It’s hard to open Google or check the latest headlines without seeing news of yet another breach—and that’s just the ones that actually make the news. That’s why, for the past few years, there’s been a critical security tool many managed service providers (MSPs) and healthcare settings are evaluating: security information and event management (SIEM).
Like plenty of unwanted pathogens, cancers, and other invaders in the body, the key to avoiding an IT system breach is early detection. Somewhat symbolically, that’s where SIEM can really shine in the healthcare setting. While early detection is the best defense against severe damage, SIEM is a beast that feeds on data. That’s why it's crucial that healthcare security leaders understand when and where SIEM will serve their best interests.
Timing Is Key
Historically, when a breach is revealed, malicious actors have been in healthcare and IT systems for weeks, months, or even years. With data pouring in and out of those systems so rapidly, threat actors have time to fester, leveraging their unauthorized access and looking for golden nuggets of data that can be sold on the Dark web or elsewhere.
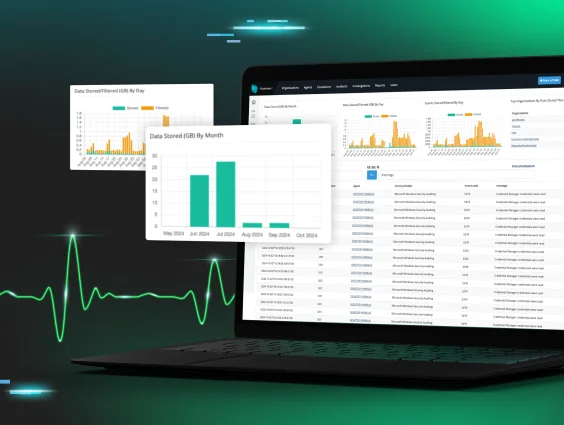
SIEM ingests data. It’s a log collector that receives data across every device on the network while parsing, correlating, and analyzing that data. It’s also great for stepping back in time, providing the functionality to investigate events from months before. However, the strength of SIEM is also the inherent challenge: collecting and holding onto so much data is traditionally very expensive.
So yes, SIEM can potentially become cost-prohibitive for some organizations if it’s aimlessly ingesting all the data, all the time. That’s why healthcare systems and MSPs should be looking for a SIEM solution that delivers that crucial, preventative care—while being smart and selective about how it stores data. Additionally, with so many healthcare systems still lacking on the SIEM side, it’s important to understand where and why this solution can serve healthcare’s long-term security needs.
When and Where SIEM Shines in Healthcare Settings
When done in a data-savvy, cost-effective way, SIEM offers three main components that are an ideal fit for healthcare settings.
1. Reinforcing Compliance in a Changing Healthcare Landscape
In so many healthcare IT considerations, Health Insurance Portability and Accountability Act (HIPAA) compliance drives the conversation—and there are myriad reasons for that. HIPAA requirements also tie into cyber insurance requirements for healthcare organizations, requiring customers to take proactive measures to build a more robust security stack now versus after a costly attack.
Additionally, mergers and acquisitions have created consolidation across healthcare, expanding attack surfaces and imperiling more provider and patient data. Through the M&A process, more sophisticated organizations can inherit weak spots in technology, allowing criminals to slip through undetected.
2. Supporting Cyber Insurance Underwriting Requirements
Cyber insurers have realized they’re proverbially “behind the eightball” in beating cybercriminals. Requirements for coverage are tightening, with more audits and proof points required during the underwriting process. Furthermore, cyber insurers are pushing customers to be more proactive and look at themselves through the lens of the attacker.
The problem is, healthcare organizations are often burdened quite enough with saving lives and serving patients. SIEM stands to act as a HIPAA-friendly, cyber insurer-approved block in a strong tech stack—but only if it meets the cost profile and user-friendly features that allow MSPs and healthcare customers to make it worth their while.
3. Defending Against Increasing Abuse of Legitimate Tools
The old approach was that some providers wrongly assumed they were simply “too small to matter” to threat actors. However, malicious actors don't have to work as hard to break into systems when leveraging legitimate business or operational tools.
Look at the ConnectOnCall incident that hit healthcare software Phreesia earlier this year. It took place through a valid tool, seemingly above board, and after a recent acquisition of the ConnectOnCall business in late 2023. But this incident took services offline and involved law enforcement and third-party cybersecurity consultation in order to start resolving the problem.
SIEM for Healthcare Needs to Break the Mold
Threat actors don’t have to break in if they can just open the front door. When it comes to healthcare software used across disparate systems and distributed provider footprints, there are untold places for criminals to hide and leverage their unauthorized access. SIEM is well positioned as a solution to help mitigate that.
Healthcare systems and MSPs focused on SIEM should look for a streamlined approach that filters the chaotic “trauma bay” of data and alerts, whittling down to the most critical alerts. A forward-thinking, integrative approach—like the one great healthcare providers use—is the way to go with SIEM. Questions decision makers should ask when evaluating a SIEM:
- Is this cost-effective and targeted in log collection?
- Is this simple and user-friendly?
- Can we get this solution onboarded and deployed quickly?
If the answer is yes, I’d say SIEM is the right prescription for healthcare. It will help healthcare defend against attacks, secure cyber insurance despite rising premiums, and ultimately, keep patients and providers safer and more secure.
About the author: Joe Goldstein is the president and founder of OCS IT. He’s a best-selling co-author of "Tech Up or Lose Out: How to Use Technology as a Competitive Advantage in Your Business" and a seasoned IT consultant and senior executive with over 30 years of experience helping businesses thrive through innovative IT solutions.