At the end of the day, employees are the firewall. Cybersecurity training is about building a workforce that doesn’t just know about threats but knows how to respond instinctively to them.
This guide is designed for business leaders, IT teams, and compliance managers who know they need more than mere surface-level awareness. These resources give you actionable frameworks, program templates, and strategies that build resilience that lasts.
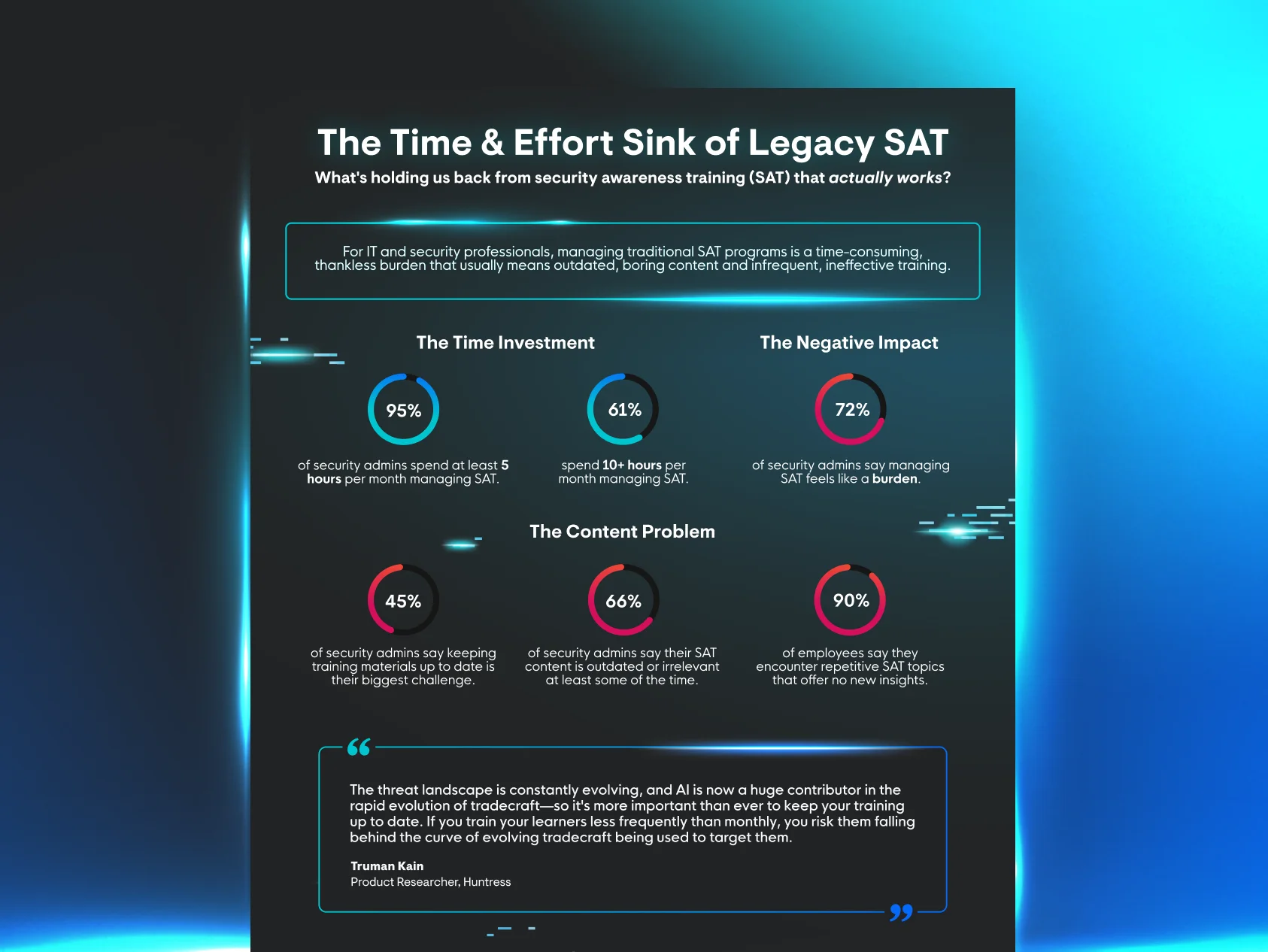
We developed this guide because too many programs fail to move the needle. We’ve seen the difference real-world training makes. Huntress Managed Security Awareness Training (SAT) blends story-driven lessons, phishing simulations, and expert-led oversight to drive real behavioral change. We help organizations train employees like they’re part of the security team—because they are.