C2 (Command and Control) in cybersecurity refers to the communication infrastructure that allows attackers to remotely control compromised devices or systems within a target network. It's essentially the digital "phone line" between cybercriminals and their malware.
TL;DR
C2 infrastructure is how hackers stay connected to your compromised systems after the initial breach. Think of it as their remote control—they use various communication channels (like HTTP(S), DNS, SSH, ICMP, Discord, Slack, or even social media) to send commands, steal data, and maintain persistence in your network. Understanding C2 is crucial because disrupting these communication channels can stop an attack in its tracks.
C2 represents one of the most importantfinal stages in a cyberattack, occurring after initial system compromise and enabling the more damaging aspects of a cyberattack, such as ransomware or data theft, to properly execute.but before major damage like data theft or ransomware deployment. This makes it a critical point for defense—catch the C2 traffic, and you can potentially stop the attack before it achieves its goals.
Understanding command and control infrastructure
Command and Control infrastructure serves as the backbone for sophisticated cyberattacks. Once attackers gain initial access to a system through methods like phishing emails or exploiting vulnerabilities, they need a way to communicate with their malware and issue further instructions.
The basic process works like this: malware installed on a compromised system "phones home" to the attacker's C2 server, checking for new commands. The attacker can then instruct the malware to steal data, spread to other systems, download additional payloads, or remain dormant until needed.
According to the MITRE ATT&CK framework, there are over 16 different command and control techniques that attackers use, ranging from simple HTTP communications to sophisticated methods using social media platforms or encrypted channels.
How C2 communications work
The communication between compromised systems and C2 servers typically follows a pattern called "beaconing." The infected device regularly contacts the C2 server at predetermined intervals, much like checking for text messages.
This allows attackers to:
Send new instructions to the malware
Download additional malicious tools
Collect stolen data from the victim's network
Maintain persistence even if some communication channels are discovered
Rapidly respond to changes in the targeted environment
Attackers often disguise their C2 traffic to look like legitimate network activity. They might use common protocols like HTTPS or DNS, or even hide commands in seemingly innocent social media posts or cloud storage services. This camouflaging makes detection significantly more challenging for security teams.
The sophistication of modern C2 infrastructure often includes redundancy measures. If one communication channel is blocked, the malware can automatically switch to backup channels, ensuring the attacker maintains control even under adverse conditions.
Common C2 techniques and methods
Traditional network protocols
Most C2 communications use standard internet protocols to blend in with normal traffic:
HTTP/HTTPS: The most common method, as web traffic is typically allowed through firewalls
DNS: Attackers can hide commands in DNS queries, which are essential for normal internet function. They may even embed their own DNS configurations into their malware in order to ensure communication.
Email: Commands can be embedded in email communications or attachments
FTP/SFTP: File transfer protocols can be used for both command delivery and data exfiltration
Social media and web services
Modern attackers increasingly leverage legitimate platforms:
Twitter/X: Commands hidden in tweets or direct messages
Facebook: Instructions embedded in posts or comments
GitHub: Code repositories used to host malicious payloads
Cloud storage: Services like Dropbox or Google Drive for command delivery via malicious docs
Messaging: Real time messaging platforms such as Slack, Telegram, and Discord for command delivery via messages, bots, or other embedded automations
Advanced obfuscation techniques
Sophisticated threat actors employ various methods to avoid detection:
Domain generation algorithms (DGAs): Automatically creating new domain names to evade blocklists
Fast Flux: Rapidly changing IP addresses associated with malicious domains
Domain fronting: Using popular CDN services such as Cloudfront or Cloudflare to mask the real infrastructure
Encrypted channels: Using encryption to hide the true nature of communications
Traffic mimicry: Making malicious traffic appear identical to legitimate applications
According to research from cybersecurity firms, attackers are increasingly using legitimate services because they're harder to block without disrupting normal business operations.
Notable C2 infrastructures
Several high-profile cyberattacks have showcased sophisticated C2 implementations:
Cobalt Strike: Originally a legitimate penetration testing tool, Cobalt Strike has become one of the most abused C2 frameworks. Its "Beacon" payload can communicate through HTTP, HTTPS, DNS, and even named pipes, making it incredibly versatile for attackers.
APT29 (Cozy Bear): This Russian advanced persistent threat group has used innovative C2 methods, including hiding commands in the metadata of images posted to social media platforms and using cloud storage services for command delivery.
Emotet banking trojan: Before its takedown, Emotet used a sophisticated C2 network with multiple layers of proxies and compromised legitimate websites as command servers, making it extremely resilient to disruption efforts.
Government response and takedowns
The FBI and international partners have conducted several successful C2 infrastructure takedowns. The 2021 Emotet takedown involved coordinated efforts across multiple countries to seize C2 servers and disrupt the botnet's communication channels.
Similarly, the 2023 Qakbot takedown demonstrated how law enforcement can infiltrate C2 networks, using the attackers' own infrastructure against them to deliver uninstall commands to infected systems.
Detection and defense strategies
Network monitoring approaches
Effective C2 detection requires comprehensive network visibility:
Traffic analysis: Looking for unusual patterns in network communications
DNS monitoring: Identifying suspicious domain requests or unusual query patterns
Behavioral analysis: Detecting anomalous behavior that might indicate C2 activity
Threat intelligence integration: Using known indicators of compromise to identify C2 infrastructure
Technical detection methods
Security teams can implement several technical measures:
Deep packet inspection: Analyzing the content of network communications via next general firewalls
Machine learning models: Using AI to identify subtle patterns that might indicate C2 traffic
Endpoint detection and response (EDR): Monitoring individual devices for signs of compromise
Host based firewalls: Enabling host based firewalls and allow-listing trusted binaries and processes to communicate outbound
Network segmentation: Limiting the potential impact of compromised systems
The challenge lies in balancing security with operational efficiency—overly aggressive filtering can disrupt legitimate business activities.
Prevention and mitigation strategies
Proactive measures
Organizations can implement several strategies to help prevent C2 establishment:
Regular security awareness training: Teaching employees to recognize phishing attempts and social engineering
Patch management: Keeping systems updated to prevent initial compromise
Application control: Limiting which programs can run on corporate systems
Network access control: Restricting outbound communications to necessary services only
NGAV and EDR: Deploying next generation anti-virus and endpoint detection and response are strong layers to prevent malware from taking a foothold
Incident response planning
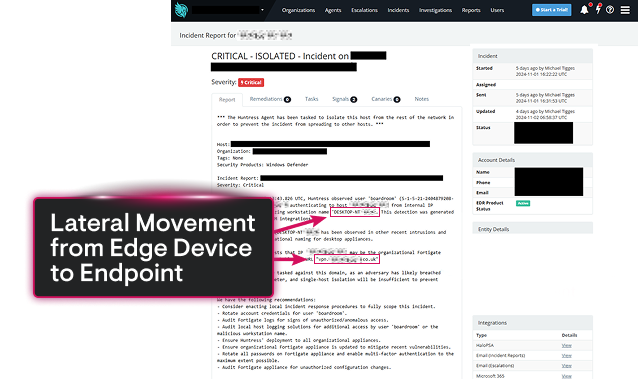
When C2 activity is detected, rapid response is crucial:
Isolation procedures: Quickly containing compromised systems
Forensic analysis: Understanding the scope and nature of the compromise
Communication protocols: Coordinating response efforts across teams
Recovery procedures: Safely restoring systems after the threat is eliminated
According to cybersecurity best practices, organizations should regularly test their incident response procedures through tabletop exercises and simulated attacks.
Frequently Asked Questions
C2 traffic is challenging to detect because attackers deliberately design it to mimic legitimate network communications. They use common protocols like HTTPS and DNS, employ encryption, and often route traffic through legitimate services that organizations rely on for daily operations. This camouflaging makes it nearly impossible to detect and risky to block without affecting business operationsfunctions.
Once initial access is gained, C2 communications can be established within minutes. Modern malware is designed to immediately "phone home" after infection, often using multiple communication channels simultaneously to ensure reliability. Some advanced malware can establish backup C2 channels within hours of initial compromise.
While most C2 communications rely on internet connectivity, some advanced malware can use alternative methods like USB drives, local network communications, or even radio frequencies in air-gapped environments. However, these methods are less common and typically associated with nation-state actors.
When C2 communications are successfully blocked, the malware becomes largely ineffective. Without instructions from the attacker, most malware will either remain dormant or follow pre-programmed instructions. However, sophisticated malware often includes multiple fallback communication methods, so blocking one channel doesn't guarantee the threat is eliminated.
Law enforcement agencies work with international partners to identify and seize C2 servers, often coordinating simultaneous actions across multiple countries. They may also work with internet service providers to redirect malicious traffic or use legal processes to take control of domain names associated with C2 infrastructure.


Key Takeaways
Understanding C2 infrastructure is essential for modern cybersecurity defense. These communication channels represent a critical vulnerability in the attack chain—successfully disrupting C2 can stop even sophisticated attacks before they achieve their objectives.
Organizations should focus on implementing comprehensive network monitoring, maintaining updated security tools, and developing robust incident response procedures. The key is achieving visibility into network communications while maintaining the operational flexibility needed for business success.
Remember that C2 detection and prevention require ongoing effort and attention. Threat actors continuously evolve their techniques, making it essential for security teams to stay informed about emerging trends and adapt their defenses accordingly.

Related Resources


Protect What Matters