Cybersecurity is always full of surprises, and 2024 has been no exception. We’re only in October, and we’ve seen some severe curveballs come our way. Hackers have gotten dirtier than ever this year, as evidenced by three major threats that have kept us all on our toes:
- RMM abuse
- BYOVD attacks
- WebDAV abuse
Let’s break down this trifecta together, shall we? After all, we’re all in this together, and with the right insights and strategies, we can embrace a proactive approach that allows our organizations not only to survive but also empowers us all to thrive.
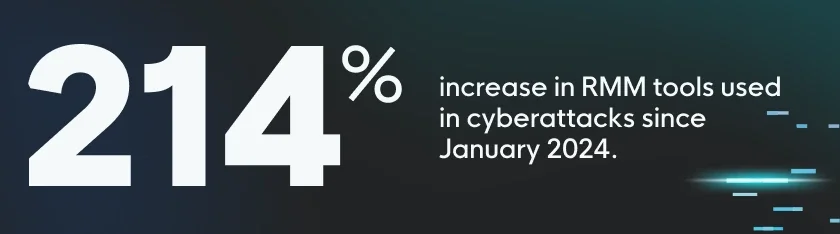
Threat #1: RMM Abuse
One of the most prevalent and dangerous threats we’ve seen in 2024 is the abuse of remote monitoring and management (RMM) tools. Since January, the number of RMM tools used in cybersecurity incidents has increased by 214%.
How RMM Abuse Works
Attackers have become quite adept at infiltrating systems using various techniques, from deploying infostealers to brute forcing passwords, launching phishing campaigns, and purchasing stolen credentials. Their aim is simply to gain initial access to your RMM software, allowing them to take over your systems.
Cybercriminals aren’t playing around. They prioritize the theft of credentials so they can laterally move within networks, abusing network tools and RMM services. Worse, they’re going rogue, installing RMM devices themselves to keep their remote access to systems wide open.
A standout example of RMM abuse is the ongoing exploitation attempts of ScreenConnect (CVE-2024-1709), a vulnerability discovered back in February. Threat actors actively use this exploit to compromise systems, and it still remains one of the most successful strategies to gain unauthorized access.
Beyond ScreenConnect, platforms like AnyDesk, Atera, ZohoAssist, LogMeIn, and TeamViewer are popular targets for password theft and lateral movement within networks. Meanwhile, rogue installations of Ninja, Domotz, Auvik, Naverisk, and Kaseya VSA have also been reported as tools abused by attackers looking to cement their foothold in an environment.
How to Defend Against RMM Abuse
RMM abuse is stealthy, and despite its rising popularity, the right strategies can help you defend against it.
- Monitor your organization: Take note which RMMs are approved for your organization and immediately investigate any evidence of unapproved RMM usage that’s detected.
- Beef up authentication: Ensure multi-factor authentication (MFA) and strong password hygiene are applied to all RMM installations.
- Restrict access: Limit RMM installations to trusted users or devices to limit lateral access opportunities.
- Audit regularly: Update or remove outdated and unnecessary RMM installations wherever possible, at least quarterly.
Threat #2: BYOVD Attacks
Since the beginning of the year, we’ve seen an alarming surge in Bring Your Own Vulnerable Driver (BYOVD) instances—quadrupling in rate of occurrence. This attack method sees hackers exploiting legitimate yet vulnerable drivers to access and control your systems. And it’s becoming a favorite among cybercriminals, especially in ransomware scenarios. In fact, nearly one in four ransomware attacks we’ve seen featured some sort of anti-EDR (evasion or tampering) or privilege escalation powered by BYOVD techniques.
How BYOVD Attacks Work
BYOVD attacks take advantage of one of the most trusted components in your system: signed drivers from legit manufacturers. Since these drivers are signed and trusted, security solutions often exclude them from deeper analysis and monitoring. That means threat actors can simply bundle their malware along with these drivers. They can abuse flaws in the drivers to bypass EDR solutions and install code with kernel-level privileges on the targeted system.
Using BYOVD tactics, attackers can kill or disable critical processes like your EDR and other monitoring applications. Worse yet, attackers can even escalate their privileges to gain complete control over your systems at the kernel level.
In the past six months alone, BYOVD has been at the center of several widespread attacks by notorious groups like Kasseika, RansomHub, Cuba, GhostLocker, INC, Rhysida, and Medusa.
How to Defend Against BYOVD Attacks
BYOVD attacks are increasingly sophisticated, but by implementing these protective measures, you can reduce your risk of becoming a victim of this malicious method.
- Enable BYOVD detection: Ensure your EDR solution and monitoring tools are properly configured to detect BYOVD attempts.
- Stay updated: Regularly apply security patches for all of your installed software.
- Block risky drivers: Apply Microsoft’s Recommended Driver Block Rules for all high-risk endpoints.
- Investigate anomalies: If your EDR or monitoring software is unresponsive, disabled, or fails to report, don’t assume everything’s okay. These can be early indicators of a successful BYOVD or anti-EDR attack.
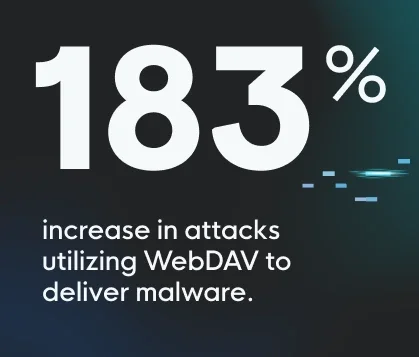
Threat #3: WebDAV Abuse
For the tech-savvy, Web-based Distributed Authoring and Versioning (WebDAV) sounds like a thing of the past. But throughout 2024, WebDAV abuse has become a growing threat, particularly to small and mid-sized businesses (SMB). Since January, we’ve seen a 183% increase in attacks utilizing WebDAV to deliver malware.
How WebDAV Abuse Works
WebDAV was initially designed for collaboration, allowing users to edit and manage files remotely. But threat actors have hijacked it since then to deliver malware, facilitate lateral movement, and exfiltrate sensitive data.
Attackers are implementing WebDAV to bypass defensive mechanisms and execute malicious code their web servers deliver. They’re pairing this with malicious LNK (Windows shortcut link) files and remote network sharing to lure users into triggering malware on their systems.
Internal systems running WebDAV are prime targets for lateral movement. Attackers exploit file system flaws exposed by the WebDAV service, allowing them to move through networks and gain access to other systems. We’ve also seen attackers abusing WebDAV to exfiltrate sensitive files and data straight to their own servers.
Despite becoming more prevalent this year, this shady attack method has actually been part of the toolkit for malware families like Bumblebee, Cicada, BadRabbit, and DarkGate since late 2023.
How to Defend Against WebDAV Abuse
Microsoft recently announced that they’re depreciating WebDAV, but plenty of systems still rely on it due to legacy configurations or third-party dependencies. So, it’s important to remain vigilant and understand how to minimize exposure to this threat.
- Disable WebDAV: If you’re not actively using WebDAV, turn off the WebClient service to block attackers from exploiting it.
- Train your users: Education is key, so teach users to identify and avoid malicious LNK files, which are commonly used in WebDAV attacks.
- Stay updated: Keep your systems patched and audit them regularly to ensure no outdated services like WebDav are enabled by default.
Huntress Has Your Back, No Matter What Threat Is Trending
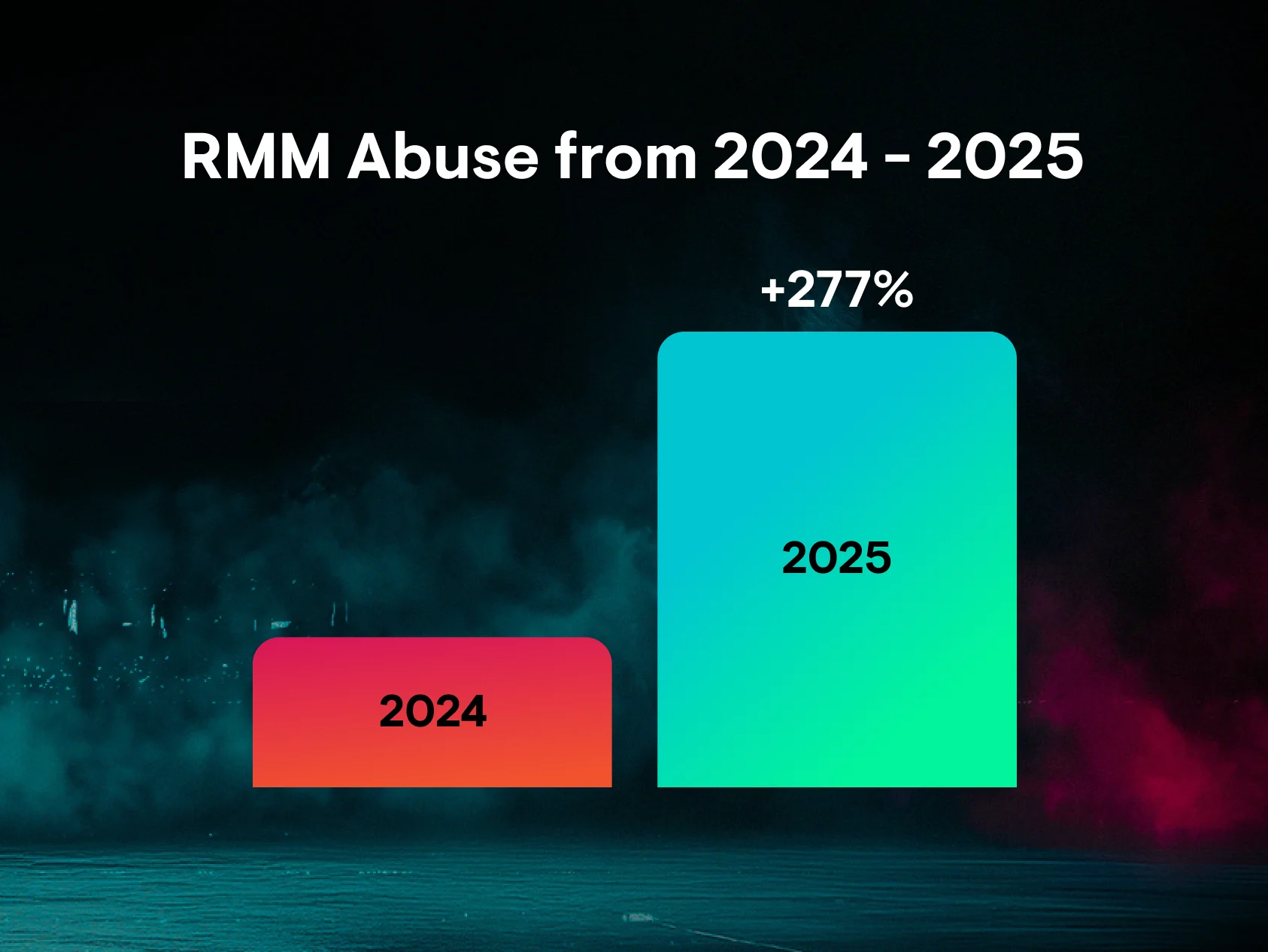
This year is coming to a close, and as we get ready for whatever the next one brings our way, one constant is obvious—a new batch of cyber threats awaits. In fact, the trio we covered here may not even crack our list in 2025. That’s why we have to stay prepared for anything.
At Huntress, we’ve got your back for the next threat that rears its ugly head. There’s no doubt hackers are out there, constantly honing their nefarious skills. And while that might be a scary thought, just remember, we’re all in this together—and we’ll always be here to guide you.
If you’d like to examine the threats we’ve observed over the past year in more detail, download our 2024 Cyber Threat Report.