Cyberattacks are constantly evolving. Does your security awareness training keep up?
Most businesses have some form of security awareness training (SAT), but traditional SAT hasn’t been effective in preventing cyber attacks. In fact, 60% of all data breaches in 2024 involved some form of the human element, a number that hasn’t changed since 2023.
Traditional SAT isn’t just ineffective—it’s outdated, overly generic, or relies only on passive (a.k.a. turn-it-on-and-walk-away) learning methods. They fail to shift behaviors and lower human risk levels because they don’t use hands-on reinforcement of training materials that require users to think critically about the threats they might encounter in the real world.
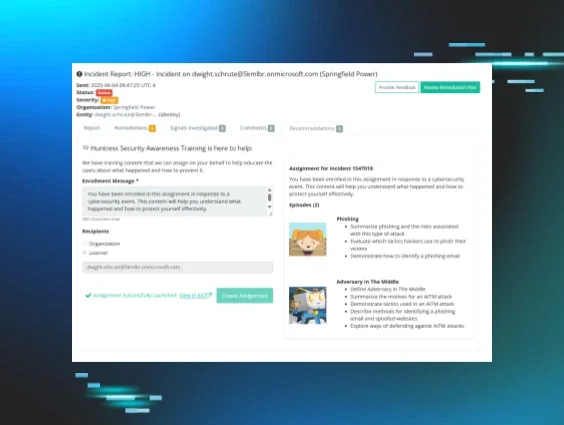
That’s why we’re introducing the brand new Threat Simulator from Huntress Managed SAT. Now, you can more effectively shift learners’ behaviors by reinforcing training with a hands-on, immersive experience that goes beyond just phishing simulations.
Why does old-school SAT stop at phishing?
Most SAT programs give some form of phishing simulations that let you test whether learners are staying vigilant in their inboxes. Yes, this is a crucial part of SAT, but it misses the bigger picture. Users are targeted with tradecraft that extends far beyond phishing emails in their inbox, so why do other programs limit the hands-on training to just phishing?
As it turns out, there are many roadblocks to giving a similar experience with any other tradecraft. Who would have thought that things like laws and regulations would mean that you can’t catfish your end users on Facebook?
But hackers are creative, so we need to be, too. But, if you can’t provide hands-on training against their tradecraft the usual way, like with phishing scenarios, what’s the alternative? Build an immersive, simulated experience that lets you train on any topic.
What is the Huntress Threat Simulator?
The Huntress Threat Simulator is a brand-new approach to SAT. It gives learners a hands-on, interactive experience that lets them step into the shoes of attackers and carry out simulated threats with different types of tradecraft, such as Open Source Intelligence (OSINT) data gathering or spearphishing, to help them better understand the different motives, tactics, and thought processes behind the tradecraft that hackers are targeting them with in the wild. By teaching them to think like a hacker, end users become better defenders against those same threats.
Here’s what Huntress Threat Simulator brings to the table:
1. Hands-on experience with real hacker tactics
Learners carry out simulations of the same threats that hackers target them with, helping them better understand how the threats work and what to do to protect themselves.
2. Interactive, game-like simulations
Unlike PowerPoint slides or basic video training, Threat Simulator enables users to interact in a way that feels like a game, while also targeting the kinesthetic learning style. Learners feel engaged as they race against the clock while challenging their critical thinking and problem-solving skills.
In fact, in a feedback survey, learners who took part in early access described the Threat Simulator as "fun," "engaging," and "informative."
3. Promotes critical thinking and reinforces training
The Threat Simulator forces learners to make strategic decisions. Cyber-savvy choices teach them how an attack works. Meanwhile, wrong choices increase the “suspicion meter,” showing how attentive employees and robust security protocols can thwart an attack. The experience makes the lessons memorable, better preparing them for real-life attacks. And it helps training stick!
If you get caught, you “fail” the Threat Simulator, which teaches learners the importance of having good cybersecurity best practices in place
4. Short training sessions for busy workdays
Part of the reason most SATs fail is that learners don’t have the time for them. These realistic, five-minute sessions are time-bound to ensure that employees can stay productive while learning super valuable skills.
5. Built by cybersecurity experts
The Threat Simulator was built by Huntress Threat Researchers with unparalleled visibility from the millions of endpoints and identities managed by the 24/7 Huntress SOC. Threat simulations reflect the real-life attacks that our SOC sees people falling victim to in the real world, to prevent those incidents from happening in the first place.
See Huntress Threat Simulator in action
Results we’ve seen so far
After just a month of early access, 24,000+ learners completed the optional first Threat Simulation, covering the topic of OSINT. Because there’s a way to “lose” the threat simulation, users took an average of 1.51 attempts to complete it, showing that they’re engaged and enjoying it enough to give it another try.
But partners and customers are seeing more than just high engagement with the Threat Simulator. Here’s what Eric Nush, Director of Technology, CETL for Homer School District 33C, had to say about it:
Try it out for yourself
Already using Huntress Managed SAT? You can assign the first installment of the Threat Simulator to your learners through the library alongside the OSINT episode.
Not yet using Huntress Managed SAT and want to give it a try? Start your free trial today to get access to the Threat Simulator along with everything else Huntress Managed SAT has to offer.
And have your say in what we build next—from SAT features and beyond. Join us at The Product Lab to get the inside scoop on our latest product innovations and tell us what you want to see on our roadmap.