It’s been widely understood and accepted for some time that a critical component of surviving a cyberattack is to have a solid, tested business continuity and disaster recovery (DR) plan that includes offline backups. This DR plan should include verification of backups, as well as regular testing to ensure that your business can effectively recover using those backups.
Verifying the backup process is paramount. Even as far back as the late 1990s, we saw recovery tests where the backup tapes were found to be blank because the process was not verified and the tapes were shipped off for storage. Even with today's backup disaster recovery (BDR) devices, we know of situations where drives were accidentally excluded from being backed up.
The Importance of Backups
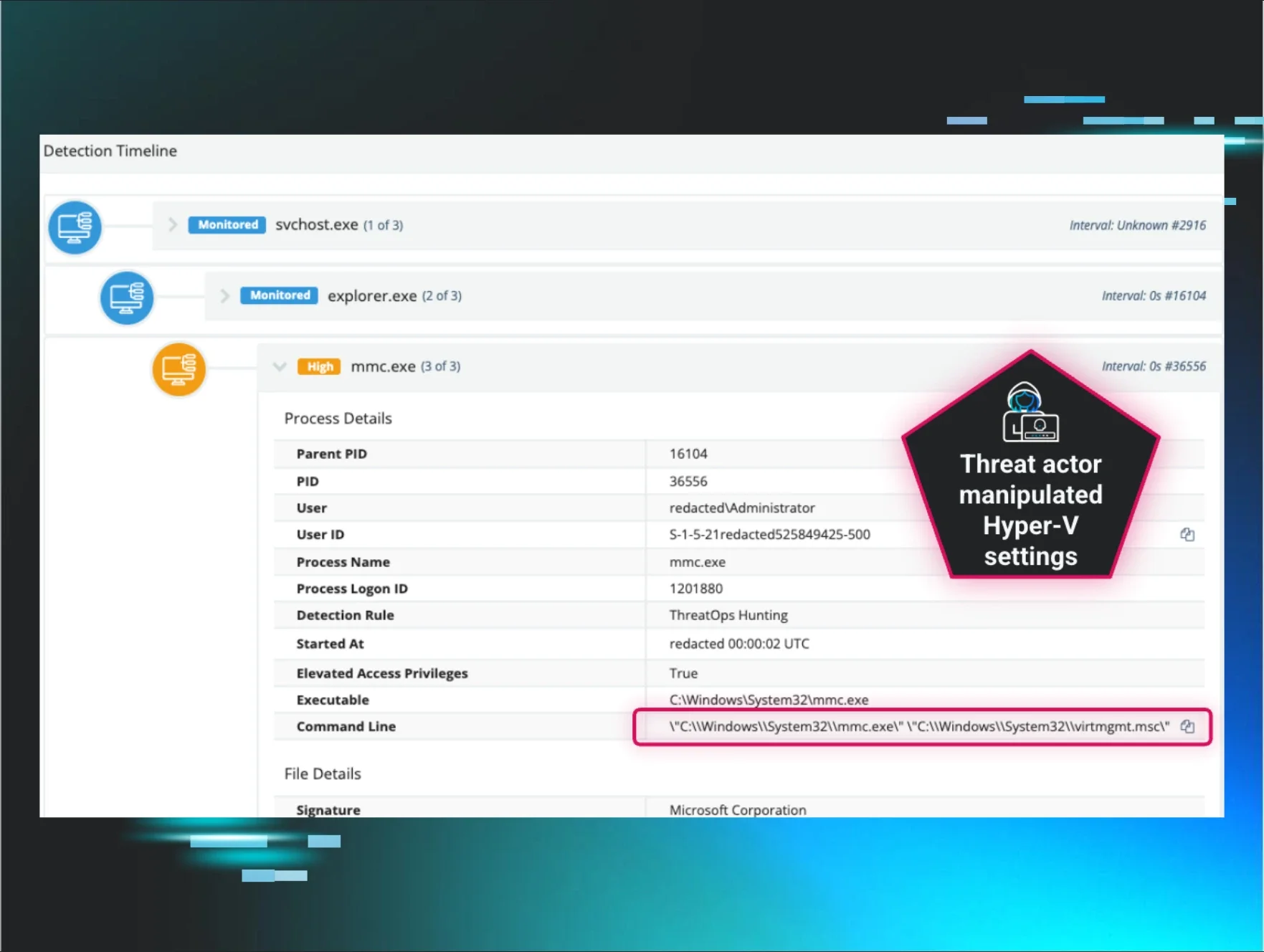
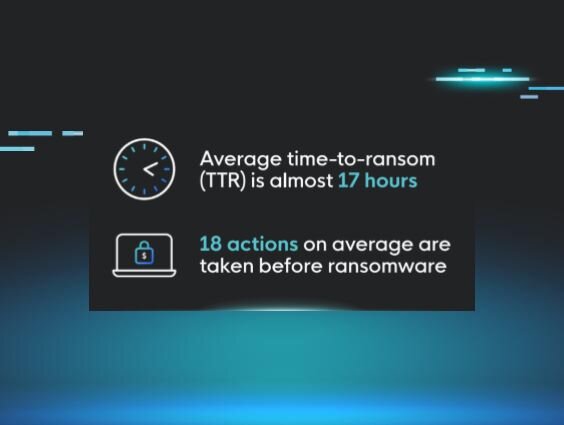
Ransomware attacks regularly and clearly demonstrate the importance of backups, particularly because threat actors actively target not only backups but also the administrator’s ability to restore systems. The commands to achieve this were originally typed in manually by the threat actor, and later included in batch files and scripts.
Once we saw the advent of “Ransomware-as-a-Service” (RaaS), these commands were embedded within the ransomware executable itself, launched before the file encryption process is started. After all, there’s really no point in encrypting files and leaving a ransom note if the target organization is left with the ability to quickly and easily recover, without paying the ransom.
With that being said, we have backups, so we’re good…right?
Not All Backups Are Equal
Well, having backups can be great for recovery and continuing to operate your business, although things didn’t go as planned for CommonSpirit Health recently. The DailyMail article reports that CommonSpirit Health was “hacked” on 3 October 2022, and more than 5 weeks later, as of the publication date of the article, Mr. Westin, a cybersecurity expert said,
“It can take months to fully recover data from a backup. It's been taking [CommonSpirit] weeks and will probably take them months to fully recover from it.”
Depending upon your organization and infrastructure, recovering from backups may not be an easy task, and as such, these activities need to be tested and practiced regularly in order to understand the actual recovery time that will be involved. In addition, how frequently are you running backups? The two key terms to really know are recovery time objective (how long will it take you to recover?) and recovery point objective (how much data can you afford to lose?).
In addition to testing your restore points related to RTO and RPO, multiple copies of the backup data necessary for a total solution. It’s usually referenced as the “3-2-1 rule” for backup. Three copies of your data, in two geographically different locations, with one stored in a location that is not accessible from the regular environment like cloud infrastructure or a disaster recovery site.
This allows you to have access to backup data to restore in case the whole environment and user access are compromised. It is also important to monitor backups for success and failure to help maintain a healthy restore chain. One of the components of monitoring your backups is the size. Not the size of the individual backup but total storage size. For example, if your backups equal 2.5 TB one day and the next they are 500 GB, What happened? Did a malicious actor delete your backups so you can’t restore from them?
Let’s keep in mind, also, that having verified, offline backups and a thoroughly tested restoration process is not the be-all and end-all of incident recovery. In the face of a cyberattack, a root cause analysis (RCA) needs to be conducted in order to determine how the threat actor was able to gain access to the infrastructure in the first place so that those holes can be plugged. After all, a threat actor going after your backups involves more than just a threat actor going after your backups, because first, they need to gain access to your infrastructure.
Conducting an RCA will help you identify holes, weak points, and the efficacy of your security controls, and then allow you to shore up your defenses so that you have the breathing room to restore your business using your backups.