“MAJOR ANNOUNCEMENT,” “GAME-CHANGING NEWS,” and “HUGE DEAL” have become common terms thrown around in the past few weeks to build excitement around…bundles. Not a bundle of joy, like a newborn baby, but a bundle of products and services from the same vendor. Microsoft has arguably been the champion of the almighty bundle for many years with its Microsoft 365 suite of products. Now, other vendors, like Kaseya's K365, are trying to replicate that strategy, offering a bundle of their IT products, even including their cybersecurity products into the mix.
Bundles Include Things You Don’t Want
Have you ever picked up beer for a barbecue? If so, perhaps you were swayed by a variety pack for $16, hoping to get the best beers the brewery makes. Breweries love variety packs because they can include the less popular beers by bundling them with their marquee offerings. This is why when you buy one of those mixed cases you often realize that out of the 12 beers, three are terrible. Effectively, you end up paying $4 for three beers you didn’t want. That’s exactly how massive bundles that involve IT services with some cybersecurity work. While they appear to offer value, they often include services that MSPs and other organizations may not need or want, inflating their perceived value without delivering real benefits. And unlike beer, where you can toss out the ones you don’t like (or pawn them off on your friends), you’re stuck with a cybersecurity solution that doesn’t meet your needs.
Perception doesn’t equal reality with these super SKU bundles that focus on giving you the feeling that you’re getting a super-sized value. However, each part of the bundle rarely offers a similar value to a leading standalone solution. That’s why they’re bundled in the first place. It’s an effective way to sell you something you wouldn’t have otherwise bought on its own. Ask yourself why these services aren’t worth selling individually. Often, it’s because they don’t hold enough standalone value or competitive edge. Including them in a bundle disguises their lack of demand and usefulness, forcing you to pay for unnecessary services.

You Get What You Pay for with Low-Value MDRs
With small and medium-sized businesses possibly facing utter ruin from a cybersecurity incident, does it make sense to choose a less robust solution because it “comes in the package”? Many managed detection and response (MDR) services included in these bundles fall short of providing real value, creating several significant problems for MSPs.
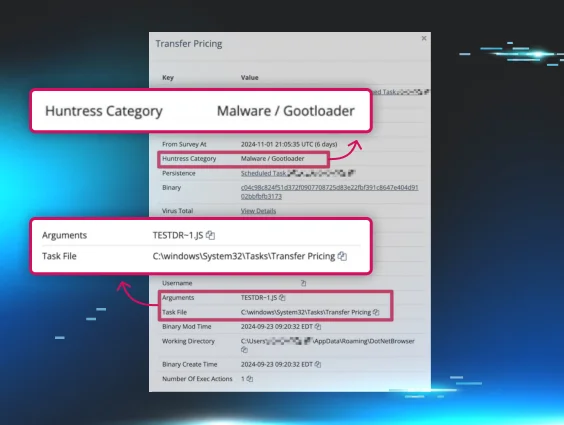
- Aggregating and Regurgitating Alerts with Little Context: Instead of filtering and analyzing data to provide actionable insights, subpar EDR and MDR cybersecurity solutions flood your dashboard with raw alerts. This approach doesn’t aid in threat detection and response, and it’ll overwhelm your team with false alerts and wild goose chases.
- Very Noisy: Unmanaged EDR and MDR solutions can be very noisy, generating numerous alerts that can distract you from real threats. The constant barrage of alerts can lead to “alert fatigue,” where significant threats might be overlooked because they’re buried under a pile of less critical notifications.
- Requires Expertise to Action: Even with all the alerts provided, acting on them requires a high level of expertise. Many IT and security teams might need more in-house capabilities to interpret and respond to these alerts effectively, necessitating additional training or even hiring specialized personnel. This increases operational costs and complexity, detracting from the supposed benefits of the bundled solution. In short, it adds work to your plate instead of taking it away.
Invest in Those Who Invest in Cybersecurity
In the rapidly evolving world of cybersecurity, there's a stark difference between companies genuinely committed to security and those just dabbling. It's not enough to be aware of the latest threats—true cybersecurity providers go beyond, aiming to be predictive rather than just reactive.

To be predictive, a company must play a completely different game. This involves teams of forward-looking researchers and top-tier threat intelligence experts who not only understand the entire threat landscape but also understand how defenses are evolving and how to counter new threats effectively. It's about seeing not just today's threats but anticipating tomorrow's challenges, and adjusting your strategy to get ahead of them.
You can easily spot these proactive and predictive companies. They regularly release in-depth blogs, conference presentations, and white papers that delve into tradecraft, evasive techniques, trend analysis, and their unique company culture. These are mission-focused cybersecurity companies at the forefront of innovation.
On the other hand, IT software solution companies that push bundles don't quite measure up. Despite their presence in the market, they lack the depth and commitment necessary to lead in cybersecurity. Their strategy often relies on acquisitions and usually follows the same pattern: the talented security experts and product developers leave once their contractual obligations are fulfilled. Betting on these companies for their cybersecurity capabilities is essentially betting against their future success.
Choosing a cybersecurity provider is more than just a decision—it's about securing the future. True leaders in the field demonstrate their commitment and expertise continuously. When evaluating options, look for those who aren’t just keeping up but are setting the pace in cybersecurity.
Forget the Bundles. For Real Value, Choose a Tailored Solution.
While the idea of a comprehensive, all-in-one solution super bundle may initially seem attractive, MSPs and other organizations need to consider the potential downsides carefully. Bundles often assign value without providing real value, including services that might not be necessary or effective.
Subpar MDRs can overwhelm you with noise and require significant expertise to manage. And specific components may fall short compared to more specialized solutions. By choosing more tailored, adaptable solutions, MSPs can better meet the specific needs of their clients, maintain operational efficiency, and stay competitive in the dynamic cybersecurity landscape.