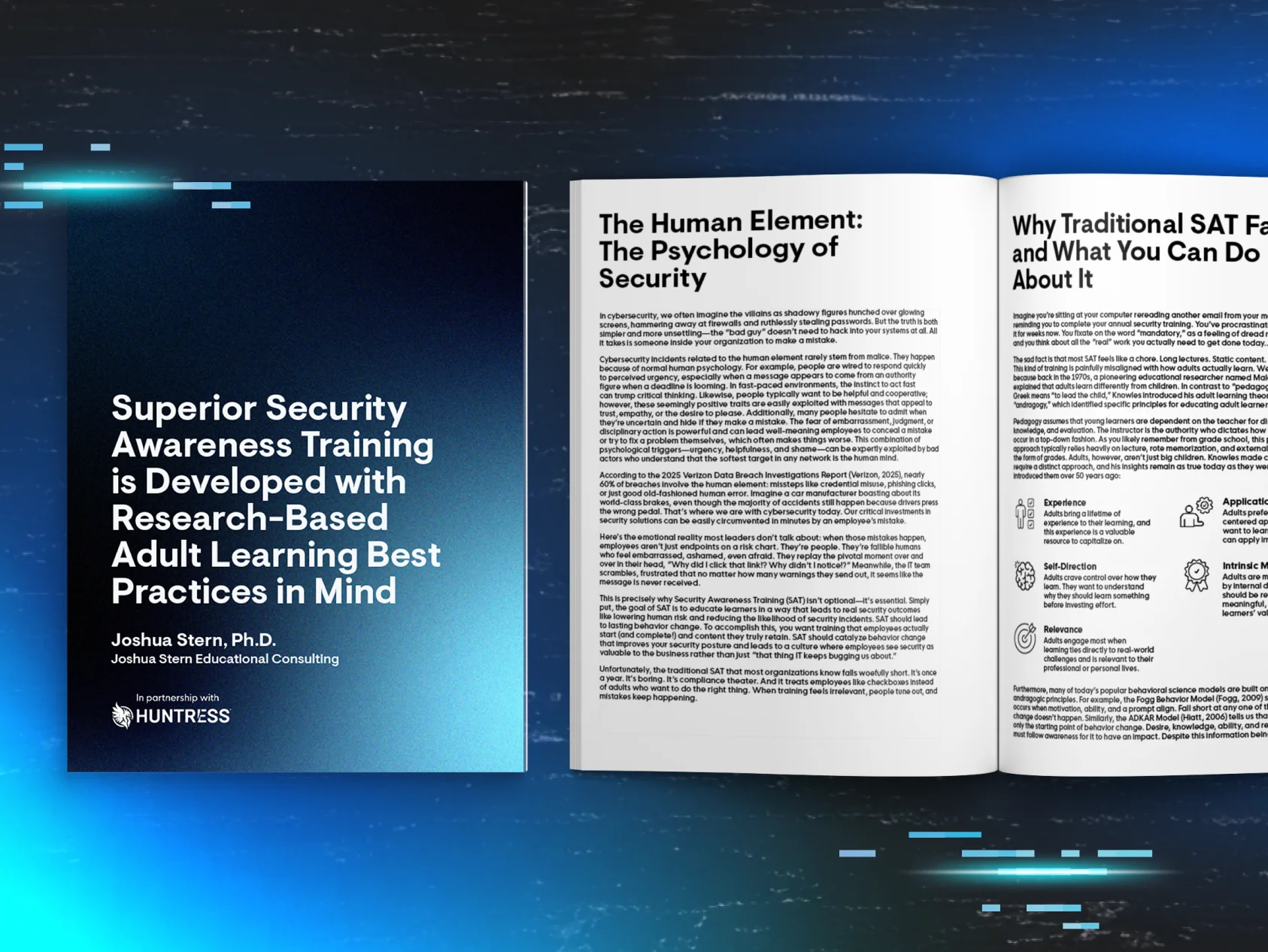
In a recent The Wall Street Journal article titled “Phishing Tests, the Bane of Work Life, Are Getting Meaner,” writer Robert McMillan explores a common critique of security awareness training: traditional SAT methods may do more harm than good. He argues they foster an adversarial relationship between employees and IT departments, and mentions that studies show these programs aren’t effective. But do these claims reflect the whole picture?
The reality is that the efficacy of security training is much more nuanced. It’s absolutely true that some SAT programs are a complete waste of time. It’s also true that some organizations treat training as a check-boxing exercise, or, even worse, punishment. This creates a culture in which employees aren’t engaged or simply ignore it.
But the opposite is also true. If done well, and approached with a growth mindset, security awareness training can be a powerfully transformational force in creating a culture of security and galvanizing the workforce to defend the organization from cyberattacks.
Let’s explore how some SAT programs fall short, and how a different approach can prove that an impactful SAT isn't just possible, but necessary.

Addressing Criticisms Against Security Awareness Training
The criticisms against SAT often stem from programs that rely on outdated, traditional practices like long-form annual training and phishing tests that aim to trick rather than educate. Let's break down some common criticisms:
- "SAT doesn't protect against breaches." Many academic studies critique the traditional approach to cybersecurity training: annual hour-long lectures. These programs often fall short, wasting employees' time by covering broad topics and jargon that rarely apply to their roles, all under the guise of "awareness." Unsurprisingly, these infrequent and lengthy sessions fail to drive meaningful behavioral changes. After all, you wouldn’t expect to get fit by working out intensely just once a year. The same principle applies to effective cybersecurity training.
- "Phishing tests are unfair and demoralizing." Critics argue that sophisticated phishing simulations targeting employees create resentment and erode workplace trust. This is trueif simulated attacks feel more like a "gotcha" tactic rather than an opportunity to learn. You’ll see this in the horror stories of over-zealous IT admins sending emails about flower deliveries in the lobby or lost puppies in the parking lot. They lean too much on playing on emotions without considering the lesson it’ll teach. Your security culture should make employees feel empowered when it comes to their cybersecurity skills, instead of being shamed (or punished) with “remedial” training that doesn’t move the needle.
- "SAT doesn't adapt to real-world challenges." One of the biggest players in the SAT space randomly chooses scenarios from a catalog they’ve amassed over the past 15 years. SAT programs that rely on outdated approaches or fail to reflect current cyber threats will naturally appear ineffective.
While these criticisms are valid for some implementations, they ignore the second half of the equation—what happens when SAT is done right?
To understand the ineffectiveness of many SAT programs, we need to analyze their potential pitfalls:
- Frequency: Once-a-year training doesn’t capture the dynamic and evolving nature of cybersecurity threats. Attackers don’t operate annually, and neither should your SAT program. Training your users on cybersecurity once a year will be the same frequency at which they think about cybersecurity. Your goal should be continuous growth and vigilance.
- Lack of engagement: Dry PowerPoint presentations or generic, randomized phishing tests fail to capture employees' attention, change their habits, or keep them vigilant to real threats. Employees often tune out, treating SAT as just another box to check before moving on with their day jobs.
- Irrelevant content: Training that doesn’t mirror the threats employees actually face in their day-to-day operations misses the mark. Employees need training rooted in scenarios that feel relevant and reflect the tradecraft they could be targeted with today. Don’t waste your employees’ time by explaining the difference between hacktivism and state-sponsored attacks if you’re a dentist’s office that’s unlikely to be affected by either.
- No reinforcement or inappropriate follow-up: Employees who engage with phishing simulations often receive no substantive follow-up, leaving them without the information they need to learn from their mistakes. On the other hand, some programs have hours-long “remedial training” as punishment. This creates the adversarial culture observed in the WSJ article and in studies.
- Absence of culture building: A forgettable SAT program doesn’t foster a workplace culture where cybersecurity is valued. Employee participation becomes surface-level at best unless you celebrate their successes and stop shaming them for honest mistakes.
What Does an Effective SAT Program Look Like?
So we’ve discussed how traditional SAT programs can fall short. But how can you build a security awareness training program that goes beyond basic checklists and turns adversarial phishing tests into learning opportunities? How can you build a positive security awareness culture that actually improves your security posture? Here’s where you can start:
1. Frequent, Consumable Training Modules
Annual training is outdated. Employees face cybersecurity risks constantly, so education should occur frequently. Short, digestible training sessions done regularly (think monthly) help employees learn without feeling overwhelmed. A 10-minute monthly session has enough substance to facilitate true learning, gives people enough material to create organic conversations among coworkers, and fits easier into their schedules. It also allows for a wide range of topics to be covered while they’re most relevant. Repetition over time reinforces knowledge and boosts retention.
2. Reflects Real-World Threats
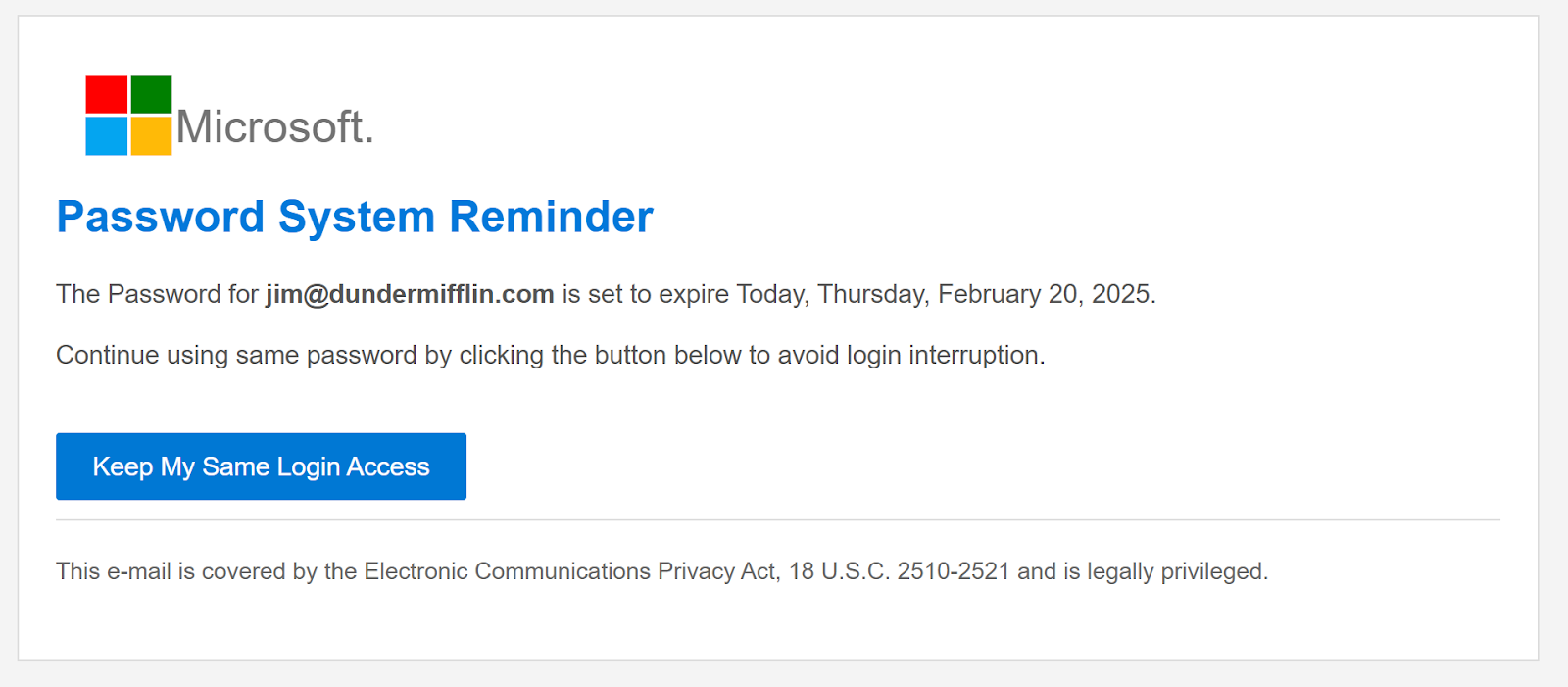
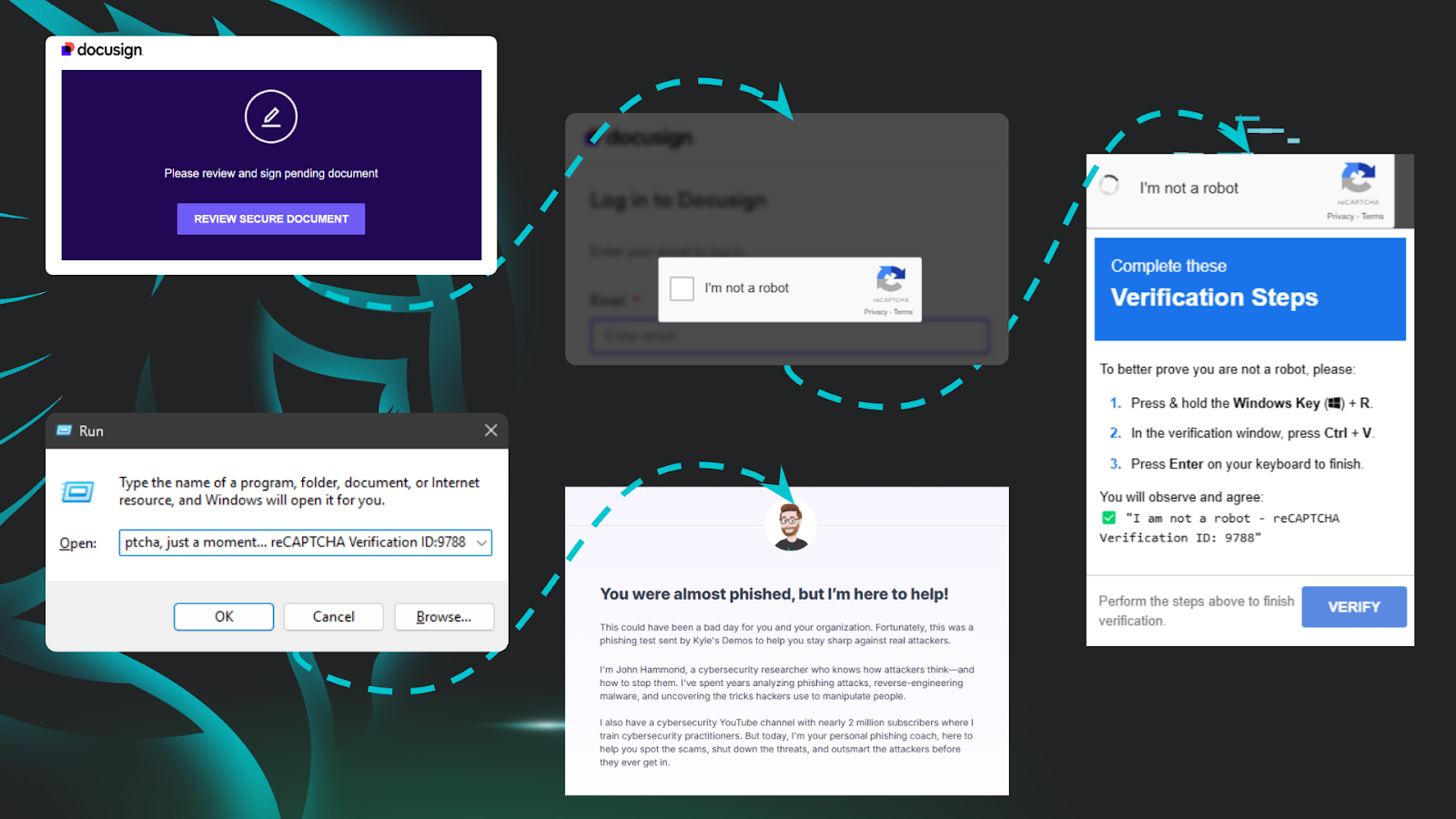
Effective SAT mirrors the sophisticated nature of real-world threats. For example, phishing simulations should use believable and relevant attacks that mimic the threats currently making their way to employee inboxes. This realism gives employees hands-on experience with emerging tradecraft, so they’re ready for the real thing.
3. Engaging Story-Based Learning
Gone are the days of boring slide decks or low-budget, poorly acted videos that go in one ear and out the other. Instead, story-based learning makes complex topics more approachable, engaging employees with characters and scenarios that resonate. An SAT program that gives learners a more concrete mental image of their adversary (like a character from the stories) instead of referring to the vague or abstract “threat actors” is far more effective at holding their attention and transcending the lesson to influence behaviors in the real world.
4. Robust Yet Concise Content
Training content should be substantive enough to impart real learning while short enough to respect employees’ time. Practical lessons like recognizing deceptive subject lines, verifying sender identities, and spotting fake links, all paired with threats most prevalent today, should take priority.
5. Personalized Follow-Up Training
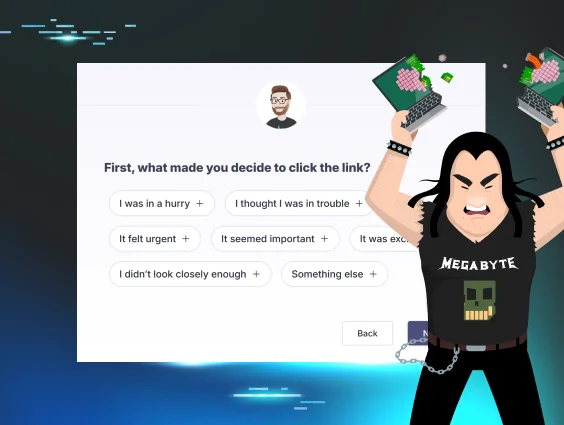
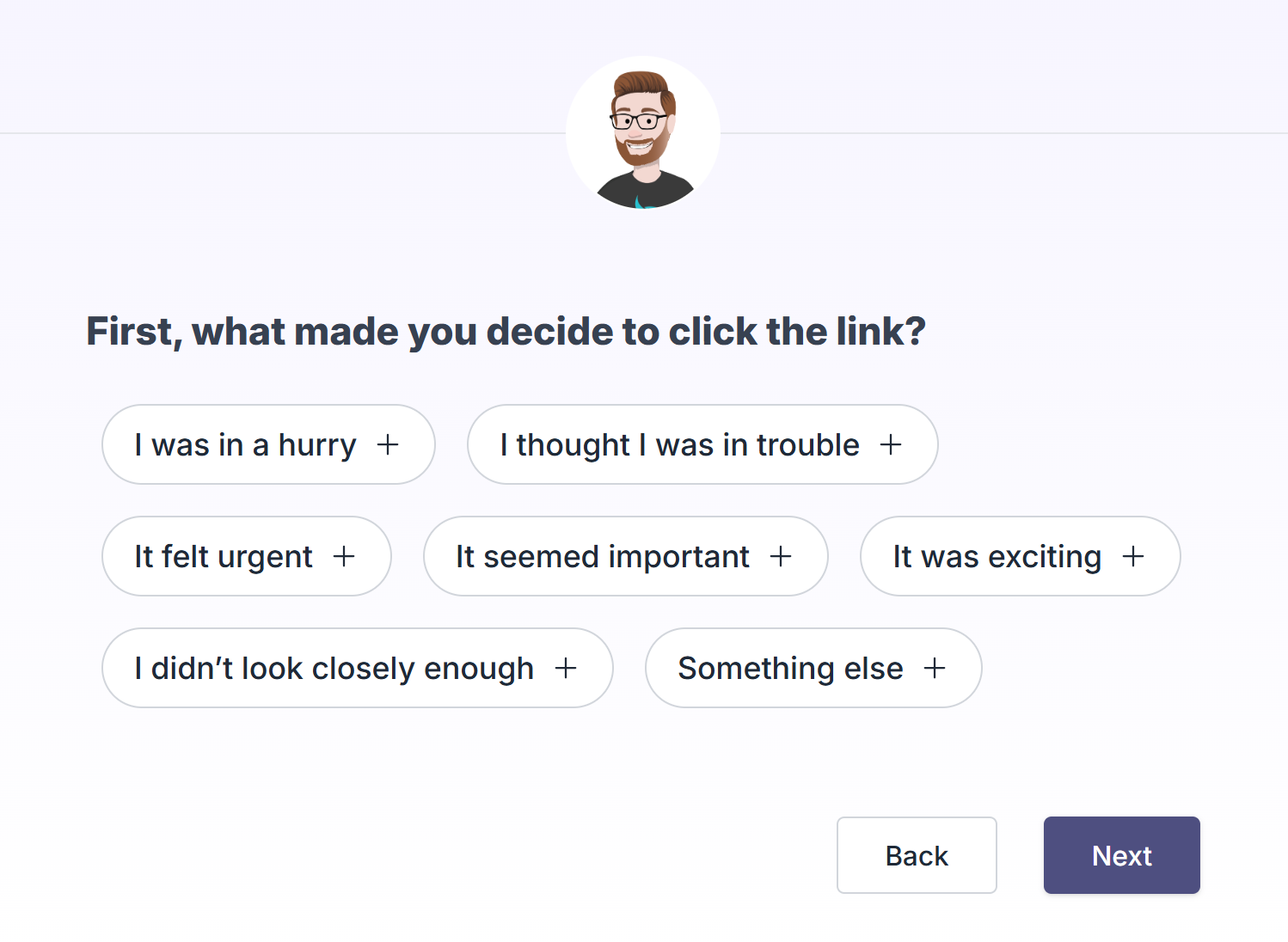
One-size-fits-all remedies don’t work when it comes to SAT. Employees who engage with phishing simulations should receive constructive, personalized follow-up to review the specific tactics used in the attack, and prompt them to consider their reason for clicking. This creates an immediate learning opportunity that instills confidence instead of shame.
6. Frequent Simulated Phishing Campaigns
Frequent simulated phishing campaigns can be beneficial in many ways when done right. First, it keeps learners on their toes. When they know they could receive a phishing email at any moment—whether it’s a simulation or the real thing—they’ll be more likely to check twice before clicking on a link. Second, it exposes them to the emerging tradecraft that hackers might target them with. Third, it helps admins understand their risk levels, which learners may pose more risk, and where you can up-level learners to lower your risk. The focus needs to be on educating users, not “gotcha” tests. And that’s where fostering a positive security culture comes in.
7. Fostering a Positive Cybersecurity Culture
Empower employees to take pride in the critical role they play in cybersecurity. Celebrate reported phishing attempts and reward employees for alerting suspicious action through activities like gamification, underlining the positive impact of their vigilance, and coaching those who may be struggling. Encourage an open dialogue about security awareness in the office (or Slack for the remote folks). Ensure everyone is up to speed and aligned with your security awareness policies and best practices. When employees feel part of a team working toward shared security goals, they’re more likely to engage.
How Huntress Delivers Results with Modern SAT Programs
With Huntress Managed Security Awareness Training, you’ll get an SAT solution that’s purpose-built to engage your learners and prepare them for today's threats. Put simply, it can drive real security outcomes for your organization.
- Story-based narrative: We incorporate engaging characters and storytelling into our training, helping employees visualize real scenarios. Whether it's defending against a character like Deedee or experiencing narratives that hit close to home, learners grasp the significance of cybersecurity.
- Realistic phishing scenarios: Managed SAT is built and backed by the same security experts from the Huntress Security Operations Center (SOC) who manage 3M+ endpoints and 1.5M+ Microsoft identities. While other SAT programs use generic email templates, these experts have a unique, real-time perspective into the threats that are causing the most damage to our user base. And they can replicate those threats as phishing scenarios in quick succession, keeping your learners one step ahead of hackers.
- Phishing Defense Coaching: If an employee clicks a simulated phishing link, we provide personalized Phishing Defense Coaching tailored to the specific scenario they interacted with. These personalized reviews create memorable learning experiences and reinforce the idea that it is indeed possible to identify signs that the email is malicious. Having this context builds stronger defenses rather than punishing for what can feel like an arbitrary test.
- Fully managed ongoing training: Those same security experts creating the phishing scenarios can also fully manage your learning programs. This means your learners are being trained monthly on the security topics most relevant to the current threat landscape, freeing you to focus on other important aspects of your business.
- Reinforced culture: From creating engaging episodes with relatable characters that transcend the training materials to adding extra motivation through gamification or coaching learners (instead of shaming them) post-compromise, Managed SAT helps promote positive security awareness cultures that result in better security outcomes.
The Future of SAT in Driving Outcomes
It’s easy to dismiss SAT as ineffective when it’s improperly implemented, like those mentioned in the WSJ article. And it’s because of those old, ineffective programs that SAT has gotten such a bad reputation.
But such a blanket dismissal ignores the potential of well-crafted, modernized SAT programs. By adapting training to reflect real scenarios, providing ongoing learning opportunities, and encouraging employees to be active participants, SAT programs can, and do, make a business more secure.
Want to create meaningful change for your organization? Start your free trial of Managed SAT today.
Reference:
McMillan, Robert. “Phishing Tests, the Bane of Work Life, Are Getting Meaner.” WSJ, Feb. 7, 2025.