The best offense is a good defense, and this is even more true when it comes to cyber threats.
Cyber insurance may not be at the top of every business's mind, but all it takes is one cyber threat you didn’t see coming to see catastrophic results. The true cost of a cyberattack can be more than $250,000, which many businesses without insurance absolutely can’t afford. Despite this alarming number, a December 2024 Huntress survey of more than 500 IT security professionals found that 22% of companies still don’t have cyber insurance.
This Huntress survey reveals critical cyber insurance trends your business needs to know in 2025, including the importance of multi-faceted coverage, with support from inside and outside your organization. Check out these key cyber insurance trends for 2025, why they matter to your business, and how to choose the right plan for your organization.
Key Takeaways
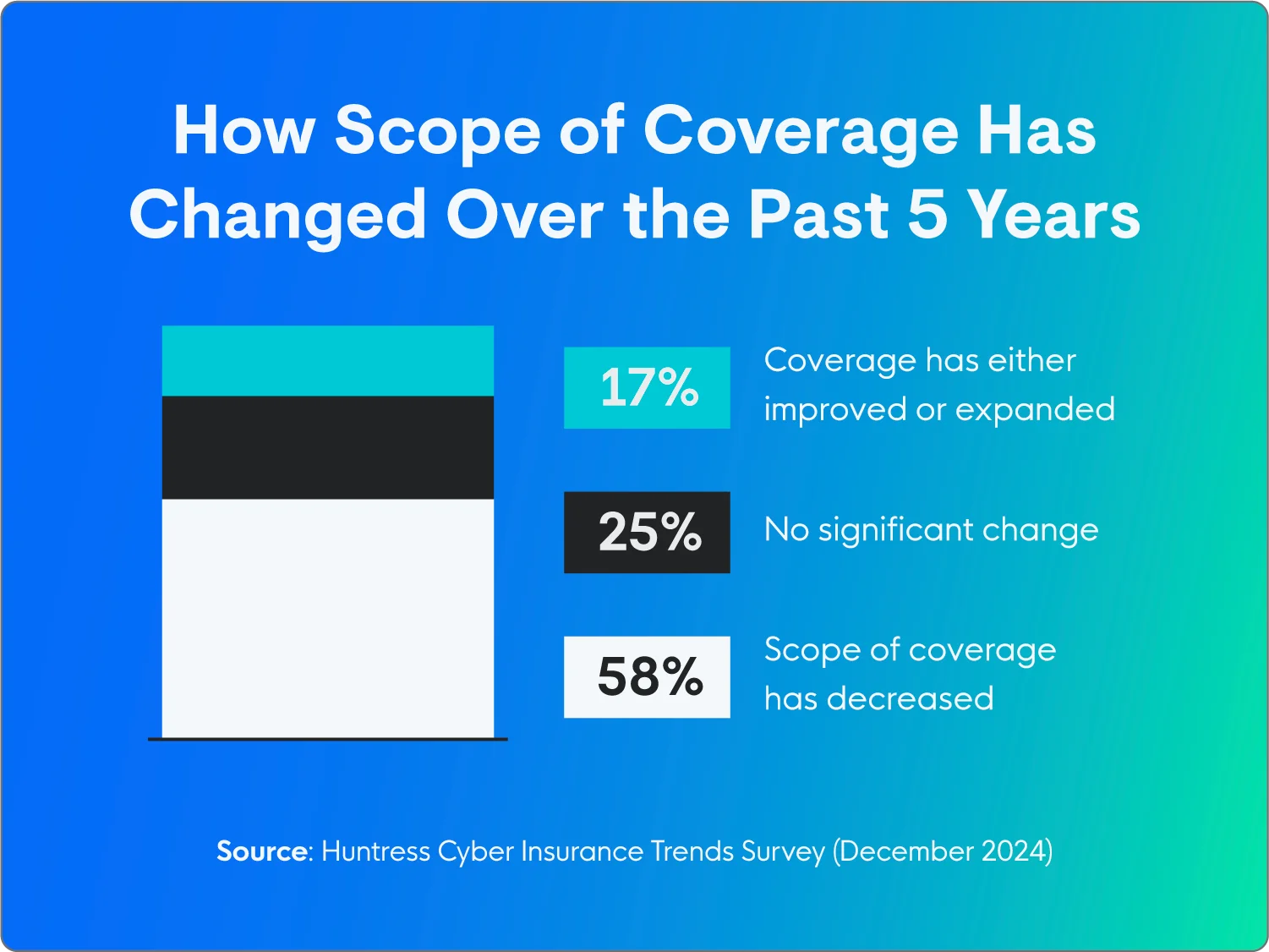
- 58% of businesses with cyber insurance report some level of decrease in their coverage over the past five years.
- Not understanding coverage options is the main reason organizations don’t have cyber insurance right now.
- 61% of respondents say AI-powered attacks are the biggest threat to their cyber insurance premiums.
58% of Respondents Report Some Level of Decrease in Coverage
The majority of respondents (58%) noted a reduction in the scope of their cyber insurance coverage over the past five years, while 25% said there hadn’t been any significant changes.
Cyber insurance costs are continually going up, which suggests that some existing policies may not adequately reflect the evolving threat landscape. This could leave organizations with insufficient protection against emerging cyber risks, and could also be why some orgs take out lower-coverage policies as they’re priced out of full coverage.
Nearly 4 out of 5 Businesses Have Cyber Insurance
One of the more surprising cyber insurance trends is that most organizations surveyed have cyber insurance. While 79% may seem high, it varies a lot by company size. Roughly 74% of companies with 500 or fewer employees have cyber insurance, with that number dropping as low as 56% for those with fewer than 50 employees.
Cost is the main factor in why many organizations (26%) choose not to get cyber insurance, so it’s not surprising that small and medium-sized businesses are less likely to invest in protecting themselves.

The Majority of Cybersecurity Professionals Feel They Have the Budget to Protect Their Orgs
The majority of respondents (55%) strongly agreed that their organization has the budget to protect itself against cybersecurity threats. Only 2% strongly disagreed, while 38% somewhat agreed and 5% somewhat disagreed.
Given that cyberattacks are getting more severe and happening more often, along with the potential for crippling financial and reputational damage, investing in comprehensive cyber insurance isn’t a nice-to-have, it’s a must-have.
Lack of Understanding of Coverage Options Is the Biggest Barrier
As cyber insurance coverage requirements change and costs go up by as much as 25.5% year over year, businesses that already have cyber insurance struggle to keep up, while those without it may not even know where to start.
The majority of respondents without cyber insurance (38%) say “not understanding coverage options” is the main reason they haven’t purchased a plan. Perceived low risk is the next consideration (28%), while cost comes in third (26%). Other factors (7%) include factors like managing cyber events in-house.

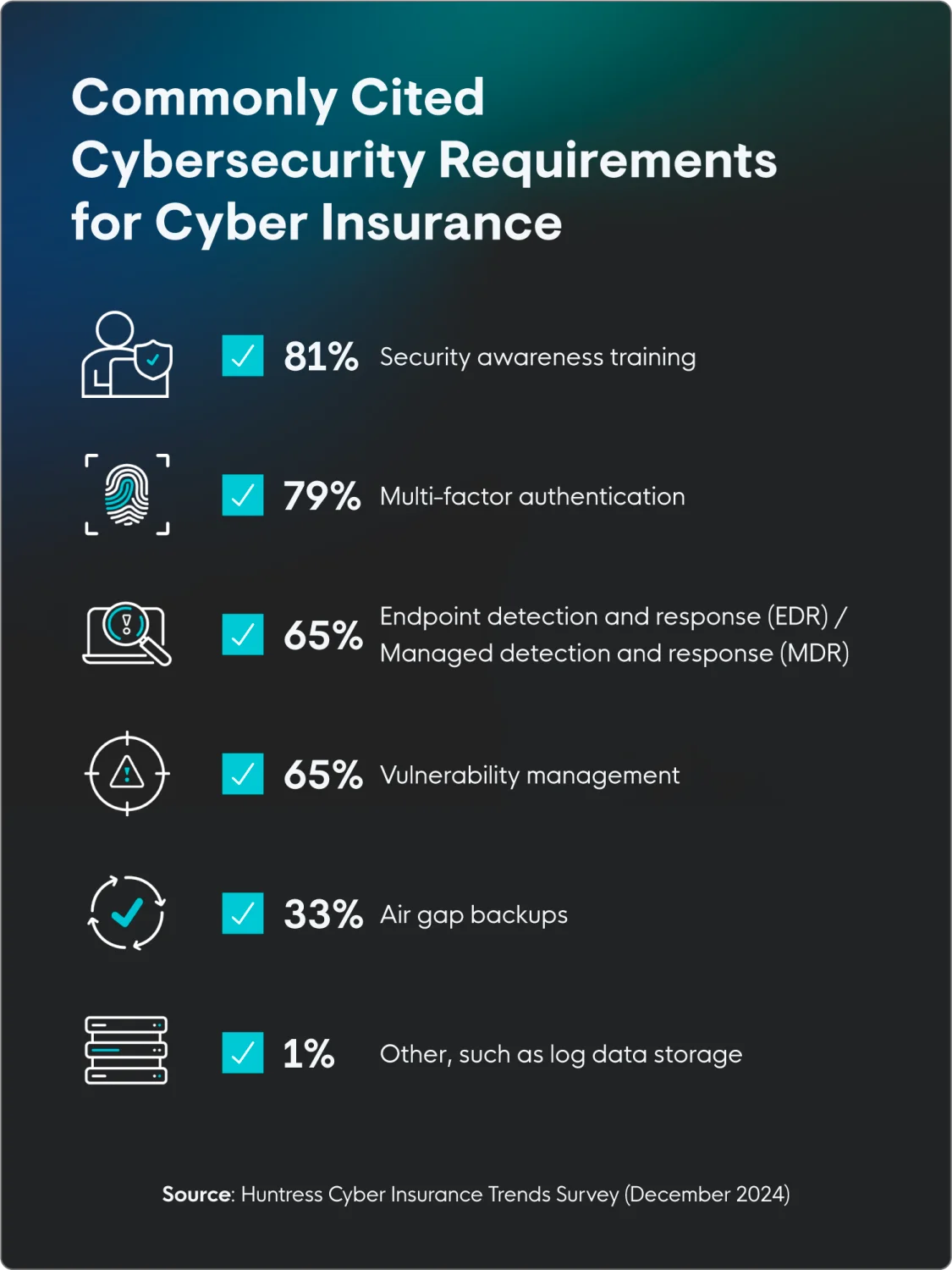
Insurers Require Several Cybersecurity Measures To Access Coverage
Seth Geftic, VP of product marketing at Huntress, has seen how cyber insurance trends have developed over the years. Businesses are more interested than ever in buying cyber insurance, but there’s also more of a burden on the company needing coverage to have certain protections in place. Geftic says that cyber insurance is “becoming a lot more expensive, cyber insurers are covering less, and they're requiring you to have more safeguards in place to be covered.”
For organizations that have coverage now, cyber insurer compliance requires:
- Security awareness training: 81% of organizations have this as a prerequisite for coverage
- Multi-factor authentication: 79%
- Endpoint detection and response (EDR) / managed detection and response: 65%
- Vulnerability management: 65%
- Air gap backups: 33%
- Other, such as log data storage: 1%
Data Recovery Is the Most Commonly Covered Cyber Event
The majority of respondents (81%) were covered for data recovery, followed closely by data breaches (80%) and ransomware (63%). Some respondents also had coverage for business interruption/lost revenue (62%) and legal costs (59%). On the other hand, less than half of cybersecurity plans included coverage for:
- Third-party claims (50%)
- Forensic investigation costs (43%)
- Fines and penalties (42%)
- Public relations costs (40%)
What’s covered under a standard cyber insurance plan varies widely by provider, so it’s important to shop around for the right plan for your organization. Always carefully review the policy documents to understand exactly what cybersecurity threats are covered and excluded.
61% of Businesses Believe AI-Powered Attacks Are the Biggest Future Threat
When asked which emerging cyber threats will have the biggest impact on the cyber insurance industry in 2025, the majority of respondents (61%) were most concerned about AI-powered attacks. This was followed by cloud security breaches (24%), IoT (internet of things) device vulnerabilities (14%), and other factors like ransomware attacks (1%).
Insurers have started to adapt their policies to better reflect the growing concern that AI is changing the threat landscape. Businesses also need to adapt by strengthening their security posture, particularly in the area of identity and access management, and by staying informed about the evolving terms and conditions of cyber insurance policies.
What To Look For in a Cyber Insurance Policy
The coverage you’ll need depends on your organization’s specific needs, the size of your business, and your industry. Here are key factors to consider when choosing a cyber insurance plan:
- Coverage scope: Make sure the coverage is comprehensive for data breach response costs (legal fees, investigations, etc.), business interruption losses, cyber extortion, third-party liability, and regulatory fines.
- Deductibles: Choose a deductible that balances cost with the potential for frequent, smaller claims.
- Complete underwriting accurately. The policy and premium you receive are based on your responses and overstating your security measures will risk a full payout of the policy in the event of an incident.
- Insurer reputation: Pick an insurer with a strong track record in cyber insurance and a deep understanding of cyber threats.
- Exclusions: Make sure you understand your policy's limitations and that the limits are sufficient to cover potential losses based on your organization's size and industry.
- Claims process: Ask about the insurer's claims-handling process to determine if it’s compatible with your organization’s needs.
How Managed Cybersecurity and Cyber Insurance Go Hand in Hand
Geftic notes how cyber insurance is similar to other types of coverage in that insurers won't provide coverage (or cover less) unless you have proper security in place, like EDR or a SIEM. He adds, “Yes, someone robbed your house, but you didn't have a deadbolt, so we're not paying,” or at least, not covering the full claim amount.
In the same way that home insurance requires a homeowner to lock their doors, not leave any open flames unattended, and generally behave safely, cyber insurance providers require the same from their insurees.
To qualify for plans and receive coverage when needed, cyber insurance trends increasingly require organizations to have fail-safes already in place, like regular cybersecurity training, multi-factor authentication, and managed EDR.
See how Huntress can support your organization’s cyber safety and help you qualify for cyber insurance for added protection.
Sign up for a free EDR trial now.
FAQ
Is Cyber Insurance Growing?
Yes, the cyber insurance market has been growing significantly in recent years. The increasing frequency and severity of cyberattacks, along with evolving regulations and more awareness of data privacy risks, are driving demand. This is combined with multiple years of losses in the cyber insurance industry that are driving closer inspection of security controls before issuing a policy.
How Much Is Cyber Insurance?
On average, businesses pay a minimum of $25,000 per year for cyber insurance, ranging anywhere from $10,000 or less to more than $100,000.
How Big Is the Cyber Insurance Market in 2025?
The cyber insurance market is expected to reach $16.6 billion in 2025, an 8% increase over 2024.
What Percentage of Companies Have Cyber Insurance?
According to our survey data, 79% of companies have cyber insurance. This percentage varies depending on the specific size and industry of the organization.
Survey Methodology
The survey of 524 US IT security professionals age 25+ was conducted via Centiment Audience for Huntress between December 17 and 20, 2024. Data is unweighted and the margin of error is approximately +/-3% for the overall sample with a 95% confidence level.





















