As technology continues to advance at an exponential pace, so does the ever-present threat of cyberattacks. In the digital landscape of 2023, mid-sized businesses find themselves at the forefront of this cybersecurity battleground.
When we partnered with Virtual Intelligence Briefing on our State of Cybersecurity for Mid-Sized Businesses in 2023 report, we set out to understand where mid-market businesses have gaps in their cyber stacks, tools and resources, and which cyber challenges are causing them the most burden. What we found was that these businesses were understaffed and unprepared to face today’s threat landscape head-on.
Recently, we hosted a webinar with Tom Riddle of Virtual Intelligence Briefing, Devon Harbord of Standard Supply, and Huntress’ Topher Lyons to discuss these challenges and findings in detail and explore how mid-sized businesses can protect themselves from the increasing impacts of cyberattacks. You can check out the on-demand recording here, or continue reading for the recap!
Key Finding #1: Mid-Sized Businesses Lack the Time and Skills Needed To Deal With Cybersecurity Threats
Time is a precious commodity, and it’s no different when it comes to cybersecurity. The demands of running a mid-sized business often leave little room for cybersecurity management, which then leaves IT and security teams struggling to allocate sufficient time and attention to comprehensively address cyber threats.
In our research report, lack of time and lack of skill topped the list for the most common internal cybersecurity challenges. This also rang true for our webinar attendees—when asked the same question, the responses came back in the same order.

On top of time constraints, mid-sized businesses face another significant obstacle in dealing with cybersecurity threats: the skill gap. They recognize the importance of staying updated with the latest security practices but lack the necessary expertise to level up. While education and training are available, the demand for cyber-savvy personnel is high, making it difficult for these businesses to attract and retain skilled professionals.
Key Finding #2: People Are the Weakest Link
Interestingly, security awareness training emerged as the area where webinar attendees felt they needed the most assistance. This differed slightly from our top response of detecting advanced threats, based on our research report.

While cutting-edge security tools are a must, the human element remains a critical vulnerability today. According to a 2022 SANS whitepaper, hackers consider phishing and social engineering to be the top two attack vectors that yield the highest ROI. This underscores the importance of security awareness training and how it can equip employees with the knowledge and skills necessary to identify and respond to threats like phishing and much more.
But the challenge extends beyond simply offering security awareness training—it’s getting people to genuinely care about security. The harsh reality is that many mid-market employees may view cybersecurity as an abstract concept that doesn't directly impact their day-to-day work. That makes protecting that weakest link, the users, even harder. I think this quote from one of our survey respondents perfectly sums up the struggle mid-sized businesses may be feeling when it comes to security awareness training:

Key Finding #3: Cybersecurity Is a Priority, but Budget Is Hard To Nail Down
When it comes to budgeting for cybersecurity, mid-sized businesses exhibit different approaches. Some allocate funds to address specific gaps in their security infrastructure, while others base their budget on their business's overall security needs.
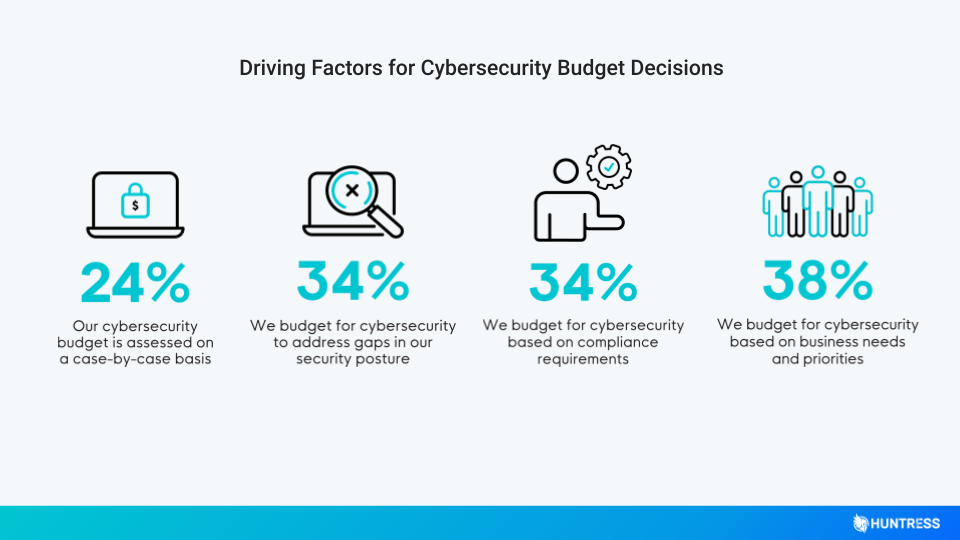
Some even take a mix of these approaches. As an example, Devon shared that he was initially focused on allocating budget to address Standard Supply’s security gaps, but now he’s transitioned to budgeting for best-in-class tools and optimizing their security posture based on their specific business requirements.
Of course, there’s no single way or right way to budget for cybersecurity—but the most important thing is that it’s seen as a priority when it comes to budget allocation.
Watch the Full Webinar
I won’t spoil too much for you, so I suggest watching the full webinar recording to hear our panelists talk in depth about these specific challenges and much more. Also, you won’t want to miss the part where Devon shares his personal experience of how we got Standard Supply to successfully address their most pressing security challenges.