Cybersecurity is like a game of chess. It’s all about moves and counter-moves to take down your opponent.
Now, I’m no chess expert (does binge-watching The Queen’s Gambit count?) but I’ve noticed that the best players are usually the ones who can pick up on their opponent’s strategy and anticipate their next move—and this is done through meticulous study and practice.
In the realm of cybersecurity, the game continues but it’s getting more complicated than ever. We’re facing more advanced players and constantly having to worry about the latest vulnerability or the next big ransomware attack. It can feel overwhelming at times, but there is great value in grasping and understanding everything that you can. As defenders, we should always be asking ourselves:
- How effective are my cyber defenses?
- Are my cybersecurity solutions and/or skill sets up to par?
- What more can I learn from real-world attackers and their processes?
Today, the key to keeping pace with the ever-evolving cyber landscape is by creating a culture of continuous learning.
Why We Need Continuous Cybersecurity Education
Cybersecurity is a problem without end because there is no such thing as perfect security. It’s more like an infinity loop—and you should be learning and improving at every turn. Continuous cyber education helps ensure you are regularly fine-tuning your strategy and skillsets, and there are plenty of benefits.
Stay one step ahead of attackers
When you put your hacker hat on and get into the mind of your adversary, you start to understand how they think and how they do what they do. That means education is one of the best solutions we have. If you know what the danger is in that phishing email, for example, you know what can be done to help prevent it. Learning and understanding these offensive techniques can help you develop a better security mindset and stay a step ahead.
Play the long game
Hackers’ strategies are constantly growing and changing, shouldn’t your cybersecurity team be too?
Without continuous learning, cyber professionals can fall behind and be considerably less effective in as little as three months. But when you keep solving new problems and building out your arsenal, your security skills will continue to grow and grow—making it easier to stay up to date on the latest tactics, techniques and procedures.
While studying cybersecurity certainly takes determination and perseverance, it also takes a significant amount of time. If it’s easier, put a training rotation in place. This is where one group of team members has dedicated time to focus on their education and training, while the others can focus on the function of the business. As time goes on, groups rotate in and out of that time for training and everyone can get a chance to level up their skills.
Strengthen your client relationships
Continuous education can certainly benefit you and your team, but it can also trickle into your client relationships. They’re the ones trusting you to be their security expert and advisor, so knowing your dedication to staying on top of all things security could make them stick around for longer. Plus the more knowledge you have, the better your chances of being the hero and keeping your clients protected when it matters most.
Cybersecurity is a team sport
As the saying goes, there is strength in numbers. We have a shared responsibility to grow as a community and learn from each other.
As an MSP, you should be dedicating some time and resources to security education, but it’s also up to vendors and established experts to provide top-notch training and contribute to knowledge sharing. At the end of the day, we all have to point our fingers towards ourselves, and we all carry the responsibility to get sharper on security.
How to Boost Your Security Knowledge
So what are some ways you can start improving your cybersecurity skills? Here are a few resources and suggestions.
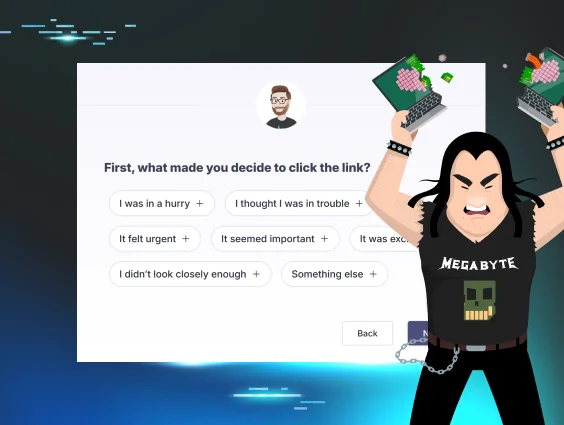
Gamification
Security is not a game, but learning about it can be. There’s a huge amount of online CTF (Capture The Flag) challenges, “wargames” or practice ranges you can use to sharpen your skills. Some popular ones are:
- TryHackMe
- HackTheBox
- RangeForce
- PicoCTF (or really any CTF available on CTFtime.org)
Of course, this is just a small sample of what’s out there, and sometimes these trainings come with a price tag.
If you’re looking for a more DIY version of security training, tabletop exercises are a great option. We even put together a tabletop-in-a-box that you can download and have everything you need to run your own tabletop exercise and test your team’s abilities through gamified scenarios.
Do your homework
A simple search will show you just how full the internet is of valuable resources to help you boost your cybersecurity knowledge. One that comes to mind is the SANS Reading Room, which has a great collection of research papers and resources.
Whether you're looking for the most recent security trends or you're curious about some of the latest zero-days, you will find plenty to read online. In addition to blogs and white papers, you can also turn to YouTube for videos or on-demand webinars if that’s more your learning style.
Industry events
We cannot underestimate the power of peer-to-peer connection in learning cybersecurity. There’s a plethora of security-focused industry events you can attend to exchange experiences with your peers and hear from experts on how they go about handling and mitigating the latest threats.
The best events are the ones that focus only on education and knowledge sharing—that’s why we created hack_it, a virtual training event designed to help security professionals sharpen their skills. We’re excited to be bringing hack_it back to our community, and we have a lot of great sessions in store—from making our own malware to sharing tales from the trenches. If this sounds interesting, you should definitely join us. There’s no cost to register!
We highly recommend attending these types of events (yes, even if it isn’t ours). It’s the best way to network with like-minded people in the industry, learn a new thing or two and grow as a community.
• • •
Whichever route you choose for your education journey, know that it’s not a “one and done” type of deal. You have to keep at it, put in the time and effort, and continuously try new things. Look at what is in front of you and don’t just ask, “how does this work?” but ask, “how can I make this not work?” When you look at technology from the perspective of “how did someone make this,” and then pivot to the stance of “how can I break this,” that’s when the real research and fun starts.
It’s a snowball effect. You will learn more, and then a bit more, and then a little bit more until you grow a certain intuition. Keep doing that, stockpile everything you learn and pass it along. And of course, make sure you are having fun and are doing what you love—after that, success will follow.
Special thanks to John Hammond for his advice and help with this blog post.