Background
Huntress analysts "see" a variety of cyberattacks taking place, with visibility into the attack itself initially becoming available at different points in the attack chain. This is true for a number of different types of cyberattacks, and is especially true for ransomware attacks. Tracking Akira ransomware attacks over the past several months, Huntress analysts have identified a number of indicators that stand out as precursors to an Akira ransomware attack.
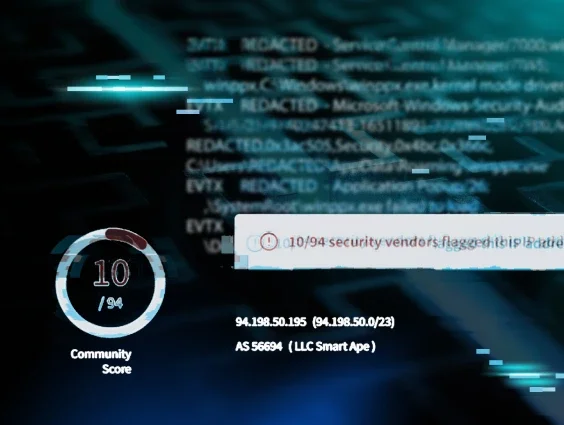
It should be noted that in some incidents, the Huntress agent is added after the ransomware file encryption has occurred. In others, the Huntress agent has not been installed completely across the infrastructure. In still other instances, older versions of Windows may still be in use within the infrastructure. All of these conditions severely limit visibility into the incident.
Attacks
Huntress analysts have observed threat actors creating new user accounts, either via type 3 network connections, moving laterally within the infrastructure, or via access to exposed MSSQL servers (via sqlservr.exe), either standalone or part of Veeam installations.
While Huntress analysts have observed threat actors creating new user accounts as an initial step in an attack that has led to Akira ransomware being deployed, these new user accounts have not always been used to access the targeted endpoint. Many times, an already-compromised account will be used to log into the endpoint. This may need to be preceded by the threat actor enabling RDP, but this has not always been the case. RDP can be enabled on endpoints via the following command:
reg add "HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server" /v fDenyTSConnections /t REG_DWORD /d 0 /f
Note that the use of this command is not unique to Akira ransomware threat actors. Huntress analysts have observed this command being used during INC and ReadText34 ransomware incidents.
In December 2023, Huntress observed the following command being issued against a targeted endpoint:
reg add
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\SpecialAccounts\UserList
/t REG_DWORD /v [USER] /d 0 /f 1
This command prevents the designated user account from being displayed on the Welcome screen, essentially hiding it from view.
Analysts have observed threat actor access via RDP originating from a workstation named WIN-JGRMF8L11HO. This workstation name will be visible in Microsoft-Windows-Security-Auditing/4624 (successful login) or Microsoft-Windows-Security-Auditing/4625 (failed login attempt) event records, as well as within Microsoft-Windows-Security-Auditing/4776 event records, indicating that an attempt was made to validate credentials for an account. All of these event records may be found within the Security Event Log, depending on the audit configuration employed on the endpoint. Huntress analysts have observed this workstation name in log entries during multiple incidents, going back to 19 April 2024, and several instances have been confirmed as Akira ransomware infections.
In several instances, Huntress has detected Cloudflared tunnels being installed on endpoints within the customer infrastructure:
C:\ProgramData\cloudflared.exe tunnel run --token REDACTED
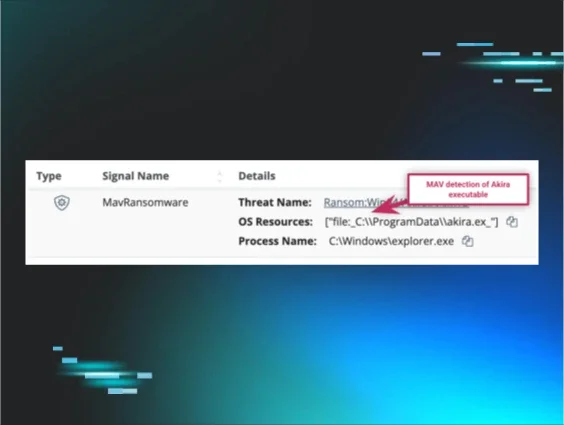
When the file encryption malware is finally deployed, the command line appears as follows:
C:\ProgramData\w.exe -p=<path> -n=2The exact path may vary depending upon the incident, and there may be multiple instances of the command seen in EDR telemetry. However, the purpose of sharing observed indicators from earlier stages of the attack cycle is to assist customers and others in the community by providing earlier warning of an impending attack, in hopes that file encryption malware deployment will be obviated, or at the very least, significantly inhibited.
Recommendations
Huntress recommends that organizations start with a thorough asset inventory, of both endpoints and exposed services. This should be followed by attack surface reduction, and monitoring via MDR and SIEM. Monitoring for and updating indicators identified as precursors to or being used during the early stages of an attack can inhibit or even obviate the threat actor’s follow-on efforts.
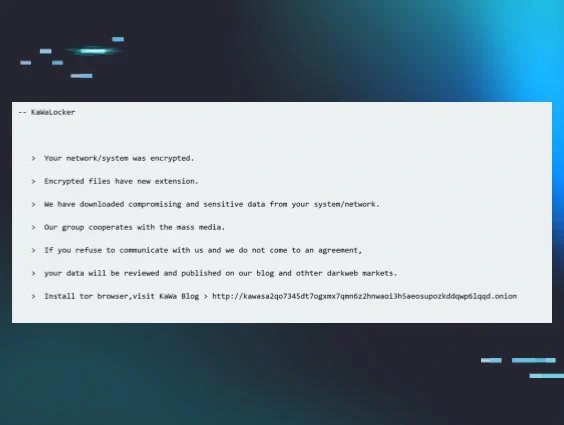
IOCs
| Item | Description |
|---|---|
WIN-JGRMF8L11HO | threat actor’s workstation name |
akira | Encrypted file extension |
akira_readme.txt | Akira ransom note file name |
Noface66Nocase! | Password observed used during new account creation, and when account password has been changed |
3b7fc61649badd73986a86d39124b69aa2c7b6ecdb1d448137080579dc4990f2 | SHA256 hash for one instance of w.exe |