Cybersecurity is a lot like insurance: it’s difficult to calculate ROI unless something bad happens.
The first auto insurance policy was sold in the US in 1897. Unfortunately for us cybersecurity pros, we haven’t been selling cybersecurity solutions for nearly that long. Plus, the cost of modern cybersecurity solutions seems to be rising exponentially. So how do you get your customers to see the value in relatively new—but often expensive—solutions?
The only thing I hate more than my answer is how often I use this answer: it depends. How someone views cybersecurity is often tied to their responsibilities within an organization. The CFO may focus on cost while the CEO may focus on reputation damage and downtime. Meanwhile, the frontline managers may only focus on the business disruptions that your solutions create.
This is why showing the value of your cybersecurity solutions depends heavily on who you’re presenting to.
Language Matters
No matter who you are or who you’re communicating with, you have to meet your audience where they are. Use the language of their business, and relate your messaging to their role in their business.
For example, you’ll want to take a different approach when talking to a CEO than you will with a frontline manager. The CEO is going to care about steering the ship with the goal of ensuring that risk and revenue are balanced, resulting in a profitable business that can support the team and earn profits. Meanwhile, the frontline manager will be more concerned with ease of use, the product or service’s ability to deliver and how empowered they feel to act if—and when—technology fails or a breach happens.
As the cybersecurity expert in the equation, it’s important that you communicate with your clients not only using the language of their business but also in a way that’s aligned with their individual or department’s business goals. Personalizing your language based on who you’re talking to will serve you well when it comes to demonstrating your value.
Leveraging Risk Assessments
Risk assessments are a great tool when used to establish the status quo. After all, you can’t know where you’re going until you know where you are.
Performing a detailed risk assessment at least once per year will provide a clear picture of what risks exist and how they could potentially impact your business. Some of those risk questions should include procedural questions, such as whether your business is prepared to continue to operate during an extended technology outage. Questions like this will help your frontline managers identify where their processes fail when technology fails them.
But pointing to a red checkbox on an assessment isn’t enough to foster improved cybersecurity posturing with leaders who don’t understand cybersecurity. Leadership teams often desire something more tangible to drive them to action.
Crunching Numbers
Enter the IT budget, which can help identify not only the cost to maintain the status quo, but may also quantify the risk of doing nothing.

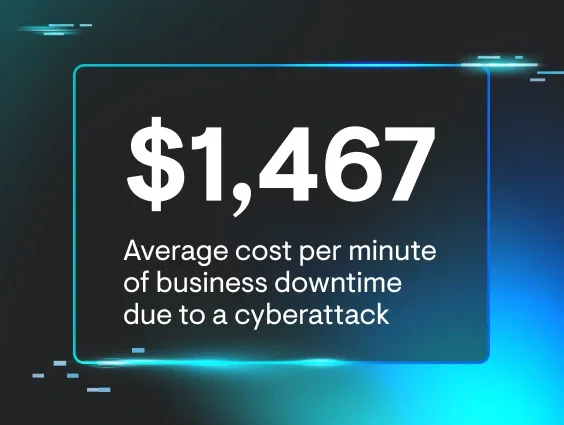
Let’s take a 30-person, $4M a year client and crunch some numbers. The business is bringing in nearly $20,000 per day for roughly 200 working days per year. The cost of five days of downtime is a staggering $100,000, which equates to 2.5% of the company’s annual revenue and a significant portion of annual profits if operations are going to a halt—never mind the incalculable reputation and employee satisfaction damage, both of which will lead to customer and employee retention problems.
Walking through a basic exercise like this with a client, helping them determine their mean time to recovery (MTTR) and putting a dollar figure to that downtime makes the damages to the business quantifiable. Armed with these numbers and a total cost of ownership technology budget (see the budget section of this sample quality business review), the CEO and CFO might make completely different decisions than if they’re simply presented with “continuing with the status quo will likely lead to some downtime.”
This goes towards what one of our consultant partners calls “turning server room conversations into boardroom conversations.” For example, at Lifecycle Insights, we help MSPs deliver quality business reviews (QBRs) to their SMB customers. This assists MSPs with demonstrating their value to their customers by taking complicated cybersecurity risk conversations and distilling them down to strategic business conversations about budget vs. risk—no nerd words needed!
Remediation planning closes the loop. Have you ever worked for a boss who refused to hear a problem unless you brought a solution to the conversation as well? Few understand technology and how it can impact a business better than an MSP. This is why when we identify risk, we need to work with our clients to find solutions that fit their business and their budget.
A three- or four-person office may not be able to afford the latest full-blown SOC/SIEM/SOAR solution, but they can afford MFA and SASE to limit the exposed attack surface. As companies grow into becoming the $4M enterprise we talked about earlier, their ability to spend and reduce risk will grow, too.
By presenting facts, numbers and a compelling business case for cybersecurity in the native language of your customer’s business, interesting things happen. The same clients who never gave your previous cybersecurity discussions a second thought start to come around to the reality that doing nothing is potentially the least business-savvy decision they could make.
Learn More
As your clients start to spend on cybersecurity, they will be looking to put a value on the money spent. Unfortunately, when you’re winning at cybersecurity, nothing happens… which leaves you in the difficult position of trying to show your customers the value of a non-event.
Regular strategic meetings (QBRs) can give you opportunities to review the reduced risk profile with your clients and identify improvements over time in the status quo. These improvements are highlighted in ever-improving risk assessment scores and roadmaps that include digging out of less and less technical debt over time.
If you’re not sure where to start, or you’d like to improve the QBRs you’re currently delivering to your clients, check out our sample QBR that’s packed with helpful tips and tricks on how you can make sure your customers know your value.