In early 2025, Huntress Security Operations Center (SOC) Analysts responded to an intrusion involving a critical market research company conducting business throughout the Fortune 50 and governments worldwide.
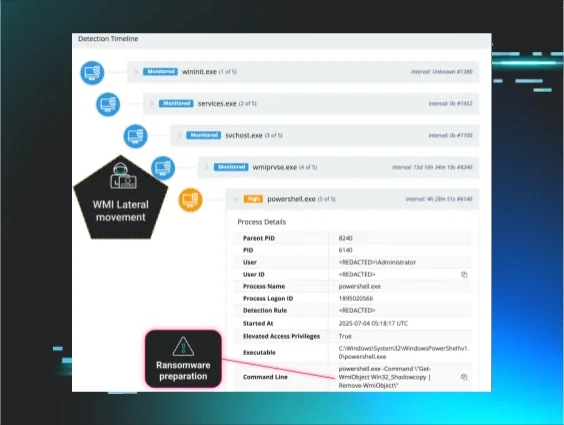
Shortly after the first alerts within the SOC, the Huntress Hunt and Response Team was alerted to potential activity, pointing to this being a targeted intrusion. We suspect this to be connected to state-aligned espionage actors.
This intrusion follows general industry trends in that it was mainly conducted via living-off-the-land techniques. This can make the ability to detect malicious activity difficult, as it will bypass traditional antivirus solutions and often endpoint detection and response (EDR) solutions as well.
Host 1: Server
The threat actor logged in to the server from a hostname uncommon with the environment’s naming convention.
The threat actor performed the following Enumeration commands, alongside many spelling errors, within minutes of logon to gather information about the environment, including recently remote interactive logged-on users, DNS Zone records, and mail exchange records within the organization. The host was isolated within minutes of the first execution to prevent further activity from occurring.
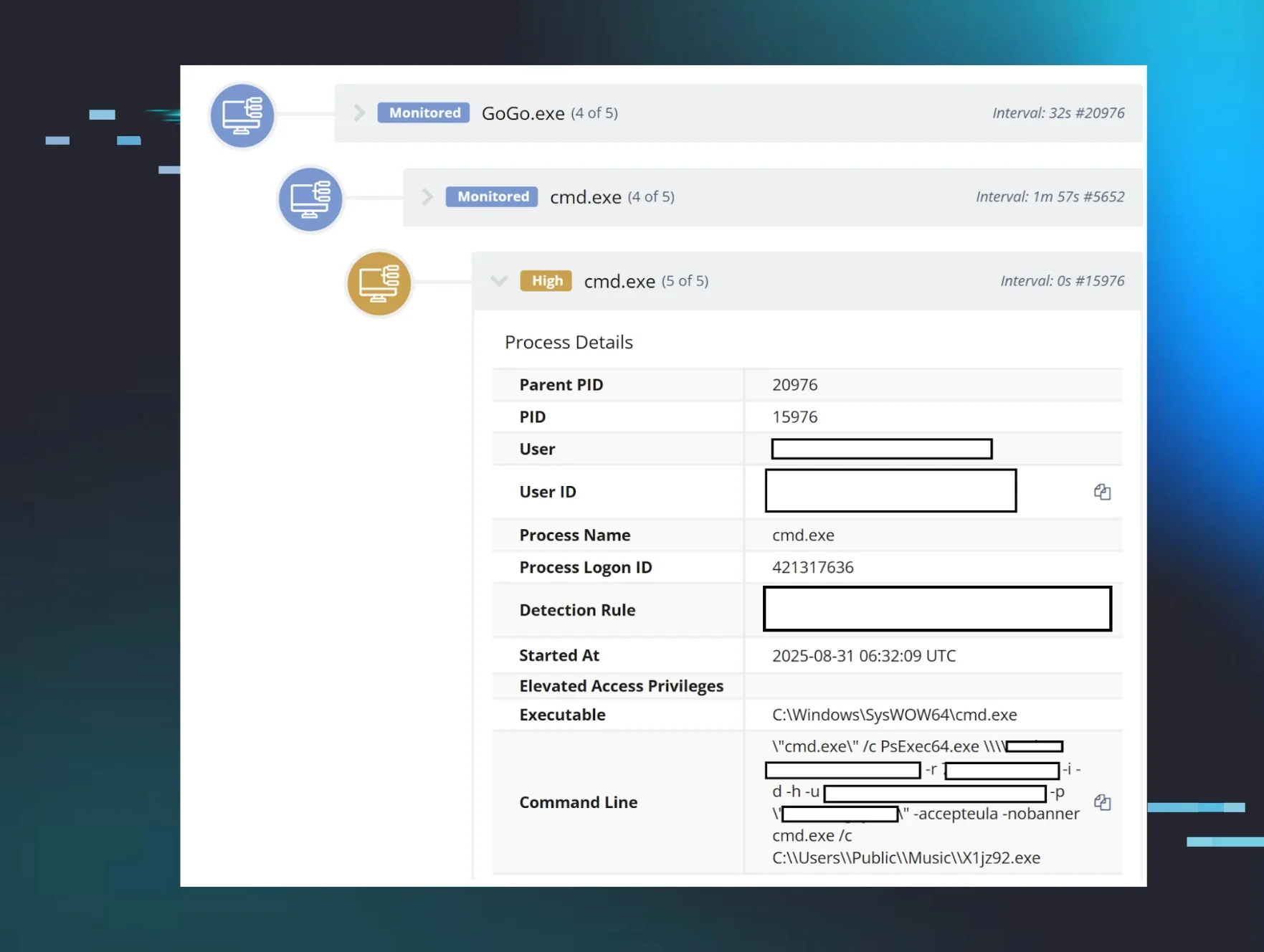
The threat actor returned days later and created a service titled WebrootCheck with a “Service File Name” (command for the service) of cmd.exe /c c:\temp\1.bat.
They then executed a dir command followed by the aforementioned bat script (likely via WMIExec) within minutes of the previous service creation:
cmd.exe /Q /c dir c:\temp\1.bat 1> \\127.0.0.1\ADMIN$\______.______ 2>&1
cmd.exe /Q /c c:\temp\1.bat 1> \\127.0.0.1\ADMIN$\_______._______ 2>&1
Although we were unable to retrieve the 1.bat file, we observed the following command to enable restricted admin mode as a result of its execution. This registry manipulation is a common tactic used by threat actors to more easily dump hashed user passwords from memory.
REG ADD "HKLM\System\CurrentControlSet\Control\Lsa" /v DisableRestrictedAdmin /t REG_DWORD /d 00000000 /f
The following command was executed to force the storage of credentials in plaintext immediately following the aforementioned registry change:
reg add HKLM\SYSTEM\CurrentControlSet\Control\SecurityProviders\WDigest /v UseLogonCredential /t REG_DWORD /d 1 /f
Host 2: Workstation
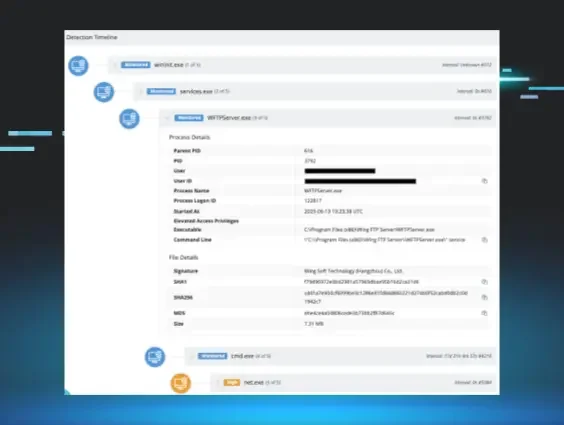
A workstation belonging to an executive was onboarded to Huntress following the incident on Host 1. It was found to have a common service modified to run an executable under the Default user’s appdata\local\temp folder. The executable utilizes an expired Webroot signature.
C:\Users\Default\AppData\Local\Temp\service.exe
The earliest known modification of this service is within a day of the last activity on Host 1 regarding the 1.bat file. As the host was onboarded well post-compromise, and we weren’t able to retrieve the file, we are unable to determine if this was the modification vector. The title of the service on Host 1 is otherwise a strong indication that they are related.
The executable was a golang binary used as a loader for a Mesh Agent executable, a common remote access tool, within the same directory titled web.exe. Although this is likely an attempt to masquerade as a Webroot binary, we cannot fully determine the reasoning for the executable name.
The Mesh Agent executable connected to an IP associated with Kaopu Cloud HK Limited within the United States (AS138915).
Hunt Guidance
We’ve provided the following two Sigma Rules detection rules that may help with your hunting efforts below. The first one detects the client software used to connect to a Mesh Central Server, while the other one detects the use of Nslookup to enumerate mail servers:
The following detection rules are not high-fidelity at scale, but may be used either separately or collectively to identify threat actor activity as part of a routine threat hunting cadence involving analytical methods such as clustering or searching.
-
Potential Discovery Activity Via Dnscmd.EXE (Sigma HQ)
-
Potentially Suspicious EventLog Recon Activity Using Log Query Utilities (Sigma HQ)
-
Suspicious Group And Account Reconnaissance Activity Using Net.EXE (Sigma HQ)
-
Potential Recon Activity Via Nltest.EXE (Sigma HQ)
Mandiant released guidance that illuminates the usage of rented virtual private infrastructure and helps guide network threat hunting operations.
We have also discussed ways to help secure your environment by performing routine asset inventories.
Both of these resources could help you improve your security posture, threat hunting capabilities, and situational awareness.