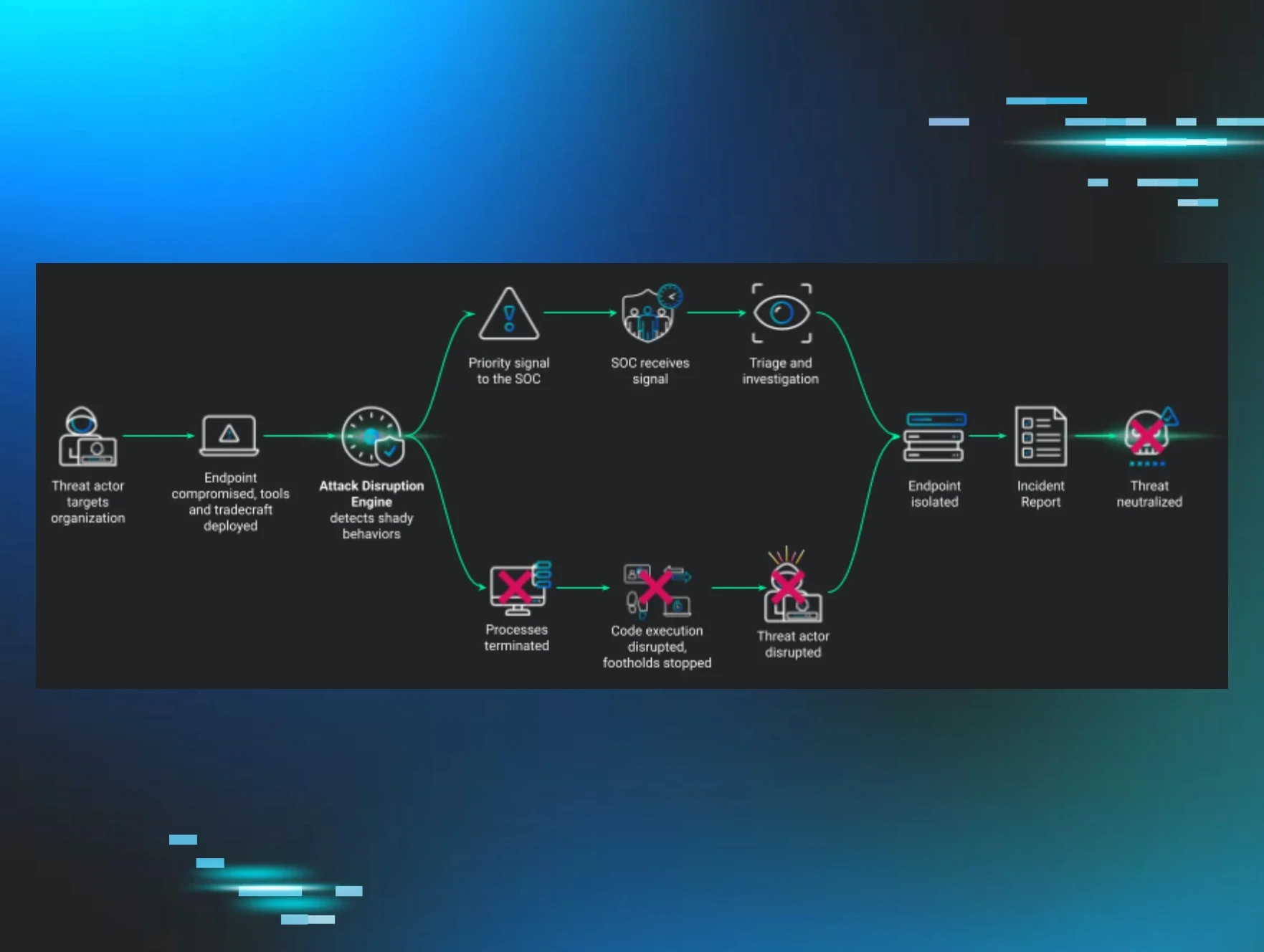
Since cybercriminals don’t sleep, they’ll find the most inconvenient moments to attack. That’s why our continuous monitoring of process executions and associated metadata makes it harder for them to hide. When a real threat is detected, our SOC investigates it and creates a unique incident report that offers easy-to-follow remediation steps that you can typically execute in just one click.
Without a Managed EDR, Threats Can Linger, Longer
If humans aren’t monitoring and managing your security 24/7, cybercriminals have plenty of time to attack before investigation and response begin. Most attacks can go days before they’re discovered, with some going as long as months before anyone notices. Huntress Managed EDR monitors malicious processes to build a comprehensive view of attacks as they happen, in real time. In 2023, Huntress SOC reported threats within one hour of being identified.
With sources claiming the average ransom demand in 2023 was as high as $1.62M, investing in a managed EDR should be a no-brainer for SMBs. It’s an excellent solution to offset the steep price tag affixed to a cyberattack. In turn, it allows you to reallocate budget as needed to other areas of your business.
And remember “alert fatigue?” Nearly 75% of the time a threat is identified, Huntress analysts can investigate and take action without our partners needing to do anything on their end, which means you can continue to focus on business without needless interruptions.
Cybercriminals might be among the hardest working people on the planet, attempting to breach systems at all hours of the day. But that’s why Huntress works harder, delivering 24/7 human-led cybersecurity for the SMBs that need it most.
Try Huntress Managed EDR for Yourself
Huntress Managed EDR is rated the #1 EDR for SMBs for the seventh quarter in a row, according to G2 users. That's because we're built to be easy on your team and hard on hackers. Try the top-rated EDR for yourself with a free trial.