Happy World Backup Day!
This is a particularly special holiday for us at Servosity because backups are what we do. At the same time, there's a fairly good chance that you hate doing backups. Most people do—and to be fair, it's understandable.
Love them or hate them, a valid backup is the last thing standing between a hacker and her payday. It’s the perpetual, mundane task that you have to do. Kind of like laundry, but worse, right?
Sadly, ransomware and cybercrime are on the rise. Entire nations are threatening to deploy cyberattacks—and in all too many cases, they follow through on those threats. It’d be easy to believe that they only focus on other governments and high-profile businesses, but unfortunately, that isn’t necessarily the case.
Small and midsized businesses (SMBs) are at a disadvantage because they have fewer resources and staffing than more prominent companies—and hackers know that. They’re targeted more often because they have access to the same critical data that hackers seek—but because they lack cybersecurity resources, they’re more vulnerable.
But living in fear won’t save you. It’s just important to have a healthy awareness. We all have to link arms and stay educated so we can be prepared. Fortunately, there are things you can do to make sure that when ransomware hits, you and your clients are prepared.
Backup Best Practices
Keep these backup best practices in mind to be prepared if the worst-case scenario becomes reality.
1. Test Your Backups—and Test Them Often
You already know this one. It probably even hangs over your head day in and day out. You know you should be doing it more, but there’s always something more demanding at the top of the to-do list, right? So, you tell yourself you’ll do it later—but does later ever come? Or does it stay at the back of your head, haunting your peace of mind? Are you happy with the amount and quality of testing that your backups are undergoing?
Ideally, you want to test your backups every day. And I’m not talking about just looking over screenshots (more on that below). It goes without saying: the more thoroughly you test, the stronger and more secure your backups will be. The reality is you are only as safe as your weakest backup. The only way to get true peace of mind is with tested, valid backups.
No time to do this? You can always outsource the work to a vendor who can do it for you. For example—and this is admittedly shameless plug time—but at Servosity, our engineers do all the testing for our partners—every day, all of it. We keep busy with backups so you don’t have to. 😅
2. Follow the "3, 2, 1" Rule
It’s pretty simple. You need three copies of the data that is being backed up: the original, the primary (on-site) backup and an offsite backup.
That’s 3 copies, in 2 locations, with 1 being offsite.
3. Use Disaster Recovery (DR) Imaging, Not Just File Backup Solutions
File backup solutions are not designed to recover you from a disaster. They’re incomplete backups. Chances are you aren’t going to back up your entire C drive—and even if you did, you’d just get a ton of error messages from all of the constant changes you’re making to the drive.
File backup goes to the cloud, which sounds nice and simple until you can’t connect to the internet. You have to be able to download your data before you can access it, so without an internet connection, you don’t have anything. It also doesn’t contain your operating system, applications, preferences, etc.
With DR imaging, the internet is not required. When your client has been compromised, the last thing you want to do is leave the system online to download backups for the next several hours (or days, depending on the amount of data).
You’re also able to spin up in the cloud or locally as a virtual machine. This gives you the ability to recover without having to actually restore, which saves you loads of time. Your client is most concerned about how fast you can have them back up and running. Downtime is costly and, in some cases, such as for hospitals or doctor offices, can quite literally be a matter of life or death. With DR imaging, you can have them recovered and back to business as usual while you handle the technicalities of fully restoring.
4. Have a Separate Remote Monitoring Management (RMM) Provider
Single sign-on is convenient—but what happens if a hacker gains access to one of the accounts? They’ll be able to not only get on all of your clients’ machines, but also the ability to disable, delete and/or alter your backups.
You could end up accidentally enabling the next supply chain attack. They’re already going to target your backups—it’s just hitting the lottery when they’re able to compromise your backups and your RMM.
5. Enable Multi-factor Authentication (MFA) Everywhere
No, seriously. Everywhere—zero exceptions.
I know that end users detest MFA because of all the extra steps. I’ll even admit that I hate it because of all those extra steps. But if a few extra steps could potentially prevent a cyberattack, aren’t they worth it?
Sometimes people tend to get rushed or extra annoyed and just disable MFA, even temporarily—and that’s the weak spot a hacker is waiting to exploit. Even if you don’t get hacked during that specific session, once you have it disabled, it can be so easy to forget to reenable it.
We actually had a client this happened to. A technician temporarily disabled MFA on a particularly busy day and forgot to reenable it. Boom. The entire system was ransomed.
MFA annoyances are minimal when compared to recovering from ransomware.
6. Don't Rely on Screenshots
This one may make your eye twitch a little, but just hang with me.
Screenshot verifications are a load of bologna.
You're probably checking them every day. You see the little green circles, and occasionally, you even review the actual screenshots. As my toddler would say, “Green, go!” One glance over, and you can carry on with your more time-sensitive tasks.
It’s actually not uncommon for the more “cautious” MSPs to even have level one technicians manually review the screenshots. Even still, it’s just false security.
The part that most people don’t take into consideration is the screenshots are only showing the boot volume. Have you ever heard of anyone storing their important data on the boot volume? Probably not. 😉 So while it’s great that you can get the system booted up and running, that won’t really matter if the data isn’t there with it.
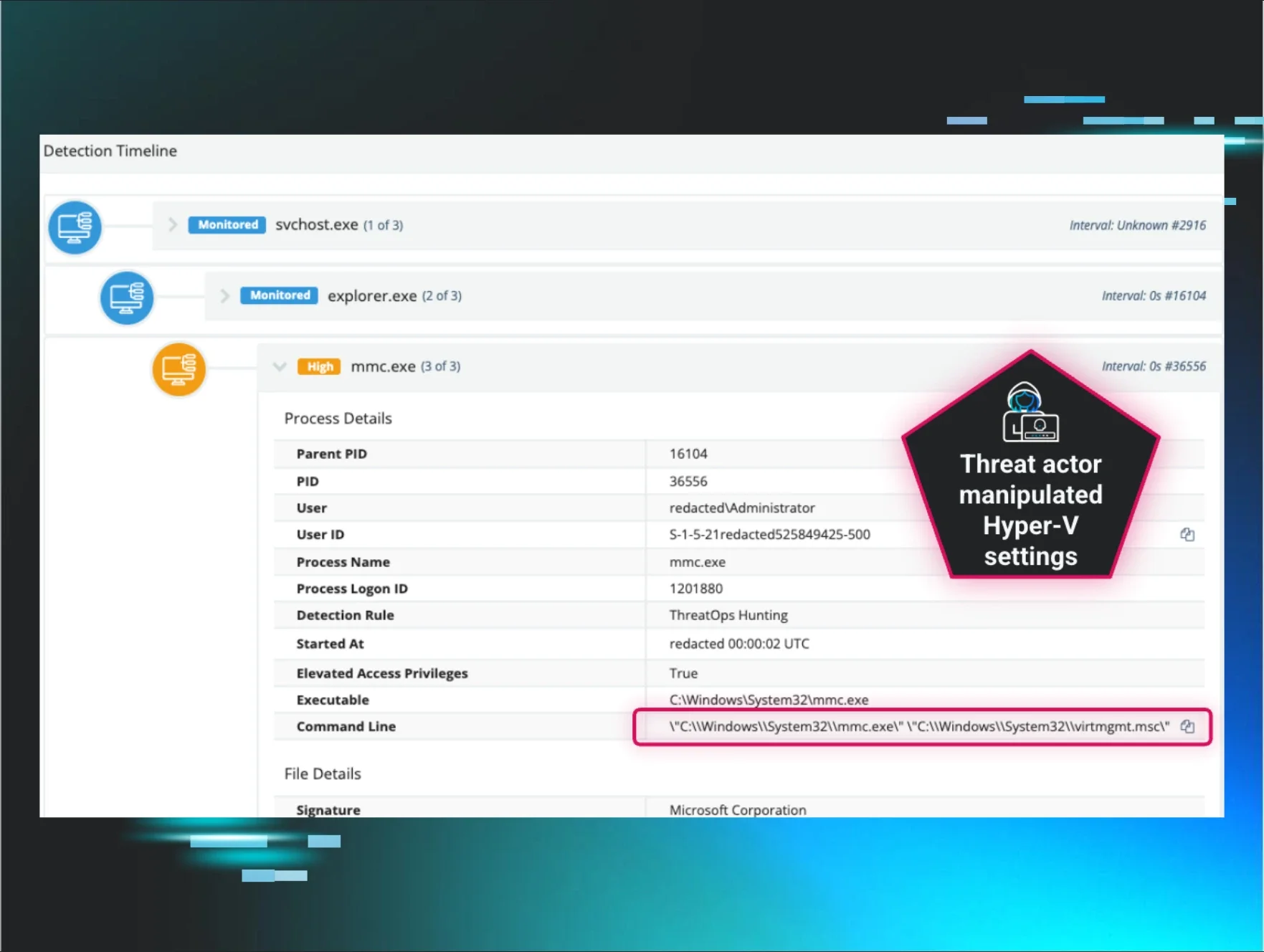
Hackers are infiltrating backups and are staying there, undetected, for months. Then, when they detonate the attack, you don’t have any accurate, valid backups—making it especially tempting to just pay the ransom.
7. Make Sure You're Storing in Truly Immutable Storage
Immutable storage is a relatively new term in the industry, but it’s quickly becoming a necessity. It’s a form of storing data that is completely unchangeable. You can’t delete it or alter it under any circumstances.
The problem is that not all immutable storage is actually immutable. With immutable storage being brand new to the industry, it’s easy to use loopholes and fine print. It’s easier to blur the lines between true immutable storage and mostly immutable storage.
Things to consider:
- Does a third-party firm audit the immutability?
- Is it entirely off-limits for everyone, including the vendor?
- Is the vendor willing to clarify the specifics of how they store your data?
If a third-party firm doesn’t audit the immutability aspect of the storage, then you have no way of really knowing if it can survive in the face of ransomware. Make sure your vendors are holding themselves accountable.
Plus, the reality is that if a vendor (or anyone at all) can still modify or delete it, it’s not true immutability. What if the vendor is compromised? The attackers can just do whatever they want with your backups. There can’t be any exceptions—not even for the vendors.
The tl;dr Dish on Backups
Huntress has a catchy saying: “Hackers gonna hack. Huntress gonna hunt.” Well, we’ve got our own version of that in honor of World Backup Day:
Hackers gonna hack. [.underline]Tested[.underline] backups bring you back. 😉
Threat actors work hard to bypass your preventive measures in your security stack. They don’t want their efforts to be in vain. As cybersecurity pros evolved their strategies and began to take backups more seriously, so did hackers—and now, targeting backups is part of their main attack plan.
With the right “backup plan,” all of the cybercriminal’s nefarious work will be in vain. You can just restore and go on about your day.
Don’t let the shady actors win.
Be the hero in your own ransomware story.
●●●
Servosity specializes in backup and disaster recovery. We make the MSP the hero in the fight against data loss and ransomware with tested backups, guaranteed.
If you'd like to assess your ransomware preparedness in terms of backups, check out our Security of Backups Checklist.
For more information about Servosity, call (800) 429-0500 ext. 1, email partners@servosity.com or visit servosity.com.