Don’t worry, this isn’t one of those “AV is dead” articles. I read that headline almost ten years ago—I didn’t believe it then, and I don’t believe it now.

Antivirus (AV) is still an important layer of endpoint protection and an overall cybersecurity strategy. However, it's been commoditized in recent years with minimal differences in protection efficacy from tool to tool.
The Plateau of Legacy AV Products
The commoditization of antivirus is reflected in AV vendor tests. For example, in the most recent AV-Comparatives test from June 2023, the variance between the top ten vendors’ malware protection rates only varied by 0.4%.
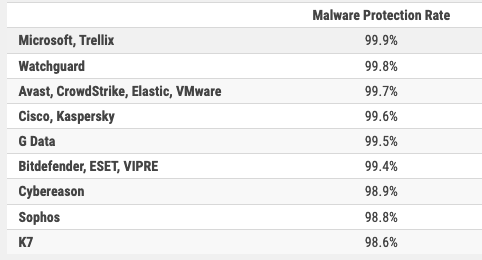
Source: AV-Comparatives Business Security Test March-June 2023
SE Labs, a lesser-known but highly respected assessment group, tested six vendors in their most recent Small Business Protection report in June. Five achieved a perfect protection accuracy score. In their Enterprise Protection report, six out of ten vendors received a perfect protection accuracy score.
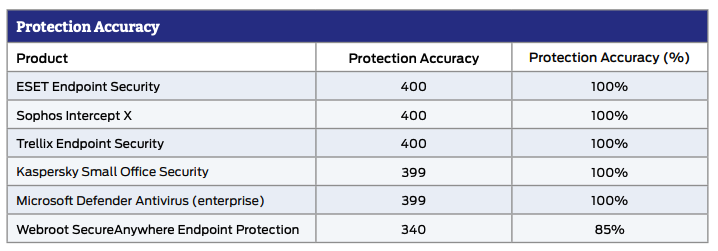
Source: SE Labs Endpoint Security Small Business Protection Apr-Jun 2023
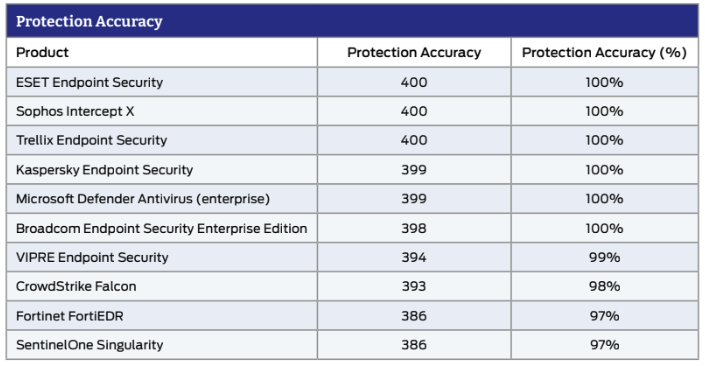
Source: SE Labs Endpoint Security Enterprise Protection Apr-Jun 2023
I used to work for an endpoint protection vendor, and I still love to geek out discussing why one tool got a 99.6% protection rating and another got a 99.8% protection rating. However, you have more important things to do with your time, and I doubt you’d ever notice the difference in protection in a real-world scenario.
So that begs the question: If endpoint protection is relatively similar across most AV vendors, what are the differences?
What Sets Endpoint Protection Products Apart From Each Other?
All endpoint protection vendors make promises, but there are three primary reasons to choose one AV tool over another:
- Management: Ease of use, amount of false positives, policy management, and deployment process
- Cost: The price you pay for the software and the ongoing time spent and expenses incurred managing it
- Endpoint detection and response (EDR) functionality: How well can the tool help you detect and respond to threats that evade automated AV detection, how easy is it to investigate suspicious activity
In their latest Magic Quadrant for Endpoint Protection Platforms (EPPs), Gartner said that “EDR should now be considered a mandatory capability” that “is now a common and mature feature of EPP solutions.” However, with that capability comes cost. “The biggest barrier to adoption of EDR tools remains the skills required to operate them and the increased total cost. On average, EDR capabilities add an extra 37% to initial costs, and adoption of EDR must be accompanied by investment in training to be effective.” This puts it out of reach for most organizations.
So how can these organizations save money, eliminate the burden of management, and get the EDR capabilities they need? Huntress is how.
Huntress Managed EDR with Managed Antivirus
Swap out your current AV for the free version of Microsoft Defender Antivirus, and Huntress will manage it as part of our Managed EDR offering. This allows you to repurpose your budget to the areas that will make the biggest impact on your organization.
If you haven’t looked at Microsoft Defender Antivirus in a while, you should revisit it. Microsoft is better than “good enough.” They are a consistent leader in the Gartner Magic Quadrant for Endpoint Protection Platforms and received a 5 out of 5 score from Forrester for Endpoint Telemetry.
With Huntress Managed EDR, Defender is even more valuable because you don’t have any management burden, and human experts monitor and investigate alerts around the clock. Even better, you get increased protection by combining it with the #1 rated EDR on G2, fully managed by our 24/7 human-led SOC.

Better protection at a lower cost, all headache-free. Does that sound appealing? If so, it's time to ditch your legacy AV.
Start Your Free Huntress Trial Today
Take Huntress Managed EDR (with Managed Windows Defender Antivirus) for a test drive and experience the power of endpoint protection, detection, and response backed by our team of human security experts. Start your free trial.