Security awareness training (SAT) is needed now more than ever. Just look at the barrage of ransomware attacks debilitating healthcare. And it’s no longer just hospitals in despair. All industries are susceptible to hackers, as malicious threat actors understand that businesses across every sector share the same vulnerability—people.
The potential for human error stands as one of the greatest attack vectors. Anyone with an email address is now a target. While most employees don’t want to see their organizations succumb to the treacherous tactics of cybercriminals, without proper security awareness and meaningful training, one careless click can result in significant losses of time, resources, and money.
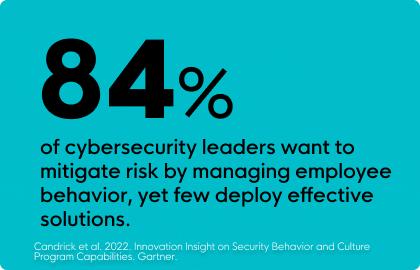
Despite the importance of security awareness training, however, many businesses still fall short when it comes to improving their security postures. But that’s because many SAT solutions fall short on what they can achieve.

The 7 SATuations to Avoid
At Huntress, we analyzed countless SAT solutions and found some common characteristics that inhibit them from achieving their stated goals around security. We encourage you to review this list, and in turn, we hope you can better assess the right SAT solution for your needs.
1. Infrequent Training
Many SAT programs deploy training annually, requiring your learners to sit through long-winded presentations and take tedious quizzes every 12 months. When security awareness is only addressed once a year, these lessons risk becoming both outdated and forgotten.
SAT shouldn’t be treated like spring cleaning—it has to happen more than once a year. Cybersecurity is ever-changing, so it requires ongoing learning. Simply put, successful SAT solutions are ones that offer frequent training all year round.
2. Forgettable Lessons
Retaining knowledge is the name of the game. But many SAT programs are dull and unengaging, failing to grab a learner's attention. This, of course, is problematic because if the lessons aren’t memorable, then nothing of value is learned. The calculus is simple: forgettable SAT equals diminished security.
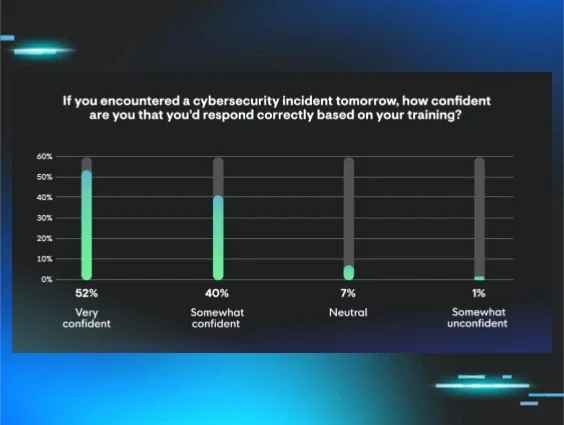
A good SAT program should engage and educate, leading to meaningful behavioral changes. To attain positive security-based outcomes, look for SAT solutions that utilize storytelling methodologies proven to increase knowledge retention.
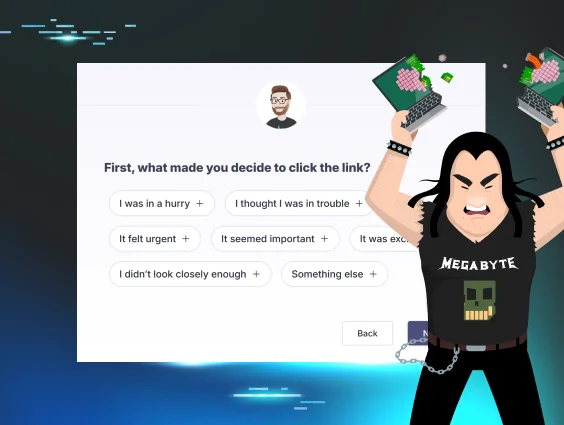
3. Treating Clicks as Failures
With some SAT solutions, you can test learners by simulating phishing attempts. These aren’t meant as malicious tricks, but as a means to keep learners alert. However, if a learner inadvertently clicks on a suspicious email, program admins consider this to be a failed test.
But as the old adage goes, you have to fall to get back up. A good SAT program doesn’t treat these situations as “failures” but as learning opportunities for the employee, allowing them to remediate mistakes and learn from their actions.
4. Inability to Cultivate a Culture of Security
Ideally, you want security to remain top of mind for your employees. However, if your SAT lessons aren’t memorable and if they’re deployed infrequently, security will rarely be second nature for anyone across your organization.

A key step in boosting intelligent cybersecurity habits is to have security-focused practices rooted in your organization’s values, routines, and behaviors. A successful SAT solution keeps learners engaged, thus encouraging conversations around cyber safety and helping ensure a security-first mindset is ingrained into the cultural fabric of your organization.
5. Focusing Exclusively on Compliance
To obtain cyber-liability insurance, most policies require that organizations possess a SAT solution. Simply allowing you to check a box for compliance, many SAT solutions are designed with little regard for driving real results among their users.
A good SAT solution should do more than support a “checkbox” mentality. While compliance is a necessity, a successful SAT program will go further, delivering engaging, memorable content that can improve your organization's overall security posture.
6. Ignoring the Latest Cyber Threats
Cybersecurity moves fast. Sometimes yesterday's defensive tactics are no longer effective today. That’s why it’s so important for SAT programs to stay up-to-date with the latest trends and emerging threats.
But here’s the problem: most SAT solutions aren’t designed by cybersecurity experts. Instead, they’re designed by generalists, most of whom aren’t even aware of the most recent tactics cybercriminals are employing in the wild. This deficiency trickles down to your learners, as they’re not exposed to the latest tradecraft, in turn putting your organization at greater risk.
For a SAT program to make a meaningful impact on your organization, it should be backed by cybersecurity experts who can design and update lessons based on the latest trends they see hackers leveraging in the real world.
7. Demanding Time and Resources to Manage Training
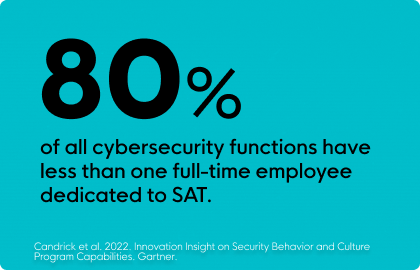
Many SAT solutions are surprisingly difficult to manage, with lengthy setup and complex deployment. They traditionally require non-technical admins to become full-on technologists, which is an unreasonable expectation for most organizations. And should you be fortunate enough to have a skilled internal IT team, it’s still a large undertaking for them to oversee and manage the program.
Implementing a SAT shouldn’t feel like a chore. Take back your time by embracing a SAT solution that’s backed by real cybersecurity practitioners who can create, curate, and manage all necessary tasks on your behalf.
Huntress Security Awareness Training is the Easy, Effective Solution for Both Admins and Learners
Designed and managed by the trusted cybersecurity experts of Huntress, Huntress SAT takes a unique approach to security awareness training. It fuses vibrant animations, memorable narratives, and science-based learning principles, leading to better knowledge retention among your employees. Better yet, it’s fully managed, so unlike other SAT solutions, you don’t need to be a cybersecurity expert just to use it.
Say Goodbye to Ineffective, Outdated Training. Say Hello to Huntress SAT.
This article focused largely on the DON’Ts of security awareness training, but if you’d like to go more in depth on the DO’s, be sure to download our Buyer’s Guide to Security Awareness Training.
And if you and your organization are ready to experience better security postures, start your free trial of Huntress SAT today.