Huntress SOC analysts recently alerted customers regarding two disparate endpoints identified as being minimally impacted by ransomware; that is, only a limited number of ransomware canary files were encrypted. In neither instance was there any indication of the threat actor conducting reconnaissance activities beyond the impacted endpoint, nor attempting to move laterally to other endpoints within the infrastructure.
In one of the incidents, the threat actor’s actions were inhibited by installed security software. Based on observed file names, the observed incidents appear to be similar to what was discussed via the VMWare blog from October 15, 2022, titled, “LockBit 3.0 Ransomware Unlocked”.
Initial Access
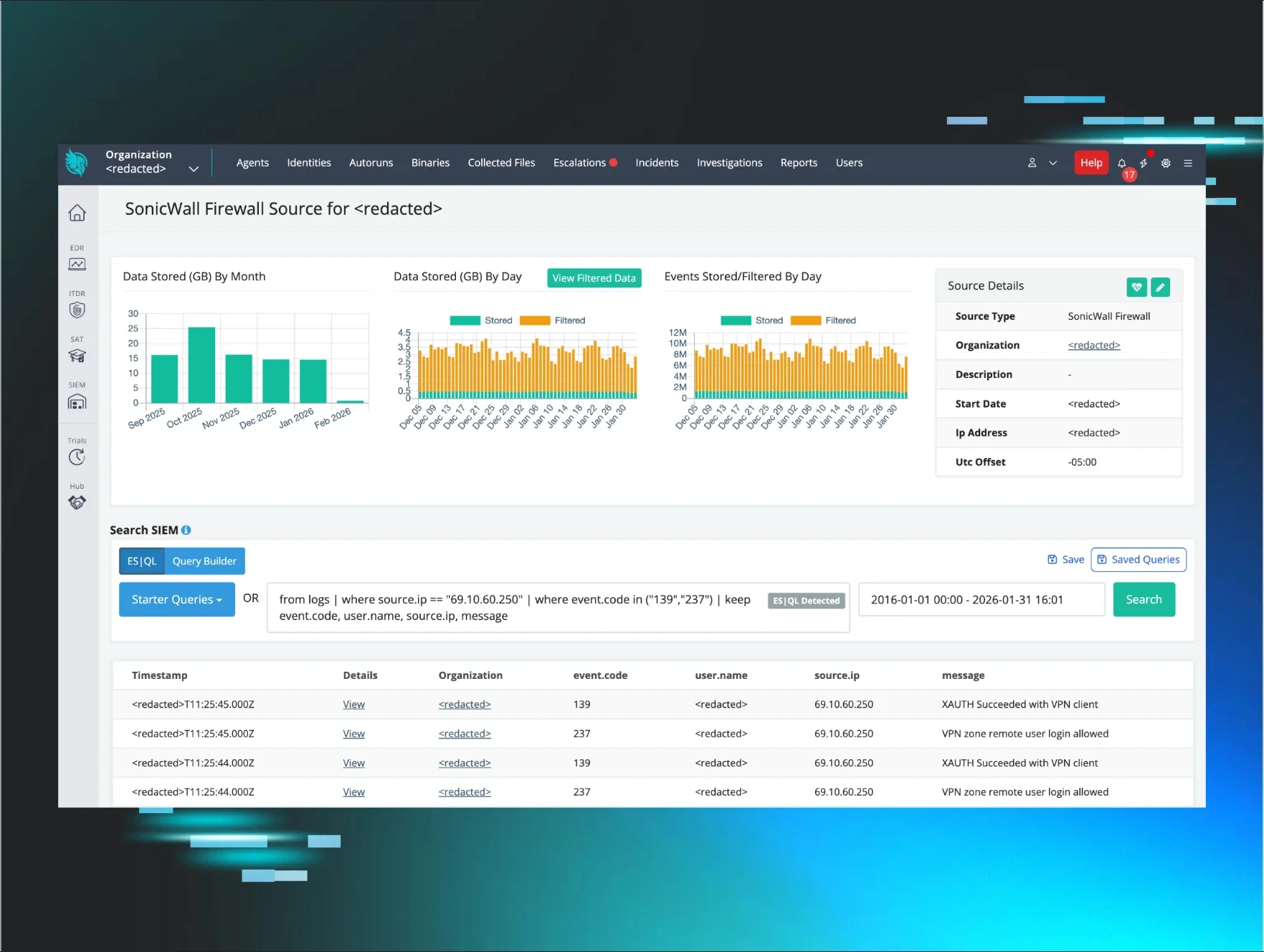
An investigation into each endpoint illustrated that initial access to each endpoint was achieved via TeamViewer. The final entry from the TeamViewer connections_incoming.txt log file showed the threat actor’s access to each endpoint.
Log entry from endpoint A:
WIN-8GPEJ3VGB8U 21-12-2023 16:22:15 21-12-2023 16:29:51 user RemoteControl {GUID}
Log entry from endpoint B:
WIN-8GPEJ3VGB8U 21-12-2023 20:03:23 21-12-2023 20:13:31 user RemoteControl {GUID}
Both log entries were extremely valuable, as they not only demonstrate that a source endpoint with the same name connected to both endpoints, but they also provide the time and length of the login session. As we can see, the login session for endpoint A lasted approximately 7½ minutes, whereas the session for endpoint B lasted just over 10 minutes.
For endpoint A, the TeamViewer connections_incoming.txt log entries illustrated repeated access by several specific individuals, whom Huntress determined to be legitimate administrators. Accesses occurred from multiple endpoints (based on the endpoint names listed in the logs), including those with “-HOME” included in the name.
For endpoint B, the connections_incoming.txt log entries extended back to 2018, but also showed that before the threat actor’s access, the last login session to the endpoint via TeamViewer had occurred over three months prior.
Huntress analysts have previously observed threat actors accessing endpoints via TeamViewer, to deploy a cryptocurrency miner, and during an incident where curl.exe was used for data exfiltration.
Ransomware Deployment Attempts
On both endpoints, the initial ransomware deployment started with a DOS batch file run from the user’s desktop:
C:\Users\user\Desktop\PP.bat
This batch file, in turn, ran the following rundll32.exe command:
rundll32 C:\Users\user\Desktop\LB3_Rundll32_pass.dll,gdll -pass <32-char password>
The ransomware impact on endpoint A was not simply limited, but limited to just that endpoint.
However, on endpoint B, installed security software inhibited the threat actor’s progress and required them to make alternate attempts to encrypt files on the endpoint. Following log messages indicating that the above DLL file was quarantined, the threat actor made several attempts to launch the following file before it was quarantined by security software:
C:\Users\user\Desktop\LB3.exe
Installed security software quarantined the following file before any apparent attempt to execute it:
C:\Users\user\Desktop\ZZZZZZZ
After this point in the logs, no additional threat actor activity was observed during the login session.
Conclusion
Basic security measures are predicated on an asset inventory, of not just physical and virtual endpoints, but also of installed applications. This—and previous incidents observed by Huntress SOC analysts—clearly demonstrate that threat actors look for any available means of access to individual endpoints to wreak havoc and possibly extend their reach further into the infrastructure.
MITRE ATT&CK Mapping
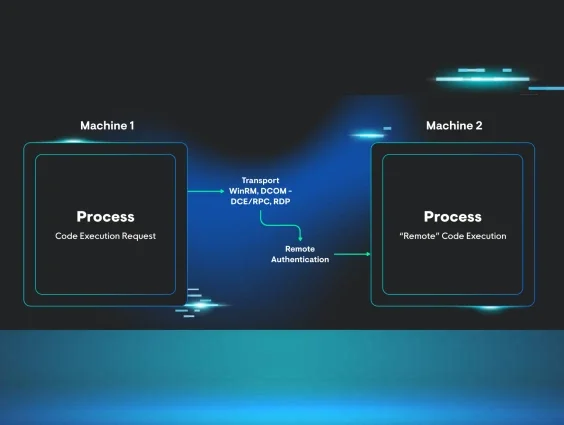
Initial Access - T1133 External Remote Service
Execution - T1059.003 Windows Command Shell
Impact - T1486 Data Encrypted for Impact
IOCs
WIN-8GPEJ3VGB8U - threat actor endpoint name, retrieved from TeamViewer connections_incoming.txt log
LB3_Rundll32_pass.dll (from endpoint A) SHA256: 60ab8cec19fb2d1ab588d02a412e0fe7713ad89b8e9c6707c63526c7768fd362