Healthcare is evolving quickly. There’s a huge shift taking place, where digital safety is affecting physical security. Healthcare providers must now look beyond traditional patient care and get a better glimpse into digital security, as this is essential for protecting patients in a world where cyber threats can have real-life consequences.
The Physical and Digital Realms are Now Interwoven
Digital health and security are becoming more intertwined with the physical world, creating complex risks that providers must manage to better protect their patients.
For example, a cyberattack on Change Healthcare disrupted indispensable healthcare services, including the accessing of patient records, scheduling appointments, and operating billing systems. The fallout was immediate, with patients encountering delays in receiving crucial care, diagnoses, and treatments. This disruption also led to missed appointments and prescriptions, further emphasizing the link between digital security and physical well-being.
Research conducted at the University of Minnesota School of Public Health exposed the grim reality of ransomware attacks on healthcare. Not only did these attacks disrupt crucial services, but they also had a measurable impact on patient mortality. The study estimated that ransomware attacks resulted in the deaths of between 42 and 67 patients over a five year period, offering a harsh reminder of the human cost of digital vulnerabilities.

Interconnected Devices are a Double-Edged Sword
The increasing integration of digital technologies like wearable heart monitors, smart inhalers, and connected imaging devices—collectively known as the Internet of Medical Things (IoMT)—is revolutionizing patient care. By 2026, healthcare providers are expected to deploy over seven million IoMT devices, doubling the amount from 2021. Simply put, IoMT devices expand targets for cybercriminals due to their interconnectedness and specialized operating systems and software.
IoMT devices are quite vulnerable, with many lacking proper security protocols or running outdated software. For instance, 39% of nurse call systems (NCS)—a vital component of patient care—harbor critical severity unpatched Common Vulnerabilities and Exposures (CVEs). Infusion pumps and medication dispensing systems exhibit similar security lapses. In addition, 19% of connected medical devices are running unsupported OS versions.
New Threats Demand New Approaches
The U.S. Department of Health and Human Services (HHS) recognizes the risks of interconnected devices, and so they’re taking action. In fact, HHS acknowledges that over 53% of connected healthcare devices possess critical vulnerabilities. And while they’ve provided guidance, securing these devices is proving to be more challenging than traditional network devices.

Unfortunately, traditional security measures are falling short, leading to the adoption of more advanced approaches like Continuous Threat Exposure Management (CTEM). CTEM approaches such as Cyber Asset Attack Surface Management (CAASM), breach and attack simulation (BAS), penetration testing, vulnerability scanners, and other tools have been rising quickly. However, these tools can be complex and demand resources that often exceed the capabilities of small- and medium-sized healthcare providers.
That’s why healthcare providers need a layered security strategy, one which integrates both proactive measures to harden interconnected devices and continuous monitoring, detection, and response mechanisms to protect networks and patient safety when cybercriminals break through. Let’s demonstrate why we need this comprehensive approach by looking at a possible real-world scenario.
Scenario: Breaching a Nurse Call System
Imagine a cybercriminal breaches your healthcare facility's network-connected NCS, a critical communication tool for patient care. Despite its importance, the NCS operates on outdated firmware and lacks strong encryption, making it an easy target. The hacker takes advantage of this vulnerability to gain unauthorized access, and the initial breach goes undetected by traditional security measures.
The true threat emerges when the cybercriminal, after having established a foothold through the NCS, begins to probe further, exploiting workstations and servers within your network. It's at this point—when the attacker moves off the NCS onto more conventional IT assets—that the layering of managed endpoint detection and response (EDR) capabilities come into play.
How Managed EDR Stops the Attacker Before Patient Safety Is Compromised
- Detecting Suspicious Activity: Managed EDR solutions keep a constant eye on your network's endpoints, identifying anything suspicious like unusual outbound connections or unrecognized scripts running on a workstation. If something seems off, it triggers an alert.
- Digging into the Incident: Experts from the managed EDR solution’s security operations center (SOC) will dive deeper into the incident. They can trace the attack back to its origin from the compromised NCS, mapping out the attacker's pathway and identifying all affected systems. Through careful examination of the compromised endpoints, they gather intel on the malware and the threat actor's tactics, techniques, and procedures (TTPs).
- Isolating Affected Endpoints: To halt the threat actor's movements, a managed EDR solution immediately isolates infected workstations and servers. This stops the spread and cuts off the attacker’s access to other parts of the network.
- Remediating and Recovering the System: Armed with insights from the investigation, the SOC facilitates remediation actions. This includes purging the malware from compromised endpoints, patching vulnerabilities, and restoring affected systems to their pre-attack state.
- Getting Stronger after the Incident: After the dust settles, the managed EDR solution delivers targeted recommendations to beef up the network’s defenses. This might involve segmenting the network to restrict access between the NCS and more sensitive areas of the IT environment; enhancing monitoring on endpoints for indicators of compromise related to this attack pattern; and tightening security protocols for other devices within the healthcare facility.
- Staying Vigilant: SOC experts enhance monitoring policies, especially for endpoints with access to communication with devices like the NCS. This way, they can ensure early detection of similar threats and protect patients down the line.
Through this scenario, it’s clear that even when direct endpoint compatibility isn’t present—as with certain IoMT or specialized systems like the NCS—managed EDR solutions play a crucial role in identifying and mitigating cyber threats once they attempt to spread to compatible parts of the network. This layered approach to security ensures that healthcare facilities can maintain robust defenses against sophisticated cyber threats, protecting both their digital infrastructure and the patients they serve.

Huntress Helps You Level the Playing Field Against Cyber Threats
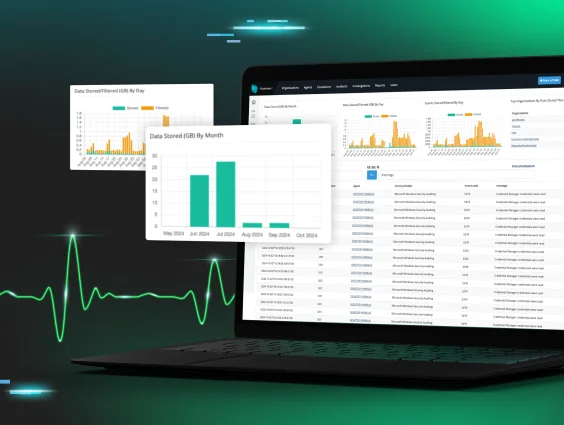
Huntress Managed EDR is tailored for healthcare providers. With a robust track record of protecting millions of endpoints, including essential healthcare systems, we help ensure healthcare organizations can concentrate on real threats. This is all thanks to our precision and sub-1% false positive rate.
With our 24/7 SOC and swift threat neutralization, Huntress Managed EDR helps healthcare organizations focus on patient care while ensuring their digital landscape remains secure. By zeroing in on genuine threats and leveraging insights for a stronger defense, we help ensure healthcare organizations are better equipped to safeguard sensitive patient data and deliver uninterrupted healthcare services. If you’d like to learn more about how Huntress’ managed solutions can better protect your endpoints, identities, and patient data, visit our page Cybersecurity for Healthcare.