Credential theft has become one of the most pervasive threats in cybersecurity, impacting businesses, individuals, and governments alike. From phishing scams to advanced malware, attackers are finding increasingly sophisticated ways to steal usernames, passwords, and other login credentials to infiltrate systems, compromise sensitive information, and cause widespread damage.
If you’re responsible for safeguarding your business environment or want to better understand the risks credential theft poses, this guide is for you. Below, we’ll explore the tactics hackers use, notable real-world examples, and, most importantly, how to detect and prevent credential theft.
Let’s jump in.
What Is credential theft?
At its core, credential theft refers to the unauthorized acquisition of login credentials like usernames, passwords, or authentication keys. These stolen credentials are then used by adversaries to impersonate legitimate users, gain unauthorized access, and perform malicious activities such as data theft, financial fraud, and more.
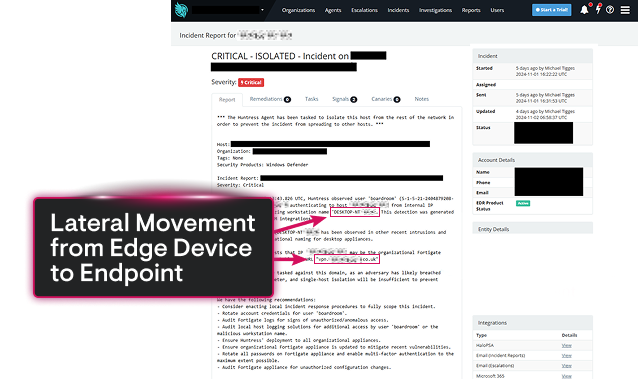
Credential theft is often the first step in a larger campaign, giving attackers initial access that can lead to lateral movement within a network, privilege escalation, and advanced persistent threats (APTs).
Here’s what makes credential theft particularly dangerous:
Low Detection Rate: Stolen credentials allow attackers to blend in with regular user activity.
High Success Rate: Many breaches start by exploiting weak or reused passwords.
Automation and Scale: Attackers use tools to steal, test, and deploy credentials at scale in automated campaigns.
Common methods of credential theft
1. Phishing
Phishing attacks trick users into willingly handing over their login credentials. Attackers create fake emails or websites that mimic trusted organizations (banks, retailers, SaaS applications) and lure victims into entering sensitive data.
Example: You receive an email from “@yourbank-secure.com” asking you to verify your account. Clicking the link leads to a fake login page that looks identical to your bank’s portal.
Why it works: Social engineering preys on trust and urgency.
2. Keyloggers and Malware
Keyloggers are malicious programs or physical devices that record keystrokes, capturing anything typed on a keyboard, including login credentials. Often delivered via infected attachments or downloads, keylogging malware silently collects data without user awareness.
Example: An employee downloads an attachment from an unknown source, triggering a keylogger that captures company email client logins.
Why it works: Victims remain unaware that their credentials are being logged and sent to attackers.
3. Credential Dumping
Credential dumping involves extracting credentials stored in plaintext or hashed forms on devices, networks, or applications. Hackers use tools like Mimikatz to obtain password hashes stored in memory (e.g., from LSASS on Windows).
Example: A hacker gains administrative access to a system and uses credential dumping tools to extract the passwords of other accounts stored in memory.
Why it works: It exploits internal system weaknesses to get additional access deeper in the network.
4. Brute Force and Dictionary Attacks
Attackers use automated tools to systematically guess passwords. Brute force tests every possible combination, while dictionary attacks rely on a pre-defined list of common passwords.
Example: A bot targets an admin login portal, cycling through millions of password combinations until it succeeds.
Why it works: Weak passwords and lack of account lockout policies make accounts easy targets.
5. Adversary-in-the-Middle (AitM) Attacks
AitM attackers intercept credentials as they are transmitted between a user and a legitimate server. Techniques like SSL stripping and malicious Wi-Fi hotspots make this possible.
Example: You log in to your cloud storage account while on an unsecured public Wi-Fi network. Meanwhile, an attacker captures your session data.
Why it works: Vulnerabilities in network security make it easy to intercept sensitive traffic.
6. Social Engineering and Insider Threats
Adversaries exploit employees or insiders to obtain credentials through manipulation or direct persuasion. Sometimes these insiders willingly assist attackers for financial incentives.
Example: A hacker impersonates an IT admin and convinces an employee to disclose their account login information.
Why it works: Relies on human errors or intentional exploitation.
Real-world examples of credential theft
1. The Colonial Pipeline Attack (2021)
Using stolen credentials, hackers infiltrated Colonial Pipeline’s network, halting operations and causing fuel shortages across the United States. This breach resulted in millions of dollars in ransom payments and reputational damage.
2. Uber (2022)
In 2022, attackers stole an employee’s credentials to access Uber’s internal Slack and cloud accounts, giving them entry to sensitive systems, source code, and databases, demonstrating how a single compromised account can cause widespread operational and reputational damage.
What these attacks highlight is how stolen credentials allow attackers to inflict devastating operational, financial, and reputational harm across industries.
How to detect credential theft
Detecting credential theft early is critical to mitigating its impact. Here’s what to look for:
Unusual Login Behavior: Monitor for anomalies like “impossible travel” (simultaneous logins from two geographically distant locations).
Login Spikes: A surge in login attempts from certain IP addresses or locations may indicate automated credential testing.
Indicators of Compromise (IoCs): Suspicious activities, including unauthorized privilege escalations, abnormal account activity, or new applications being installed.
Exploration of Breach Discovery Tools: Use tools like Security Information and Event Management (SIEM), User and Entity Behavior Analytics (UEBA), and Endpoint Detection and Response(EDR) to automate anomaly detection.
Dark Web Monitoring: Track stolen or leaked credentials using threat intelligence platforms to alert you if your organization’s accounts are compromised.
Steps to prevent credential theft
Taking proactive measures to secure your organization can prevent successful credential theft campaigns from achieving their goals.
1. Enforce Strong Password Policies
Use complex, unique passwords. (Avoid common passwords)
Avoid reusing passwords across platforms.
Deploy password managers to generate and store credentials securely.
2. Implement Multi-Factor Authentication (MFA)
Add an extra layer of protection by requiring a secondary form of identification, such as a one-time password (OTP), push notification, or biometrics.
3. Train and Educate Users
Recognize phishing emails or websites.
Avoid clicking on suspicious links or attachments.
Validate requests for login credentials via independent channels.
4. Leverage Technology
Deploy enterprise-grade cybersecurity solutions, including:
Single Sign-On (SSO) for secure access management.
Behavioral monitoring to flag suspicious account activity.
Identity and Access Management (IAM) tools to enforce least privilege access and secure sensitive accounts.
5. Conduct Regular Security Audits
Perform routine penetration testing and red-teaming exercises to identify vulnerabilities in your systems before attackers do.
Credential theft vs credential stuffing vs password spraying
To further differentiate these attack methods:
Credential Theft refers to acquiring login credentials via phishing, malware, or breaches.
Credential Stuffing uses leaked passwords from one breach to try accessing accounts on other sites.
Password Spraying involves testing common passwords (e.g., “123456”) across multiple accounts to avoid detection from failed logins.
Each technique has unique characteristics, but layered defenses (like MFA) can protect against all.
FAQs about credential theft in cybersecurity
Attackers are sneaky, and they’ve got plenty of tricks up their sleeves, including:
Phishing emails that lure you into giving up your info
Keyloggers and malware that spy on what you type
Man-in-the-middle (MitM) attacks that intercept your data
Credential dumping tools like Mimikatz
Good old-fashioned social engineering that tricks people into spilling the beans
At the end of the day, they’re banking on human error (a.k.a. us making mistakes), unpatched vulnerabilities, or weak passwords.
This is where things get dicey. Once attackers have your credentials, they might:
Take over your account (hello, account lockout)
Escalate privileges or move laterally through your network
Sell your login info on the dark web (not exactly eBay-friendly)
Launch credential stuffing attacks to break into your accounts on other platforms
The fallout? Data theft, financial fraud, or even full-on breaches. Not great.
Good news— tools and strategies exist to catch this stuff before it spirals. Credential theft detection often involves:
Behavioral monitoring to flag sketchy login patterns (e.g., impossible travel)
Endpoint detection and response (EDR) tools
SIEM platforms that sound the alarm on out-of-the-ordinary access events
Dark web monitoring tools to see if your credentials are for sale
Watching for failed login spikes or suspicious MFA bypass attempts
It’s like setting up a cybersecurity tripwire.
Here’s the playbook for locking down your credentials and keeping attackers out of your business:
Rock strong, unique passwords (no “Password123,” please)
Enable multi-factor authentication (MFA) everywhere you can
Teach your team to recognize phishing attempts (phishy emails belong in the trash 🗑️)
Deploy endpoint protection and secure email gateways
Regularly audit credentials and rotate them as needed
Use password managers and single sign-on (SSO) tools to simplify and strengthen security
Think of this as your cyber suit of armor.
Not exactly. Phishing is just one method of stealing credentials, where attackers trick you into handing over your login details (usually through bogus websites or scammy emails). Credential theft covers way more ground, including malware-based attacks, credential dumping, and straight-up con jobs.
The right tools make all the difference. Here’s a cheat sheet for bolstering your defenses:
EDR solutions, like Huntress Managed EDR
ITDR solutions, like Huntress Managed ITDR
SIEM platforms, like Huntress Managed SIEM
MFA providers
Password managers
Dark web monitoring tools
Pair these with a solid dose of user training, and you’ll have a solid shot at stopping credential theft in its tracks.
Why Huntress for credential theft detection
Credential theft continues to evolve as attackers gain access to automation, advanced tools, and insider tactics. The combination of stolen credentials with social engineering can allow even the most secure systems to be breached.
By educating your team, enforcing technical safeguards, and being watchful for warning signs, your organization can reduce its vulnerability to credential-based attacks.
Remember, it only takes one compromised credential to jeopardize your entire security infrastructure.
Take the first proactive step today by starting a free trial of Huntress today.



Related Resources


Protect What Matters