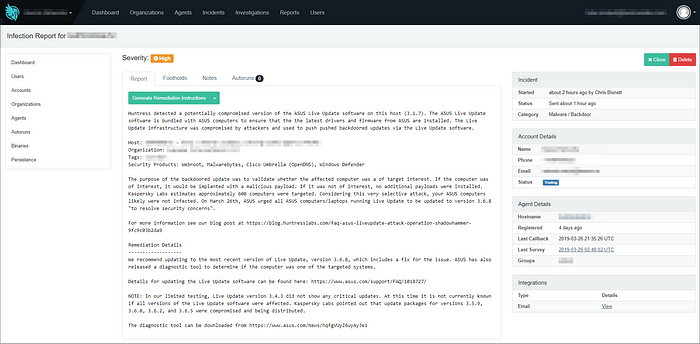
Periodically, a large scale cybersecurity issue requires “all hands on deck” from the Huntress Team (see WannaCry, Kaseya Cryptominer, GANDGRAB outbreak). The unfolding ASUS Live Update fiasco also happens to be one of those moments. We’ve created this blog is to provide simple answers to a complex supply chain attack affecting global IT Departments.
Situation Overview
The hardware manufacturer ASUS included an application on all of their Windows devices called Live Update. Between June and November 2018, Hackers compromised ASUS’ automatic updating infrastructure and pushed backdoored updates via the Live Update software. Kaspersky Lab suggests that over a million hosts may have run a backdoored update.
The purpose of the backdoored update was to validate whether the affected computer was a target of interest. If the computer was of interest, it would be implanted with a malicious payload. If it was not of interest, no additional payloads were installed. It’s estimated approximately 600 computers were targeted. Considering this very selective attack, your ASUS computers likely were not infected. On March 26th, ASUS urged that all ASUS computers/laptops running Live Update should be updated to version 3.6.8 “to resolve security concerns”.
To give our partner’s peace of mind, the Huntress Development Team created custom tools to discover any computer, laptop, or server running Live Update below version 3.6.8 (huge thanks to MNS Group for being our guinea pig!)
The ThreatOps Team has reported all hosts running an outdated Live Update application and we’ll continue to monitor the situation for any updates or new agents that come online.
How to Verify if a Backdoored Update was Executed
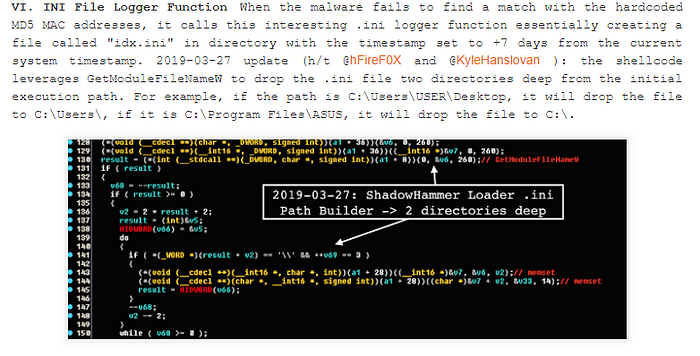
All backdoored updates for Live Update included a modified version of Setup.exe. Within this application, the attackers added an obfuscated shellcode payload (this is what was looking for the targeted MAC addresses).
If your computer was not targeted, the shellcode will create a file called idx.ini similar to the following example:
As a result of this discovery, you can search your file system for the idx.ini file to determine if a backdoored update was run on your host!
Vitali Kremez’s blog dives into the technical implementation of this much deeper and demonstrates how the shellcode will write the idx.ini file to a directory up to two levels higher than where Setup.exe was executed.
How to Verify if an ASUS Computer was Targeted
Only 600 hosts were targeted with the second stage malware which means you and your clients likely didn’t receive the attention of a nation-state adversary 🕵️ (sorry to disappoint). However, we totally understand the difference between assuming and knowing you weren’t targeted.
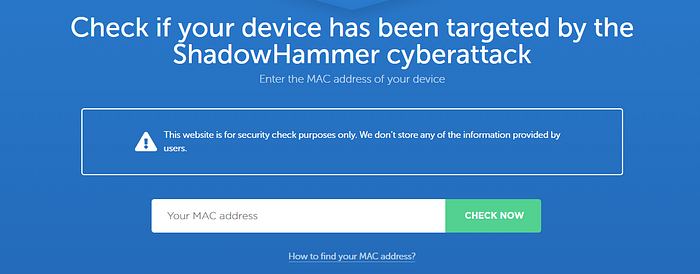
For those looking to verify if their computer was on the hit list, check out the security diagnostic tools release by ASUS and Kaspersky Lab. These applications will gather host details like the MAC address and cross reference your data against list of targeted MAC addresses.
Hesitant to run the software? Security researchers reverse engineered Kaspersky Lab’s tool and released nearly all 600 MAC addresses that were targeted which you can check against. A website has also been created which allows you to manually submit your ASUS computer’s MAC address.
Is Your Computer Targeted?
If a diagnostic tool indicated you’re targeted, we’re here to help! Contact us at support[at]huntress.io and we’ll have someone quickly reach out to you.
With that said, it should be noted that one of the targeted MAC addresses belonged to a generic VMware interface:
In this case, the backdoored update actually checked for the presence of two MAC addresses. As long as your other NIC did not have MAC address 70:77:81:C0:FD:49, you’re likely in the clear.
How to Update ASUS’ Live Update
According to ASUS’ media response on March 26th, 2019, Live Update version 3.6.8 was released. ASUS specifically highlighted this new version:
…introduced multiple security verification mechanisms to prevent any malicious manipulation in the form of software updates or other means, and implemented an enhanced end-to-end encryption mechanism.
The US Cybersecurity and Infrastructure Security Agency (CISA) also made an announcement about Live Update version 3.6.8 stating:
This version addresses vulnerabilities that a remote attacker could exploit to take control of an affected system. These vulnerabilities were detected in exploits in the wild.
For IT Departments or Managed Service Providers looking to upgrade Live Update to version 3.6.8, please follow ASUS’s online checklist.
What if Live Update is Not Updating?
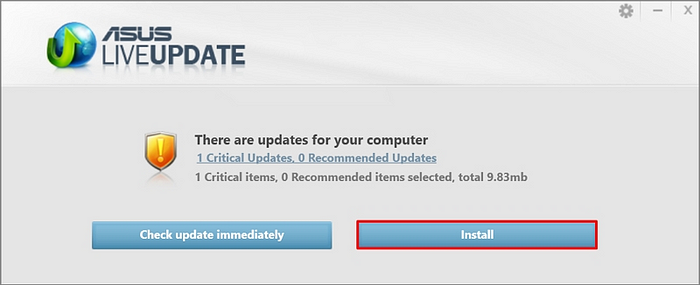
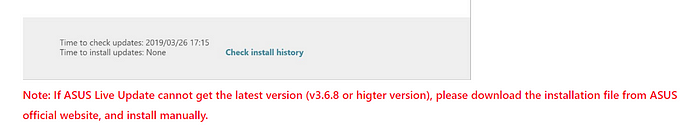
While working with our partners, we observed some issues with Live Update checking for updates:
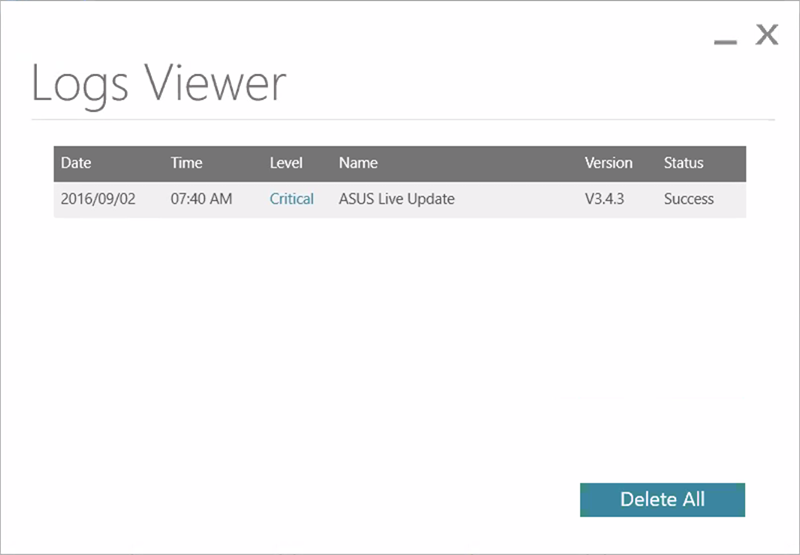
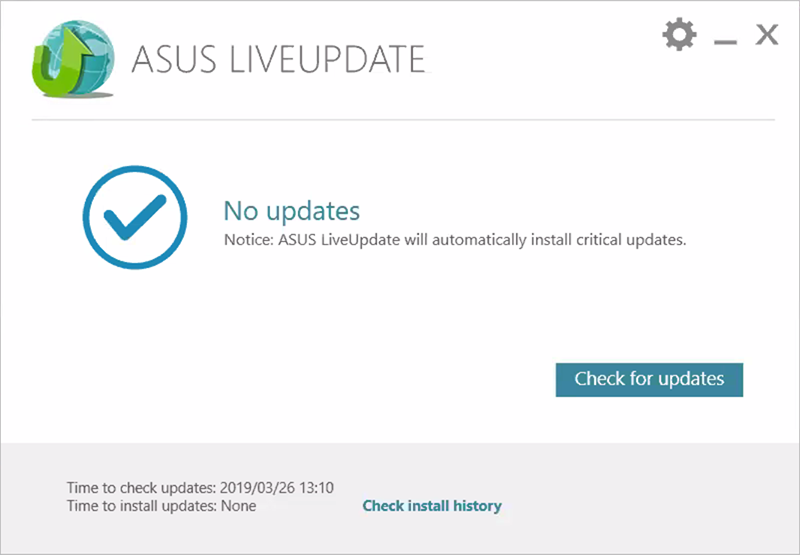
As demonstrated above, at least some hosts running Live Update below version 3.6.8 are not receiving the new update. ASUS noted this could happen in their support documentation. Unfortunately, we have not found a manual installer for version 3.6.8.
Notifying Your Customers
It’s very likely this issue will garner media attention as details continue to unfold. IT departments and Managed Service Providers should leverage this opportunity to demonstrate their ability to address breaking cybersecurity incidents.
We’re currently creating some resources to help you articulate what was done to ensure your company’s and client’s security. Stay tuned!
Huntress Play-by-Play
This situation is still unfolding. Check the section frequently for updates!
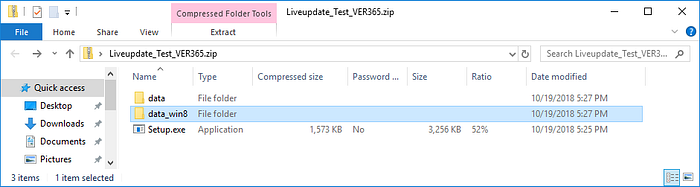
On March 25th, 2019, journalist Kim Zetter dropped an explosive article detailing the supply chain attack against ASUS’ Live Update. Shortly after, Kaspersky Lab followed up with a handful of indicators of compromise (IOC) which included four malicious .ZIP files:
- hxxp://liveupdate01.asus[.]com/pub/ASUS/nb/Apps_for_Win8/LiveUpdate/Liveupdate_Test_VER365.zip
- hxxps://liveupdate01s.asus[.]com/pub/ASUS/nb/Apps_for_Win8/LiveUpdate/Liveupdate_Test_VER362.zip
- hxxps://liveupdate01s.asus[.]com/pub/ASUS/nb/Apps_for_Win8/LiveUpdate/Liveupdate_Test_VER360.zip
- hxxps://liveupdate01s.asus[.]com/pub/ASUS/nb/Apps_for_Win8/LiveUpdate/Liveupdate_Test_VER359.zip
These .ZIP archives contained a setup .EXE and two .MSI files. The MSI files also extracted over a dozen applications and configuration files for Live Update. This made determining the backdoor less trivial.
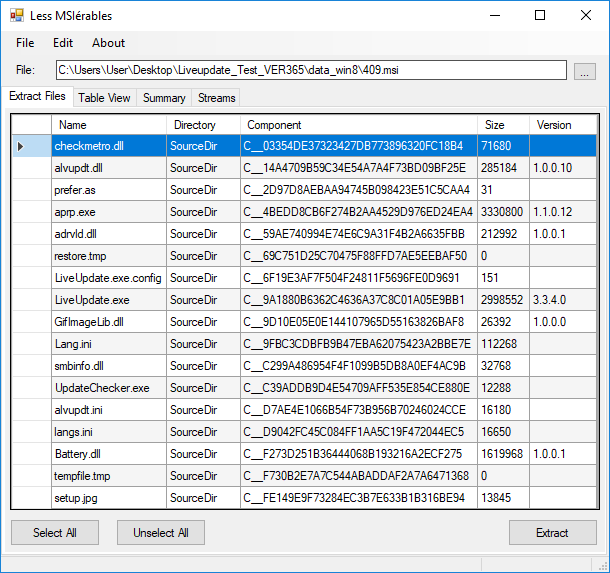
Researchers on Twitter also pointed out that Setup.exe was specifically backdoored to decrypt and run the attackers payload.
Using these details, the Huntress ThreatOps team gathered known malware samples and started the analysis process to understand which parts of Live Update was actually compromised.