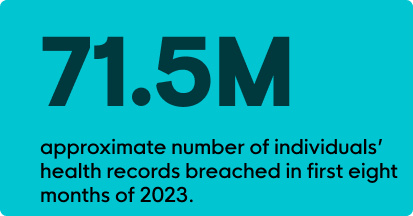
In the first eight months of 2023, nearly 71.5M individuals’ health records had been breached. On top of this startling stat, 88% of surveyed healthcare organizations experienced a cyberattack in the past year. This is a 244% year-on-year increase over August 2022. And 612,000 Medicare beneficiaries were affected in the MOVEit breach as of May 2023. It should be obvious—healthcare is under attack.
Today, a lot of the discussion surrounding cybersecurity in healthcare revolves around antiquated technology; a lack of resources, both people and financial; and the industry’s unique vulnerability to disruptions. Pair these challenges with the fact healthcare organizations house personal health information (PHI) and electronic health records (EHR), and it becomes clear why healthcare is such an attractive target for cybercriminals.
In Healthcare, a Cyberattack Really Can Be Life or Death
If we just look at business email compromise (BEC)—one of the more frequent types of attacks on healthcare organizations—we’ve really got a problem. The HIPAA Journal surveyed 653 healthcare organizations, with 71% of participants reporting that BEC attacks caused poor patient outcomes due to delayed procedures. These delayed procedures led to procedural complications, longer lengths of stay, and increased readmission rates. Even more staggering, 23% of those surveyed saw a rise in mortality rates.
These were just a few of the drivers behind President Biden’s executive order in March 2023. After almost a year, change is finally happening. But not fast enough. That’s why the U.S. Department of Health and Human Services (HHS) is now stepping on the gas. As early as the spring of 2024, HHS plans to:
- Publish voluntary Healthcare and Public Health sector Cybersecurity Performance Goals (HPH CPG) to help healthcare organizations plan and prioritize implementation of high-impact cybersecurity practices.
- Provide resources to incentivize and implement cybersecurity practices by working with Congress to obtain new authority and funding to administer financial support and incentives for domestic hospitals to implement high-impact cybersecurity practices.
- Implement an HHS-wide strategy to support greater enforcement and accountability. HHS will propose new enforceable cybersecurity standards, informed by the Cybersecurity Performance Goals. These will be incorporated into existing programs, including Medicare and Medicaid and the HIPAA Security Rule.
- Expand and mature the one-stop shop within HHS for healthcare sector cybersecurity by deepening HHS and the Federal government’s partnership with the industry, improving access and uptake of government support and services, and increasing HHS’s incident response capabilities.
Do These Apply to Small- and Medium-Sized Organizations?

They do. Health Insurance Portability and Accountability Act (HIPAA) penalties aren’t just reserved for larger healthcare organizations. In 2022, 55% of the financial penalties assessed by HHS’s Office for Civil Rights (OCR) were on small medical practices.
In fact, there’s no shortage of healthcare organizations currently under investigation by OCR. Some of these facilities have as few as 25 employees.
The bottom line is this—enforceable standards are coming. HIPAA Security Rules will be updated as early as spring 2024. And it’s time to get prepared.
Where Does This Leave Smaller Healthcare Organizations?
HHS identifies the top five most impactful threats as:
- Social engineering
- Ransomware attacks
- Loss or theft of equipment or data
- Insider, accidental, or malicious data loss
- Attacks against network-connected medical devices that may affect patient safety
Within each of these threats, HHS identifies the top ten Cybersecurity Practices (or what they call CSPs) to mitigate these threats. To get the full download, HHS does a great job at outlining the vulnerabilities, impact, and best practices to consider. You can check them out here.
If you look across the five most impactful threats, you’ll also see a few repeat offenders among the vulnerabilities.
- Lack of anti-malware detection and remediation tools
- Lack of network security controls, such as segmentation and access control
- Lack of adequate monitoring, tracking, and auditing of access to patient information on EHR systems
- Lack of IT resources for managing suspicious emails
- Lack of awareness training
With finite IT resources and limited teams, there’s a lot of pressure to do more with less. There are few organizations out there offering tools custom built for smaller organizations with under 50 physicians, under 500 providers, or less than 300 beds. There are even fewer orgs that offer multiple solutions and a person to call (or will call you) if something suspicious crops up.
So, What Can You Do?
Endpoint Protection Systems
Specifically, an endpoint detection and response (EDR) solution can monitor, detect, investigate, and respond to malicious activity. A managed EDR, such as Huntress Managed EDR, can be a cost-effective way to extend the capabilities of your team with a 24/7 Security Operations Center (SOC), fully staffed with cybersecurity experts who can respond accordingly to suspicious behavior. With more patient triage and administrators working remotely, it’s important to make sure that whichever solution you choose, it can manage hybrid work environments.
Email Protection Systems
These services can monitor, identify, and respond to suspicious login activity, suspicious email forwarding configurations, and privilege escalation attempts. In 2023, just up to August, BEC attacks had increased by 279% (compared to 2022 levels). That’s why you need a team that can support you 24/7.

Security Awareness Training (SAT)
An engaging SAT program can educate your clinical and administrative staff on cyber threats. But it’s important to make sure the program is relevant to your business and your challenges. Look for courses that dive into how to:
- identify social engineering practices
- identify phishing scams
- underscore the value of patient data
- uphold HIPAA regulations
- maintain password “hygiene”
An effective SAT enables your team to be your first line of defense. After all, it’s best not to take on cyber threats alone.
Humans
When it comes to cybersecurity, your organization is the patient. You shouldn’t have to self diagnose. That’s why you need a trusted team who can guide you, contact you directly, and educate you on how to keep your organization healthy and hacker-free.
Huntress stands alongside you 24/7, protecting your sensitive health records and vulnerable endpoints from malicious threats. Learn more about how Huntress can be integral to your healthcare IT systems.
At the end of the day, healthcare organizations do so much good. You deserve HHS’s carrots. Not their sticks. Learn more about what you can do to prepare for these new guidelines in our webinar: Dissecting the New Health and Human Services Regulations.
Or speak with Huntress experts directly and schedule a live demo.





















