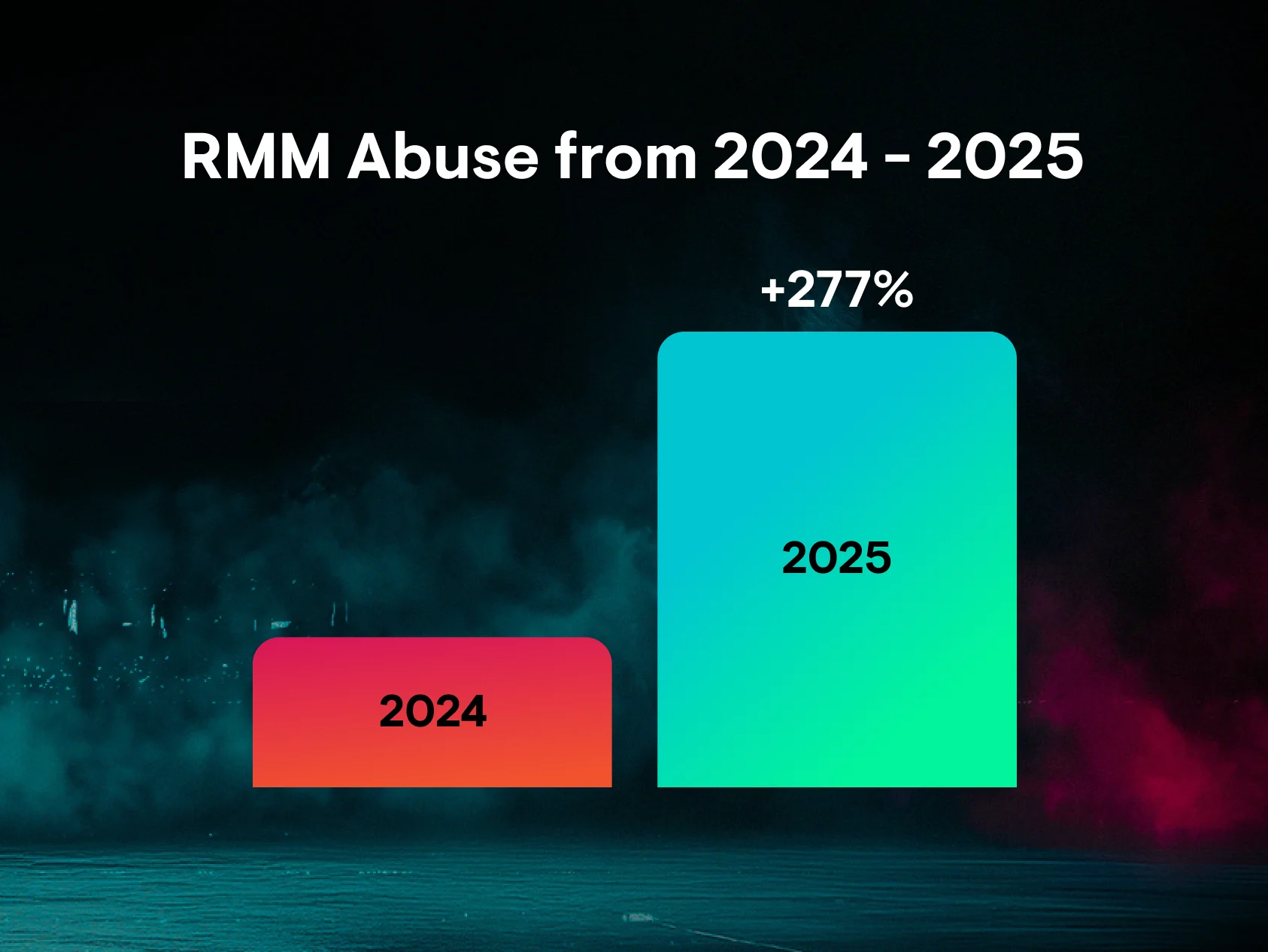
Huntress lives in the small- to medium-sized business (SMB) space, partnering with managed service providers (MSPs), and as a result, sees a wide spectrum of remote monitoring and management (RMM) tool usage. While a great deal of this usage is legitimate and necessary, some of that usage is identified as clearly malicious, which is when Huntress analysts step in and wreak havoc on the hackers!
RMM Persistence
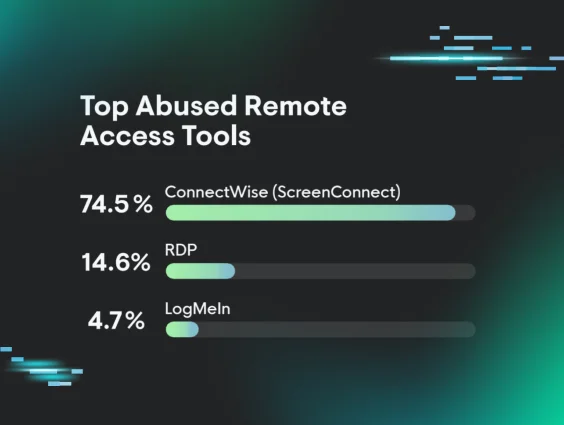
Threat actors have been observed installing RMM tools as a means of maintaining persistence within a compromised organization. Huntress analysts continue to report on rogue ScreenConnect installations, very often associated with helpdesk or support scams. Huntress analysts have also seen a number of incidents during which threat actors have obtained access via some means (often Microsoft's Remote Desktop Protocol, or “RDP”) and installed an RMM tool such as AnyDesk or RustDesk to maintain persistence.
Legacy RMM Tools
However, recent incidents where threat actors have attempted to install ransomware, installed the XMRig cryptocurrency miner, or used the native utility curl.exe to exfiltrate data from an endpoint, were distinctly different, and all have one thing in common: initial access was obtained via an already-installed instance of TeamViewer. That is to say that the threat actor did not copy or download the TeamViewer installation files to the endpoint; rather, they accessed an already-installed TeamViewer instance, using known credentials.
In some instances, the TeamViewer ‘connections_incoming.txt’ log shows apparently legitimate connections going back as far as 2018. In a few of the instances, some of those legitimate (based on user and source endpoint names) connections were made just days before the threat actor connected.
This does not appear to be the result of a vulnerability to, nor misconfiguration of, TeamViewer itself. Rather, based on the ease of access, it's highly likely that credentials had previously been compromised via some means. In every observed instance, a Huntress agent was not installed on all endpoints involved in legitimate access, especially those used to access the endpoint legitimately, so visibility is limited. As such, it's possible that credentials were obtained from an endpoint other than the one monitored by Huntress. For example, credentials and information relevant to accessing the TeamViewer instances may have been stolen via an infostealer or keystroke logger, and possibly obtained from an initial access broker (IAB).

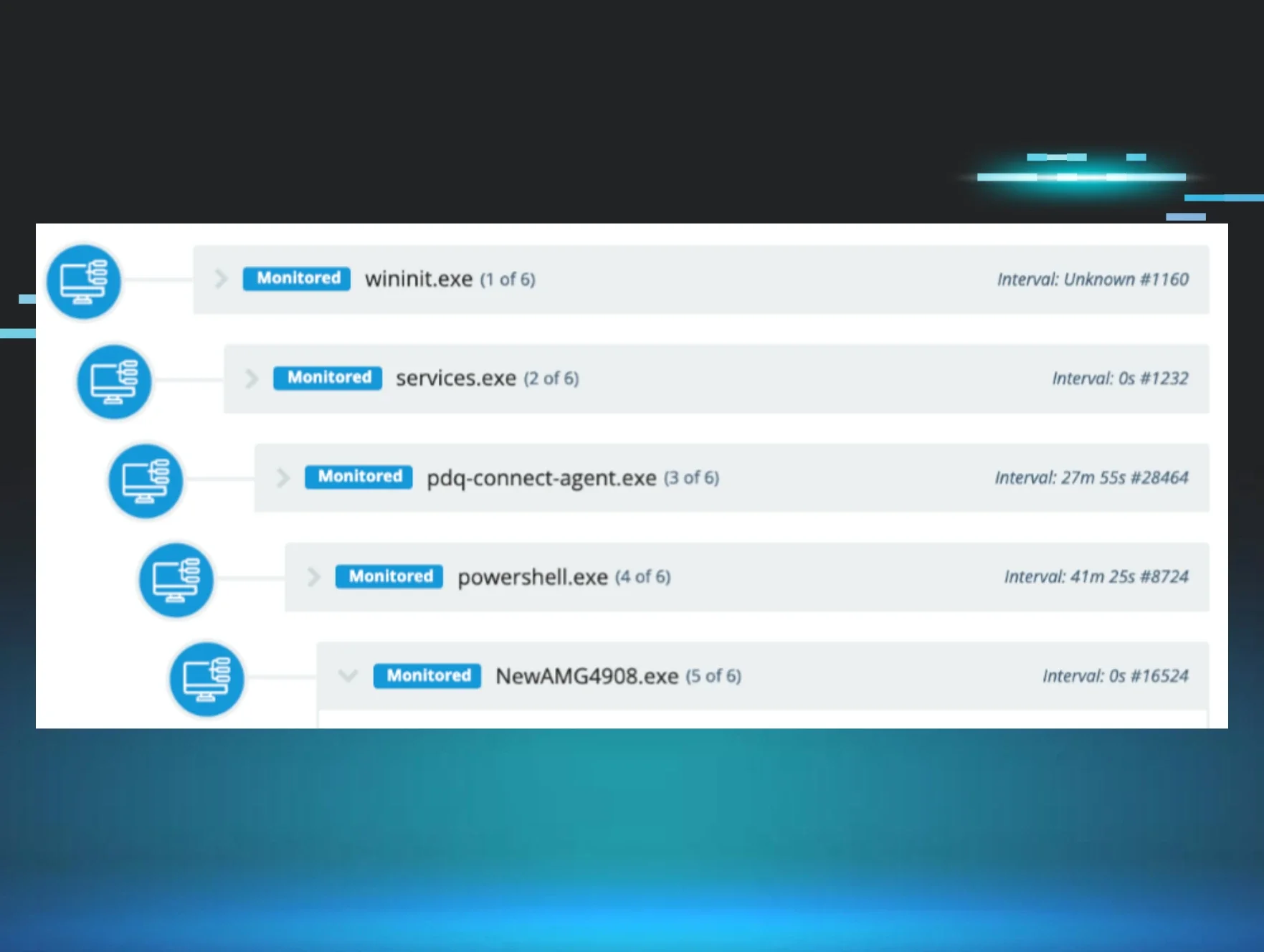
Given the timing involved in a recently observed incident (the threat actor spent 7 ½ minutes accessing endpoint A, 10 minutes accessing endpoint B), it would appear that the threat actor arrived on the endpoints with a plan in place for their actions, deploying the necessary files (pp.bat batch file, LB3_rundll32_pass.dll) and quickly launching their attack. However, other insights derived from the threat actor’s actions included the fact that there was no apparent attempt to develop situational awareness of the environment (that is, what applications and services were already running on the endpoint), nor were there any attempts to extend their reach beyond the endpoint, moving laterally into the infrastructure. There were no reconnaissance commands to collect information about the endpoint or the infrastructure, no attempts to collect additional credentials, nor information about other endpoints on the network. In fact, the attempted attacks appeared to be limited solely to the accessed endpoints.
This attack was similar in nature to previous attacks via TeamViewer where the XMRig cryptocurrency miner was installed; the sole activity appeared to be the installation of the miner, with no observable attempts to move beyond the endpoint to other systems within the infrastructure.
Conclusion
Addressing this issue requires that we rely on the basics of IT and “cyber” hygiene, specifically that we develop an accurate asset inventory, not just with respect to physical and virtual systems within the infrastructure, but also of applications installed, running and accessible on endpoints. This is particularly true when an SMB owner switches to a different MSP, as any legacy RMM tools employed by the previous provider may continue to provide access to the managed endpoints.
If you do have TeamViewer installed and regularly used for legitimate business purposes, be sure to review the ‘connections_incoming.txt’ log file to ensure that there are no suspicious or malicious logins.