| Password security is the first defense against cyber threats, and with billions of credentials stolen each year, it’s important to practice good password hygiene. |
If your password is 123456, you’re one of more than 3 million accounts using that string of numbers to keep yourself secure.
From using common passwords to reusing passwords and not changing them after a breach, these password statistics reveal just how uncommon it is to follow password best practices. With nearly half (46%) of people getting their passwords stolen in 2024, password security is extremely important.
“People really underestimate how important password security is. It may seem like a given, but the more complex your password is, the more difficult your account is to access,” says Lindsey Welch, Technical Community Engagement Writer at Huntress. “That doesn’t even factor in things like being sure to change your password after a breach and using different passwords, all of which improve security.”
Compiled from a diverse range of data sources, read about some of the most surprising (or unsurprising) password security findings, plus some tips to improve your own password hygiene.
Key Takeaways
- Password reuse and weak credentials remain widespread vulnerabilities: Nearly 30% of people report their passwords were stolen due to reuse, and 35% of hacking victims attribute the breach directly to weak passwords, making unique, complex passwords one of the most critical defenses against unauthorized access.
- The scale of credential theft is staggering: With an estimated 24 billion credentials exposed annually through data breaches and infostealers accounting for 24% of cyber incidents in 2024, no user or organization is immune from the risk of compromised passwords.
- Strong passwords require length, complexity, and uniqueness: Security guidance recommends passwords of at least 16 characters combining upper and lowercase letters, numbers, and special characters, while avoiding personally identifiable details that can be easily guessed or researched by threat actors.
- Password managers and multi-factor authentication (MFA) are underutilized but highly effective tools: Despite 70% of security experts endorsing password managers as the safest management method and 88% of people utilizing MFA, significant gaps remain, with nearly 1 in 4 people using no protective measures at all to safeguard their credentials.
Top password security statistics
Think of your passwords as the keys to your digital kingdom. They guard everything from personal emails and financial accounts to critical business data. While often taken for granted, the strength and security of these digital keys directly impact your safety and privacy online. These key facts about passwords underscore their importance in the face of increasing cyberattacks. By understanding these numbers, you can gain valuable insights into the risks and proactive measures necessary to protect your digital endpoints.
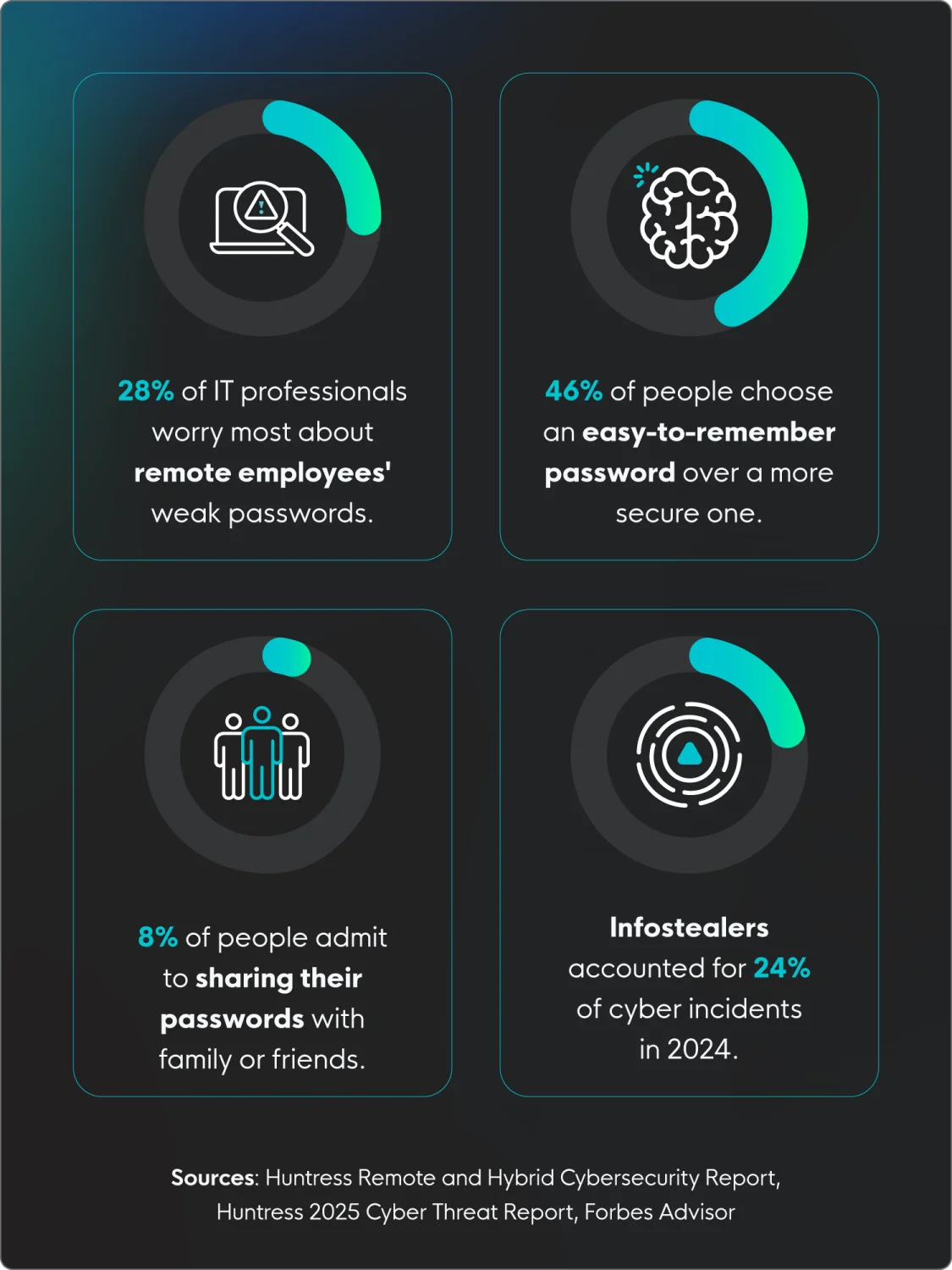
- Password security is a top concern in remote and hybrid work environments, with more than a quarter (28%) of cybersecurity professionals saying that employees using the same or weak passwords is their worst habit. (Huntress Remote and Hybrid Cybersecurity Report)
- Approximately 42% of people who have been hacked have passwords that use a combination of letters and numbers, but these passwords have a personal significance to them, making them easier to guess. (Forbes Advisor)
- Infostealers, a form of malicious software designed to gather credentials and sensitive information, are being used more to steal credentials, with 24% of cyber incidents in 2024 using them. (Huntress 2025 Cyber Threat Report)
- In a 2023 survey, nearly half (46%) of respondents said they chose an easy-to-remember password over one that’s more secure. (Pew Research Center)
- Only about 13% of people use random password generators to create their passwords. (Forbes Advisor)
- Nearly 63% of people only change their passwords when prompted to. (GoodFirms)
- When creating a password, 34% of people use the specific requirements of the platform, adding a number or special character to their base password. (Forbes Advisor)
- While not everyone may be willing to admit it, about 8% of people admitted to sharing passwords with family or friends. (Forbes Advisor)
Huntress Managed SAT
Password Simulation
Stats tell the story. Training changes the behavior. See how Huntress SAT teaches employees real password habits in a way they'll remember.
Password breach statistics
How often are passwords actually compromised? These password hacking statistics offer a look at the persistent threat landscape. From brute force attacks to widespread and deliberate data breaches, these figures show how important proactive password security strategies are in reducing the persistent risk of unauthorized access.
9. Nearly half (46%) of people had a password stolen in 2024. (Forbes Advisor)
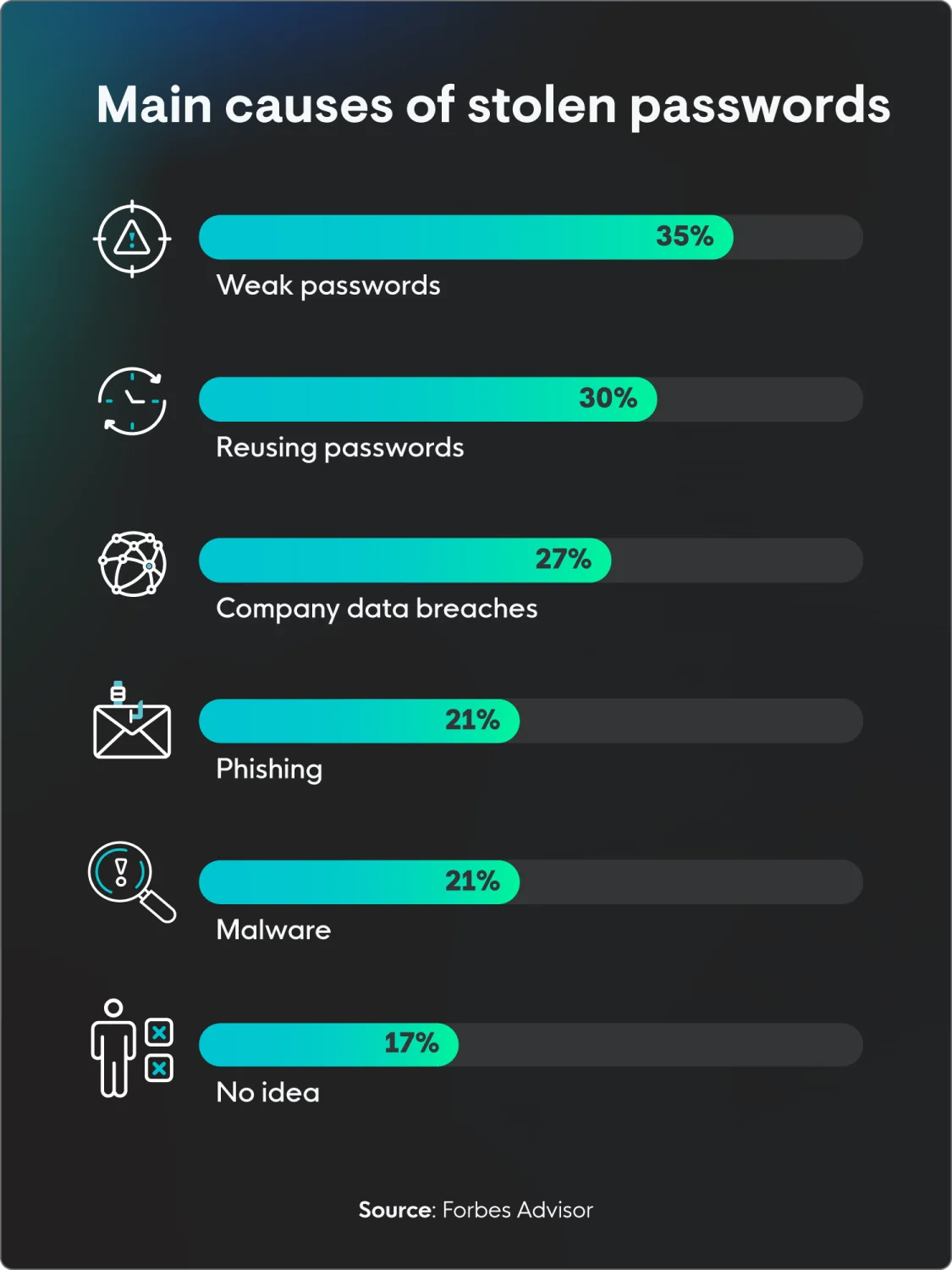
10. According to more than a third (35%) of people who were hacked, weak passwords were to blame. (Forbes Advisor)
11. More than half of Americans (53%) say they’re confident they know what to do in the event of a cyberattack. (Pew Research Center)
12. Conversely, cybersecurity experts, particularly those in healthcare, feel that they’re very prepared for a cyberattack, with 90% rating themselves as either very confident (37%) or somewhat confident (53%). (Huntress Healthcare Cybersecurity Report)
13. Company data breaches were the cause of 27% of stolen passwords. (Forbes Advisor)
14. It’s estimated that more than 24 billion credentials are exposed each year in data breaches. (Security Magazine)
15. About 17% of people have no idea how their passwords were stolen. (Forbes Advisor)
16. The most commonly stolen information in password attacks is first and last name (39%), followed by phone number (38%) and personal address (37%). (Forbes Advisor)
Password reuse statistics
While convenient, the seemingly harmless habit of reusing passwords across multiple accounts creates a dangerous domino effect. Once a single password is compromised in a breach, threat actors gain access to a potentially vast network of your online life.
Learn how common password reuse is and the potential risks of poor password hygiene. Understanding the interconnectedness of your accounts through shared credentials is the first step in breaking this risky habit.
17. Approximately 23% of people reuse a password across three or four different accounts. (Forbes Advisor)
18. It’s no wonder people choose to reuse their passwords, with 69% saying they feel overwhelmed by the number of passwords they need to remember. (Pew Research Center)
19. According to 30% of people, their passwords were stolen because they’d reused it. (Forbes Advisor)
20. Worse still, as many as 92% of IT professionals have admitted to reusing passwords. Do as I say, not as I do, right? (Bitwarden)
Password management statistics
What is password management? It’s exactly what it sounds like: how people manage and remember their passwords. It might seem odd, but it’s actually a booming industry, with many different options on the market to help people remember and secure their passwords.
Here are some key facts about password management:
21. The password management industry is expected to reach more than 2 billion in revenue by the end of 2025. (Statista)
22. Nearly 1 in 4 people (22%) don’t use any particular methods to keep their passwords safe, like using biometrics or password managers. (Forbes Advisor)
23. More than a quarter (27%) of people feel that they waste a lot of time managing passwords, while 67% feel it’s not a waste of time. (GoodFirms)
24. When it comes to password storage, 38% of people write down their passwords. (Forbes Advisor)
25. A different study had similar results, showing that 41% of US adults write their passwords down, while 34% save them to their browser, and 21% just reset them every time they forget. (Pew Research Center)
26. Impressively, more than a third of people (35%) rely on only their memory to recall passwords. (Forbes Advisor)
27. In another study, more than half (51%) of the respondents boasted that they had their passwords memorized. (Security.org)
28. About a quarter of people (24%) store their passwords on their computer, which is not recommended. (Forbes Advisor)
29. The number of people using a password manager rose from 20% in 2019 to 32% in 2023. (Pew Research Center)
30. Google Password Manager is the most popular choice for users. (Security.org)
Stats about password security best practices
While these password statistics may be concerning, the good news is that significant improvements in your security are within reach. The focus should be on actionable steps and proven best practices for creating and managing strong passwords effectively.
While password policy best practices used to include changing your password frequently, that’s not the case anymore. It’s better to create a strong password to begin with, store it securely, and use multifactor authentication (MFA).
By implementing these guidelines, you can take control of your digital security and significantly reduce your risk of falling victim to password-related attacks.
31. About 68% of people are forced to change their passwords at least once a year because of compromised credentials. (Forbes Advisor)
32. A secure password should be long, random, and unique. (CISA)
33. For optimal security, a password should be at least 16 characters long, but the longer, the better. (CISA)
34. About 88% of people utilize multifactor authentication, which is a key way to add extra layers of protection. (GoodFirms)
35. At least 70% of security experts believe password managers are the safest choice for managing passwords. (GoodFirms)
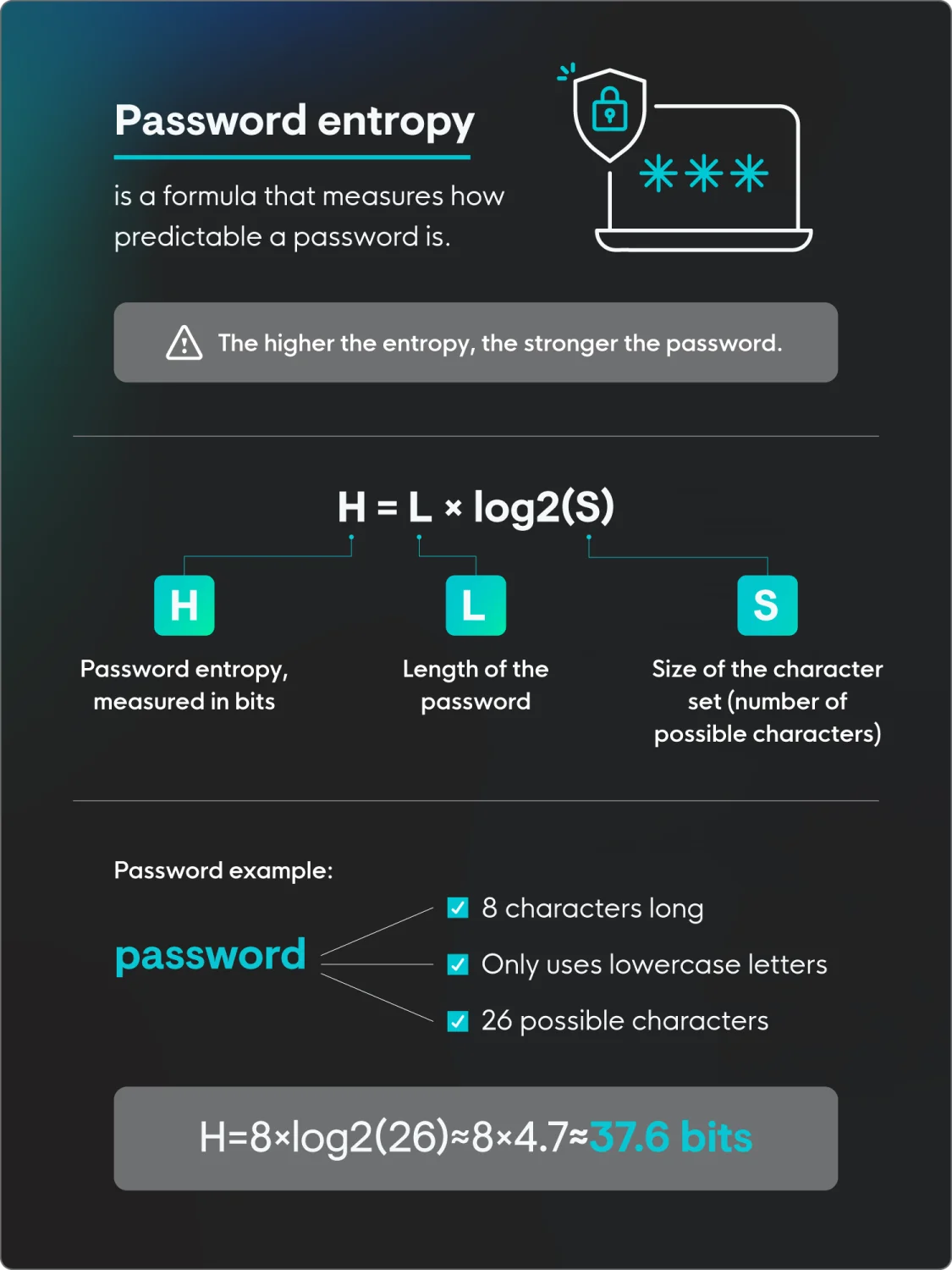
36. There’s actually a formula for measuring password strength or password entropy, which essentially calculates how long it would take to crack a password. Again, the longer, the better. (TechTarget)
How to choose a strong password
Crafting strong passwords is your first and most crucial line of defense. Passwords should be unique, long, and a combination of letters, symbols, and numbers. It should also be something not easily guessable.
“If there’s one single thing that people do when it comes to their passwords, it’s picking something that isn’t reused or easily guessable,” says Welch. “A password that’s easy to guess is a password that’s easy to hack.”
Here are some other key password security tips:
- Make it long: Passwords should be at least 16 characters long.
- Use a mix of characters: A secure password will mix lower and uppercase letters, numbers, and random characters.
- Ensure it’s unique: Avoid using popular passwords, like 123456 or password, as those are very easily guessable.
- Don’t make it personal: Don’t choose the name of your favorite pet or your mom’s maiden name, as those are personal details that someone could easily know or find out.
- Consider using a password manager: These tools securely store and generate strong, unique passwords for all your accounts, so you only need to remember one master password.
- Enable multi-factor authentication whenever possible: MFA adds an extra layer of security by requiring a second verification method (like a code from your phone) in addition to your password.
- Be cautious of phishing attempts: Don't click on suspicious links or enter your password on unfamiliar websites. Always verify the legitimacy of a login page.
- Keep your software up-to-date: Updates often include security patches that can protect against known vulnerabilities.
- Monitor your accounts for suspicious activity: If you notice anything unusual, change your password immediately and report it.
Protect your passwords—and yourself—with identity theft protection
Understanding these password statistics and how to better secure your accounts is the first step of many to ensure your security online.
We understand what threats like credential theft and unauthorized access mean for your business, and we’re here to help. Huntress has you covered with managed identity threat detection and response (ITDR), protecting identities across your organization 24/7.
Password Stats FAQs
How many passwords does the average person have?
The common number used to be about 100, but new research suggests it’s about 168 passwords across personal accounts and 87 for business accounts, meaning the average person may have more than 250.
What is the number 1 most used password?
The most common password is 123456.
How many passwords are hacked every day?
Likely millions of passwords are hacked across the world every day. Cyberattacks are super frequent, with an attack about every 39 seconds.