
Remote Desktop Services (RDS) benefit employees and IT administrators alike. With employees often working from anywhere, remote desktop reduces the physical burden of carrying a work laptop home 🏠. It also makes updating and managing systems easier, which can alleviate the administrative burden when handling a large network. 👨💼
Unfortunately, a vulnerability recently discovered in RDS has the potential to let hackers remotely wreak havoc on computers or servers running RDS — and their networks — if the issue isn’t patched. Read on to learn more!
What is BlueKeep?
During Windows’ May 2019 patch cycle, Microsoft released a patch for a remote code execution bug in their Remote Desktop Services software. If left unpatched, this vulnerability could allow remote, unauthenticated attackers to execute payloads with administrative privileges and spread to other computers/servers within a network.
Errata Security CEO, Robert Graham, scanned all externally facing IP addresses on May 28th, 2019 for systems susceptible to BlueKeep.
In his blog, Robert estimated nearly one million computers, laptops, and servers may be vulnerable and Microsoft noted that if an attacker is able to gain access into the system, they could then “install programs; view, change, or delete data; or create new accounts with full user rights.”
Exploiting the Vulnerability
Offensive security researchers have worked around the clock to prove the BlueKeep vulnerability could be exploited by malicious hackers. On June 3rd 2019, Ryan Hanson showcased his success on Twitter despite having “very little experience with kernel exploitation”.
Considering previous wormable attacks like WannaCry, the Huntress team has high confidence that hackers will start attacking unpatched computers and servers in the very near future. Microsoft, NSA, and dozens of fellow security vendors have made similar conclusions and advise IT departments to immediately patch affected systems.
How Did Huntress Determine Vulnerable Hosts?
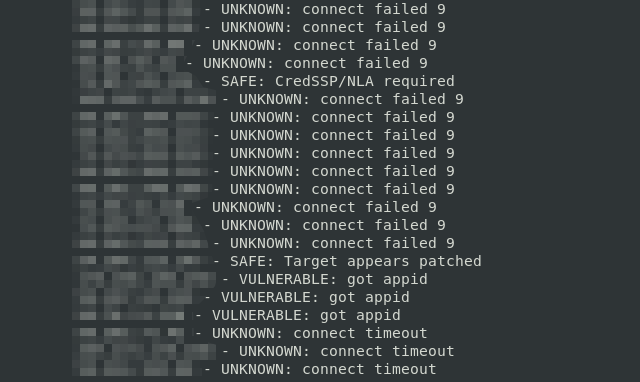
The Huntress team has kept a close eye on Robert Graham’s success with identifying vulnerable hosts using RDPScan. Once all quirks were ironed out, we leveraged his hard work to cross-reference our partner’s Windows Vista, 7, Server 2008, and Server 2008 R2 hosts. We specifically examined these hosts’ externally facing IP addresses which exposed 3389 to the internet. We did not look for non-standard/obfuscated RDP ports and Huntress doesn’t run on XP or Server 2003 hosts.
The Huntress team recorded the external IP address of every host that RDPScan claimed was vulnerable. With this database, we created custom tools to notify all affected partners via email on June 4th, 2019.
Since we assessed these hosts externally, it’s worth noting you may have more vulnerable systems within your network(s) that were offline, not running the Huntress software, or simply not externally accessible. Please see our section on finding hosts that are vulnerable to help you gain full awareness of your patch status.
How Do I Fix This Vulnerability?
Due to the severity of BlueKeep, Microsoft has released patches for all actively supported versions of Windows and the old/busted versions from yesteryear. You can find these patches here:
- Windows 7, Server 2008, and Server 2008 R2 patches
- Windows XP, Server 2003, Server 2003 R2, and Windows Vista patches
Installing the appropriate patch via your tried and tested patching process will fix this vulnerability. Considering the criticality of this issue, we strongly suggest you trust but verify the success of these patches.
What is the Risk of Not Fixing the Vulnerability?
Vulnerable hosts are extremely likely to be remotely compromised by an attacker which could lead to data theft or encryption of all files using ransomware.
Considering this has the potential to be a wormable exploit, not only would the exploited host be affected but an entire network could be impacted as well.
How Can I Test Which Hosts Are Vulnerable?
Robert Graham developed a simple assessment tool called RDPScan that the Huntress ThreatOps team used to remotely detect which externally facing hosts were vulnerable. This same tool can be used to locally determine if a Windows computer/server is vulnerable. To do this, perform the following steps:
- Download the RDPScan tool from GitHub.
- Extract the application from the downloaded .ZIP archive to a location of your choice.
- Open a command prompt and navigate to the directory where you extracted rdpscan.exe.
- Type the command rdpscan.exe localhost to test whether this host is vulnerable BlueKeep.
- If vulnerable, RDPScan will report VULNERABLE—got appid as seen below.
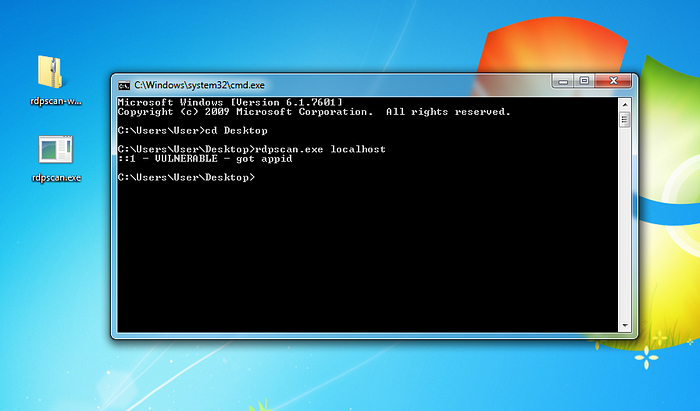
For MSPs and IT departments with RMM software, it’s absolutely possible to recreate this process en masse. This may be an easier method than attempting to remotely scan within segmented/VLAN’d networks.
Will Testing the Vulnerability Harm My Hosts?
During our testing, the RDPScan tool appeared quite stable and did not cause any serious side-effects on the systems we tested. However, some security researchers using other tools have demonstrated this vulnerability is capable of crashing hosts.
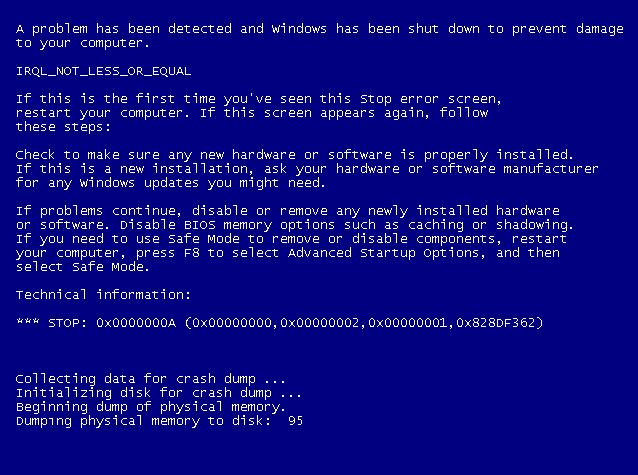
With this in mind, it seems plausible a scanned host could crash and restart but shouldn’t have any lasting effects.
How Do I Make Sure Hosts Are No Longer At Risk?
Once you have successfully installed the Microsoft patch on all vulnerable hosts, these computers/servers should no longer be at risk to this threat. Considering the risk posed by attackers using BlueKeep, we strongly encourage that partners verify the fix was correctly applied to reduce any unexpected surprises in the future.
The Huntress team will continue to assess your hosts and notify you if any other affected external IP addresses are identified.
Answers to Some Very Good Questions You Might Still Have After Reading this Post
Does a vulnerability mean an attack has happened?
No, but it does mean an attack could happen. Microsoft has issued a second Advisory this month asking RDS users to install a patch. The sooner this is done, the better.
Now that BlueKeep is well-known, are the chances of an attack higher?
Yes, it’s only a matter of time before an attacker takes advantage of this vulnerability.
Why hasn’t everyone installed the patch yet?
Compare this to knowing someone has a key to your house, but they haven’t ever used the key yet. You might know you need to change the locks on your doors, but other day-to-day life keeps getting in the way.
Do I need to install the patch now?
Yes. Go. Why are you still reading this post?
The Huntress team will continue to update this post as developments emerge on BlueKeep.
Follow our team on Twitter for more insights, guidance, and tips.








