Cybersecurity isn’t easy. Every day, attackers get a little smarter and a little quicker. And they always seem to have another trick up their sleeve. Keeping up can feel like an endless game of cat and mouse, but the stakes are way higher than any game. It's your data, your business, and your reputation on the line.
That’s why tools like endpoint detection and response (EDR) have become critical in the fight against cyber threats. The problem is that EDR is evolving and isn't just about traditional AI and playbooks anymore. These are incredible parts of cybersecurity, being able to use intelligence models to anticipate and try to understand what attackers are trying to accomplish. The real magic happens when you combine EDR with behavioral analysis.
Let’s unpack what behavioral analysis really means, why it’s changing the game, and how it increases the overall effectiveness of EDR by focusing on behaviors—not just rules or known threats.
What’s Behavioral Analysis, Anyway?
Behavioral analysis is pretty much what it sounds like. It's about understanding what "normal" looks like across your systems and endpoints, and then flagging anything that seems out of the ordinary.
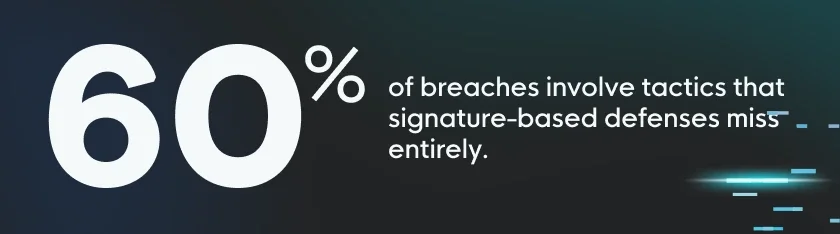
Think of it this way: if one of your employees suddenly starts logging in from two locations at the same time or accessing systems they never usually touch, behavioral analysis is what will pick that up. Traditional methods, like signature-based detection, rely on known patterns—they catch the bad guys only if the system recognizes their signature. But most modern attacks don’t leave an obvious signature. According to Verizon’s 2023 Data Breach Investigations Report (DBIR), 60% of breaches involve tactics that signature-based defenses miss entirely.
Behavioral analysis turns the tables by focusing on what’s happening right now, in real-time. It’s like that little extra intuition that says, “Something’s off here.”
Why Traditional EDR Alone Isn't Enough
By now, you’ve probably heard a lot about AI and playbooks. They’re the cornerstones of modern cybersecurity. But the truth is they’re not enough.
AI is awesome for spotting known patterns and automating tasks, but it’s only as good as the data it’s trained on. If it’s never seen a specific attack before, it could miss it.
Playbooks are basically pre-scripted responses to certain triggers. Great, right? Well, yes…unless the attack doesn’t match any of your pre-built scenarios.
The challenge is that cybercriminals innovate quickly. They’re not waiting for your AI to catch up, and they’re definitely not sticking to your playbooks. They’re finding new, creative ways to sneak in—and that’s where behavioral analysis steps up. It doesn’t need to know the attacker’s name, face, or MO. It just needs to see when something feels “off.”
How Behavioral Analysis Supercharges EDR
At Huntress, we’re doing something special by building our platform around behavioral analysis. Our guiding mindset is one where we assume that bad actors are already inside your system, and then we work backward from there. We can catch the subtle footholds attackers use to escalate their attacks before it’s too late.
Here’s how behavioral analysis adds a huge value boost to our Managed EDR solution:
- Real-time threat detection: Instead of waiting for a specific signature or rule-based alert, we watch for anomalies in behavior. Is that application suddenly accessing files it normally wouldn’t? Did a user log in unexpectedly, out of the blue? Behavioral analysis flags those instantly.
- Less noise and more signals: Security teams everywhere know the pain of false positives. In fact, 45% of alerts in most systems are false alarms. You end up wasting hours chasing down leads that turn out to be dead ends. Our behavioral analysis reduces false positives by understanding context—not every strange behavior is malicious, and our system knows the difference. Less noise means you can focus on what really matters.
- Human-powered threat hunting: We don’t rely solely on automation. Once an alert pops up, it’s reviewed by human threat hunters. Yep, real people. These cybersecurity experts validate the alert and, if necessary, escalate it. You’re not dealing with endless “cry wolf” scenarios. It’s high-fidelity alerts with real impact.

Stats That Tell the Story
According to Verizon’s 2023 DBIR, 80% of breaches involve stolen credentials. And, as you might’ve guessed, those won’t trigger your signature-based detection. Behavioral analysis, on the other hand, catches the weird ways those credentials are used, like logins from unusual locations or unusual times of day.
Based on Mandiant's M-Trends report, the average attacker stays hidden in a network for 24 days. That’s almost a month to roam around, escalate privileges, and exfiltrate data. Behavioral analysis spots the breadcrumbs early and stops attackers in their tracks.
The DBIR adds that 59% of organizations report a major improvement in detecting unknown threats once they add behavioral analysis to their toolkit. AI can’t learn fast enough to catch everything, but behavioral analysis can.
Why “Good Enough” Isn’t Good Enough
In cybersecurity, "good enough" just isn’t good enough. Traditional EDR systems—while better than nothing—leave too many gaps. They react to known threats, while hackers are busy cooking up unknown ones. Behavioral analysis changes that dynamic. It looks at what’s happening right now, in the moment, and flags anything that doesn’t line up with normal behavior.
This proactive approach is a game-changer. Attackers are getting more sophisticated, and your defense systems must be, too. We know that, and we’ve baked behavioral analysis into our EDR to stay ahead of the curve.
The Human Element—Why It Matters
Here’s something that often gets overlooked: the human element. That’s why we pair our behavioral analysis with a human threat hunting team. When the software says, “Hey, something’s not right,” the team jumps in, investigates, and confirms the threat.
This matters because it means you can trust the alerts you get. When Huntress sounds the alarm, it’s not just a system doing what it’s been programmed to do. It’s a team of experts saying, “This is real—take action now.”
Wrapping It Up
Behavioral analysis is transforming the way we approach cybersecurity—especially when paired with EDR—providing not just tools, but a whole new approach to threat detection. By focusing on behaviors, not just pre-defined signatures or AI predictions, behavioral analysis brings a proactive, context-aware defense to your cybersecurity stack.
When the hackers change their game, you need to change yours. With behavioral analysis on your side, you can do more than just fight back—you can stay ahead.