Microsoft's recent troubles with fake login pages. Amazon scam sites stealing customer data. Tesla impersonators spreading malware through social media. These aren't random cyber incidents—they're all examples of brandjacking, a cybersecurity threat that's becoming increasingly sophisticated and dangerous.
While most security teams focus on protecting their internal networks, brandjacking attacks bypass traditional defenses by exploiting something that exists entirely outside your security perimeter: your brand's reputation and identity.
See how Huntress protects you from brandjacking and more. Get a demo
What is Brandjacking?
Brandjacking is the unauthorized use of a company's brand identity—including logos, domain names, social media profiles, and other brand assets—to deceive victims and carry out malicious activities. Originally a marketing concern focused on trademark violations, brandjacking has evolved into a serious cybersecurity threat vector.
In the cybersecurity context, brandjacking encompasses several key tactics:
Domain hijacking and subdomain takeover: Registering domains similar to legitimate brands or taking control of abandoned subdomains
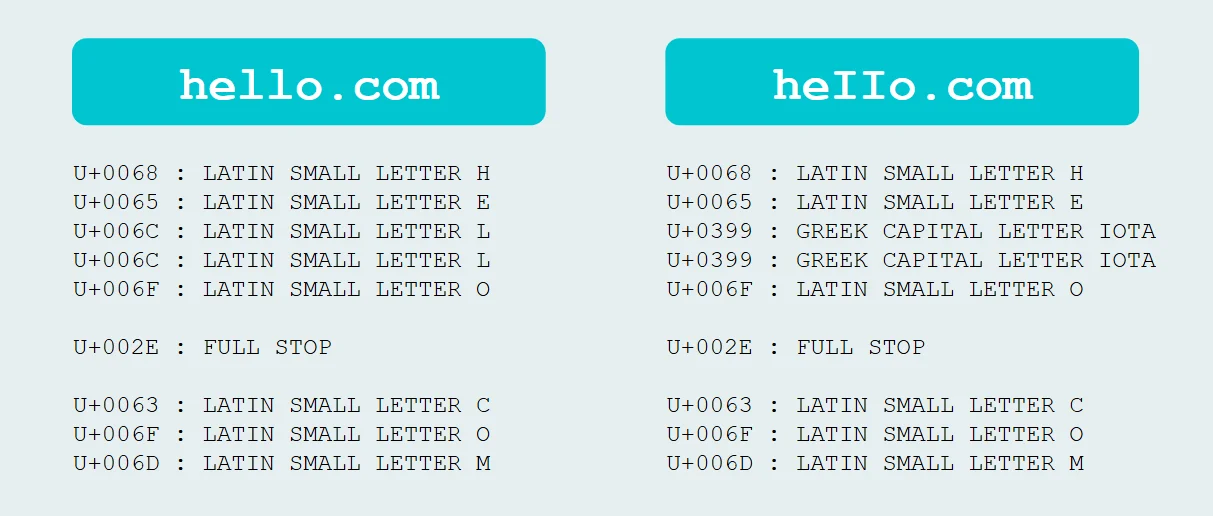
Typosquatting: Creating websites with slightly misspelled versions of popular domain names
Social media impersonation: Creating fake profiles that mimic legitimate brands on social platforms
Fake websites: Building convincing replicas of legitimate sites to harvest credentials or distribute malware
Malicious packages: Publishing fake software packages that impersonate legitimate open-source libraries
The attacker's ultimate objectives vary but typically include data theft, credential harvesting, malware distribution, financial fraud, and damaging the target organization's reputation.
Why Brandjacking Matters in Cybersecurity
Bypasses Traditional Security Controls
Traditional cybersecurity defenses are designed to protect your internal network perimeter. Brandjacking attacks operate entirely outside this boundary, making them particularly dangerous. When attackers impersonate your brand, they can:
Launch phishing campaigns that appear to come from trusted sources
Compromise supply chain security by distributing malicious packages under your brand
Exploit customer trust to bypass user skepticism about suspicious emails or websites
Operational Risk Amplification
Brandjacking creates operational risks that extend far beyond typical cyber threats. These attacks can:
Damage customer relationships and erode brand trust built over years
Create legal liability when customers fall victim to brand impersonation scams
Generate significant incident response costs as teams scramble to identify and shut down impersonation sites
Impact business operations when customers lose confidence in legitimate communications
Expanding External Attack Surface
Modern businesses have moved beyond traditional network perimeters. Your external attack surface now includes:
Social media presence across multiple platforms
Domain registrations and subdomain configurations
Third-party integrations and partnerships
Customer communication channels
Each of these represents a potential brandjacking target that may not be monitored by conventional security tools.
AI-Powered Threat Evolution
Emerging technologies are making brandjacking more sophisticated and harder to detect. AI and machine learning enable:
Automated generation of convincing fake websites and social media profiles
Deepfake technology for video and audio impersonation
Natural language processing to create believable phishing content
Scaled attacks targeting multiple brands simultaneously
How Brandjacking Works: Anatomy of an Attack
Phase 1: Reconnaissance
Attackers begin by researching target brands to understand their digital footprint, including domain structures, social media presence, and customer communication patterns. They look for vulnerabilities such as:
Expired or abandoned subdomains
Unused social media handles
Similar available domain names
Brand assets that can be easily replicated
Phase 2: Asset Creation
Based on reconnaissance findings, attackers create malicious assets designed to impersonate the target brand:
Typosquatting domains: Registering variations like "amazom.com" instead of "amazon.com"
Subdomain takeover: Taking control of abandoned subdomains like "old-portal.company.com"
Fake social profiles: Creating convincing Facebook, Twitter, or LinkedIn accounts using stolen brand assets
Malicious search ads: Bidding on the target's brand name to display fake advertisements in search results
Phase 3: Distribution and Exploitation
Attackers use the impersonation assets to carry out their objectives:
Sending phishing emails that appear to come from the legitimate brand
Hosting fake login pages to harvest credentials
Distributing malware through fake software downloads
Conducting social engineering attacks via impersonated social media accounts
Indicators of Compromise
Security teams should monitor for these brandjacking warning signs:
Unusual domain registrations containing your brand name or variations
Spikes in social media mentions from unverified accounts
Customer complaints about suspicious communications claiming to be from your organization
Phishing attempts targeting your customers using your brand assets
Search results showing unfamiliar websites using your branding
Detection, Prevention & Response Strategies for Security Teams
Proactive Monitoring
Implement comprehensive brand monitoring across multiple channels:
Domain monitoring: Use automated tools to detect new domain registrations containing your brand name or variations
Social media monitoring: Set up alerts for unauthorized use of your brand assets across social platforms
Search engine monitoring: Track search results for your brand to identify fake websites or malicious advertisements
Package repository monitoring: Monitor software repositories for packages that might impersonate your legitimate software
Technical Controls
Deploy technical safeguards to make impersonation more difficult:
Email authentication: Implement DMARC, DKIM, and SPF records to prevent email spoofing
Domain registration practices: Proactively register common misspellings and variations of your domain
Subdomain hygiene: Regularly audit and clean up unused subdomains to prevent takeover
SSL certificate monitoring: Monitor certificate transparency logs for unauthorized certificates issued for your domains
Incident Response Planning
Develop specific procedures for brandjacking incidents:
Rapid response team: Designate team members responsible for brandjacking incident response
Takedown procedures: Establish relationships with domain registrars, hosting providers, and social media platforms for quick removal of impersonation sites
Legal escalation: Work with legal teams to pursue trademark violations and coordinate with law enforcement when appropriate
Customer communication: Prepare templates for notifying customers about impersonation attempts
Security Awareness Training
Education is crucial for both employees and customers:
Employee training: Teach staff to recognize brandjacking attempts and report suspicious activity.
Customer education: Provide guidance on how customers can verify legitimate communications from your organization
Security awareness: Include brandjacking scenarios in regular security awareness training programs
Huntress Managed SAT prepares learners for real threats through approachable and consumable content, immersive Threat Simulations, gamification, & more, making every learner an active participant in your company’s cybersecurity.
Cross-Functional Collaboration
Brandjacking spans multiple organizational functions:
Marketing teams: Can provide insight into brand assets and customer communication patterns
Legal departments: Essential for trademark protection and takedown procedures
IT security: Provides technical detection and response capabilities
Customer support: Often the first to hear about impersonation attempts from customers
Advanced Defense Strategies
Consider implementing advanced protection measures:
External attack surface management (EASM): Use specialized tools to continuously monitor your external digital footprint
Digital risk protection (DRP): Deploy comprehensive solutions that monitor for brand abuse across the internet
Threat intelligence: Subscribe to threat feeds that include brandjacking indicators specific to your industry
Automated response: Implement tools that can automatically initiate takedown requests for obvious impersonation attempts
Implications for Enterprise Cybersecurity Programs
Risk Assessment Integration
Brandjacking should be incorporated into formal risk assessment frameworks:
Asset inventory: Include external brand assets (domains, social media accounts, etc.) in your asset inventory
Threat modeling: Consider brandjacking scenarios when modeling threats to customer-facing systems
Third-party risk: Evaluate how partner organizations might be targeted for brandjacking that affects your brand
Metrics and KPIs
Track brandjacking defense effectiveness through specific metrics:
Time to detection: How quickly you identify new impersonation attempts
Time to takedown: How long it takes to remove malicious content after detection
Customer impact: Number of customers affected by brandjacking incidents
Cost per incident: Total cost including detection, response, and remediation activities
Future Considerations
Prepare for evolving brandjacking threats:
AI-generated content: Develop capabilities to detect AI-created fake websites and social media content
Deepfake detection: Consider tools and training for identifying synthetic media impersonating your executives
Regulatory compliance: Monitor emerging regulations that may require specific brandjacking protections
Supply chain integration: Work with suppliers and partners to ensure they're also protected against brandjacking
Frequently Asked Questions
While phishing attacks may use brand impersonation as a technique, brandjacking refers more broadly to the unauthorized use of a brand's entire identity for malicious purposes. Phishing typically focuses on stealing credentials or personal information through deceptive emails or websites, while brandjacking encompasses a wider range of activities including domain hijacking, social media impersonation, and malicious package distribution. Think of brandjacking as the overarching attack method, with phishing being one possible outcome.
Watch for these key indicators: unusual domain registrations containing your brand name or similar variations, spikes in social media mentions from unverified accounts, customer complaints about suspicious communications claiming to be from your organization, and phishing attempts targeting your customers using your brand assets. Implement automated monitoring tools to track domain registrations, social media mentions, and search engine results for your brand name.
The most prevalent techniques include typosquatting (registering domains with slight misspellings of legitimate brands), social media spoofing (creating fake profiles that mimic real brands), domain hijacking or subdomain takeover (gaining control of legitimate but abandoned domains), malicious search engine advertisements impersonating brands, and fake software packages that impersonate legitimate open-source libraries.
Implement these key controls: proactive domain registration of common misspellings and variations, email authentication protocols (DMARC, DKIM, SPF), regular subdomain auditing and cleanup, automated brand monitoring across digital channels, SSL certificate transparency monitoring, and strong trademark protection practices. Additionally, deploy external attack surface management tools and establish relationships with domain registrars for quick takedown procedures.
Brandjacking prevention requires collaboration between multiple teams. Cybersecurity teams (led by the CISO) should handle technical detection and incident response, marketing teams provide insight into brand assets and customer communication patterns, legal departments manage trademark protection and takedown procedures, and IT departments implement technical controls. Customer support teams often serve as early warning systems since they frequently receive reports of suspicious communications from customers.
Absolutely. Small and medium-sized businesses may actually be more vulnerable to brandjacking because they typically have fewer resources dedicated to monitoring and enforcement. Attackers often target smaller brands because they're less likely to have comprehensive brand protection measures in place. However, the reputational damage from brandjacking can be proportionally more devastating for smaller businesses that rely heavily on customer trust and word-of-mouth marketing.
AI and deepfake technology are making brandjacking attacks more sophisticated and harder to detect. Attackers can now use AI to automatically generate convincing fake websites, create realistic social media profiles at scale, produce synthetic media (audio and video) impersonating company executives, and craft more believable phishing content using natural language processing. Organizations should prepare for these advanced threats by investing in AI-powered detection tools and training employees to recognize synthetic media indicators.


Building Resilient Brand Protection
Brandjacking represents a fundamental shift in the cybersecurity threat landscape. As businesses become more digital and customer-facing, protecting your brand identity becomes as critical as protecting your network infrastructure.
Effective brandjacking defense requires a holistic approach that combines technical controls, process improvements, and cross-functional collaboration. Organizations that treat brand protection as a core security function—rather than just a marketing concern—will be better positioned to maintain customer trust and business continuity.
The key is to start monitoring and protecting your external digital presence before you become a target. By implementing proactive detection, building incident response capabilities, and fostering collaboration between security, marketing, and legal teams, you can significantly reduce your exposure to brandjacking attacks.
Remember: your brand is often the most valuable asset your organization has. In an era where trust and reputation can be damaged instantly but take years to rebuild, protecting your brand from cybersecurity threats isn't optional—it's essential.

Related Resources


Protect What Matters