It’s a usual Tuesday morning, maybe you’re sipping some coffee or tea, when you get lit up with alerts. Systems go down. Your internal comms channels are in chaos, the people who use those systems are noticing something’s up, and your team’s looking for answers. At some point, someone clicked something they shouldn’t have, and now you’ve got ransomware locking down your network.
Great…now what?
See, every decision maker has a plan until they get hit with a cyberattack. Then you get to find out if your incident response plan actually works.
While this scenario might be hypothetical, attacks like this one happen to businesses of all sizes every single day. What really matters is how prepared you are to respond to an attack. Because if you don't have a tested, actionable incident response plan ready to set you and your teams up for success, all the fancy security tools in the world won’t help you deal with the fallout of a cyberattack. Everyone gets hacked—you can get over that. But plenty of businesses don’t recover if they can’t respond to the financial, reputational, or legal damages of an attack.
Improvising an incident response plan is no longer an option. So here are some ideas and resources to get you started building (or improving) your own.
Why bother with an incident response plan?
Hackers aren’t very picky. Sure, some have some loose ethical lines they won’t cross, but the VAST majority of businesses, big or small, are fair game. The approach of “it couldn’t happen to me” won’t cut it when the consequences could cost nearly $5M on average. But it’s not like it’s just your wallet at risk. There are regulatory consequences. Legal consequences. Reputational consequences. It’s one thing to lose some money—but it’s another thing to lose the trust of your customers.
Think of an incident response plan like preparing for a holiday meal. You can absolutely freestyle things in the kitchen if you want. You’ve cooked before. You know what people like. How hard could it be? Well, when the pressure’s on, and you only have one chance to get it right, you better hope things work out. A botched holiday meal might just mean some disappointed dinner guests and takeout. But in the case of a cyber incident, not having a plan might mean disaster.
Here’s what a solid incident response plan can do for you:
-
Reduce downtime: Fast threat containment limits operational and financial fallout.
-
Safeguard public trust: Well-orchestrated communication reassures customers or clients.
-
Enable faster recovery: Defined restoration steps bring services back online quickly.
-
Support regulatory compliance: Documentation and reporting requirements are met.
-
Minimize legal exposure: Decisions are made with legal counsel, reducing compliance pitfalls.
All businesses need an incident response plan because ALL businesses are potential targets.
What does an effective incident response plan look like?
Responding to a cyber incident involves, broadly speaking, a few key things: strategic decision making, communication, and technical precision. A successful response relies on the right people knowing their roles, timely escalation, and the right playbook for both business leaders and technical teams.
Business leaders
When things hit the fan, leadership is more important than ever. While the security and technical response to an incident aims to shut down threats and limit further damage, a business’ immediate and future standing lies in the hands of its leaders. This is what goes into it:
- Strategic choices: Top-level decisions on business continuity and reputation management.
-
Clear communications: Approving what’s shared with clients, regulators, and the press.
-
Regulatory navigation: Initiating data breach notifications, if required (think GDPR, HIPAA).
-
Coordination: Delegating outreach and support to affected customers and stakeholders.
Technical teams
While they’re not immediately concerned with reputation or financial losses, they’re the first responders who contain and clean up threats before things get worse:
-
Rapid containment: Isolating affected systems before threats spread.
-
Root cause analysis: Assessing the depth and extent of damage.
-
Restoration: Prioritizing restoring core systems safely and quickly.
-
Ongoing vigilance: Auditing accounts, reviewing logs, rotating credentials, and ensuring all software and tech are updated.
Don’t leave who does what to chance. A strong incident response plan spells out who covers every to-do, be it an executive priority or a technical action, so chaos and confusion can be avoided.
Beginning steps to incident response planning
Not every incident response plan is the same. Plenty of businesses have unique needs: specific regulatory concerns; individual team or regional considerations; varying customer or client needs; etc. But most incident response plans should follow the same general steps.
Here’s an example:
-
Damage assessment: Technical experts gauge the scope and nature of an attack. This drives decisions like whether to temporarily turn off affected systems or continue support in a limited fashion.
-
Rapid notification: Business leaders connect with legal counsel and cybersecurity insurers, while technical teams prepare to isolate affected endpoints or user accounts.
-
Communication begins: Approved scripts and templates are circulated, so consistent messaging is delivered.
-
Coordinated steps: Leadership focuses on “big picture” issues and legalities, while technical teams run through steps like containment, log auditing, or credential changes.
-
Restoration and recovery: Once the threat is dealt with, leadership oversees regulatory updates, and technicians deal with reducing the incident’s operational impact.
The plan before the plan
So, now you know what to do when things pop off—but that’s not all. Preventing an incident is always better than responding to one. But on top of that, ensuring you’re ready to implement your plan is just as important as having one in the first place.
These are some preparedness steps for when there isn’t an incident going down:
-
Practice your plan: Regularly run tabletop exercises so your teams know the plan by heart.
-
Clarify team roles: Make sure every member (technical and business leaders) knows their responsibilities and role during an incident response.
-
Backup everything: Audit your backups, perform restoration tests, and keep clean system images ready for rapid deployment.
-
Secure legal lines: Have insurance contacts and legal advisors identified and ready to contact.
-
Communication prep: Draft scripts for various scenarios, pre-approved by counsel, so you can act fast under scrutiny.
-
Evaluate surge capacity: Determine if you have the necessary IT resources or need third-party support on standby.
-
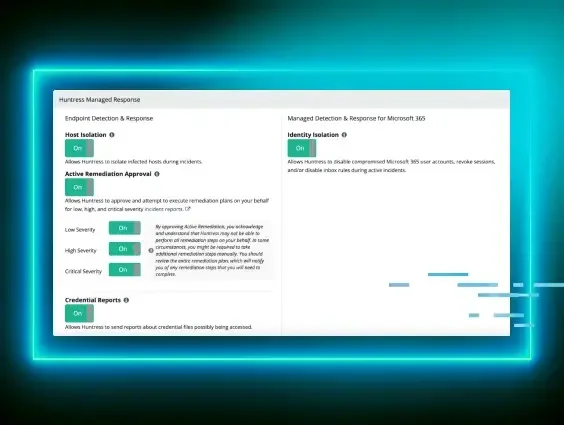
Monitor for threats: Utilize endpoint detection and response (EDR), identity threat detection and response (ITDR), and security information and event management (SIEM) to proactively identify threats before an attack happens.
It sounds like a lot of work for something that might happen, or might not be that bad. But by getting ahead of things, you reduce the risk of confusion and wasted time during a real-life incident.
Now it’s your turn: Make sure your incident response plan’s ready to go
Listen, your incident response plan isn’t some magical “break in case of emergency” tool. And it’s (hopefully) not just a PDF that gets lost in the ether of your documents folder. It can truly be the difference between a successful incident response and a total nightmare.
Whether you’re an IT leader in a massive enterprise, an MSP with clients of varying needs, or you’re protecting any kind of business, an incident response plan is a critical safety net. And while having one is necessary for modern businesses, they’re never completely done. As the threat landscape changes, so too do the needs of your plan.
So, whether you’re just creating your first incident response plan or looking to update your existing one, we’ve got plenty of resources to help. Check out our Incident Response Tabletop-in-a-Box for everything you need to test and optimize your plan. You can also watch our on-demand webinar, "Practical Incident Response Planning," to hear from our expert panel on the ins and outs of planning for the worst.
Hackers love it when they catch you unprepared—let’s make sure they’re disappointed.