From stethoscopes to smartphones, healthcare's embracing technology—and the risks that come with it.
The things that have made healthcare more accessible, like online prescription fillings and virtual appointments, are also the things that make private healthcare data more accessible to threat actors.
There’s no doubt that cybersecurity threats in healthcare have gotten more complex. The decentralized nature of the data creates a larger attack surface (or more points of entry) for threat actors. This decentralized data, often spread across many devices and platforms, makes it harder to implement consistent security measures in healthcare.
“The elevated concern in healthcare is due to the type of data they possess. It’s highly personal and sensitive to the individual (test results, conditions, etc) as well as unchangeable (social security numbers). This leads to increased risks of identity theft,” says Tony Black, Principal Product Researcher at Huntress.
“In addition, disruption to healthcare providers can have significant impacts to the health and safety of patients. The theft of a credit card or bank information, while not insignificant, has numerous stop gaps and recovery options. Theft of a SSN has little recourse and will require constant vigilance for the rest of the affected individual's life.”
To get a pulse on the biggest cybersecurity threats in healthcare in 2025, we surveyed more than 500 healthcare IT professionals to hear what common cyberattacks are keeping them up at night, what they’re doing to stay one step ahead, and the bigger-picture plans they have in store for 2025.
Keep reading to see what we found.
Key takeaways
- Data breaches are the top concern in healthcare cybersecurity, while phishing attacks are the most common.
- The biggest impact of cyber threats in healthcare is the disruption of patient care.
- 37% of respondents say enhancing employee training is their top cybersecurity priority in 2025.
- The evolving threat landscape poses the biggest challenge to healthcare organizations when it comes to implementing and maintaining effective cybersecurity measures.
1 in 3 say data breaches are the biggest cybersecurity concern in healthcare
One in three IT professionals (33%) said that data breaches were their top concern in cybersecurity for healthcare for the year ahead. People were also worried about threats like phishing (19%) and ransomware (15%). One of the least common concerns was supply chain attacks (5%), despite reports that these threats can cause disruptions, sometimes lasting weeks.
Personal data is sensitive, especially when it comes to private medical information. Would any of us want our medical history shared with the world? That’s why data breaches in healthcare are particularly concerning. These concerns aren’t unfounded either, with a noticeable increase in data breaches in healthcare settings, like:
- Change Healthcare’s 2024 hacking incident that impacted some 190 million individuals
- Kaiser’s 2024 unauthorized access incident, which impacted as many as 13.4 million individuals
- Maximus’ 2023 hacking incident that impacted 9.2 million individuals

Phishing attacks are actually the most common threat reported by healthcare IT professionals
When asked what cybersecurity incidents their organization has experienced in the last 12 months, the largest number of respondents (40%) said phishing attacks. Other top cybersecurity threats in healthcare include data breaches (20%), malware infections (19%), denial-of-service (DoS) attacks (12%), and ransomware attacks (12%).
That said, a surprising number of respondents (37%) didn’t report any cybersecurity incidents over the past year. While this is certainly a positive, it doesn't necessarily mean they weren't targeted or that their security is foolproof—it could also mean a lack of proper detection and reporting mechanisms, potentially masking underlying vulnerabilities.
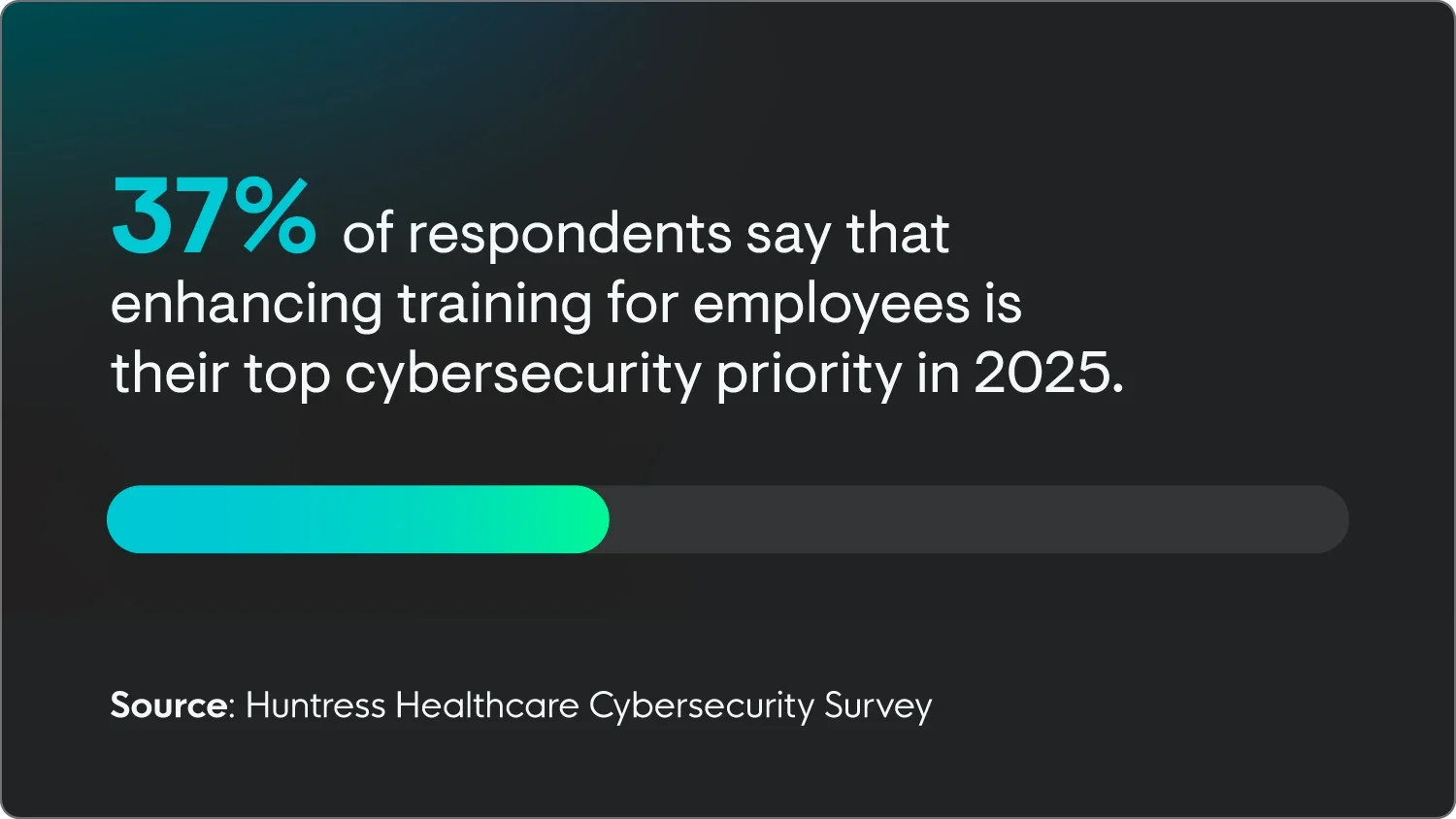
Security awareness training is a top priority in healthcare settings
Roughly two-thirds (66%) of people surveyed complete cybersecurity training at least every six months and the majority of respondents (37%) say that enhancing security awareness training for employees is their top priority in 2025. This emphasis on frequent training underscores the growing recognition of the significant risk that human error plays in not meeting the standards required to ensure cybersecurity in healthcare.
“First, to use an old saying, ‘trust but verify’. Phishing frequently preys on people's desire to be helpful and by instilling a sense of urgency. When the contents of an email or text seem odd, the recipient should always verify with the sender through direct means (IM, phone call, face-to-face),” says Black.
“Second, be mindful of physical records. Faxing is still routine in healthcare organizations and is a common avenue for unauthorized disclosure of Protected Health Information (PHI). Employees should be mindful of sending and receiving PHI by verifying the receiver's information and promptly retrieving any physical records when received.”
Empower your employees with Managed Security Awareness Training today.
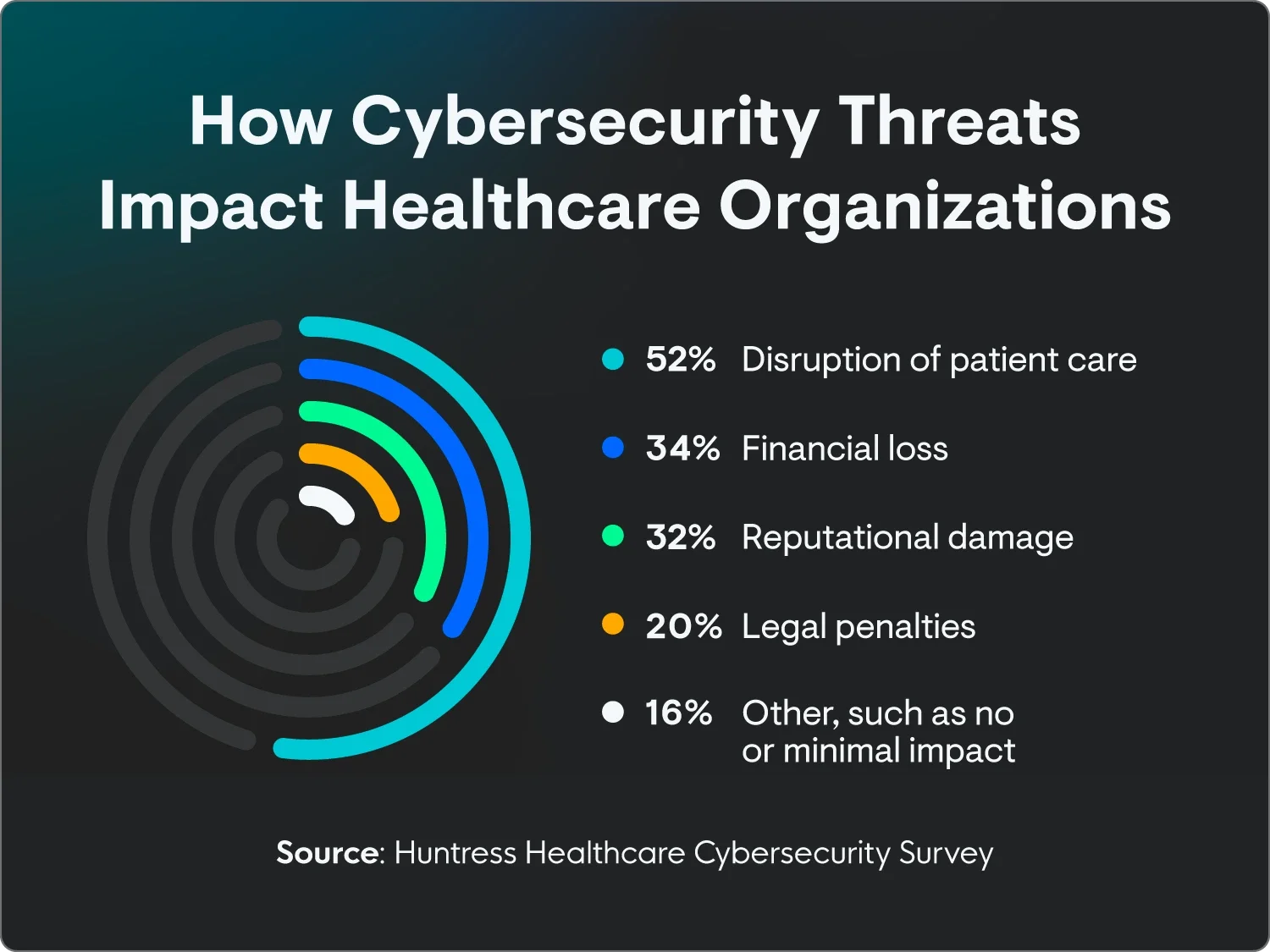
Disruption of patient care is the biggest consequence of cyber threats
Most healthcare IT professionals (52%) say that the most significant impact cyber threats have on their organization is the disruption of patient care. Even something as simple as slow Wi-Fi can impact how quickly and effectively patients receive care. Just imagine the effects of a full-scale attack where data is breached and programs are locked.
Other impacts include:
- Financial loss (34%)
- Reputational damage (32%)
- Legal penalties (20%)
- Other, such as no or minimal impact (16%)
It’s not just inconvenient—these attacks can have life-or-death consequences. Research shows that healthcare cyberattacks can lead to patients needing to be diverted, risking their quality of care, or even not receiving urgent medical attention on time. Ransomware attacks can strain the entire healthcare system, making accessing patient information or administering necessary care difficult.
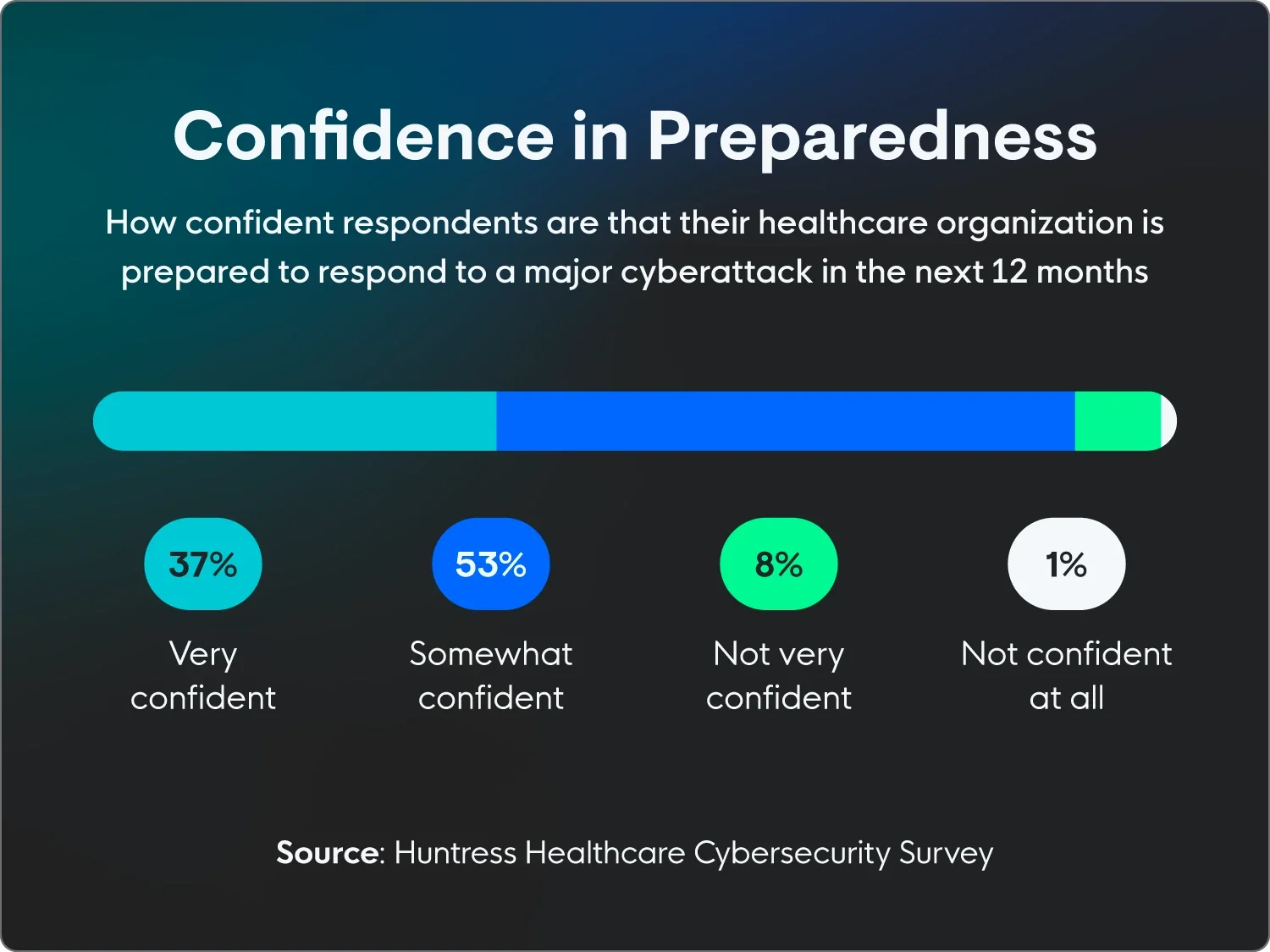
90% are at least somewhat confident in their preparedness for a cyberattack
When asked how confident they are about their organization’s preparedness for responding to a major cyberattack in the next 12 months, 37% of respondents said they are very confident, while 53% are somewhat confident.
On the flip side, 8% are not very confident, while a small 1% are not confident at all. We’ll get into the challenges healthcare organizations face in more detail below, as they’re dealing with a wide range of issues. While some are common across industries, like AI and data privacy concerns, others are unique to healthcare, like compliance issues and extreme budgetary constraints.
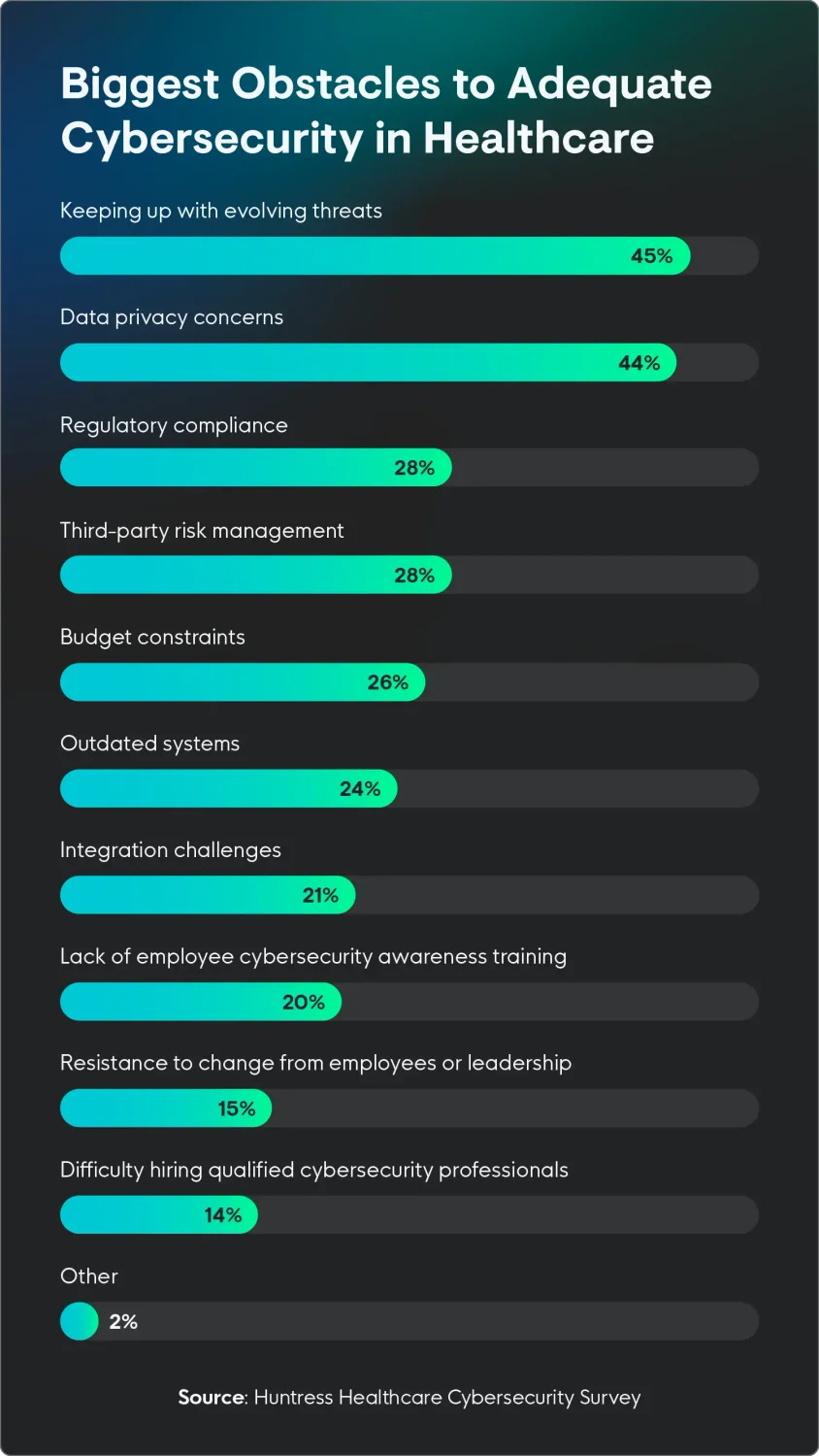
Nearly half say keeping up with evolving threats is the biggest challenge
The one thing healthcare IT professionals are most worried about in the coming years? It’s not AI or budgetary concerns—or at least not those exclusively—but the overall evolving threat landscape.
When asked about the biggest challenges their organizations face when it comes to implementing and maintaining effective cybersecurity measures, respondents said keeping up with evolving threats (45%) and data privacy concerns (44%) are top of mind.
“Several of the largest breaches from the past decade have been due to organizations not implementing basic security controls. For Change Healthcare, it was lack of MFA on a Citrix host. For Equifax, it was an unpatched Apache server,” says Black. “Organizations need to ensure they are performing the basics. What used to be called ‘best practices’ should now be called ‘common practices’.”
“In short, organizations need to ensure MFA is enabled on all external platforms, a vulnerability management program exists and is followed, network segmentation practices are implemented (especially for legacy equipment and IoT devices), and that ‘least privileged’ is implemented across user and application accounts,” Black explains.
Other challenges faced by healthcare organizations included:
- Regulatory compliance and third-party risk management (28% each)
- Budget constraints (26%)
- Outdated systems (24%)
How to improve cybersecurity in healthcare
Healthcare organizations are increasingly vulnerable to cyberattacks because patient data is sensitive and medical devices and systems are interconnected. To protect patient privacy and ensure the continuity of care, robust cybersecurity measures are essential.
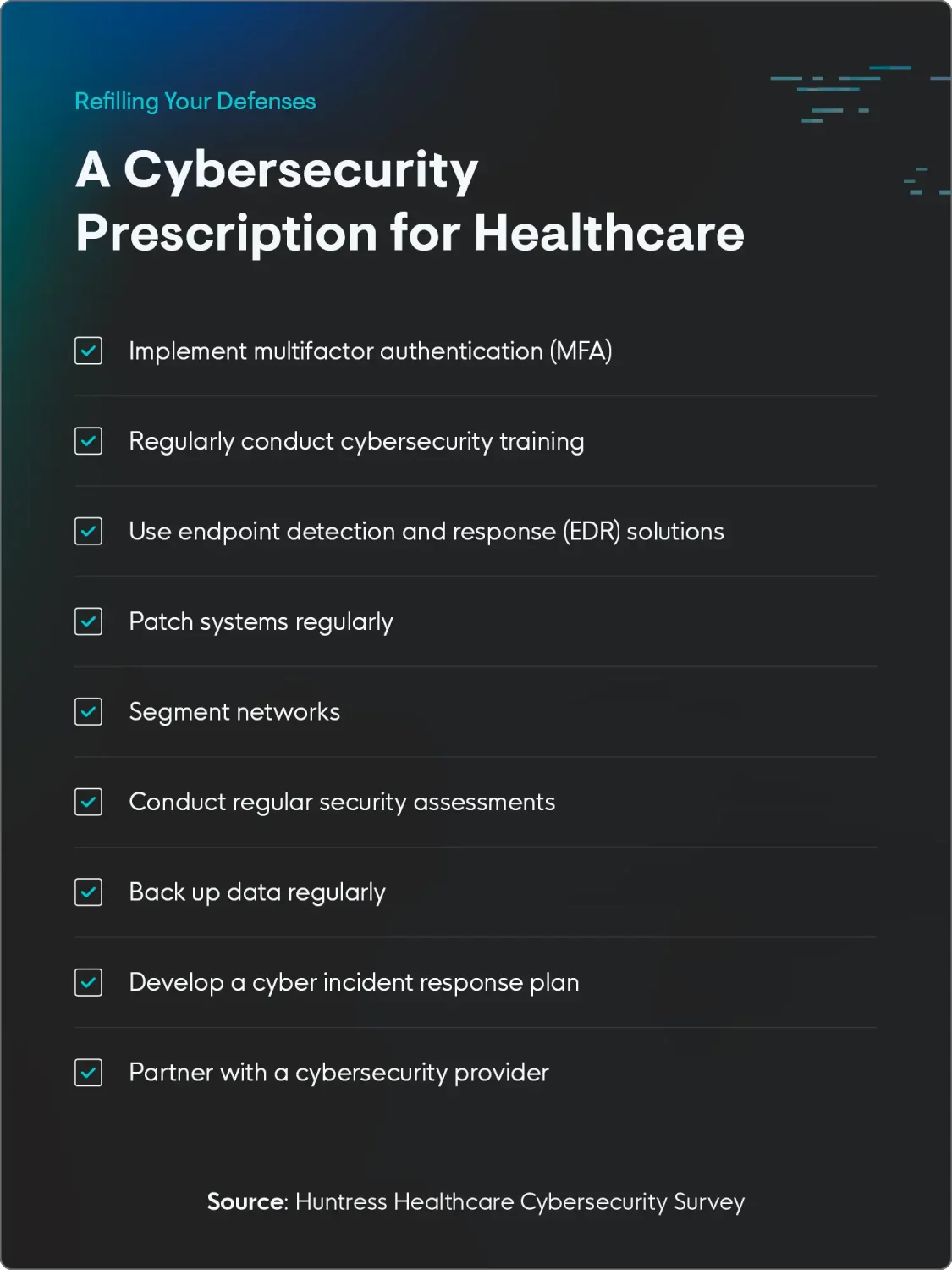
Here are ways you can protect your healthcare organization:
- Implement multi-factor authentication (MFA): MFA asks users to provide two or more factors for authentication, making it much harder for threat actors to gain unauthorized access to accounts and systems.
- Regularly conduct cybersecurity training: Educate employees about common cyber threats and how to protect themselves. This training should cover topics like password management, safe browsing practices, and how to report suspicious activity.
- Use endpoint detection and response (EDR) solutions: EDR solutions monitor endpoints for signs of malicious activity and can automatically take action to mitigate threats. This helps detect and respond to attacks quickly, reducing potential damage.
- Patch systems regularly: Threat actors often exploit software vulnerabilities, so it’s important to keep all systems, including operating systems, applications, and medical devices, patched with the latest security updates.
- Segment networks: Dividing the network into smaller segments can help reduce the attack surface and limit the spread of malware in case of a breach. This can also make it easier to identify and isolate infected devices.
- Conduct regular security assessments: Regular security assessments can help prevent attacks and make sure your security measures are up-to-date by identifying potential vulnerabilities.
- Back up data regularly: Regular data backups can help minimize the impact of a ransomware attack or other data loss event. Backups should be stored securely and tested regularly.
- Develop a cyber incident response plan: Outline the steps to contain a cyberattack, mitigate the damage, and recover from the incident.
- Partner with a cybersecurity provider: Partner with a reputable cybersecurity provider (like Huntress!) to help you implement and manage your security measures. These providers can give you access to expertise and resources that you may not have in-house.
Protect your healthcare organization from evolving threats
While there’s definitely been some progress in cybersecurity training and awareness within healthcare, it’s an uphill battle. The ever-evolving threat landscape and growing data privacy concerns and regulatory pressures demand a multi-faceted approach.
“Treat cybersecurity as an extension of patient care,” says Black. “Protecting sensitive health records should be given similar importance to the physical and mental care provided to a patient.”
Focus on healthcare, not site health, with Huntress’ healthcare solution.
Methodology
The survey of 517 US healthcare IT professionals ages 25+ was conducted via Centiment Audience for Huntress between January 27 and February 5, 2025. The data is unweighted, and the margin of error is approximately +/-3% for the overall sample, with a 95% confidence level.









