Microsoft has come a LONG way with respect to security in the last decade. I really mean a LONG way. When I was at other vendors back in the day (I sound older than I am, but it really feels like forever ago), it was very easy to say, “Microsoft is not a security company” or “Microsoft causes all the problems, they can’t fix them.” That is no longer true.
I’m sure some of you reading this are triggered and can start thinking of all the things wrong with Microsoft. I’m not here to argue with you. What I am here for is to say that if you’ve invested in Microsoft tools (or someone else in your organization did), you are probably not getting your money’s worth today.
Like other security tools, Microsoft requires people, time, and expertise to manage—three things you could probably use more of. That is where Huntress can help. We are a Microsoft Verified SMB Solution, and our Huntress Managed Security Platform integrates with several key Microsoft Security tools.
Microsoft Defender for Endpoint + Huntress Managed EDR
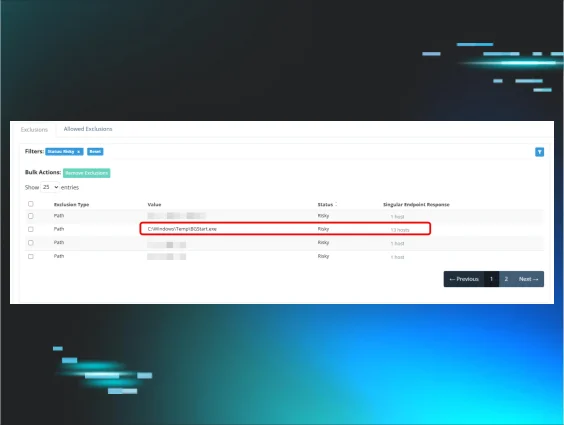
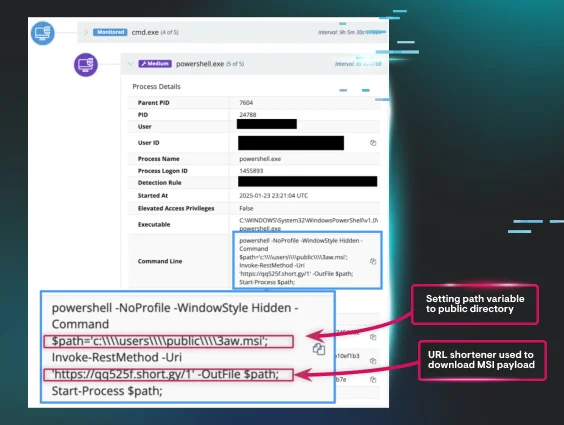
Defender for Endpoint (MDE) has been a Gartner Leader in Endpoint Protection Platforms (which includes EDR) for several years running. However, we speak to organizations all the time that have not taken advantage of Defender for Endpoint's EDR capabilities. Some simply don’t have the in-house expertise and bandwidth to get much value out of it. Others got it as part of a bigger Microsoft package and haven’t touched it. That is a lot of wasted potential. Huntress Managed EDR unleashes that potential. We supplement our EDR telemetry with additional insight from MDE. And like all Huntress solutions, it's backed by our 24/7 human-led SOC. Together, they create a defense that frustrates hackers. You can finally get the value of MDE and level up your security at the same time. And the best part? It’s free for Managed EDR users.
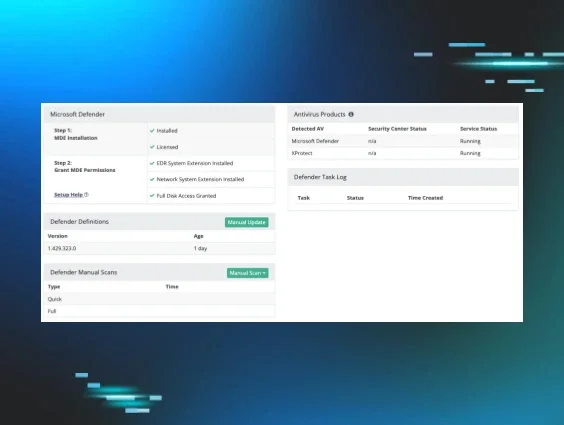
Microsoft Defender Antivirus + Huntress Managed EDR
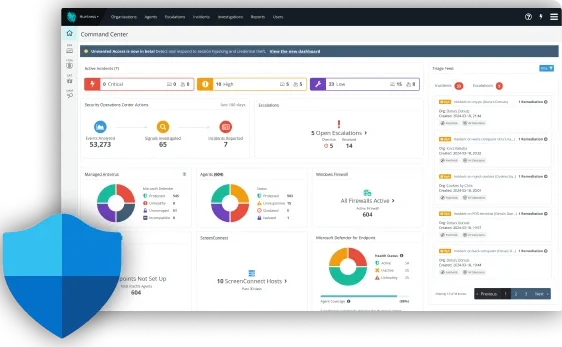
I’ve asked this question before, but I’m going to ask it again: Why Are You Still Paying for Antivirus? For many organizations, the free version of Defender AV is a better alternative to the antivirus you are likely overpaying for. Not only will you save money by swapping out your AV, but you will also likely be more secure. Huntress manages Defender AV as part of Huntress Managed EDR. This allows you to repurpose your budget to the areas that will make the biggest impact on your organization. With multi-tenant support from the Huntress dashboard, we centrally manage detections and events, monitor scans and protections, and execute remediation actions for all protected endpoints. So not only will you save money, you’ll save time by having us do the work for you.
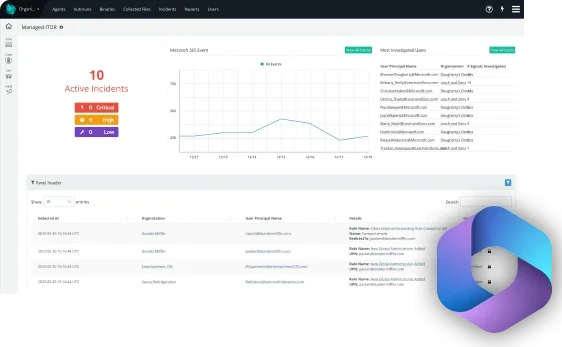
Microsoft 365 + Huntress Managed ITDR
Built for users of Microsoft 365, Huntress Managed Identity Threat Detection and Response (ITDR) is a fully managed identity protection solution that safeguards businesses against the inbound tidal wave of identity-focused tradecraft. It provides 24/7 managed detection and response for Microsoft 365—triaging alerts and notifying you of threats only when they’re designated truly malicious. With Microsoft Entra ID, Microsoft’s identity and access management suite, Huntress Managed ITDR takes in Risky User data to illuminate any weak spots in your security strategy and highlight risky behavior. Our experienced threat analysts monitor and respond in real-time to critical security threats like session hijacking, credential theft, malicious inbox & forwarding rules, account takeover, and business email compromise (BEC) attempts.
Microsoft + Huntress: Better Together
We are committed to making your Microsoft security tools come to life. That is why Huntress has become a Verified SMB solution within the Microsoft Intelligent Security Association (MISA), an ecosystem of independent software vendors (ISVs) and managed service providers (MSPs) that have integrated their solutions with Microsoft Security technology to help build the defenses of SMBs and MSPs against increasing and more aggressive cyber threats.