Spear phishing is one of the most dangerous and deceptive cyberattacks today, preying on human trust rather than technical vulnerabilities. Unlike broad phishing scams that cast a wide net, spear phishing is laser-focused, meticulously crafted to manipulate specific individuals or organizations. And that’s what makes it so effective.
For IT professionals, understanding spear phishing isn’t just another skill—it’s an essential line of defense in today’s cybersecurity landscape. In this guide, we’ll break down how it works, why it’s so effective, and what you can do to protect yourself and your organization.
What is Spear Phishing?
Spear phishing is a targeted form of phishing where cybercriminals attempt to steal data, install malware, or gain unauthorized access by crafting personalized, convincing messages.
Unlike standard phishing emails that blast thousands of generic messages, spear phishing emails are carefully tailored using details like your name, job role, or even recent activities. This level of personalization makes the attack feel real, increasing the chances that the victim will click a malicious link, download an attachment, or unknowingly share sensitive information.
What’s the Difference?
Phishing vs. Spear Phishing vs. Whaling
It’s easy to mix up different types of phishing attacks, so here’s a quick breakdown:
- Phishing: Mass emails sent to countless recipients, hoping someone falls for the bait. Think of it as the “shotgun approach.”
- Spear Phishing: A highly personalized attack aimed at a specific person or organization, often using details from social media, company websites, or leaked data.
- Whaling: A spear phishing attack targeting high-level executives or decision-makers, often to steal financial data or sensitive company information.
How Does Spear Phishing Work?
Spear phishing isn’t just about sending an email—it’s a multi-step process that often involves detailed research before the attack even begins.
1. Reconnaissance (Research & Preparation)
Attackers study their targets using publicly available information—LinkedIn profiles, company websites, even social media posts. For example, if your company just announced a new software update, an attacker might send an email pretending to be from IT, asking employees to log in to "verify" the update.
2. Crafting the Bait (The Hook)
Next, the attacker creates a convincing email designed to look like it’s from a trusted source—a manager, a vendor, or even the CEO. They may replicate official email templates, company logos, and formatting to make the email appear legitimate.
3. The Attack (Taking the Bait)
The victim receives the email and is encouraged to take action—clicking a link, downloading an attachment, or entering login credentials. Because the message often feels urgent and personal, many people fall for it.
4. Exploitation (The Damage Is Done)
Once the victim takes the bait, the attacker moves fast. They might steal passwords, install malware, gain unauthorized access to internal systems, or even launch further attacks from inside the company’s network.
The Social Engineering Tricks Behind Spear Phishing
Spear phishing is so effective because it relies on social engineering—the art of manipulating people into making security mistakes. Here are the most common techniques attackers use:
- Pretexting: Creating a fake but believable scenario, like an urgent email from IT asking you to reset your password.
- Urgency & Fear: Making the recipient panic—e.g., “Your account will be locked in 24 hours unless you verify your identity.”
- Impersonation: Pretending to be a trusted individual, such as a coworker, vendor, or even a CEO.
- Emotion Manipulation: Playing on fear, curiosity, or trust—like an email claiming suspicious activity on your account or an overdue invoice that needs immediate attention.
The Growing Role of AI in Spear Phishing
Here’s the scary part—cybercriminals are now using AI to make spear phishing even more convincing.
AI-powered tools can:
- Automate reconnaissance, scanning the web for personal details about potential victims.
- Generate phishing emails that mimic a person’s writing style, making them feel even more authentic.
- Use deepfake audio or video to impersonate executives, potentially tricking employees into transferring money or sharing sensitive data.
The result? Attacks that are harder to detect than ever before.
Who Are the Most Common Targets of Spear Phishing?
Cybercriminals don’t just target random individuals—they go after people who have access to valuable information:
- Finance & HR Teams: They handle payroll, invoices, and financial transactions, making them high-value targets.
- New Employees: Less familiar with company security policies, making them easier to trick.
- Executives & Leadership: High-level targets (whaling attacks) due to their access to critical corporate data.
How to Spot a Spear Phishing Email
Here are some common red flags to watch out for:
- A sense of urgency: “Your account will be suspended if you don’t act now!"
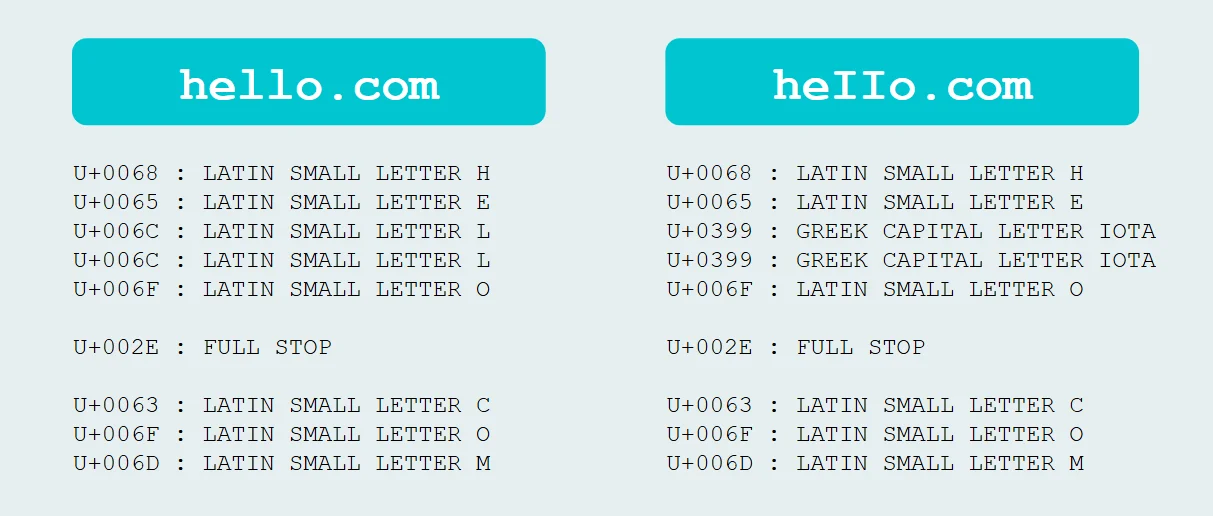
- A sender email that looks slightly off: A fake domain like @yourcompany-security.com instead of @yourcompany.com.
- Odd grammar or phrasing: Sometimes subtle, but noticeable.
- Suspicious links or attachments: Especially if they’re unexpected.
- Requests for sensitive information: No real company will ask for your password via email.
How to Protect Your Organization
You can’t stop spear phishing emails from landing in inboxes—but you can make sure employees know how to handle them.
1. Security Awareness Training
Teach employees how to spot phishing attempts with regular training and simulated phishing tests.
2. Enable Multi-Factor Authentication (MFA)
Even if an attacker gets a password, MFA adds an extra layer of security—like a one-time code from an authenticator app.
3. Use Advanced Email Security Tools
Filters, spam detection, and authentication protocols like DMARC, SPF, and DKIM can block some phishing emails before they reach employees.
4. Keep Software & Systems Updated ("patch, patch, patch")
Many attacks exploit outdated software, so regular updates and patches are a must.
5. Verify Links & Sender Info
Encourage employees to hover over links before clicking and verify sender email addresses.
How to Protect Your Organization
Spear phishing thrives on deception, but with the right training, tools, and awareness, organizations can fight back. Cybersecurity isn’t just about technology—it’s about people. And the more informed your team is, the harder it becomes for attackers to succeed.
- Train your employees
- Use multi-layered security
- Stay proactive with threat detection
Because when it comes to spear phishing, a little caution can save millions.

Related Resources


Protect What Matters
Sign up for a free Huntress Managed Security Awareness Training trial and empower your employees with the knowledge to outsmart attackers.